Top Education Platforms & Courses for Crypto (2025)

Why Crypto education platforms & courses Matter in September 2025
Crypto moves fast—and the gap between hype and real skills can be costly. If you’re evaluating the best crypto courses or structured paths to go from zero to fluent (or from power user to builder), the right program can compress months of trial-and-error into weeks. In short: a crypto education platform is any structured program, course catalog, or academy that teaches blockchain, Web3, or digital-asset topics with clear outcomes (e.g., literacy, developer skills, startup readiness).
This guide curates 10 credible options across beginner literacy, smart-contract engineering, and founder tracks. We blend SERP research with hands-on criteria so you can match a course to your goals, time, and budget—without the fluff.
How We Picked (Methodology & Scoring)
- Curriculum depth & rigor (30%): Syllabi clarity, assessments, capstones, recognized instructors.
- Credibility & security posture (25%): Transparent teams, reputable institutions, security topics baked in.
- Coverage & specialization (15%): Breadth (BTC, ETH, DeFi, NFTs, security) plus specialist tracks (Solidity, oracles, ZK).
- Costs & access (15%): Free tiers, scholarships, value per hour, certificates.
- UX & learning experience (10%): In-browser coding, cohort support, community, multilingual content.
- Support & outcomes (5%): Mentorship, career support, community reach.
Data sources: official provider pages (program docs, security/FAQ, curriculum), plus widely cited market datasets for cross-checks only. Last updated September 2025.
Top 10 Crypto education platforms & courses in September 2025
1. Coursera — “Bitcoin and Cryptocurrency Technologies” (Princeton) — Best for academic foundations
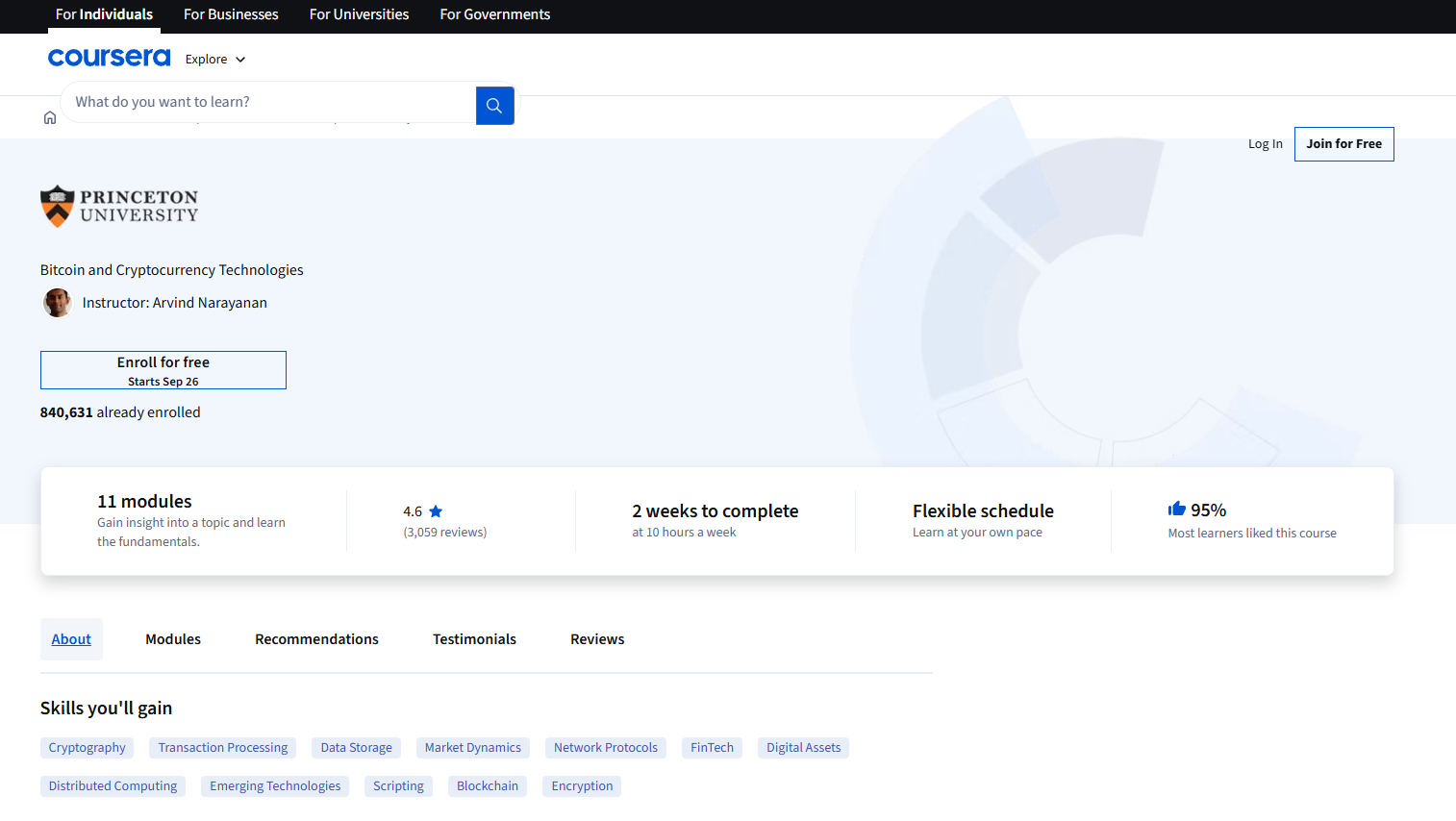
- Why Use It: A seminal university course that demystifies Bitcoin and core crypto concepts with a rigorous, vendor-neutral lens. Clear lectures and assessments make it ideal for newcomers who want trustworthy fundamentals. Coursera
- Best For: Beginners, product managers, compliance/finance pros, technical leaders needing conceptual grounding.
- Notable Features: University-backed syllabus; security/anonymity modules; future/regulation perspectives; conceptual foundations for building. Princeton Online
- Consider If: You prefer hands-on Solidity right away—this is theory-first.
- Alternatives: edX (Berkeley), Coinbase Learn.
- Regions: Global. Fees Notes: Coursera pricing varies by locale.
2. edX — Berkeley Blockchain Fundamentals — Best for university-brand plus survey depth
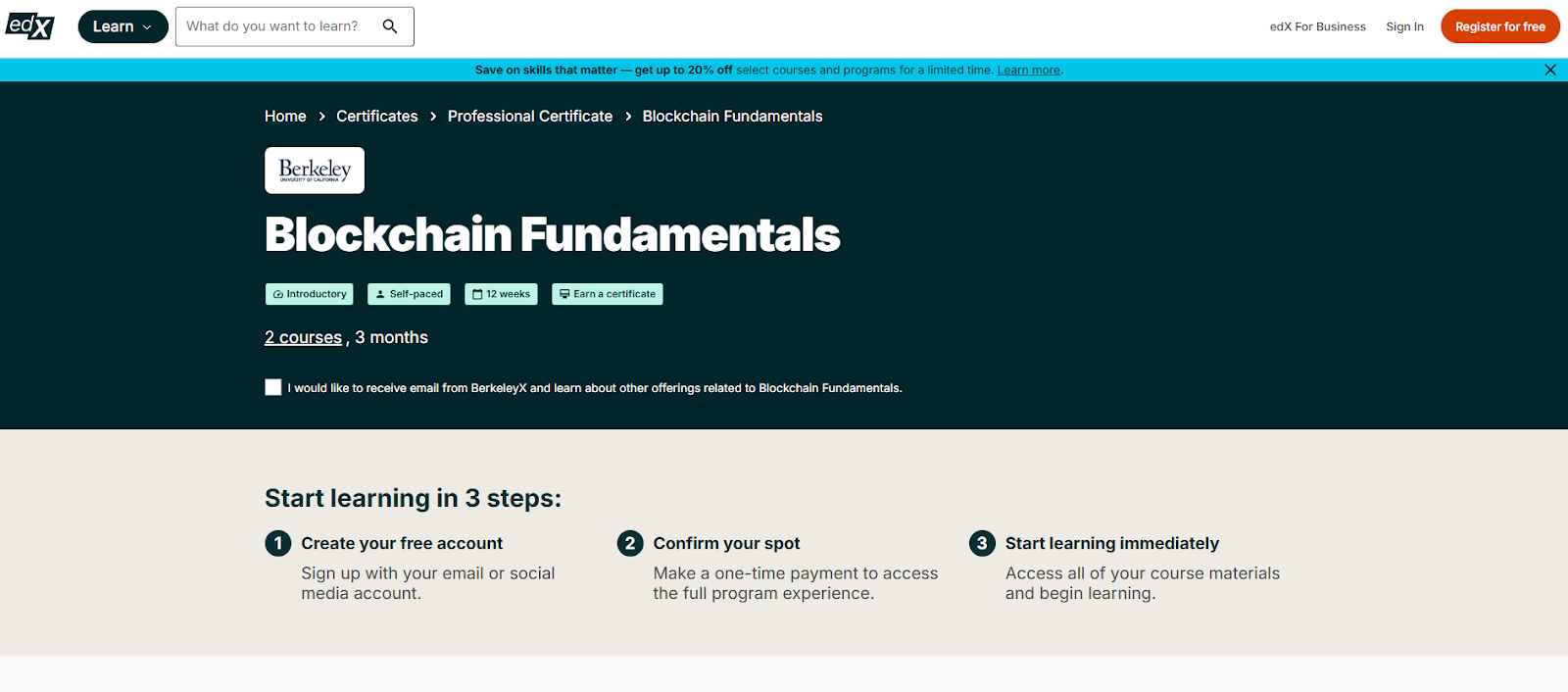
- Why Use It: UC Berkeley’s professional certificate pairs an overview of blockchain and crypto with academic rigor and clear learning paths. Good bridge between literacy and technical depth. edX+1
- Best For: Cross-functional teams, MBA/finance learners, policy/ops, curious devs.
- Notable Features: Recognized university credential; modular courses; wide topical span across Bitcoin, Ethereum, and applications. edX
- Consider If: You need coding-heavy, cohort-based Solidity training now.
- Alternatives: Coursera (Princeton), ConsenSys Academy.
- Regions: Global. Fees Notes: edX offers audit (free) and paid certificate tracks. edX
3. Binance Academy — Best free, multilingual crypto literacy hub
- Why Use It: A large, constantly updated library of beginner-to-intermediate guides, glossaries, and tutorials in many languages—100% free. Binance+1
- Best For: Absolute beginners, non-technical teams, multilingual audiences, fast refreshers.
- Notable Features: Courses + articles + videos; Bitcoin halving hubs; multi-language support; bite-size explainers. Binance
- Consider If: You want a formal certificate or university grade.
- Alternatives: Coinbase Learn, edX.
- Regions: Global. Fees Notes: Free.
4. Coinbase Learn — Best for simple, trusted onboarding
- Why Use It: Friendly entry point with practical “how-to” guides that answer common questions about Bitcoin, Ethereum, NFTs, wallets, and safety. Great for reluctant first-timers. Coinbase+1
- Best For: New investors, finance teams exploring crypto policy, busy executives.
- Notable Features: Step-by-step tutorials; beginner hubs; platform-agnostic primers. Coinbase
- Consider If: You need dev-level skills or a cohort experience.
- Alternatives: Binance Academy, Coursera.
- Regions: Global. Fees Notes: Free learning content.
5. ConsenSys Academy — Best for Ethereum developer bootcamps
- Why Use It: The training arm of a core Ethereum company, with cohort-based programs, mentor access, and security best practices baked in. Strong for professionalizing Solidity skills. Consensys - The Ethereum Company+1
- Best For: Software engineers, Web2 devs crossing to Web3, career switchers.
- Notable Features: Flagship Blockchain Developer Bootcamp; team projects; office hours; certificates. Consensys - The Ethereum Company
- Consider If: You need completely free self-paced content.
- Alternatives: Alchemy University, Moralis Academy.
- Regions: Global (online). Fees Notes: Paid bootcamps; prices vary. Consensys - The Ethereum Company
6. Alchemy University — Best free, hands-on Solidity path
- Why Use It: A popular builder track with free in-browser coding, projects, and a modern Solidity course aligned to current compiler versions. Alchemy+1
- Best For: Aspiring smart-contract devs, hackathon teams, self-paced builders.
- Notable Features: Free Solidity course; code-along projects; hackathons; JS + Ethereum tracks. Alchemy
- Consider If: You want a cohort and instructor mentorship.
- Alternatives: ConsenSys Academy, Encode Club.
- Regions: Global. Fees Notes: Free.
7. Moralis Academy — Best for blended dev + trading curriculum
- Why Use It: Combines structured dev courses with trading strategy content and a community. Offers free starts with optional Pro for deeper tracks. academy.moralis.io
- Best For: Builders who also want market context; ambitious beginners.
- Notable Features: Step-by-step tracks; community; trading modules; ties to Moralis dev tooling. Moralis | Enterprise-Grade Web3 APIs
- Consider If: You prefer purely academic or vendor-neutral content.
- Alternatives: Alchemy University, Binance Academy.
- Regions: Global. Fees Notes: Free tier; paid plans available. academy.moralis.io
8. University of Nicosia (UNIC) — Free MOOCs + MSc in Blockchain/Digital Currency — Best for formal academia & credentials
- Why Use It: UNIC pioneered a dedicated MSc in Digital Currency and runs free entry MOOCs—a long-standing academic pathway in crypto. University of Nicosia+1
- Best For: Career-switchers wanting formal credentials; policymakers; educators.
- Notable Features: Free MOOC intros; postgraduate degrees; broad coverage across tech, economic, and legal aspects. University of Nicosia
- Consider If: You need short, purely practical dev sprints.
- Alternatives: edX (Berkeley), Coursera.
- Regions: Global (online). Fees Notes: MOOCs free; degree programs paid. University of Nicosia
9. Chainlink Education & Bootcamps — Best for oracle, data, and hybrid smart-contract skills
- Why Use It: If you’re building with real-world data, Chainlink’s education hub and instructor-led bootcamps teach oracle patterns, cross-chain messaging, and production-grade smart contracts. Chainlink+1
- Best For: Devs targeting DeFi, on-chain finance, and data-rich dApps.
- Notable Features: Tutorials on NFTs/stablecoins; live bootcamps; developer advocates; ecosystem resources. chainlinkecosystem.com
- Consider If: You want chain-agnostic theory without vendor context.
- Alternatives: Alchemy University, ConsenSys Academy.
- Regions: Global. Fees Notes: Many resources free; bootcamp formats vary.
10. a16z Crypto — Crypto Startup Accelerator (CSX) — Best for founders & operators
- Why Use It: Beyond coding, founders need go-to-market, legal, and product mentorship. CSX offers a cohort model with capital, expert lectures, and crypto-specific startup support. a16z crypto
- Best For: Early-stage founders, PMs, operators validating product-market fit in Web3.
- Notable Features: Curated mentorship network; structured curriculum; demo days; evolution of the original Crypto Startup School into a full accelerator. a16z crypto
- Consider If: You’re pre-idea or not building a company yet—start with literacy/dev courses first.
- Alternatives: Encode Club accelerators, Solana-ecosystem programs.
- Regions: Global (programs periodically in specific cities). Fees Notes: Accelerator terms vary by cohort.
Decision Guide: Best By Use Case
- Academic fundamentals (theory-first): Coursera (Princeton), edX (Berkeley). Coursera+1
- Free multilingual literacy: Binance Academy; Coinbase Learn (simple, practical). Binance+1
- Hands-on Solidity (free): Alchemy University. Alchemy
- Cohort dev bootcamp: ConsenSys Academy. Consensys - The Ethereum Company
- Developer + trading blend: Moralis Academy. academy.moralis.io
- Formal credentials: University of Nicosia (MOOC, MSc). University of Nicosia
- Oracle/data-driven dApps: Chainlink Education/Bootcamps. Chainlink
- Founder/accelerator path: a16z Crypto (CSX). a16z crypto
How to Choose the Right Crypto education platforms & courses (Checklist)
- Confirm level & outcomes (literacy, dev skills, or founder playbook).
- Review syllabus & assessments; look for capstones or code reviews.
- Match specialization (Solidity, ZK, DeFi, security, oracles) to your goal.
- Check costs & time (audit/free vs. paid, cohort dates).
- Evaluate support (mentors, office hours, Discord/Forum).
- Prefer credible institutions/teams; scan FAQs/security sections.
- Red flags: vague outcomes, hard upsells, no instructor transparency.
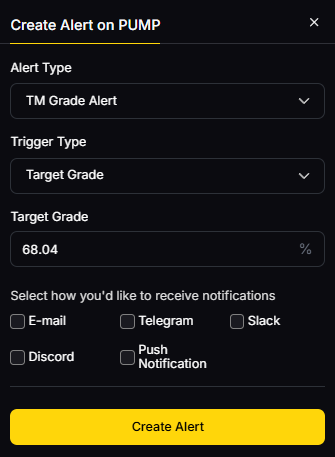
Use Token Metrics With Any Crypto education platforms & courses
- AI Ratings to screen tokens you’ll study or trade.

- Narrative Detection to spot momentum across sectors.
- Portfolio Optimization to size positions by risk.
- Alerts/Signals to monitor entries/exits as you learn.
Workflow: Research → Choose a course → Practice on sandboxes → Execute with a small wallet → Monitor with Alerts.
Primary CTA: Start free trial.

Security & Compliance Tips
- Enable 2FA and hardware keys on all learning-linked accounts.
- Keep a separate practice wallet; never paste seed phrases into course portals.
- Use reputable docs for KYC/AML topics; understand regional eligibility.
- Practice safe contract deployments on testnets first.
- Document RFQ or OTC steps if your course touches institutional flows.
This article is for research/education, not financial advice.
Beginner Mistakes to Avoid
- Jumping into paid bootcamps before trying free literacy/prep modules.
- Treating dev tutorials as plug-and-play without security reviews.
- Chasing certifications without projects to show.
- Ignoring region/eligibility notes or program timelines.
- Over-indexing on one chain—learn concepts that transfer.
FAQs
What’s the fastest way to start learning crypto in 2025?
Start with a free literacy hub (Binance Academy or Coinbase Learn), then audit a university course (Coursera/edX) before committing to a paid bootcamp. This builds intuition and saves money. Binance+2Coinbase+2
Which course is best if I want to become a Solidity developer?
Alchemy University is a free, hands-on path with in-browser coding; ConsenSys Academy adds mentor-led structure and team projects for professional polish. Alchemy+1
Do I need a formal degree for crypto careers?
Not strictly. A portfolio of projects often trumps certificates, but formal programs like UNIC’s MSc can help for policy, compliance, or academia-adjacent roles. University of Nicosia
Are these programs global and online?
Most are fully online and globally accessible; accelerators like a16z CSX may run cohorts in specific cities, so check the latest cohort details. a16z crypto
Will these courses cover wallet and security best practices?
University and dev bootcamps typically include security modules; literacy hubs also publish safety guides. Always cross-check with official docs and practice in testnets. Consensys - The Ethereum Company+1
Conclusion + Related Reads
If your goal is literacy and safe onboarding, start with Binance Academy or Coinbase Learn; for academic depth, layer in Coursera (Princeton) or edX (Berkeley). Builders should choose Alchemy University (free) and consider ConsenSys Academy for mentor-led polish. For credentials, UNIC stands out. Founders ready to ship and raise should explore a16z Crypto’s CSX.
Related Reads:
- Best Cryptocurrency Exchanges 2025
- Top Derivatives Platforms 2025
- Top Institutional Custody Providers 2025
Sources & Update Notes
We verified each provider’s official pages for curriculum, format, and access. Third-party datasets were used only to cross-check prominence. Updated September 2025.
- Coursera / Princeton — “Bitcoin and Cryptocurrency Technologies” (course page; Princeton overview). Coursera+1
- edX / UC Berkeley — “Blockchain Fundamentals” (program page & course page). edX+1
- Binance Academy — site & topic pages. Binance+1
- Coinbase Learn — Learn hub; tips & tutorials. Coinbase+1
- ConsenSys Academy — Academy overview; Bootcamp details. Consensys - The Ethereum Company+1
- Alchemy University — University overview; Solidity course page. Alchemy+1
- Moralis Academy — Academy site; Moralis developer platform. academy.moralis.io+1
- University of Nicosia — MOOC pages. University of Nicosia+1
- Chainlink — Education hub; Bootcamp page; Learn resources. Chainlink+2Chainlink+2
a16z Crypto — CSX accelerator; CSS history/update. a16z crypto+1
Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)







.svg)




.png)