API Security Essentials: How to Authenticate and Protect Your API Requests

APIs power everything from mobile apps to crypto trading platforms. As they become the backbone of digital finance and decentralized applications, securing API endpoints is more critical than ever. A single vulnerability can expose sensitive data, undermine user trust, or even lead to costly breaches. So, how can you authenticate and secure your API requests effectively?
Understanding API Authentication Fundamentals
API authentication is the process of verifying that API requests come from legitimate sources. This step is essential to prevent unauthorized access and data leaks, especially in industries handling sensitive information like cryptocurrency and finance. There are several standard authentication methods:
- API Keys: Basic yet popular; clients receive a unique token identifying their requests. However, keys alone are not sufficient unless properly managed and kept confidential.
- OAuth 2.0: An authorization framework used by many leading platforms for delegated user access without exposing credentials. It supports fine-grained permissions and token expiration for higher security.
- JWT (JSON Web Tokens): Encoded tokens containing user and permission data, signed for integrity. JWTs are commonly used in stateless authentication flows due to their portability and standardization.
- HMAC (Hash-based Message Authentication Code): Ensures both authenticity and integrity by letting clients sign API requests using a shared secret, verifying that the data has not been altered in transit.
Choosing the right authentication mechanism depends on your application's needs, security requirements, and threat model. For example, high-value crypto data or transaction endpoints require more robust solutions than public info APIs.
Securing API Requests: Encryption and Data Protection
Authentication can only go so far without communication channel security. APIs must use encryption to safeguard data in transit. Here’s how to reinforce API requests against interception and tampering:
- HTTPS/TLS: Mandatory for all API traffic. Encrypted connections prevent man-in-the-middle attacks and secure private data exchanged with your API.
- Certificate Pinning: Reduces the risk of certificate authority (CA) compromise by ensuring API clients only connect to trusted, recognized servers.
- Encrypt Sensitive Payloads: For especially private information (e.g., wallet keys, user identifiers), encrypt payloads beyond transport encryption before sending.
- Limit Data Exposure: Only return necessary data in API responses. Overexposed APIs create unnecessary risk, especially when returning critical financial or identity information.
Data protection is not purely about outside attackers. Proper encryption and data minimization also reduce compliance risk and support privacy best practices relevant to digital assets.
Best Practices for API Key and Secret Management
API keys and secrets are valuable attack targets—treat them like passwords. Here are practical steps to keep them secure:
- Never Embed Secrets in Client-Side Code: Keys in JavaScript or mobile apps can be easily extracted and abused. Always handle sensitive tokens on a secure backend server.
- Implement Key Rotation: Change secrets regularly and immediately revoke compromised keys. Automated rotation limits potential damage from leaks.
- Use Scoped Permissions: Assign only the minimum required privileges to API keys. Fine-grained permissions restrict what actions a compromised key could perform.
- Storage in Secret Managers: Use established tools (e.g., AWS Secrets Manager, HashiCorp Vault) for storing and accessing keys, rather than environment variables or config files.
- Monitor Key Usage: Set up alerts for abnormal key activity—such as new locations, excessive requests, or usage spikes—to catch and act on suspicious behavior quickly.
In the world of crypto APIs, where unauthorized trades or fund transfers can have major consequences, diligent key management is foundational to API security.
Additional API Security Controls and Threat Prevention
Authentication and encryption are essential, but holistic API security requires additional layers of defense:
- Rate Limiting & Throttling: Prevents API abuse and distributed denial-of-service (DDoS) attacks by restricting the number of requests per minute or hour for each client.
- IP Allowlisting: Restrict API access to approved server or office ranges to limit exposure in case keys are leaked.
- Input Validation & Sanitization: Defend against injection attacks by ensuring only properly formatted, expected data can be submitted to your API endpoints.
- Logging and Audit Trails: Record who accessed what and when. Detailed logs help identify breaches quickly and fulfill regulatory audit requirements.
- Regular Penetration Testing: Simulate attacks to find and patch weaknesses before they are exploited in production environments.
Effective API security is an ongoing process. Stay updated with the latest threats and best practices—especially as new technologies and decentralized protocols evolve in the crypto sector.
How AI and Secure APIs Are Shaping Crypto Development
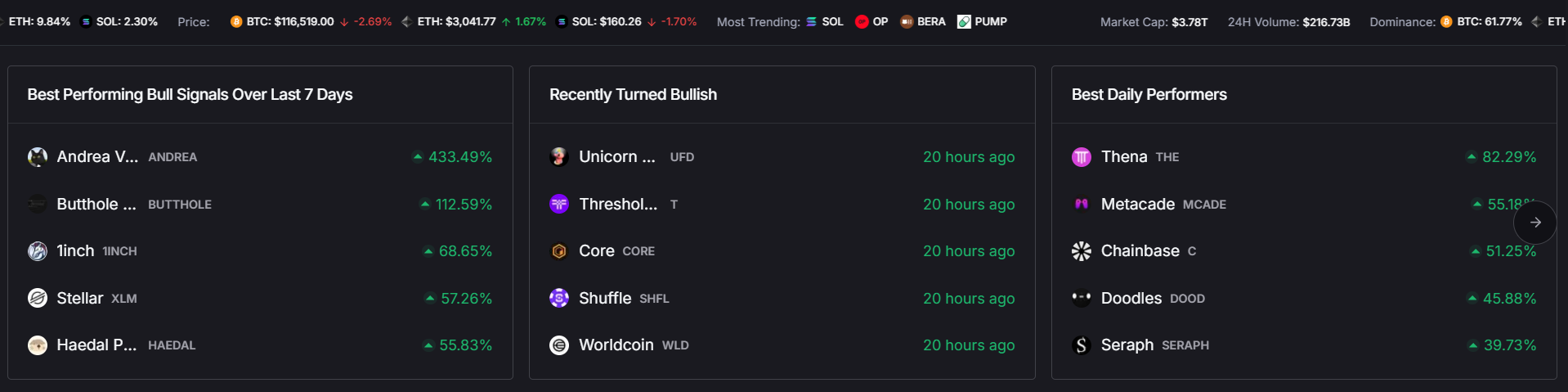
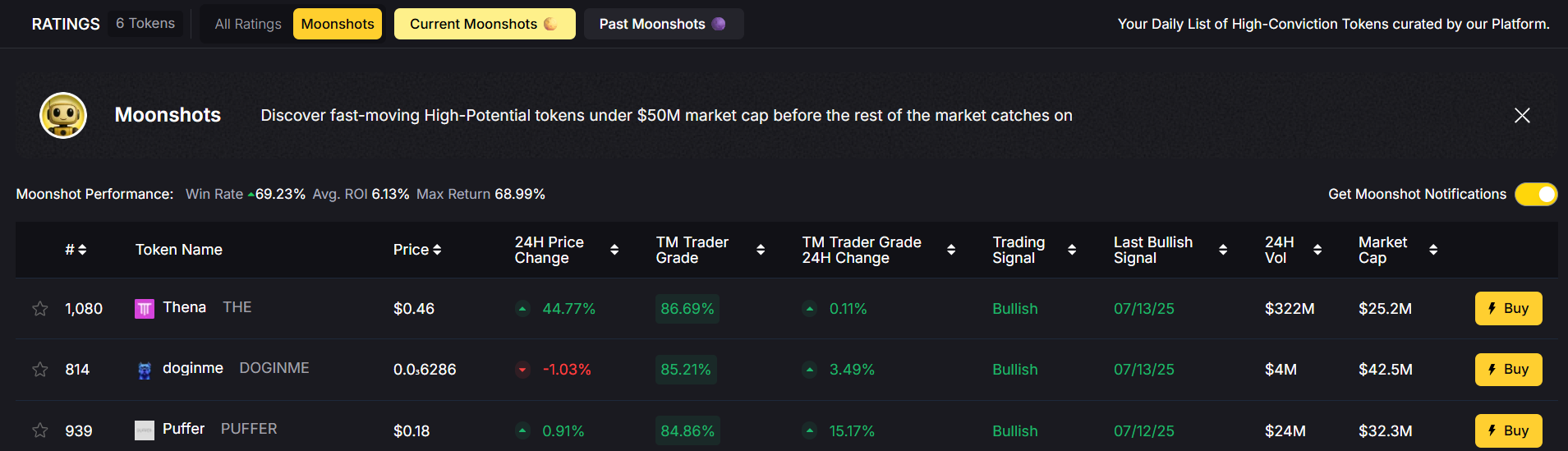
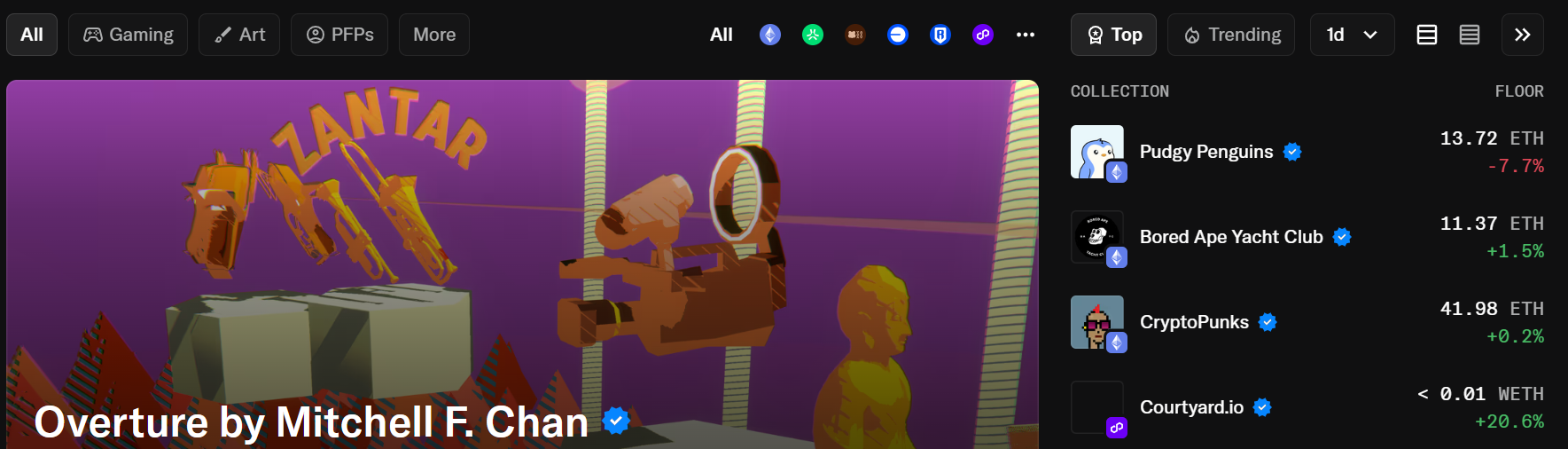
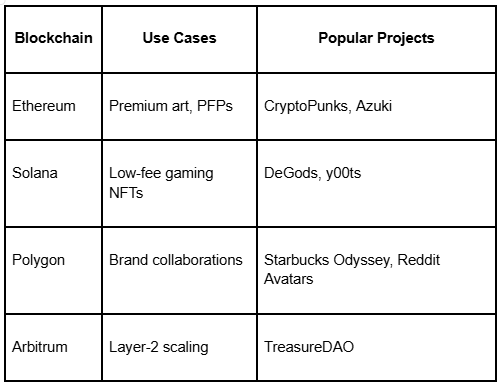
The rapid growth of digital assets has driven demand for real-time data, automated trading strategies, and personalized user experiences. Crypto APIs, especially those leveraging AI, enable everything from on-chain analytics to dynamic risk scoring. However, these capabilities also come with heightened security stakes: AI-driven agents making transactions or analyzing blockchain data depend on reliable, tamper-proof sources.
Integrating secure APIs backed by strong authentication and threat prevention supports:
- Accurate, timely access to pricing and blockchain analytics
- Protection against malicious interference in trading signals or execution
- Compliance with increasing regulatory and cybersecurity requirements
- Trust in AI-driven decision support systems for both individual and institutional users
Using advanced API security controls helps crypto app developers maximize innovation while safeguarding users and market integrity.
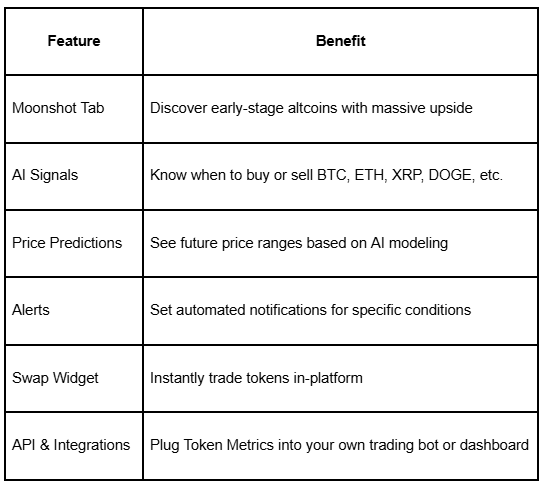
Build Smarter Crypto Apps & AI Agents with Token Metrics
Token Metrics provides real-time prices, trading signals, and on-chain insights all from one powerful API. Grab a Free API Key
FAQ: Securing API Requests
What is the difference between API authentication and authorization?
Authentication confirms the identity of the API requestor, while authorization defines what resources and actions that identity can access or perform. Both are needed for secure API usage.
Should I use API keys, OAuth, or JWT for my crypto app?
The choice depends on your use case. API keys are simple for service-to-service communication. OAuth offers stronger, user-specific security. JWT excels in stateless authentication. Many robust crypto APIs use combinations depending on endpoint sensitivity.
How can I safely distribute API keys to users?
Provide keys using secure, authenticated user portals. Avoid email or plaintext transmission. Always ensure users understand to treat API credentials like passwords and never share or expose them.
What are common mistakes that weaken API security?
Embedding secrets in frontend code, not enforcing HTTPS, failing to rotate keys, ignoring rate limits, and returning too much sensitive data are common but avoidable risks.
How often should I review and update my API security settings?
Review security policies and settings at least quarterly, or following any significant change (e.g., new endpoints, user roles, or integration partners). Promptly address newly discovered vulnerabilities and emerging threats.
Disclaimer
This content is for educational and informational purposes only. It does not constitute technology, investment, or legal advice. Security strategies and technologies evolve rapidly; always consult with cybersecurity professionals before implementing any measures in critical or regulated environments.
Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)








.png)





.svg)




.png)