How to Create a Crypto Wallet: A Complete Beginner’s Guide (2025)
.png)
As the popularity of cryptocurrencies continues to grow in 2025, more people are seeking safe and secure ways to manage their digital assets. The first step in your crypto journey? Creating a crypto wallet.
In this guide, we’ll explain:
- What a crypto wallet is
- Different types of wallets
- How to create one (step-by-step)
- Tips for securing your wallet
- How Token Metrics can help you trade smarter after setup
🪙 What Is a Crypto Wallet?
A crypto wallet is a digital tool that allows you to store, receive, and send cryptocurrencies like Bitcoin, Ethereum, and thousands of altcoins. Instead of holding physical money, it stores your private and public keys, giving you access to your blockchain assets.
Two Major Types:
- Hot Wallets – connected to the internet (ideal for active users)
- Cold Wallets – offline and more secure (ideal for long-term storage)
Whether you're buying Bitcoin for the first time or diving into DeFi tokens, you'll need a crypto wallet to safely store and manage your coins.
🔥 Hot Wallets vs. 🧊 Cold Wallets
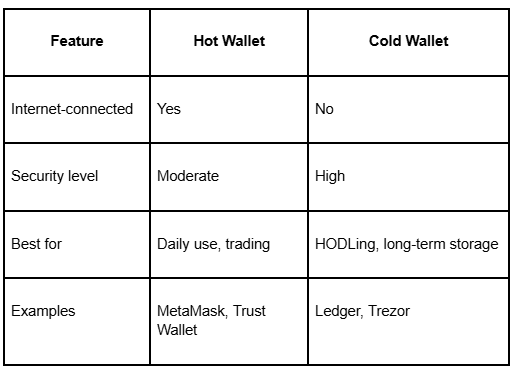
Hot wallets are easier to set up and use, while cold wallets offer greater protection against hacks and malware.
🛠️ How to Create a Crypto Wallet (Step-by-Step)
Option 1: Creating a Hot Wallet (e.g., MetaMask or Trust Wallet)
Step 1: Download the App or Browser Extension
- Visit the official MetaMask website or your mobile app store.
- Install the extension or app.
Step 2: Create a New Wallet
- Click “Create a Wallet”
- Set a strong password
Step 3: Backup Your Recovery Phrase
- Write down the 12 or 24-word seed phrase
- Store it offline (NOT on your phone or computer)
Step 4: Confirm Your Recovery Phrase
- MetaMask will ask you to re-enter it to ensure it's saved correctly
Step 5: Wallet is Ready
- You can now receive, send, and store ETH, ERC-20 tokens, and NFTs
✅ Pro Tip: Connect your wallet to Token Metrics to explore trading signals, moonshots, and AI analytics directly.
Option 2: Creating a Cold Wallet (e.g., Ledger Nano X)
Step 1: Buy a Ledger or Trezor device
- Always order from the official website to avoid tampered devices
Step 2: Install Wallet Software
- Download Ledger Live or Trezor Suite
Step 3: Set Up Device and PIN
- Follow the on-screen instructions
- Create a secure PIN code
Step 4: Write Down Your Recovery Phrase
- The device will show a 24-word seed phrase
- Write it down and store it in a fireproof safe
Step 5: Start Receiving Crypto
- Use Ledger Live or Trezor Suite to generate wallet addresses
- Send crypto from exchanges or other wallets
✅ Pro Tip: Use your cold wallet to store moonshots and long-term assets, then analyze performance using Token Metrics Portfolio tools.
🛡️ Tips for Securing Your Crypto Wallet
- Never share your seed phrase
Anyone with your seed phrase can steal your funds - Enable Two-Factor Authentication (2FA)
For added protection on wallet apps and exchange accounts - Use a strong, unique password
Avoid reusing passwords across multiple accounts - Avoid phishing sites
Always double-check URLs before connecting your wallet - Keep backups offline
Use metal seed plates or paper stored in multiple safe locations
🔎 How Token Metrics Supports Your Wallet Journey
While Token Metrics doesn't create wallets, it integrates seamlessly with your Web3 wallets to help you maximize profits and minimize risks.
1. AI-Powered Ratings
Once your wallet is set up, use Token Metrics to find top-rated tokens across risk levels, market caps, and sectors.

2. Moonshots Dashboard
Explore early-stage tokens with massive upside using the Moonshots tab—only available to Premium members.
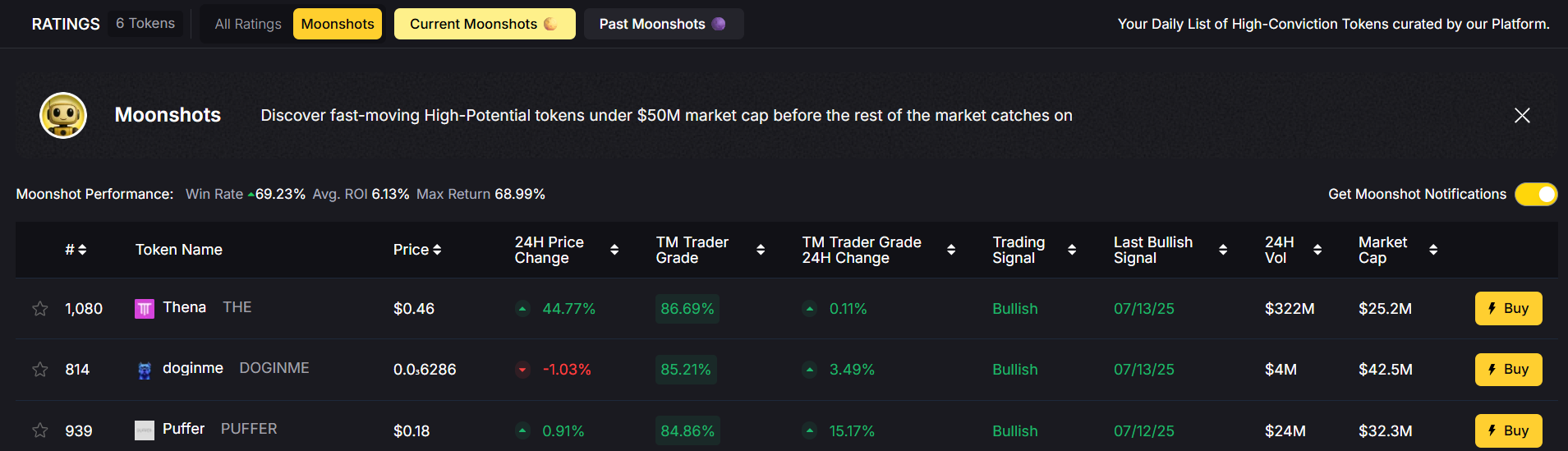
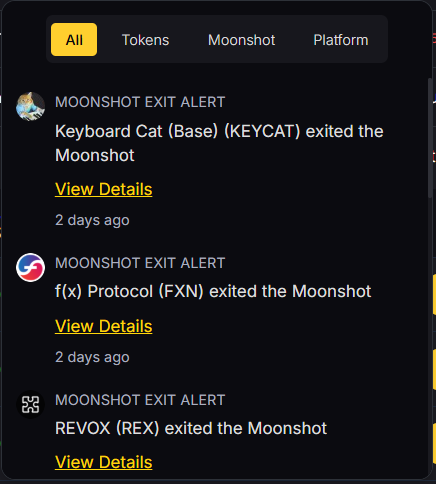
3. Real-Time Alerts
Set up alerts for price, investor grade, or bullish/bearish signals—and receive them directly to your connected wallet’s contact info.
4. Track Your Portfolio
Monitor wallet performance across tokens with a real-time dashboard powered by on-chain data.
📦 What Can You Store in Your Crypto Wallet?
- Bitcoin (BTC)
- Ethereum (ETH) and ERC-20 tokens
- DeFi tokens like UNI, AAVE, LINK
- NFTs like digital art or game assets
- Stablecoins like USDT, USDC, DAI
- Moonshots found on Token Metrics
Different wallets support different blockchains, so always check compatibility before sending assets.
📲 Best Wallets to Use in 2025
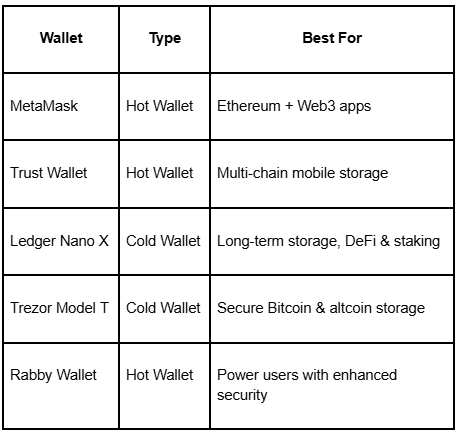
🔄 Wallet Creation FAQs
Q: Is creating a crypto wallet free?
Yes, most wallet apps like MetaMask or Trust Wallet are free.
Q: Can I create multiple wallets?
Absolutely. Many investors use different wallets for different purposes (e.g., trading, staking, savings).
Q: What happens if I lose my recovery phrase?
You lose access to your wallet permanently. Always store it securely.
Q: Do I need a wallet to use Token Metrics?
No, but connecting a wallet enhances your experience by allowing you to monitor portfolios, moonshots, and alerts in real time.
🧠 Final Thoughts
Creating a crypto wallet is your gateway to the decentralized world of digital finance. Whether you’re a seasoned trader or a beginner buying your first token, having a secure wallet is non-negotiable.
By choosing the right wallet (hot or cold), securing your keys, and combining it with powerful tools like Token Metrics, you can build a smart, secure, and profitable crypto journey.
Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)







.svg)




.png)