
15 Low Cap Crypto Altcoins for the Next Bull Run

Click here to buy Cryptocurrencies from Gate.io
Contact us at promo@tokenmetrics.com for marketing and sponsorship programs.
As we move further into 2025, the best crypto altcoins are capturing the attention of both retail investors and professional traders worldwide. While Bitcoin and Ethereum remain dominant assets anchoring the cryptocurrency market, the altcoin market is witnessing a surge of innovation fueled by advancements in AI, decentralized finance (DeFi), and smart contracts. Crypto coins are a fundamental category of digital assets, serving as native currencies on their respective blockchains and playing a crucial role in transactions and ecosystem functions. Altcoins can apply different consensus protocols for transaction verification and may offer unique or better features and functions compared to Bitcoin. This dynamic environment presents unparalleled opportunities for investors seeking to diversify their portfolios beyond the most cryptocurrencies and explore promising altcoin investments with high growth potential.
In this article, we will explore the top 15 best crypto altcoins to watch in 2025. These projects span various sectors such as AI integration, Web3, decentralized compute, and the creator economy. Each altcoin offers unique utilities, competitive advantages, and strong communities, making them attractive options for those interested in long-term investments or active trading. A skilled and capable project team behind an altcoin can indicate its long-term success potential. Understanding these altcoins’ value propositions and market dynamics is essential. It’s important to note the distinction between coins (or crypto coins) and tokens: coins, also referred to as crypto coins, function as the primary currency or utility within their blockchain ecosystems, while tokens often serve specific purposes on top of existing blockchains. This clarification will help investors navigate the crypto ecosystem more effectively while managing risk tolerance in a space known for price fluctuations.
Introduction to the Crypto Space
The cryptocurrency market has rapidly evolved into a global financial ecosystem, with its total market capitalization now exceeding $2 trillion. This vibrant crypto space is home to a wide array of digital currencies, including Bitcoin, altcoins, and various tokens, each offering unique features and use cases. Unlike traditional financial institutions, the crypto market operates on a decentralized platform, enabling peer-to-peer transactions and the execution of smart contracts without intermediaries. While this independence fosters innovation and accessibility, it also introduces significant price fluctuations and volatility. Altcoins carry more risk than Bitcoin and many of the smaller ones may not be trustworthy investments. As a result, investors must conduct thorough research and understand the inherent risks before participating in the cryptocurrency market. Whether you’re exploring Bitcoin or the latest altcoins, staying informed and cautious is essential for navigating this dynamic and often unpredictable market.
The Cryptocurrency Market Landscape
The cryptocurrency market landscape is incredibly diverse, boasting over 10,000 different cryptocurrencies. While Bitcoin remains the most recognized and widely held asset, altcoins such as Ethereum, Binance Coin, and Ripple have carved out substantial market shares and are favored by many investors. Cardano (ADA) is an advocate for proof-of-stake consensus and offers a blockchain solution with low fees and high security. The market capitalization of these altcoins can shift dramatically, often influenced by market sentiment, technological advancements, and broader economic trends. Financial institutions and regulatory bodies like the Securities and Exchange Commission are increasingly engaging with the crypto market—some by investing directly, others by establishing guidelines to ensure investor protection and market integrity. Decentralized finance (DeFi) has emerged as a transformative force within the crypto market, offering innovative platforms for lending, borrowing, and trading that operate independently of traditional banks. As the market continues to mature, understanding the interplay between these elements is crucial for anyone looking to invest or trade in cryptocurrencies.
Altcoin Season and Market Trends
Altcoin season is a phenomenon in the crypto market where altcoins outperform Bitcoin, often resulting in rapid increases in altcoin prices. These periods are typically driven by shifts in market sentiment and emerging trends, making them highly attractive to investors seeking significant returns. However, the crypto market is known for its volatility, and price fluctuations can be swift and unpredictable. Seasoned crypto investors often employ strategies such as diversification and risk management to navigate these turbulent times. For example, Bitcoin Cash has experienced notable price swings during past altcoin seasons, attracting traders looking to capitalize on these movements. Bitcoin Cash (BCH) offers fast transaction times and lower fees compared to Bitcoin, making it a popular choice during these periods. Staying attuned to market trends and sentiment is essential for making informed decisions and maximizing opportunities during altcoin season, while also managing the inherent risks of trading in such a dynamic environment.
1. Token Metrics AI ($TMAI)

Token Metrics AI ($TMAI) stands out as a groundbreaking project that merges AI with crypto analytics to empower smarter investing decisions. This platform offers an all-in-one AI trading assistant that combines autonomous agent tooling, on-chain infrastructure, and predictive analytics. Users can stake $TMAI tokens to access features like crypto indices, research automation, and trader/investor grading systems.
The Token Metrics AI platform is particularly valuable for seasoned crypto investors and traders who rely on data-driven insights to navigate the volatile crypto market. Its integration with various tools, including Signals and Smart Agents, facilitates seamless trading and investing processes by streamlining the process of executing trades, analyzing data, and managing assets through a clear workflow. With $TMAI, users benefit from a sophisticated ecosystem designed to optimize returns and reduce the guesswork commonly associated with altcoin trading.
2. Suilend ($SEND)

Suilend ($SEND) is a native DeFi lending protocol built on the Sui blockchain, which is gaining traction due to its low transaction fees and innovative parallel transaction processing. The platform's low fees provide a competitive advantage for users, making it especially appealing to cost-conscious traders and investors. As the Sui network expands, Suilend is positioned to capitalize on the growing demand for capital-efficient lending and borrowing services.
The platform supports Sui-native tokens, enabling users to leverage their crypto assets efficiently within a low-competition DeFi environment. This makes $SEND an attractive option for investors seeking exposure to decentralized finance with minimized transaction fees and a scalable infrastructure. Its rapid total value locked (TVL) growth underscores its rising market value and adoption.
3. Blackhole ($BLACK)
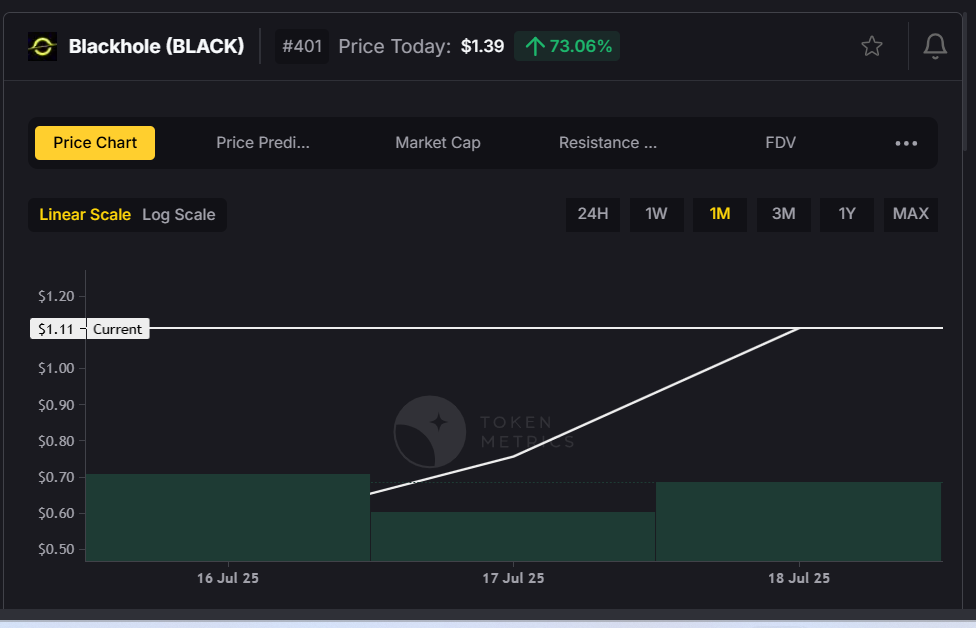
Blackhole ($BLACK) is carving a niche as a decentralized compute platform that provides GPU resources for AI, machine learning, and crypto infrastructure projects. By incentivizing GPU providers and AI developers through its native $BLACK token—the native coin of the Blackhole platform, essential for transaction fees and overall platform operations—the platform fosters a collaborative environment for decentralized AI compute sharing.
This project is pivotal for the evolving decentralized finance and AI sectors, offering a decentralized platform where compute power can be rented and shared securely. For investors interested in the intersection of AI and blockchain technology, Blackhole represents a unique asset with the potential to disrupt traditional centralized compute services.
4. Resolv ($RESOLV)

Resolv ($RESOLV) innovates at the crossroads of AI and smart legal contracts by developing AI agents that automate compliance, arbitration, and dispute resolution. This platform empowers decentralized autonomous organizations (DAOs) and dApps with tools for on-chain contract enforcement and legal agreement automation.
As regulatory scrutiny from bodies like the Securities and Exchange Commission increases, projects like Resolv that enhance legal transparency and automation are becoming essential. By integrating large language models (LLMs) into smart contracts, Resolv offers a competitive edge in the crypto space, appealing to users and investors focused on compliance and decentralized finance.
5. Cookie.fun ($COOKIE)

Cookie.fun ($COOKIE) blends social engagement, AI creativity, and entertainment by offering AI-generated animated content and meme NFTs. This platform leverages the virality of meme culture to create a decentralized social environment where creators and fans can monetize digital content.
The unique combination of meme NFTs and community rewards makes Cookie.fun a standout in the creator economy. For crypto enthusiasts looking to participate in the cultural side of the crypto market, $COOKIE offers a novel way to engage with digital assets while benefiting from the rise of AI-generated entertainment.
6. Usual Money ($USUAL)

Usual Money ($USUAL) addresses the need for a user-friendly, decentralized stablecoin platform optimized for DeFi payments and yield generation. By combining a seamless user experience with smart routing for capital efficiency, Usual Money enhances the dollar experience for crypto-native users.
This platform’s focus on yield-bearing stablecoins and low transaction fees positions it well within the growing decentralized finance sector. Investors seeking stable, utility-driven tokens with real-world applications in payments and DeFi will find $USUAL an appealing asset.
7. Freysa AI ($FAI)

Freysa AI ($FAI) is building a decentralized framework for AI agents capable of interacting with blockchains, decentralized exchanges (DEXes), and dApps. This infrastructure supports on-chain automation and facilitates the development of crypto copilots that enhance user interaction within the crypto ecosystem.
By integrating leading AI models with on-chain APIs, Freysa AI offers a powerful toolset for developers and users aiming to streamline complex processes. Its role in decentralized AI infrastructure makes $FAI a promising token for investors focused on the future of AI-driven blockchain applications.
8. LOFI

LOFI is an innovative project at the intersection of AI, music, and culture. It enables artists and fans to co-create and monetize AI-generated generative music NFTs, focusing on ambient soundscapes and fan engagement.
This platform taps into the creator economy by facilitating music royalties and fostering fan economies through blockchain technology. LOFI’s unique approach to combining generative music with NFTs offers a fresh avenue for investors interested in cultural and entertainment-related crypto assets.
Click here to buy Cryptocurrencies from Gate.io
9. Gradients ($SN56)
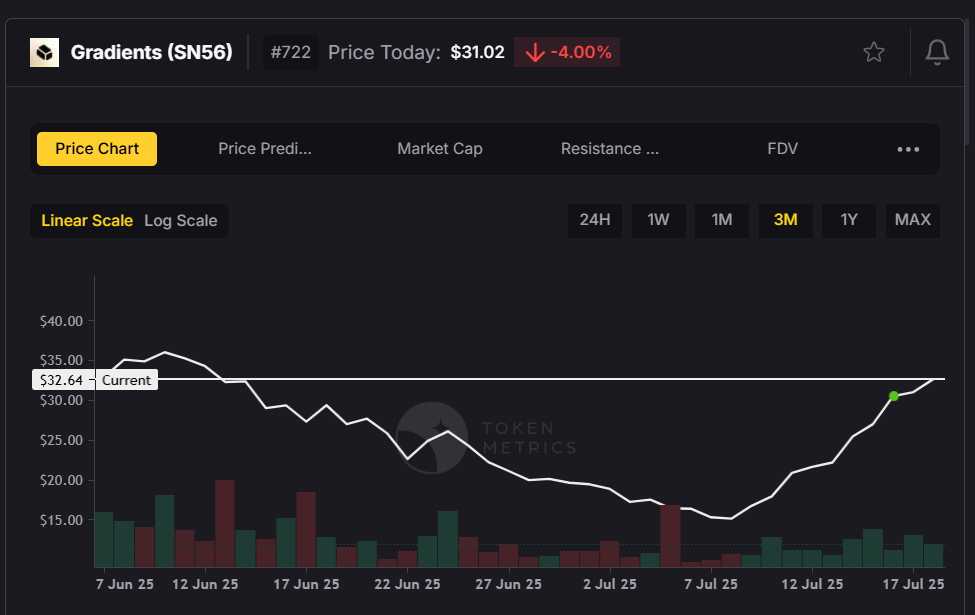
Gradients ($SN56) operates a token-incentivized data marketplace that crowdsources datasets for AI training and machine learning model development. This decentralized approach to data collection and sharing enhances the quality and accessibility of training data for AI developers.
With token-gated access to proprietary datasets, Gradients empowers users and developers to contribute to and benefit from the growth of AI capabilities. Investors focused on AI and data-driven crypto projects will find $SN56 an intriguing addition to their portfolios.
10. BIO Protocol ($BIO)

BIO Protocol ($BIO) merges biotechnology with decentralized science (DeSci) by enabling researchers and biotech firms to tokenize experiments and scientific contributions. This platform fosters on-chain reputation systems and data royalties, incentivizing scientific innovation and collaboration.
By facilitating AI-driven drug discovery and scientific data sharing, BIO Protocol addresses real-world challenges through blockchain technology. This project appeals to investors interested in the convergence of biotech, AI, and decentralized finance.
11. Swarms ($SWARMS)

Swarms ($SWARMS) is developing an open-source protocol for multi-agent coordination across decentralized applications. This technology enables smart agents to execute complex tasks such as DAO governance, DeFi arbitrage, and airdrop farming efficiently.
The platform’s swarm AI logic supports parallelized on-chain execution, enhancing scalability and automation. For traders and investors looking at the next wave of decentralized automation, $SWARMS offers compelling utility and growth potential.
12. Creator.bid ($BID)

Creator.bid ($BID) is an auction platform where fans can bid on personalized content created by AI-powered influencers and creators. This project combines AI celebrity clones with fan tokens to revolutionize creator monetization.
Its auction dynamics and custom content-generation models provide a unique marketplace within the creator economy. Investors interested in AI-driven social platforms and fan engagement will find $BID an exciting asset.
13. Collaterize ($COLLAT)

Collaterize ($COLLAT) bridges the gap between real-world assets and decentralized finance by allowing users to tokenize and collateralize assets such as invoices and real estate. This integration facilitates asset-backed lending and yield generation within DeFi.
With transparent smart contracts and real-world audits, Collaterize enhances trust and security for investors. This project is particularly appealing to those seeking exposure to real-world asset (RWA) collateralization in the crypto market.
14. aixbt by Virtuals ($AIXBT)

aixbt ($AIXBT) is an AI-powered trading bot platform that leverages both on-chain and off-chain data to execute autonomous crypto trading strategies. The platform enables users to trade altcoins using advanced AI-driven tools, providing flexibility and efficiency in managing a diverse portfolio. It offers real-time trade simulations and leaderboard-based strategy competitions.
This platform caters to traders looking for sophisticated, data-driven tools to navigate price fluctuations and market sentiment. $AIXBT’s innovative approach to AI trading bots makes it a valuable asset in the competitive crypto trading landscape.
15. MyShell AI ($SHELL)

MyShell AI ($SHELL) enables users to create voice-based AI characters that operate across multiple platforms like Discord and Telegram. This project supports voice-to-earn economies and multi-platform bot deployment, enhancing user interaction and customer support.
By combining AI agents with creator studios, MyShell AI taps into the growing demand for personalized, voice-enabled digital experiences. Investors interested in AI-driven user engagement and decentralized platforms will find $SHELL noteworthy.
Trading Strategies for Altcoins
Trading altcoins successfully requires a solid grasp of the crypto market and its ever-changing trends. Professional traders often rely on technical analysis, chart patterns, and market indicators to anticipate price movements and make strategic trades. When trading altcoins, it’s important to consider factors such as trading fees, transaction fees, and the overall volatility of digital currencies. Understanding the underlying technology, use cases, and competitive landscape of each altcoin can provide a significant edge. Many exchanges, including industry leaders like Binance and Kraken, offer robust platforms for trading a wide variety of altcoins, making it easier for investors to access and trade these digital assets. By staying informed and leveraging the right tools, traders can navigate the complexities of the crypto market and optimize their trading strategies for better results.
Risk Management for Altcoin Investors
Investing in altcoins presents unique challenges, including high price volatility, potential market manipulation, and evolving regulatory landscapes. Retail investors must be proactive in managing these risks by diversifying their portfolios and conducting thorough research before making any altcoin investments. Long term investments in altcoins can yield substantial rewards, but they require a deep understanding of the crypto market and its shifting dynamics. The Securities and Exchange Commission has provided guidelines to help investors navigate the regulatory aspects of cryptocurrency investing, and it’s crucial to ensure compliance with these rules. Platforms like Tron Network and Ripple Labs have introduced low-fee structures and stablecoin solutions to help mitigate some of the risks associated with trading and investing in altcoins. By understanding both the risks and potential rewards, investors can make informed decisions and confidently participate in the ever-evolving world of altcoins and digital assets.
Final Thoughts: How to Evaluate Altcoins in 2025
Selecting the best crypto altcoins for 2025 requires thorough research and a strategic approach. Investors should prioritize projects with strong narratives aligned to AI, DeFi, real-world assets, and autonomous agents. Active development and vibrant communities are essential indicators of a project’s sustainability and growth potential. Monitoring new coins entering the market is important, as their supply and circulating supply can impact scarcity and value.
Real token utility and demand mechanisms, such as staking, transaction fee savings, or governance rights, add tangible value to crypto tokens. Interoperability with expanding ecosystems like Sui, Base, and Solana further enhances an altcoin’s market capitalization and market cap stability.
For many investors and traders, platforms like Token Metrics AI ($TMAI) serve as critical tools to analyze market data, track performance, and gauge market sentiment. Crypto prices are influenced by supply, demand, and trading activity, so understanding these factors is crucial for evaluating altcoins. Utilizing such resources can help navigate the complexities of the cryptocurrency market, balancing risk tolerance with the pursuit of high-reward altcoin investments.
In summary, the best crypto altcoins in 2025 are those that combine innovative technology, competitive advantages, and real-world applications within a rapidly evolving crypto ecosystem. When comparing altcoins to other cryptocurrencies, it is important to consider their performance, trading volume, and the platforms they utilize—such as the XRP ledger, which supports fast transactions and differs from traditional blockchains. How actively an altcoin is traded can also indicate its liquidity and investor interest. By staying informed and leveraging cutting-edge platforms, investors can position themselves to capitalize on the rise of new crypto assets and the next altcoin season.
Click here to buy Cryptocurrencies from Gate.io
Contact us at promo@tokenmetrics.com for marketing and sponsorship programs.

.svg)

Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)







.svg)




.png)