Best Crypto Media Outlets (2025)

Why Crypto Media Outlets Matter in September 2025
If you trade, build, or invest in digital assets, your edge starts with information. The PRIMARY_KEYWORD—“best crypto media outlets”—are the publishers and platforms that break market-moving stories, explain complex narratives, and surface on-chain trends fast enough to act. In one line: A crypto media outlet is a specialized publisher that reports, analyzes, and contextualizes digital-asset markets and technology for investors and builders.
This guide is for retail traders, crypto-native professionals, and institutions comparing crypto news websites and blockchain news sites to build a trustworthy daily stack. We synthesized public info from official publisher pages and cross-checked coverage breadth, depth, and consistency. Below, you’ll find concise picks, a decision guide by use case, and a practical checklist so you can choose confidently.
How We Picked (Methodology & Scoring)
- Scale & reach (30%): publishing cadence, breadth of coverage across assets/sectors, market relevance.
- Security & integrity (25%): disclosures, editorial standards, conflicts-handling, reputation.
- Coverage depth (15%): investigative work, explainers, data/indices, multimedia (podcasts/video).
- Costs & access (15%): free vs. paid offerings, newsletter value, archives, tools.
- User experience (10%): site speed, navigation, categorization, mobile experience.
- Support (5%): newsletters, alerts, community channels.
We relied on official sites, about/trust pages, product pages, and disclosures; we used widely cited market datasets (e.g., CoinGecko/Kaiko/CCData) only to sanity-check scale claims. Last updated September 2025.
Top 10 Crypto Media Outlets in September 2025
1. CoinDesk — Best for market-wide coverage & benchmarks
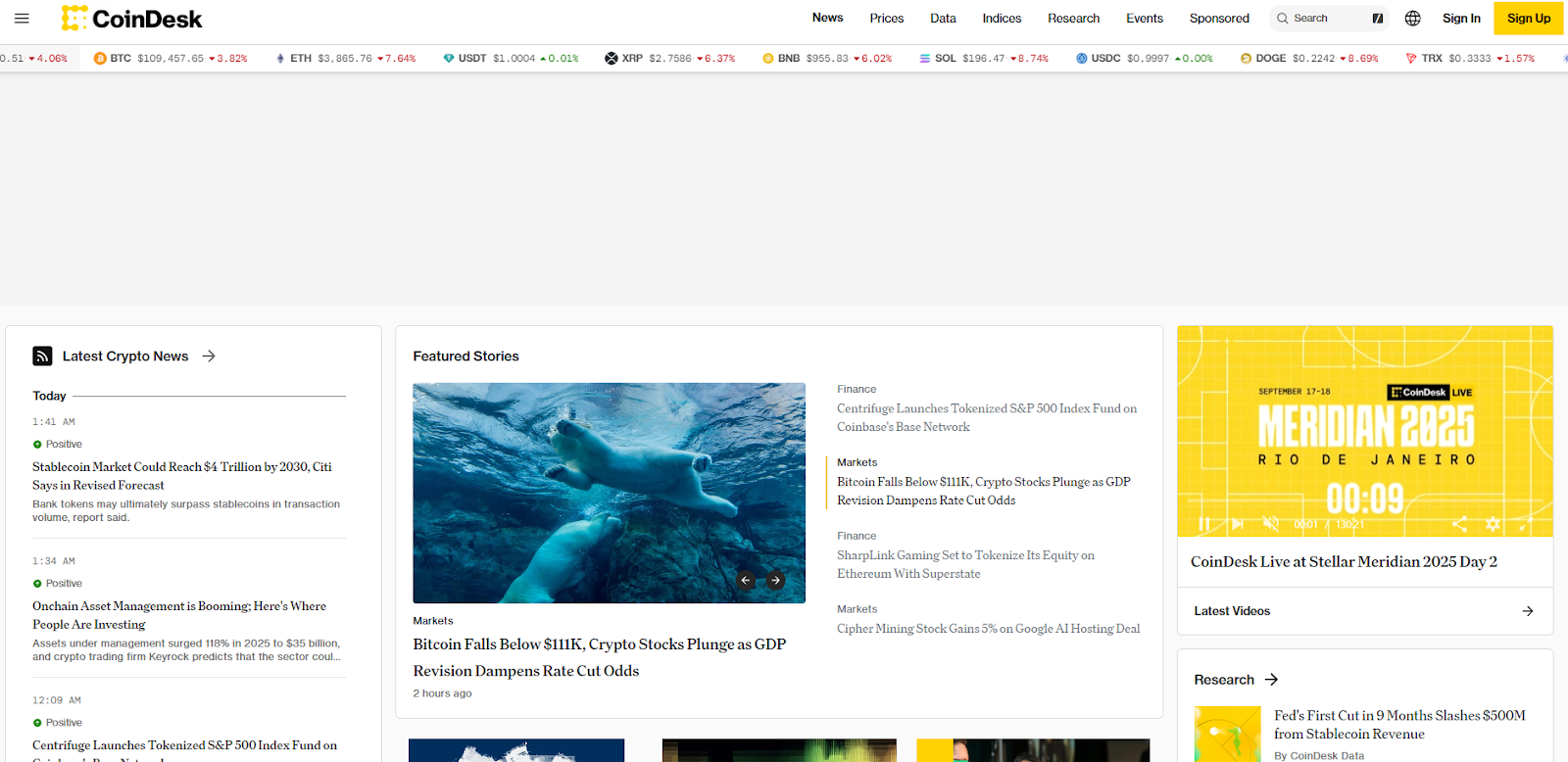
- Why Use It: Longstanding leader with high-volume daily reporting across markets, policy, and tech. Its indices arm adds a data-backed lens that helps translate headlines into benchmark context.
- Best For: Active traders, institutions, researchers, founders.
- Notable Features: Newsroom with global scope; real-time prices; CoinDesk Indices benchmarks; newsletters & events.
- Consider If: You want one primary feed that balances speed with breadth.
- Regions: Global
- Fees Notes: Free site; optional premium/event products.
- Alternatives: The Block, Blockworks
2. The Block — Best for market and policy scoops

- Why Use It: Known for quick market and regulatory coverage with a professional tone, plus companion price pages. It’s a strong second screen for intraday context and breaking items.
- Best For: Pro traders, compliance teams, venture & research analysts.
- Notable Features: Latest-crypto-news hub; market sections; newsletters; headlines geared to execution decisions.
- Consider If: You want fast, concise reporting that’s easy to scan during volatile sessions.
- Regions: Global
- Fees Notes: Free core content; optional subscriptions/events.
- Alternatives: CoinDesk, DL News
3. Blockworks — Best for pro-grade analysis & podcasts
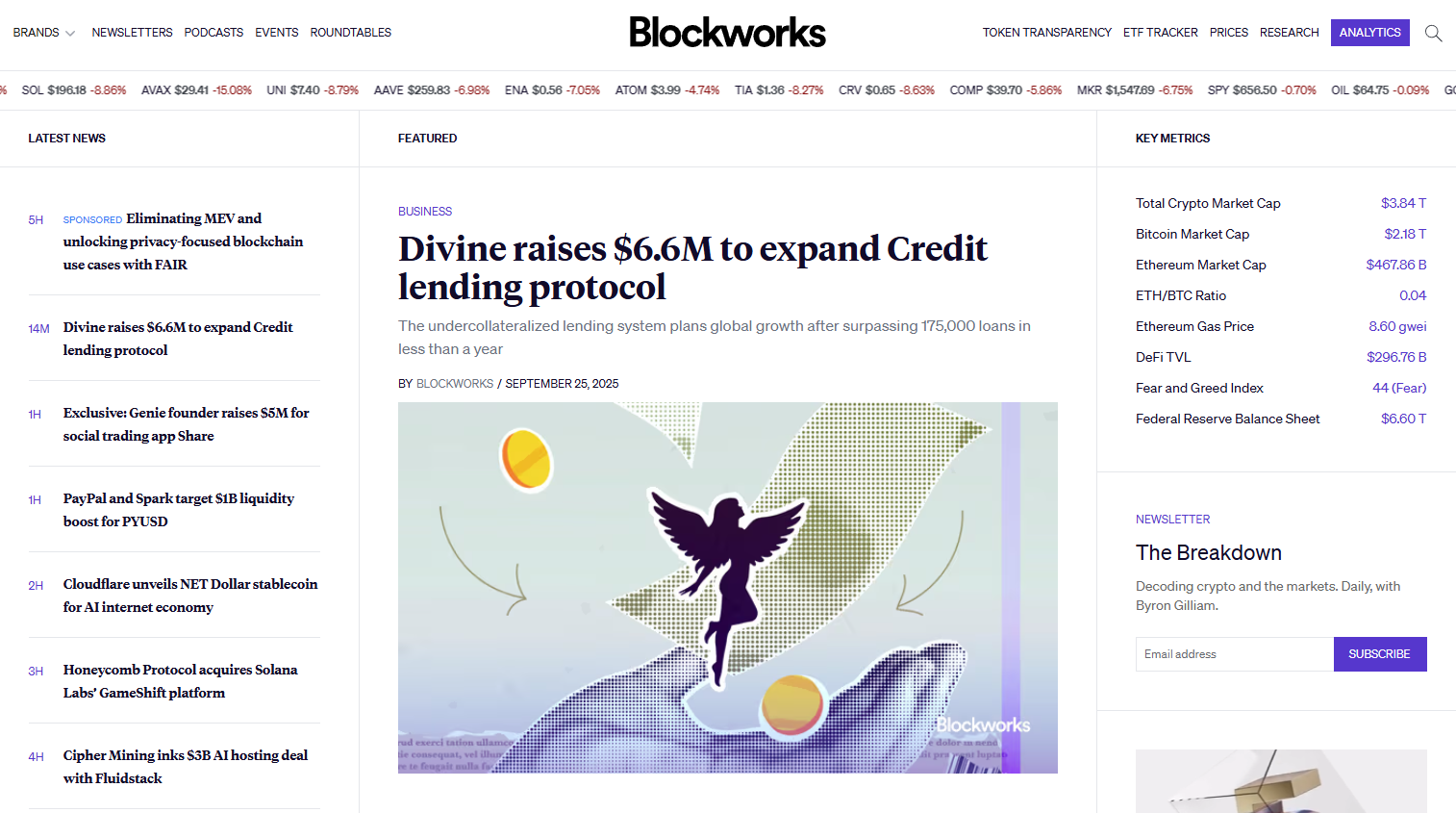
- Why Use It: Bridges media and markets with insightful explainers, a strong podcast lineup, and clean price/data pages—useful for macro-to-micro synthesis.
- Best For: Professionals, allocators, builders, podcast-first learners.
- Notable Features: Deep-dive articles; daily/weekly shows; conference heritage; tidy category navigation; coin price pages.
- Consider If: You prefer long-form insights and audio alongside headlines.
- Regions: Global
- Fees Notes: Mostly free; premium experiences may vary.
- Alternatives: CoinDesk, The Defiant
4. Cointelegraph — Best for global/multilingual news flow
- Why Use It: Large, global newsroom with multi-language publishing and consistent cadence across Bitcoin, Ethereum, DeFi, NFTs, and regulation.
- Best For: Global audiences, multi-market traders, newcomers seeking regular updates.
- Notable Features: Multilingual site; daily roundups; app; newsletters; opinion/education content.
- Consider If: You want wide geographic and thematic coverage in one destination.
- Regions: Global
- Fees Notes: Free site; branded content clearly labeled.
- Alternatives: Decrypt, CryptoSlate
5. Decrypt — Best for culture-meets-crypto storytelling
- Why Use It: Combines markets and tech with culture, gaming, and emerging tech angles—useful to understand adoption narratives, UX shifts, and mainstream crossovers.
- Best For: Builders, marketers, retail investors tracking user-facing trends.
- Notable Features: News + explainers; multimedia; creator/vertical experimentation; active newsletters.
- Consider If: You value context on how crypto meets consumer internet and media.
- Regions: Global
- Fees Notes: Free site; sponsored posts labeled.
- Alternatives: Cointelegraph, Blockworks
6. DL News — Best for investigations & DeFi/regulation depth
- Why Use It: Independent outlet with a reputation for original reporting on markets, DeFi, and policy. A strong pick when you need more than a headline.
- Best For: Risk managers, DeFi natives, legal & policy watchers.
- Notable Features: Investigations; markets/regulation verticals; newsletters; in-depth articles.
- Consider If: You want rigorous follow-through on complex stories.
- Regions: Global
- Fees Notes: Free core content; memberships may vary.
- Alternatives: The Defiant, Protos
7. Bitcoin Magazine — Best for Bitcoin-only depth
- Why Use It: OG Bitcoin publication with dedicated coverage of BTC markets, mining, policy, and culture; ideal as a specialized complement to broader feeds.
- Best For: Bitcoin investors, miners, infra teams, macro allocators watching BTC cycles.
- Notable Features: News & analysis; mining/market sections; conference heritage; op-eds from BTC experts.
- Consider If: You want focused BTC-first reporting without altcoin noise.
- Regions: Global
- Fees Notes: Free site; premium/events may apply.
- Alternatives: CoinDesk, Cointelegraph
8. CryptoSlate — Best for directory-style context + news
- Why Use It: Combines daily news with handy project/company directories and market pages, making it a useful jumping-off point when researching unfamiliar tickers.
- Best For: Generalists, research assistants, retail learners.
- Notable Features: News 24/7; asset/company directories; insights sections; categories by chain and sector.
- Consider If: You like to pivot from headlines to directories for quick diligence.
- Regions: Global
- Fees Notes: Free informational site.
- Alternatives: Cointelegraph, Decrypt
9. The Defiant — Best for DeFi-native explainers & interviews
- Why Use It: DeFi-first outlet with explainers, newsletters, and podcasts/videos that decode protocols, tokenomics, and governance for practitioners.
- Best For: DeFi builders, power users, on-chain analysts.
- Notable Features: News; interviews; education; strong newsletter cadence; multimedia formats.
- Consider If: You want builder-grade clarity on DeFi narratives.
- Regions: Global
- Fees Notes: Free content; optional paid products may appear.
- Alternatives: DL News, Blockworks
10. Protos — Best for skeptical takes & accountability reporting
- Why Use It: Delivers clear, skeptical, “cut-through-the-noise” reporting—useful as a counterbalance to hype cycles and for accountability coverage.
- Best For: Risk teams, auditors, seasoned traders who value contrarian perspectives.
- Notable Features: Investigative tone; editorials; market-moving tidbits; concise format.
- Consider If: You want a critical lens alongside bullish feeds.
- Regions: Global
- Fees Notes: Free site.
- Alternatives: DL News, The Block
Decision Guide: Best By Use Case
- One primary daily feed: CoinDesk
- Fast policy/market scoops: The Block
- Pro-grade audio + analysis: Blockworks
- Global/multilingual coverage: Cointelegraph
- Consumer/culture angles: Decrypt
- Investigations & DeFi policy: DL News
- Bitcoin-only depth: Bitcoin Magazine
- Headlines with directories: CryptoSlate
- DeFi explainers & interviews: The Defiant
- Skeptical/forensic lens: Protos
How to Choose the Right Crypto Media Outlet (Checklist)
- Region & language: Does it serve your market and preferred language(s)?
- Coverage fit: Generalist vs. Bitcoin-only vs. DeFi-native.
- Depth: Are there explainers, investigations, indices, or data to go beyond headlines?
- Access & costs: Free vs. paid tiers; newsletter value; RSS/alerts.
- UX & speed: Mobile performance, category navigation, price pages.
- Integrity: Disclosures, labeled sponsored content, clear editorial standards.
- Support/community: Podcasts, newsletter cadence, socials.
- Red flags: Vague sourcing; unlabeled ads; sensational claims without links.
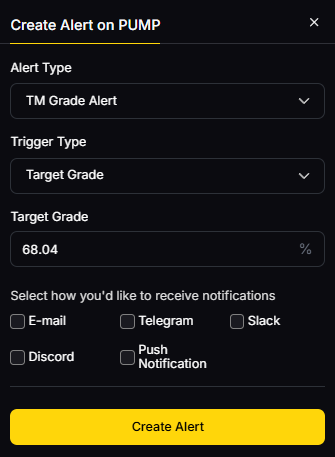
Use Token Metrics With Any Crypto Media Outlet
Pair trusted news with quant and AI to act with conviction:
- AI Ratings to screen narratives and assets quickly.

- Narrative Detection to spot momentum in sectors (L2s, RWA, DeFi).
- Portfolio Optimization to size bets with risk constraints.
- Alerts & Signals to time entries/exits as headlines hit.
Workflow: Research → Shortlist → Execute with your chosen venue → Monitor via TM alerts.
Primary CTA: Start free trial

Security & Compliance Tips
- Enable 2FA on all publisher and newsletter logins to protect account access.
- Treat media as input, not instruction—cross-check with official project docs and disclosures.
- Keep a research journal: link sources, note dates, and log what changed your mind.
- Separate ad/sponsored content from editorial and verify claims before acting.
- Use wallet hygiene and a risk budget when headlines tempt FOMO.
This article is for research/education, not financial advice.
Beginner Mistakes to Avoid
- Relying on a single outlet; diversify your media stack.
- Confusing sponsored posts with editorial.
- Acting on headlines without checking primary sources/on-chain data.
- Ignoring regional policy context that changes risk.
- Chasing every narrative without a portfolio plan.
FAQs
What is a crypto media outlet?
A publisher focused on digital-asset markets and technology—covering news, analysis, and explainers for traders, investors, and builders. Many also offer newsletters, podcasts, and events.
How many outlets should I follow daily?
Two to three complementary sources usually balance speed and depth (e.g., one generalist, one investigative/DeFi, one podcast). Add specialized feeds (e.g., Bitcoin-only) as needed.
Are paid crypto news subscriptions worth it?
They can be if you use the added depth (investigations, research notes, data). For most traders, a free stack plus one targeted premium product is sufficient.
Which outlet is best for U.S. regulatory coverage?
Generalists like CoinDesk and The Block cover U.S. policy closely; DL News and The Defiant provide strong DeFi/regulation analysis. Cross-check with official agency releases.
Where can I get crypto news in multiple languages?
Cointelegraph runs multilingual editions and apps; several outlets offer newsletters and region-specific writers. Verify language availability and local relevance.
Do these sites move markets?
Major scoops, enforcement actions, or exchange/security stories can move prices, especially in thin-liquidity hours. Use alerts and confirm via official disclosures.
Conclusion + Related Reads
The “best” outlet depends on your role and the decisions you make. If you need one primary feed, start with CoinDesk; add The Block for scoops and Blockworks for pro-grade audio. Layer DL News/The Defiant for DeFi and Bitcoin Magazine for BTC focus. As always, pair news with structured research and disciplined risk.
Related Reads:
- Best Cryptocurrency Exchanges 2025
- Top Derivatives Platforms 2025
- Top Institutional Custody Providers 2025
Sources & Update Notes
We verified offerings and focus areas on each outlet’s official pages and current navigation, plus recent announcements. Cross-checks included widely cited market datasets to gauge breadth and cadence. Updated September 2025.
- CoinDesk — Homepage, Prices, Indices pages. CoinDesk+2CoinDesk+2
- The Block — Homepage, Latest Crypto News. The Block+1
- Blockworks — Homepage, News & Prices. Blockworks+2Blockworks+2
- Cointelegraph — Homepage, Latest News, Multilingual footprint. Cointelegraph+1
- Decrypt — Homepage, News. Decrypt+1
- DL News — Homepage, About, Articles. DL News+2DL News+2
- Bitcoin Magazine — Homepage, News/Markets/Articles. Bitcoin Magazine+3Bitcoin Magazine+3Bitcoin Magazine+3
- CryptoSlate — Homepage, News, Directories. CryptoSlate+2CryptoSlate+2
- The Defiant — Homepage. The Defiant
- Protos — Homepage, About. Protos+1
Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)









.svg)




.png)