Best Crypto Tax Software (2025)

Why crypto tax reporting & portfolio reconciliation software Matters in September 2025
Crypto taxes are messy—DeFi, NFTs, cross-chain bridges, airdrops, staking, and perpetuals all create taxable events. The best crypto tax software helps you import everything, reconcile cost basis, and generate compliant reports (e.g., IRS Form 8949/Schedule D) in minutes. In one line: crypto tax software is a tool that ingests your on-chain and exchange data and produces compliant tax reports for your jurisdiction.
In 2025, new broker reporting rules and evolving national guidance raise the stakes for accuracy. This guide prioritizes global coverage, robust reconciliations for DeFi/NFTs, and clear pricing. Whether you’re a retail investor, active DeFi/NFT trader, or a tax pro, you’ll find vetted options below, plus a quick decision map and setup checklist. (See Sources section for official docs cited.)
How We Picked (Methodology & Scoring)
- What we scored (weights): Scale & data handling (30% liquidity/coverage in practice—can it ingest many venues at volume?), Security (25%) including 2FA, data handling, disclosures; Coverage (15%) of assets/DeFi/NFTs/chains; Costs (15%) (transparent plans, value at higher tx counts); UX (10%) (import helpers, error resolution); Support (5%) (tax-pro help, chat, docs).
- Data sources: Official product and security pages, pricing and docs; limited cross-checks with widely cited market datasets for context. We do not rely on affiliate reviews.
- Freshness: Last updated September 2025; we noted regional changes (e.g., deprecations/partnerships) from official announcements. Koinly+2ZenLedger+2
Top 10 crypto tax reporting & portfolio reconciliation software in September 2025
1. Koinly — Best for fast setup across 20+ countries

{
"name":"Koinly",
"url":"https://koinly.io/",
"tagline":"Best for fast setup across 20+ countries",
"why_use_it":"Polished imports, broad exchange/wallet support, and clean reports you can hand to your CPA. Strong retail UX with preview-before-pay and ready-made IRS forms. Good balance of speed and depth for DeFi/NFTs.",
"best_for":"Retail investors; casual DeFi users; U.S., EU & APAC filers needing standard forms",
"notable_features":["Free preview of gains","Form 8949 & Schedule D exports","Integrations for major exchanges/wallets"],
"fees_notes":"Free preview; paid tiers scale by transaction count.",
"regions":"Global",
"alternatives":["CoinLedger","CoinTracker"]
}
Key facts per official site: global availability, free preview, IRS forms. Koinly+1
2. CoinLedger — Best for U.S. filers who want simple, fast forms
{
"name":"CoinLedger",
"url":"https://coinledger.io/",
"tagline":"Best for U.S. filers who want simple, fast forms",
"why_use_it":"Straightforward import flow with strong U.S. forms and helpful education. Good DeFi/NFT coverage for most retail needs without overcomplicating the setup.",
"best_for":"U.S. filers; creators/traders mixing CEX, NFTs, staking; DIY with CPA handoff",
"notable_features":["Instant tax forms","DeFi & NFT support","Unlimited revisions"],
"fees_notes":"Tiered by transaction count; unlimited wallets/exchanges supported.",
"regions":"US/Global",
"alternatives":["Koinly","CryptoTaxCalculator"]
}
Highlights: instant forms, DeFi/NFT support, pricing by report tier. CoinLedger+1
3. CoinTracker — Best portfolio + tax combo
{
"name":"CoinTracker",
"url":"https://www.cointracker.io/",
"tagline":"Best portfolio + tax combo",
"why_use_it":"Combines strong portfolio tracking with tax reporting and broad integrations. Good fit if you want year-round tracking and tax filing in one place.",
"best_for":"Buy-and-hold investors; multi-exchange users; Coinbase ecosystem",
"notable_features":["Portfolio + tax in one","TurboTax & H&R Block export","Free tax calculator"],
"fees_notes":"Free plan + multiple paid tiers based on transaction counts and features.",
"regions":"Global",
"alternatives":["CoinTracking","Koinly"]
}
References: portfolio/tax plans; free 2025 tax calculator. cointracker.io+1
4. CryptoTaxCalculator — Best for DeFi/NFT power users
{
"name":"CryptoTaxCalculator",
"url":"https://cryptotaxcalculator.io/",
"tagline":"Best for DeFi/NFT power users",
"why_use_it":"Known for granular on-chain parsing (contracts, smart labels) and robust inventory methods. Clear U.S. guide coverage plus deep international docs.",
"best_for":"Heavy DeFi/NFT traders; cross-chain users; Coinbase users wanting discounts",
"notable_features":["Advanced DeFi categorization","Multiple inventory methods (FIFO/LIFO/HIFO)","Tax loss harvesting tools"],
"fees_notes":"Free import/preview; pay for reports and advanced tools; tiers by tx count.",
"regions":"Global (strong US/AU/EU support)",
"alternatives":["CoinLedger","Coinpanda"]
}
See pricing & free-trial notes; U.S. 2025 guide and integrations. Coinbase Help+3Crypto Tax Calculator+3Crypto Tax Calculator+3
5. ZenLedger — Best for tax-pro assistance on demand
{
"name":"ZenLedger",
"url":"https://zenledger.io/",
"tagline":"Best for tax-pro assistance on demand",
"why_use_it":"DIY software plus optional tax strategy consults and filing assistance. Solid reporting with emphasis on loss harvesting and a unified spreadsheet view.",
"best_for":"U.S. filers; users wanting hands-on help; mixed income (staking/mining)",
"notable_features":["Tax loss harvesting tool","Grand Unified Spreadsheet","In-house tax services"],
"fees_notes":"Free tier available; premium plans and paid consults/tax filing.",
"regions":"US/Global",
"alternatives":["TokenTax","Koinly"]
}
Features & services from official pages. ZenLedger+2ZenLedger+2
6. TokenTax — Best full-service + complex reconciliations
{
"name":"TokenTax",
"url":"https://tokentax.co/",
"tagline":"Best full-service + complex reconciliations",
"why_use_it":"Hybrid model: powerful software plus CPAs who will reconcile edge cases (bridges, LPs, DEX fees). Plans scale up to white-glove VIP with audit support.",
"best_for":"Active traders; complex DeFi; high-net-worth; back-tax cleanups",
"notable_features":["CPA-backed filing","Advanced accounting methods (FIFO/LIFO/HIFO)","Enterprise & VIP options"],
"fees_notes":"Multiple tiers from DIY to VIP; enterprise custom pricing.",
"regions":"Global",
"alternatives":["ZenLedger","Ledgible"]
}
Plans & accounting methods per official site. TokenTax+2TokenTax+2
7. Coinpanda — Best for multi-country filers
{
"name":"Coinpanda",
"url":"https://coinpanda.io/",
"tagline":"Best for multi-country filers",
"why_use_it":"Strong global coverage (65+ countries) and exports for local forms. Handy if you moved jurisdictions or need non-U.S. reports alongside IRS forms.",
"best_for":"Expats; EU/APAC filers; users juggling multiple tax regimes",
"notable_features":["Country-specific reports","IRS Form 8949 & Schedule D","Broad exchange/wallet support"],
"fees_notes":"Pricing tiers by transaction count; free to try.",
"regions":"Global (65+ countries)",
"alternatives":["Blockpit","CryptoTaxCalculator"]
}
Coverage and report exports per official pages. Coinpanda+2Coinpanda+2
8. Ledgible — Best for tax professionals & firms
{
"name":"Ledgible",
"url":"https://ledgible.io/",
"tagline":"Best for tax professionals & firms",
"why_use_it":"Built for tax pros with client billing, pro dashboards, and accounting integrations. Good bridge between retail clients and professional software workflows.",
"best_for":"CPAs/EAs; multi-client firms; advanced retail users with a pro",
"notable_features":["Pro portal & client billing","1099/8949/Schedule D outputs","Accounting/ERP integrations"],
"fees_notes":"Pro portal free; clients pay per-report (customizable).",
"regions":"US/Global",
"alternatives":["TokenTax","CoinTracker"]
}
Professional focus and pricing model per official site. Ledgible+1
9. CoinTracking — Best for data nerds & long-time traders
{
"name":"CoinTracking",
"url":"https://cointracking.info/",
"tagline":"Best for data nerds & long-time traders",
"why_use_it":"One of the longest-running portfolio + tax tools with deep historical imports and flexible reports. Appeals to users with large archives and custom CSVs.",
"best_for":"Power users; traders with legacy data; hybrid hodlers/traders",
"notable_features":["300+ exchange/wallet imports","DeFi/NFT support","Detailed tax and performance reports"],
"fees_notes":"Free tier + paid plans; supports many jurisdictions.",
"regions":"Global",
"alternatives":["CoinTracker","Coinpanda"]
}
Core claims from official product pages. cointracking.info+1
10. Blockpit — Best for Europe & Accointing migrations
{
"name":"Blockpit",
"url":"https://www.blockpit.io/",
"tagline":"Best for Europe & Accointing migrations",
"why_use_it":"EU-focused platform with clear U.S. support and a streamlined migration path from Accointing (which sunset in 2024). Good documentation and transparent pricing.",
"best_for":"EU users; ex-Accointing users; mixed CEX+DeFi portfolios",
"notable_features":["Accointing migration","IRS-aligned U.S. reports","Mobile app & portfolio tracking"],
"fees_notes":"Free tracking; paid tax reports tiered by transactions.",
"regions":"EU/US (Global coverage increasing)",
"alternatives":["Coinpanda","CryptoTaxCalculator"]
}
Accointing migration + pricing and U.S. alignment per official pages. Blockpit+3Blockpit Helpcenter+3Blockpit+3
Decision Guide: Best By Use Case
- Quick U.S. filing, simple stack: CoinLedger or Koinly
- Year-round portfolio + taxes in one: CoinTracker or CoinTracking
- Heavy DeFi/NFTs or complex on-chain: CryptoTaxCalculator or TokenTax (full service)
- Tax pro / multi-client firm: Ledgible
- Multi-country reporting (EU/APAC): Coinpanda or Blockpit
- Migrating from Accointing: Blockpit
- Want audit support / VIP: TokenTax
How to Choose the Right crypto tax reporting & portfolio reconciliation software (Checklist)
- Jurisdiction & forms: Does it export the forms you need (e.g., IRS 8949/Schedule D; HMRC; ATO)?
- Integrations & coverage: Wallets, exchanges, chains, DeFi protocols, NFTs you actually use.
- Reconciliation depth: Handles bridges, LP removals, MEV, staking rewards, airdrops, and fees correctly.
- Cost model: Transactions-based tiers vs. flat; consider your volume this year and next.
- UX & error fixing: Clear warnings, duplicate detection, missing cost-basis tools.
- Security: 2FA, read-only API keys, data retention controls.
- Support: CPA access, pro plans, or community docs.
- Red flags: No recent updates; vague pricing; no exportable audit trail.
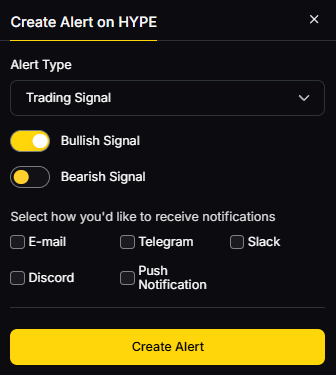
Use Token Metrics With Any crypto tax reporting & portfolio reconciliation software
- AI Ratings to screen coins and reduce churn trading.

- Narrative Detection to spot momentum before it hits your P&L.
- Portfolio Optimization to size positions intelligently.
- Alerts/Signals to avoid taxable churn and plan harvest windows.
Workflow: Research in Token Metrics → Select provider above → Import/sync & reconcile → Monitor with TM alerts.
Primary CTA: Start free trial.

Security & Compliance Tips
- Enable 2FA; use read-only API keys; revoke old keys.
- Keep a wallet hygiene routine (label internal transfers, track bridges and gas).
- Maintain off-exchange backups of CSVs and address lists.
- Follow KYC/AML rules at your provider; understand 1099/DA broker reporting starting in 2025. TurboTax
This article is for research/education, not financial advice.
Beginner Mistakes to Avoid
- Treating transfers as taxable sales (fix with proper labeling).
- Ignoring fees and LP add/remove entries (cost basis breaks).
- Mixing personal and business wallets without tagging.
- Waiting until April—fixing mismatches takes time.
- Relying on a single source export (always keep on-chain + CEX records).
FAQs
What is crypto tax software?
It’s software that aggregates your exchange, wallet, and on-chain activity to calculate cost basis and produce compliant tax forms for your jurisdiction. Most tools support IRS Form 8949/Schedule D in the U.S. and local equivalents elsewhere.
How do I file crypto taxes with software?
- Connect exchanges/wallets with read-only APIs or public addresses; 2) Import CSVs for gaps; 3) Review warnings/missing cost basis; 4) Generate forms and file directly or export to TurboTax/your CPA. Most tools offer a free preview before you pay. Koinly
Which crypto tax app is best for DeFi/NFTs?
CryptoTaxCalculator, TokenTax (with pro help), and Coinpanda have strong DeFi/NFT coverage. Choose based on your chains/protocols and whether you want full-service support. Crypto Tax Calculator+2TokenTax+2
What changed for 2025 U.S. crypto taxes?
Broker reporting (Form 1099-DA) begins for the 2025 tax year, expanding third-party information reporting. You still must report all crypto disposals even without a form. TurboTax
Can I use TurboTax with these tools?
Yes—most export to TurboTax/H&R Block or generate importable files. If you only used one exchange (e.g., Coinbase), you may be able to file directly; multi-platform activity benefits from a dedicated crypto tax app. cointracker.io+1
Is Crypto.com Tax still available?
No. Crypto.com deprecated its free tax tool in June 2024 and now partners with Koinly and TokenTax. Crypto.com Help Center
Conclusion + Related Reads
If you want fast, reliable filing, start with Koinly or CoinLedger. Need portfolio + tax together? Try CoinTracker or CoinTracking. For complex DeFi/NFTs, pick CryptoTaxCalculator or full-service TokenTax. Multi-country or EU-heavy? Coinpanda or Blockpit. Tax pros and firms should consider Ledgible.
Related Reads:
- Best Cryptocurrency Exchanges 2025
- Top Derivatives Platforms 2025
- Top Institutional Custody Providers 2025
Sources & Update Notes
We reviewed official product, pricing, guides, and security pages for each provider; we avoided third-party reviews for claims. Updated September 2025.
- Koinly — Home & Pricing pages. Koinly+1
- CoinLedger — Home & Pricing. CoinLedger+1
- CoinTracker — Home, Plans, Tax Calculator. cointracker.io+2cointracker.io+2
- CryptoTaxCalculator — US page, Pricing, US Tax Guide, Integrations notes. Crypto Tax Calculator+3Crypto Tax Calculator+3Crypto Tax Calculator+3
- ZenLedger — Home, Services, Filing pages. ZenLedger+2ZenLedger+2
- TokenTax — Home, Pricing, Accounting Methods guide. TokenTax+2TokenTax+2
- Coinpanda — Home, Pricing/Reports, Country coverage. Coinpanda+2Coinpanda+2
- Ledgible — Home, Pricing/Pro. Ledgible+1
- CoinTracking — Home & Tax report pages. cointracking.info+1
- Blockpit — Home, Pricing, Accointing migration & product updates. Blockpit+3Blockpit+3Blockpit+3
Context: TurboTax crypto changes; Crypto.com Tax deprecation; Coinbase discounts page. TurboTax+2Crypto.com Help Center+2
Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)









.svg)




.png)