What Is Cryptocurrency Market Cap? A Comprehensive Guide

Understanding the cryptocurrency market cap is fundamental for anyone interested in investing or trading digital currencies. Market capitalization, often referred to as market cap, is a key metric that reflects the total value of a cryptocurrency in the market. Cryptocurrency market capitalization represents the total value of all coins that have been mined for a specific cryptocurrency or all cryptocurrencies combined. This article will explore what cryptocurrency market cap means, how it is calculated, and why it matters for investors navigating the dynamic crypto market.
Introduction to Market Capitalization
Market capitalization represents the total value of a cryptocurrency's circulating coins in the market. It is a crucial metric used by investors and professionals to gauge the relative size and importance of a digital currency within the crypto ecosystem. Understanding market cap is essential for making informed investment decisions, as it provides a snapshot of a cryptocurrency’s size, popularity, and growth potential.
The market cap of a cryptocurrency is calculated by multiplying its current price by the number of coins in circulation. This simple formula offers insight into the cryptocurrency’s total value and helps investors compare different crypto assets effectively. By knowing the market cap, investors can better understand a cryptocurrency’s position in the market and assess its potential for future growth.
Crypto Market Cap and Circulating Supply
To fully grasp the concept of crypto market cap, it is important to understand the role of circulating supply. The circulating supply refers to the number of coins currently available and actively traded in the market. It is this supply that determines the crypto market cap when multiplied by the cryptocurrency’s current price.
Circulating supply is distinct from total supply, which includes all coins that have been created, including those not yet available for trading or locked in reserves. For example, some projects may have a large total supply but a smaller circulating supply due to tokens held by the development team or locked in smart contracts. Recognizing the difference between circulating supply and total supply is vital when evaluating a cryptocurrency’s market capitalization and its potential impact on price and growth.
Calculation and Importance
Market cap is calculated by multiplying the current price of a cryptocurrency by its circulating supply, providing a real-time measure of the asset's total value in dollars or other fiat currencies. This calculation is dynamic, as both price and circulating supply can fluctuate, causing the market cap to change rapidly.
This metric is important because it helps investors assess the size and value of a cryptocurrency relative to others in the crypto market. A higher market cap often indicates a more established and widely adopted cryptocurrency, such as Bitcoin or Ethereum, which tend to have greater network security and liquidity. Conversely, a low market cap may signal a newer or more speculative digital asset, often associated with higher risk and volatility.
Understanding market cap allows investors to make informed choices by comparing the total value of different cryptocurrencies and evaluating their potential for growth or decline.
Investment Strategies and Market Trends
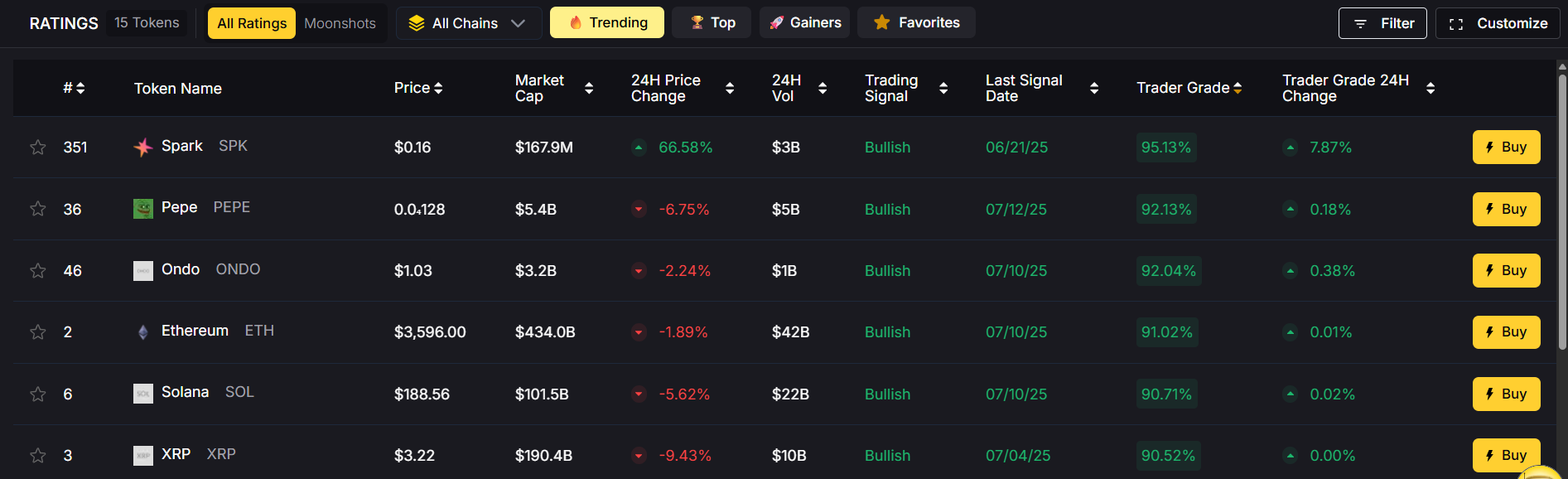
Market capitalization plays a significant role in shaping investment strategies within the crypto market. It influences the level of risk investors are willing to take and the potential returns they might expect. Cryptocurrencies are categorized into three market cap sizes: large-cap (over $10 billion), mid-cap ($1 billion to $10 billion), and small-cap (under $1 billion). Large cap cryptocurrencies, typically those with a market cap exceeding $10 billion, are generally less volatile and more stable. These assets are favored by conservative investors who prioritize security and steady growth.
On the other hand, mid cap and small cap cryptocurrencies often present higher growth potential but come with increased risk and price volatility. Small cap cryptocurrencies may be more susceptible to market fluctuations and liquidity challenges but can offer substantial returns if their underlying projects succeed.
Staying informed about market trends and understanding how market cap affects demand, liquidity, and price movements are essential for developing effective investment strategies. Investors who respond appropriately to these factors are better positioned to capitalize on opportunities and mitigate risks.
Characteristics of a Liquid Market
A liquid market is characterized by the ability to quickly buy or sell assets without causing significant price changes. In the crypto market, liquidity is a critical factor affecting volatility and trading volume. High liquidity means that there is a large number of buyers and sellers, facilitating smooth transactions and reducing price manipulation risks.
Cryptocurrencies with a high market cap tend to have more liquid markets due to their popularity and widespread adoption. This liquidity attracts institutional investors and traders who require the ability to enter and exit positions efficiently. Conversely, small cap cryptocurrencies may suffer from low liquidity, leading to higher volatility and wider bid-ask spreads.
A liquid market with high trading volume provides better price stability and more trading opportunities, making it more attractive for both short-term traders and long-term investors.
The Crypto Market Ecosystem
The crypto market ecosystem is a complex and evolving environment influenced by various factors beyond market cap. Blockchain technology underpins all cryptocurrencies, providing the decentralized infrastructure that ensures transparency and security. Network security, driven by consensus mechanisms and the number of active nodes, plays a crucial role in maintaining trust and stability in the market.
Institutional investors have increasingly entered the crypto market, bringing greater capital, legitimacy, and scrutiny. Their participation often affects market trends and can lead to increased liquidity and reduced volatility in large cap cryptocurrencies.
Understanding this ecosystem and the interplay of technology, investor behavior, and market dynamics is essential for anyone looking to navigate the crypto market successfully. The market is constantly responding to new technologies, regulatory developments, and shifts in investor sentiment.
Large Cap Cryptocurrencies
Large cap cryptocurrencies, such as Bitcoin and Ethereum, dominate the crypto market with market caps exceeding $10 billion. These digital assets are widely regarded as more stable and less volatile compared to smaller cryptocurrencies. Their established track records and strong network security make them attractive safe havens during periods of market uncertainty.
Large cap cryptocurrencies benefit from high liquidity and trading volume, which contribute to better price stability and ease of trading. However, because of their already substantial market capitalization, these assets may experience slower price growth compared to mid or small cap cryptocurrencies.
Investors often include large cap cryptocurrencies in their portfolios to provide balance and reduce overall risk.
Growth Potential and Analysis
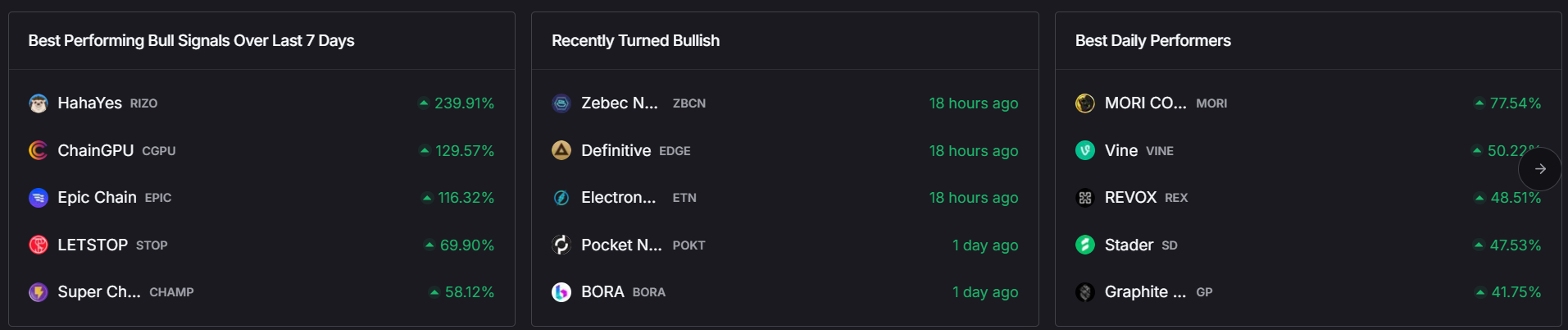
While large cap cryptocurrencies offer stability, mid cap and small cap cryptocurrencies often present greater growth potential. These smaller crypto assets may be in earlier stages of development, with innovative projects and technologies that can lead to significant price appreciation.
Analyzing growth potential involves examining a cryptocurrency’s market cap, trading volume, underlying blockchain technology, and the strength of its project or business model. Investors also consider factors such as tokenomics, total supply, and network security to assess long-term viability.
However, higher growth potential comes with increased risk, including higher volatility and liquidity challenges. Investors must carefully weigh these factors and conduct thorough research before committing to investments in smaller cap cryptocurrencies.
Developing Effective Investment Strategies
Crafting effective investment strategies in the crypto market requires a comprehensive understanding of market trends, risk management, and portfolio diversification. Investors should clearly define their investment goals and risk tolerance before entering the market.
Market capitalization is a critical consideration in strategy development, as it affects liquidity, volatility, and potential returns. Diversifying investments across large cap, mid cap, and small cap cryptocurrencies can help balance risk while capturing growth opportunities.
Staying informed about the latest market trends, technological advancements, and regulatory changes is essential. Investors should be prepared to adapt their strategies as the crypto market evolves, responding to shifts in demand, supply, and broader economic factors.
In conclusion, understanding what cryptocurrency market cap is and how it influences the crypto market is vital for making informed investment decisions. By considering market cap alongside other metrics such as circulating supply, trading volume, and network security, investors can navigate the complex world of digital assets with greater confidence and success.
Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)









.svg)




.png)