Best Retail Crypto Wallets (Mobile/Web) 2025

Why Retail Crypto Wallets (Mobile/Web) Matter in September 2025
Retail-friendly mobile and web wallets make crypto usable—on your phone and in your browser—without relying on a centralized custodian. This guide ranks the best retail crypto wallets for 2025 so you can safely store, send, swap, and explore Web3. A crypto wallet is software that holds your keys and lets you sign transactions; self-custody means you control those keys.
We focus on practical needs: everyday buys, swaps, NFT viewing, multi-chain coverage, and clear fees. Expect mainstream names alongside rising multichain players. Secondary considerations include mobile crypto wallet UX, web3 wallet dapp access, and self-custody wallet security. If you’re new, start with a wallet that offers simple onboarding and robust recovery. If you’re advanced, look for pre-transaction risk checks, multichain swaps, and hardware support.
How We Picked (Methodology & Scoring)
- Liquidity (30%) – depth and routing quality for in-wallet swaps/bridging; reliable asset movement.
- Security (25%) – self-custody design, audits, MPC/multisig options, hardware compatibility, recovery.
- Coverage (15%) – number of supported chains/tokens and NFT handling.
- Costs (15%) – transparent swap/bridge fees and gas handling.
- UX (10%) – onboarding, performance, transaction clarity, portfolio/NFT views.
- Support (5%) – docs, help centers, in-app support channels.
Sources: official product/docs pages, security/transparency pages, and (for cross-checks only) reputable market datasets. Last updated: September 2025.
Top 10 Retail Crypto Wallets (Mobile/Web) in September 2025
1. MetaMask — Best for EVM & massive dapp coverage
Why Use It: The most ubiquitous Web3 wallet, MetaMask balances power and familiarity. It’s everywhere dapps are, with mobile + browser extension, good network support, and strong swap/bridge routing in-app. Smart Transactions and built-in security alerts improve reliability for everyday users. MetaMask
Best For: EVM users, NFT collectors, L2 explorers, DeFi regulars.
Notable Features: Smart Transactions; Swaps/Bridge aggregator; MetaMask Learn; mobile + major browsers. MetaMask+1
Consider If: You want explicit fee transparency—MetaMask Swaps includes a 0.875% service fee (plus network gas). MetaMask Help Center
Alternatives: Trust Wallet, OKX Wallet.
Regions: Global.
Fees Notes: Network fees; MetaMask Swaps service fee 0.875%. MetaMask Help Center
2. Trust Wallet — Best all-rounder for mobile + extension
Why Use It: Trust Wallet offers a simple, one-stop experience: buy, send, swap, stake, and manage NFTs across many chains. Its mobile app is fast, and the extension integrates with popular EVM and non-EVM chains. Trust Wallet+1
Best For: Beginners who want breadth; multichain NFT holders; mobile-first users.
Notable Features: Built-in DApp browser; simplified swaps with gas optimization; staking flows. Trust Wallet
Consider If: You want no added swap fee—Trust says it doesn’t charge extra on swaps (you still pay network/third-party fees). Trust Wallet
Alternatives: MetaMask, Crypto.com Onchain.
Regions: Global.
Fees Notes: Network/partner fees apply; Trust states no added in-app swap fee. Trust Wallet
3. Base app (formerly Coinbase Wallet) — Best for Coinbase ecosystem & onchain social
Why Use It: Rebranded as the Base app, the former Coinbase Wallet keeps familiar self-custody features while embracing Base/L2 culture and onchain social/activity. If you already use Coinbase products, onboarding is straightforward while staying self-custodial. Coinbase
Best For: Coinbase users going self-custody; Base/L2 explorers; web3 social/NFT dabblers.
Notable Features: Self-custody; trading, posting, playing; continuity for Coinbase Wallet users. Coinbase
Consider If: You prefer chain-agnostic advanced tooling—others may offer deeper multichain utilities today.
Alternatives: MetaMask, Rainbow.
Regions: Global.
Fees Notes: Network fees; third-party swap/partner fees where used. Coinbase
4. Phantom — Best for Solana + solid multichain UX
Why Use It: Phantom started Solana-first and has grown into a polished multichain wallet (Solana, Ethereum, and more). The interface is clean, with strong NFT views and transaction clarity—great for newcomers to Solana and cross-chain dabblers. Phantom+1
Best For: Solana users, NFT traders, multichain retail.
Notable Features: In-wallet swaps and bridging; gasless swaps on Solana (select cases); robust notifications/history. Phantom Support+1
Consider If: You want the lowest possible swap fees—Phantom lists 0.85% on select pairs, with separate gas/bridge fees. Phantom Support
Alternatives: OKX Wallet, Trust Wallet.
Regions: Global.
Fees Notes: Network fees; Phantom fee 0.85% on select swaps; gasless-swap fee rules apply on Solana. Phantom Support+1
5. OKX Wallet — Best for power users who want DEX depth
Why Use It: OKX Wallet (extension + mobile) plugs you into OKX’s DEX aggregator, NFT marketplace, and DeFi. It offers multiple swap modes and solid routing—useful when chasing best execution across chains. OKX Wallet+1
Best For: DeFi users seeking liquidity routing; cross-chain swappers; NFT traders.
Notable Features: Multi-mode swaps; DEX aggregator; marketplace; Earn/Discover sections. OKX Wallet
Consider If: You need crystal-clear fee schedules—OKX lists DEX interface fee tiers up to 0.85% depending on pair groups. OKX Wallet
Alternatives: MetaMask, Bitget Wallet.
Regions: Global (wallet).
Fees Notes: Network fees; OKX DEX interface fee 0–0.85% by pair category. OKX Wallet
6. Exodus — Best for design & easy portfolio views
Why Use It: Exodus is a long-standing, self-custodial wallet with a beautifully designed UI across desktop and mobile. Portfolio tracking and NFT galleries are polished, and its Web3 Wallet extends multichain support. Exodus
Best For: Newcomers who want clarity; portfolio-first users; multi-device use.
Notable Features: Multichain Web3 Wallet; thousands of swap pairs; simple buy/sell integrations. Exodus
Consider If: You want explicit fee details—Exodus doesn’t charge send/receive wallet fees, but network and partner fees still apply. Exodus Knowledge Base
Alternatives: Crypto.com Onchain, ZenGo.
Regions: Global.
Fees Notes: No Exodus send/receive fees; network fees + third-party swap/fiat fees may apply. Exodus Knowledge Base
7. Crypto.com Onchain — Best for simple multichain + Crypto.com tie-ins
Why Use It: Formerly known as the DeFi Wallet experience, Crypto.com Onchain is a self-custodial app with multichain support, in-wallet trading, and dapp access. It’s friendly for users who like Crypto.com’s ecosystem but want self-custody keys. Crypto.com
Best For: Mobile-first users; staking/earn explorers; Crypto.com ecosystem fans.
Notable Features: Local key encryption; import via 12/18/24-word phrases; multichain trading & dapp browser. Crypto.com
Consider If: You prefer a purely chain-agnostic wallet without exchange brand ties—others may feel “lighter.”
Alternatives: Trust Wallet, Exodus.
Regions: Global (feature availability can vary).
Fees Notes: Network/partner fees; self-custody (no custodial withdrawal fees). Crypto.com
8. ZenGo — Best for seed-phrase-free MPC security
Why Use It: ZenGo uses MPC to remove single-point seed phrase risks while keeping you in self-custody. That makes setup and recovery less nerve-wracking for new users, without buying hardware. Zengo+1
Best For: Beginners prioritizing recovery; mobile-only users; security-conscious travelers.
Notable Features: Seed-phrase-free MPC; in-app buy/swap; staking for select assets. Zengo+1
Consider If: You want classic seed control or advanced on-chain tooling—some power features are simpler by design.
Alternatives: Ledger Live (with hardware), Trust Wallet.
Regions: Global.
Fees Notes: Network fees; partner fees for buy/swap as quoted in-app. Zengo
9. Bitget Wallet — Best for active swappers & airdrop hunters
Why Use It: Formerly BitKeep, Bitget Wallet has grown into a large multichain wallet with DEX aggregation, dapp discovery, and memecoin-friendly flows. It’s geared for on-chain traders who want routing and token coverage across 65+ chains. Bitget Wallet+1
Best For: Power users in DeFi; memecoin and airdrop participants; cross-chain swaps.
Notable Features: Multichain DEX aggregator; dapp hub; iOS/Android + Chrome extension. Bitget Wallet
Consider If: You prefer a simpler, beginner-first interface—others above are more hand-holding.
Alternatives: OKX Wallet, MetaMask.
Regions: Global.
Fees Notes: Network fees; interface/partner fees vary by route/pair. Bitget Wallet
10. Ledger Live — Best for hardware-backed mobile/desktop security
Why Use It: Ledger Live is the companion app to Ledger hardware wallets; it brings buy, swap, stake, and portfolio monitoring into a single interface while private keys stay in the hardware device. Great for retail users who want a mobile/desktop app but insist on offline signing. Ledger
Best For: Long-term holders; high-value accounts; users planning to add hardware.
Notable Features: Buy/sell/swap/stake modules; multi-asset support; iOS/Android + desktop. Google Play+1
Consider If: You don’t own hardware—full security benefits require a Ledger device.
Alternatives: ZenGo (MPC), Trezor Suite (with hardware).
Regions: Global.
Fees Notes: Network fees; partner fees for buy/swap as quoted in-app. Ledger
Decision Guide: Best By Use Case
- Regulated U.S. on-ramp familiarity: Base app (formerly Coinbase Wallet)
- Global multichain coverage + liquidity routing: OKX Wallet, Bitget Wallet
- Solana-first with smooth UX: Phantom
- EVM & dapp coverage: MetaMask
- Mobile simplicity (no seed phrase): ZenGo
- Polished design & portfolio tracking: Exodus
- Exchange-brand ecosystem, self-custody keys: Crypto.com Onchain
- Hardware-secured flows: Ledger Live
- Beginner-friendly all-rounder: Trust Wallet
How to Choose the Right Retail Crypto Wallet (Checklist)
- Confirm eligibility/availability in your region and app store.
- Verify chain coverage (BTC + your primary L1s/L2s).
- Decide on custody model: classic seed, MPC (no seed), or hardware-backed.
- Review fees: swap/bridge interface fees + network gas.
- Evaluate UX: transaction previews, risk alerts, NFT view, portfolio.
- Check support: searchable help center, in-app ticketing.
- Compliance fit: consider your tax/KYC needs with on-ramps.
- Red flags: fake download pages; apps that ask you to type your seed phrase into a website or pop-up.
Use Token Metrics With Any Wallet
- AI Ratings to screen assets by quality and momentum.
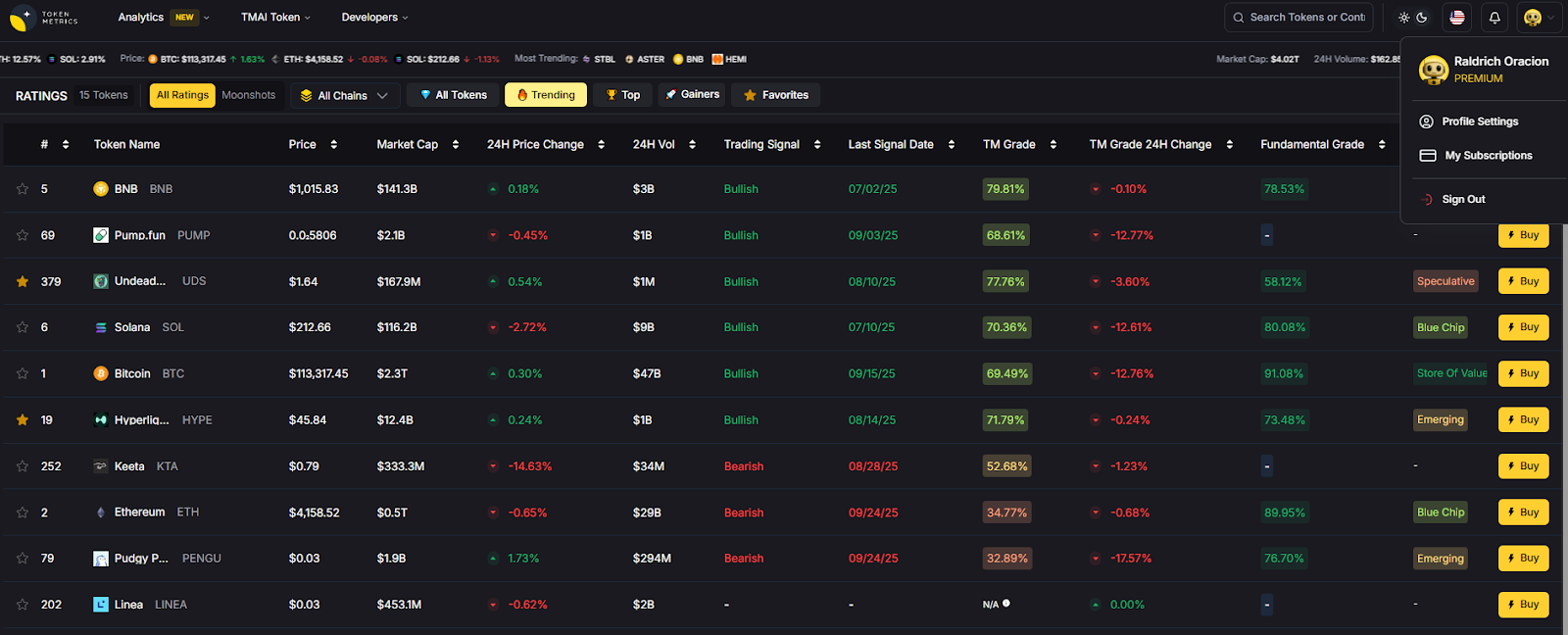
- Narrative Detection to spot early theme shifts.
- Portfolio Optimization to balance risk across chains.
- Alerts & Signals to monitor entries/exits.
Workflow: Research → Select wallet → Execute on-chain → Monitor with alerts.\

Primary CTA: Start free trial

Security & Compliance Tips
- Enable biometrics + 2FA (where available) and set a strong passcode.
- Back up recovery materials: seed phrase metal card, or MPC recovery kits.
- Prefer hardware signing for larger balances.
- Use transaction previews and simulation/risk checks before signing.
- Keep software updated; download only from official sites/app stores.
This article is for research/education, not financial advice.
Beginner Mistakes to Avoid
- Saving seed phrases in cloud notes/screenshots.
- Sending coins to the wrong chain or address format.
- Ignoring fee settings or slippage in swaps.
- Approving unlimited token allowances without review.
- Falling for phishing domains and fake extensions.
FAQs
What is a retail crypto wallet (mobile/web)?
A mobile/web retail wallet is software that stores your private keys and lets you sign transactions from your phone or browser. Most are self-custodial, meaning you—not an exchange—control your keys.
Is a self-custody wallet safer than keeping coins on an exchange?
Self-custody removes exchange counterparty risk. However, you must protect recovery methods (seed phrase, MPC recovery) and your device. Hardware or MPC-based options can add protection.
Which wallet is best for beginners?
For simplicity: Trust Wallet, Exodus, or ZenGo. They have straightforward onboarding, clear portfolio views, and solid docs. Advanced users might prefer MetaMask, Phantom, or OKX Wallet for deeper on-chain tooling. OKX Wallet+5Trust Wallet+5Exodus+5
What fees should I expect?
You’ll always pay network gas. Some wallets add interface/service fees on swaps/bridges (e.g., MetaMask 0.875%; Phantom 0.85% on select pairs; OKX DEX 0–0.85% depending on token groups). MetaMask Help Center+2Phantom Support+2
Do I need hardware for mobile/web wallets?
No. Many work fine without hardware. For higher balances, pairing a mobile/web app with a hardware wallet (e.g., via Ledger Live) can reduce signing risk. Ledger
Can I use one wallet across multiple chains?
Yes—most featured wallets are multichain. Check chain lists and NFT support before migrating. OKX Wallet+2Bitget Wallet+2
Conclusion + Related Reads
If you want maximum dapp coverage, go MetaMask; Solana-centric with great UX, pick Phantom; for exchange-adjacent simplicity, choose Base app or Crypto.com Onchain; for hardware-backed security, Ledger Live. Power users chasing routing and airdrops may prefer OKX Wallet or Bitget Wallet, while newcomers should consider Trust Wallet, Exodus, or ZenGo.
Related Reads:
- Best Cryptocurrency Exchanges 2025
- Top Derivatives Platforms 2025
- Top Institutional Custody Providers 2025
Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)








.svg)




.png)