
Best Crypto Exchanges for Altcoins: A Complete Guide to Alternative Cryptocurrencies in 2025

As the cryptocurrency market continues to evolve beyond Bitcoin, the term altcoins has gained significant importance. Altcoins are traded on various cryptocurrency exchanges, which are essential platforms in the crypto industry. A cryptocurrency exchange is an online platform that facilitates the buying, selling, and trading of digital assets. In 2025, thousands of digital currencies are actively traded, each designed to serve unique purposes—from powering smart contracts and decentralized finance to enhancing privacy and supporting gaming and artificial intelligence applications. For retail investors and crypto traders looking to diversify their digital asset portfolios, understanding what altcoins are, how they function, and how they differ from Bitcoin is crucial.
This comprehensive guide will explore the concept of altcoins, their various types, the reasons behind their existence, and the risks and rewards of investing in them. The diversity of cryptos available to investors has grown as the industry has evolved to support a wide range of digital assets. Today, exchanges serve millions of customers worldwide, providing tailored solutions for both retail and institutional clients. Additionally, we will highlight how platforms like Token Metrics help investors analyze and trade altcoins confidently in today’s dynamic crypto market. The range of crypto services offered by both exchanges and traditional financial institutions continues to expand, including custody solutions and banking services for digital assets.
Introduction to Crypto Exchanges
Crypto exchanges are the backbone of the digital asset ecosystem, providing a secure and efficient way for users to buy, sell, and trade cryptocurrencies like Bitcoin and a wide range of altcoins. These platforms connect crypto traders and retail investors to the broader crypto market, making it possible to exchange digital currencies for traditional fiat money or other crypto assets. As the industry has matured, the best crypto exchange platforms have become known for their low fees, robust security protocols, and top-tier customer service, catering to both beginners and advanced traders alike.
With the growing popularity of cryptocurrency exchanges, accessing and managing digital assets has never been easier. Whether you’re looking to trade crypto actively or simply invest in the best crypto projects, exchanges offer a variety of tools and services to help users navigate the fast-paced crypto market. From intuitive interfaces to advanced trading features, these platforms are designed to support a diverse range of trading strategies and investment goals.
🔍 What Are Altcoins?
The word “altcoin” is an abbreviation of “alternative coin,” referring to any cryptocurrency other than Bitcoin. While Bitcoin remains the most valuable cryptocurrency by market cap and serves as a digital store of value, altcoins represent the diverse ecosystem of other crypto assets developed after Bitcoin’s inception.
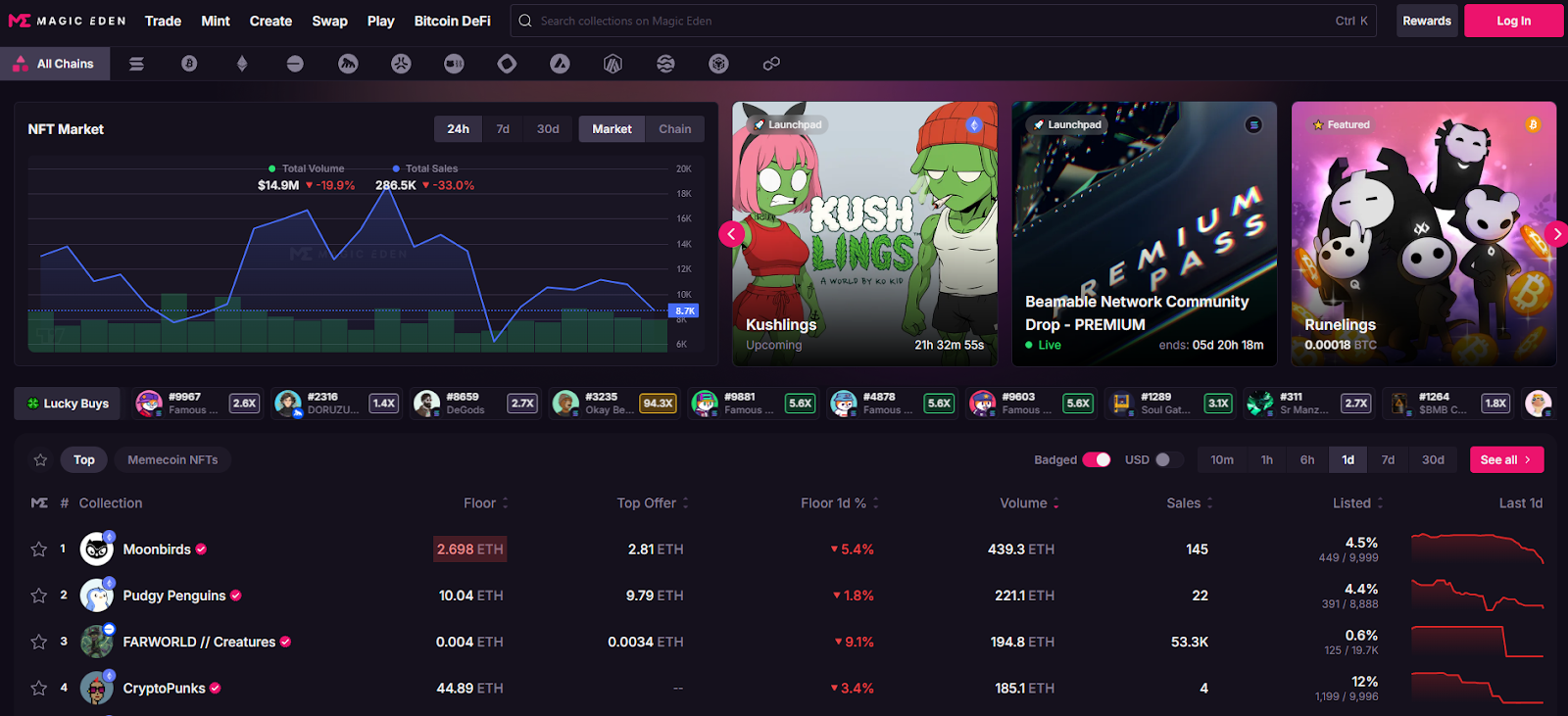
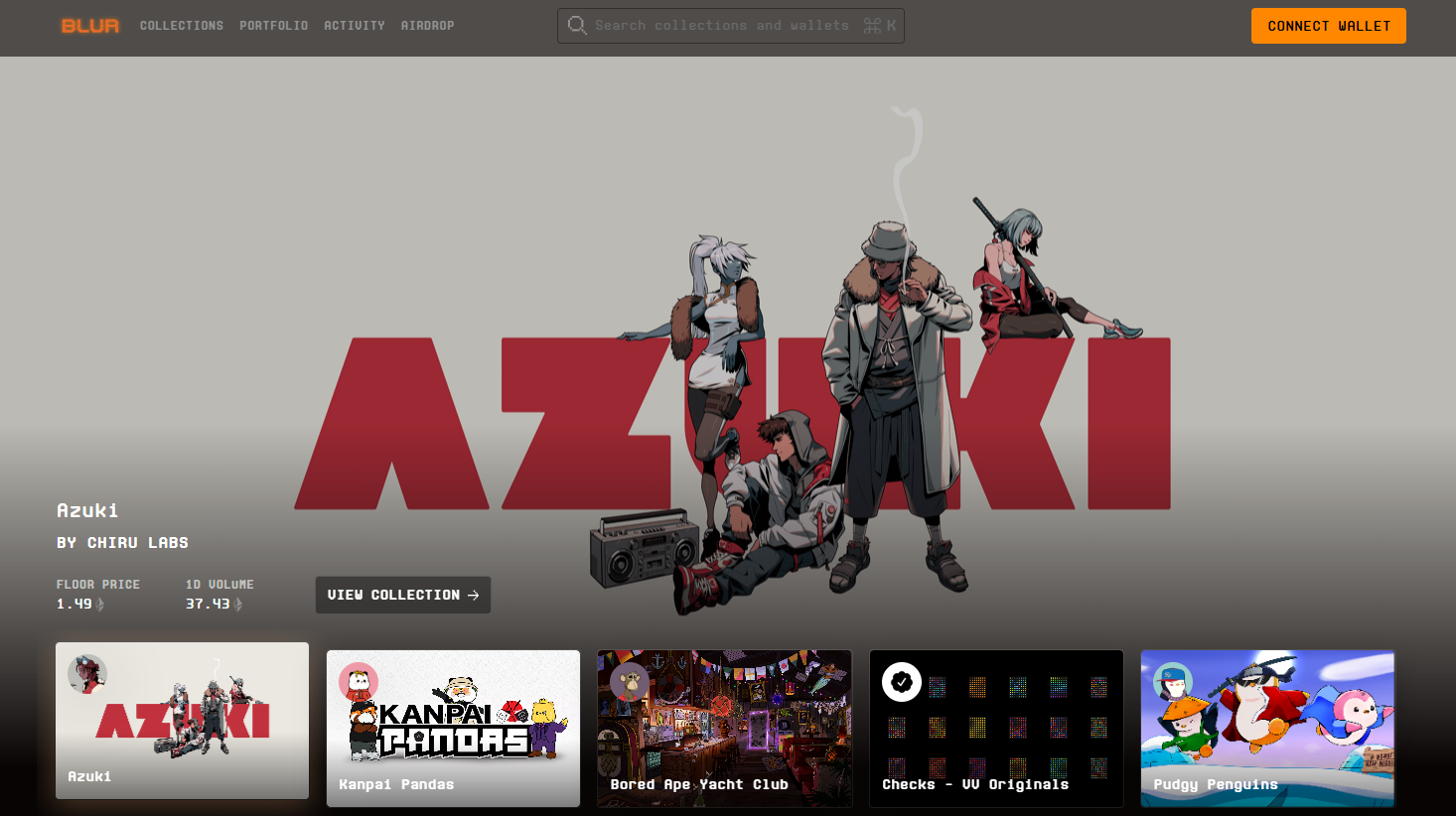
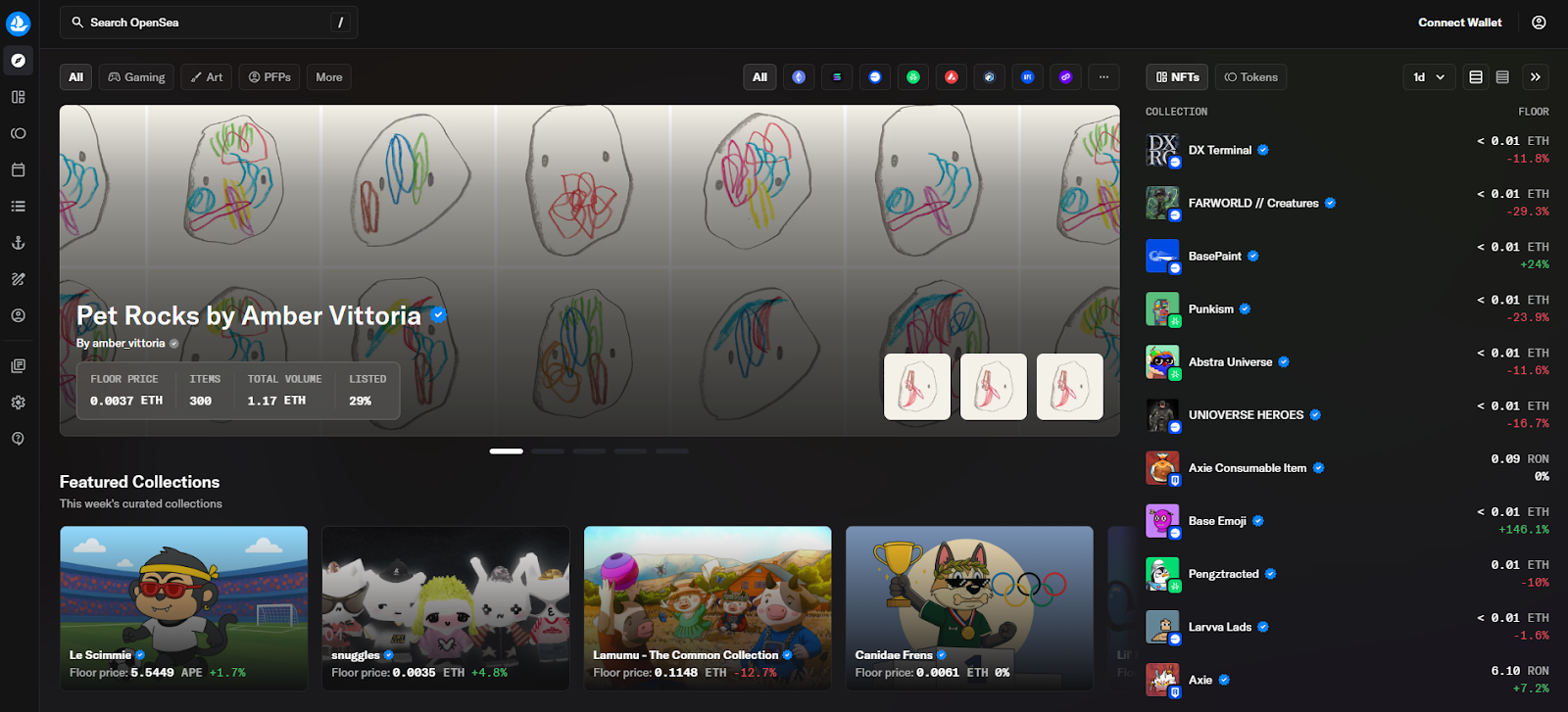
Altcoins encompass a wide array of digital currencies that differ in technology, consensus mechanisms, and use cases. Some altcoins are forks of Bitcoin’s codebase, while others operate on entirely separate blockchains. Altcoins are typically traded on a crypto exchange, which is usually operated by a business that facilitates secure cryptocurrency transactions. In 2025, altcoins have become essential in powering decentralized applications (DApps), smart contracts, decentralized finance (DeFi) protocols, non-fungible tokens (NFTs), and blockchain gaming platforms. Their innovation expands the possibilities of the crypto market far beyond Bitcoin’s original scope.
🧱 Types of Altcoins
Altcoins can be categorized based on their primary functionality and purpose within the crypto ecosystem. In addition to these main categories, there are many other coins available, including meme coins that have gained popularity due to internet trends. Here are some of the major types:
1. Smart Contract Platforms
These altcoins provide blockchains that host decentralized applications and execute programmable contracts, enabling complex interactions without intermediaries.
- Ethereum (ETH): The pioneering smart contract blockchain that supports a vast range of DApps and DeFi projects.
- Solana (SOL): Known for its high-speed transactions and low fees, Solana is a popular platform for DeFi and NFTs.
- Avalanche (AVAX): Offers scalability and interoperability, making it suitable for various decentralized applications.
- Cardano (ADA): A research-driven blockchain with a focus on sustainability and formal verification.
2. Stablecoins
Stablecoins are cryptocurrencies pegged to fiat currencies, usually the US dollar, to maintain price stability and facilitate transactions without volatility.
- Tether (USDT)
- USD Coin (USDC)
- DAI: A decentralized, algorithmic stablecoin managed by smart contracts.
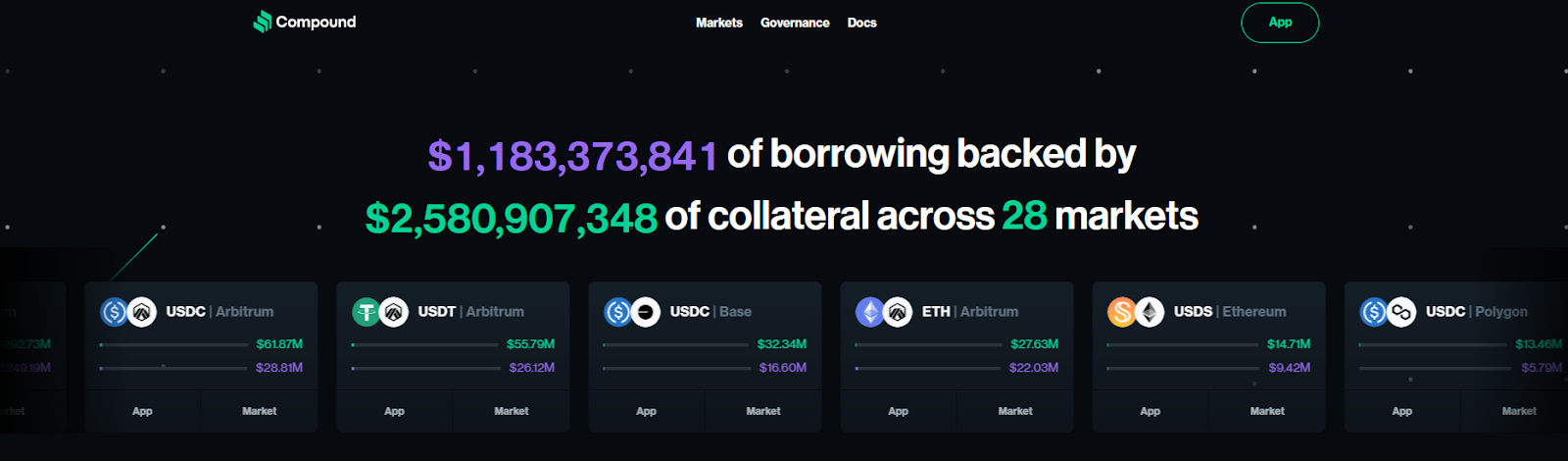
3. DeFi Tokens
These tokens power decentralized finance protocols that provide services like lending, borrowing, and yield farming without traditional intermediaries.
4. Privacy Coins
Designed to offer anonymous and untraceable transactions, privacy coins enhance user confidentiality.
5. Gaming and Metaverse Tokens
Used within blockchain-based games, NFT marketplaces, and virtual worlds, these tokens facilitate in-game economies and digital asset ownership.
- Axie Infinity (AXS)
- Immutable X (IMX)
- The Sandbox (SAND)
6. AI and Infrastructure Tokens
Focused on artificial intelligence, decentralized oracles, and data-sharing platforms, these altcoins support emerging tech use cases.
- Chainlink (LINK): A decentralized oracle network connecting smart contracts to real-world data.
- Ocean Protocol (OCEAN): Enables decentralized data exchange.
- TMAI (Token Metrics AI): Powers AI-driven research and analytics in crypto trading.
💡 Why Altcoins Exist
Altcoins were developed to address Bitcoin’s limitations and introduce new features. While Bitcoin excels as a secure, decentralized digital currency, it lacks programmability, speed, and flexibility for broader applications.
Altcoins aim to:
- Enhance scalability and transaction speed.
- Enable smart contracts and decentralized applications.
- Support decentralized ecosystems such as DeFi, DAOs, and NFTs.
- Provide privacy and anonymity for users.
- Facilitate governance and utility within blockchain protocols.
Altcoins are also driving the integration of blockchain technology into traditional finance, as banks and financial institutions begin to adopt crypto-related services.
By expanding the capabilities of blockchain technology, altcoins drive innovation and adoption across various sectors.
💼 Altcoin Wallets and Storage
As the popularity of altcoins continues to grow, choosing the right wallet and storage solution is essential for anyone looking to secure and manage their digital assets. With many cryptocurrency exchanges offering access to a wide range of coins, understanding how to safely store your assets is a major focus for both new and experienced crypto traders.
Hot Wallets vs. Cold Wallets
When it comes to storing altcoins, users can choose between hot wallets and cold wallets, each offering different levels of convenience and security:
- Hot Wallets: These are software-based wallets connected to the internet, such as desktop, mobile, or web wallets. Hot wallets are ideal for active trading and quick access to your crypto, making them popular among users who frequently buy, sell, or trade on many crypto exchanges. However, because they are online, they are more susceptible to hacking and cyber threats.
- Cold Wallets: These wallets store your private keys offline, using hardware devices like Ledger or Trezor. Cold wallets provide a higher level of security, making them the preferred choice for long-term storage of digital assets. While less convenient for frequent trading, they offer robust protection against unauthorized access.
Many crypto exchanges now offer integrated wallet services, allowing users to store their assets directly on the platform. When selecting a wallet—whether through an exchange or a standalone solution—consider factors such as the fee structure, security features, supported coins, and ease of use. Always research the reputation and security measures of any exchange or wallet provider before storing your crypto.
Security Best Practices
Protecting your digital assets requires more than just choosing the right wallet. Here are some essential security best practices:
- Enable Two-Factor Authentication (2FA): Add an extra layer of security to your wallet and exchange accounts.
- Use Strong, Unique Passwords: Avoid reusing passwords and consider using a password manager.
- Keep Software Updated: Regularly update your wallet software and any related apps to patch security vulnerabilities.
- Backup Your Wallet: Create secure backups of your wallet’s recovery phrase or private keys, and store them in a safe location—such as a physical safe or encrypted cloud storage.
- Consider Multi-Signature Wallets: Some wallets and top crypto exchanges offer multi-sig options, requiring multiple approvals for transactions, which can further secure your assets.
By following these best practices and leveraging the advanced security features offered by many exchanges, you can help ensure your digital assets remain safe and accessible only to you.
⚒️ Altcoin Mining and Staking
Participating in the creation and validation of new blocks is a core part of many altcoin networks. Altcoin mining and staking not only help secure blockchain networks but also offer opportunities for users to earn rewards and grow their cryptocurrency holdings.
In addition to mining and staking, many exchanges provide access to futures contracts, allowing experienced traders to speculate on the price movements of altcoins and other digital assets.
How Mining Works for Altcoins
Mining for altcoins can involve different processes depending on the underlying blockchain protocol:
- Proof-of-Work (PoW): Similar to Bitcoin, some altcoins use PoW, where miners compete to solve complex mathematical problems. The first to solve the problem validates the transaction and adds a new block to the blockchain, earning rewards in the form of cryptocurrency.
- Proof-of-Stake (PoS): Many newer altcoins use PoS, where users “stake” their coins by locking them in the network. Validators are chosen to create new blocks based on the amount of cryptocurrency they hold and are willing to stake, rather than computational power.
With the rise of many crypto exchanges, users no longer need to set up their own mining rigs or run complex software. Many exchanges offer mining pools and staking services, allowing users to participate in these processes with lower barriers to entry. These platforms often provide copy trading features and educational resources, making it easier for both beginners and advanced traders to get started.
By understanding the differences between mining and staking, and utilizing the services offered by reputable exchanges, users can make informed decisions about which altcoins to invest in and how to participate in the broader crypto market. Whether you’re looking to earn rewards, diversify your crypto portfolio, or simply learn more about blockchain technology, mining and staking offer valuable ways to engage with the cryptocurrency ecosystem.
📊 Investing in Altcoins: Risks and Rewards
For investors looking to expand their crypto portfolio beyond Bitcoin, altcoins present both exciting opportunities and notable risks. Compared to traditional assets like stocks, which are generally more established and regulated, altcoins offer higher potential returns but also come with greater risk.
✅ Benefits:
- Potential for higher growth compared to Bitcoin, with some altcoins delivering 10x to 100x returns.
- Exposure to innovative sectors like AI, DeFi, gaming, and privacy.
- Often more accessible to retail investors due to lower entry prices.
- Opportunities to earn passive income through staking or yield farming.
⚠️ Risks:
- Higher price volatility than Bitcoin, leading to rapid gains or losses.
- Lower liquidity in small-cap altcoins can make trading more challenging.
- Risk of scams, rug pulls, or projects with weak fundamentals.
- Regulatory uncertainty that can impact certain altcoins.
- Many altcoin projects fail, emphasizing the need for careful research.
🧠 How to Research Altcoins
Thorough research is essential before investing in altcoins. Key factors to analyze include:
- The project’s use case and real-world utility.
- Tokenomics, including supply schedule and distribution.
- The development team’s credibility and roadmap.
- Market trends and community sentiment.
- Partnerships, integrations, and ecosystem support.
Manually conducting this research can be time-consuming and subjective. This is where AI-powered tools like Token Metrics provide valuable assistance.
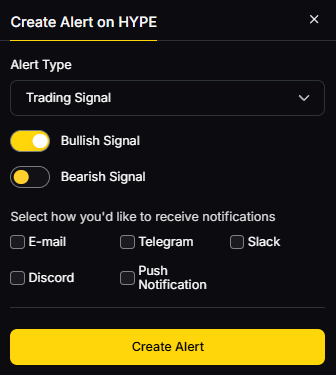
🚀 Using Token Metrics to Analyze Altcoins
Token Metrics is an advanced crypto analytics platform that leverages artificial intelligence and machine learning to help users find, analyze, and trade the best altcoins. It offers comprehensive data-driven insights tailored for both investors and advanced traders.
Platforms like Fidelity Crypto, which position themselves as marketplaces with a focus on transparency and regulatory compliance, are also gaining traction among investors seeking alternative ways to access crypto products and services.
Key Features for Altcoin Traders:
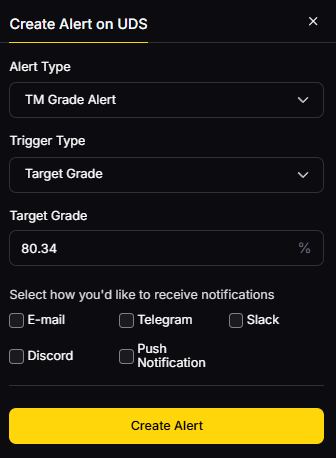
- Investor Grade & Trader Grade Scores: Evaluate long-term potential and short-term momentum.
- Bullish/Bearish Signals: Actionable alerts based on sophisticated indicators.
- Moonshots Section: Identify under-the-radar altcoins with explosive growth potential.
- Token Rankings: Daily updated rankings using technical analysis, on-chain data, and AI models.
- Portfolio Tools: Backtesting, asset allocation, and risk management features.
With over 80 data points analyzed per token, Token Metrics empowers users to filter noise from signal and uncover high-conviction altcoin opportunities before the broader market reacts.
👉 Interested investors can try Token Metrics’ 7-day free trial to explore altcoins like a pro.
🔮 Altcoin Trends in 2025
Several trends are shaping the altcoin landscape in 2025: Altcoins are now traded across global markets, with significant activity in regions like Singapore and South Korea, which are home to leading exchanges. Top exchanges offer access to a wide range of altcoins and trading pairs, making it easier for users to diversify their portfolios and benefit from increased liquidity and trading efficiency. Platforms differentiate themselves by providing the best customer service, including 24/7 support options and educational resources to help users navigate the evolving crypto environment. Users can easily sign up for new accounts and quickly buy or sell bitcoin and altcoins on these platforms, reflecting the growing ease of access and transaction execution in the crypto markets.
1. AI-Powered Tokens
Artificial intelligence has become integral to Web3 innovation. Tokens such as TMAI (Token Metrics AI) combine real-time data analytics with autonomous trading systems, enhancing decision-making for investors.
2. Narrative Investing
Altcoins connected to compelling narratives—such as Decentralized Physical Infrastructure Networks (DePIN), Real-World Asset tokenization, and zero-knowledge rollups (ZK-rollups)—are attracting significant attention. Platforms like Token Metrics help detect these emerging themes early.
3. Modular Blockchains
Projects like Celestia and Avail introduce modular blockchain designs, enabling faster, more flexible chain creation and unlocking new altcoin possibilities.
4. Regulation and Compliance
As U.S. and global regulations evolve, some altcoins are registering as digital securities or utility tokens to comply with legal frameworks, impacting their market dynamics.
5. Cross-Chain Interoperability
Altcoins facilitating asset transfers across multiple blockchains (e.g., Axelar, LayerZero) are gaining importance in the increasingly multi-chain crypto market.
Choosing the Right Exchange
Selecting the right crypto exchange is a crucial step for anyone looking to trade crypto or build a diverse portfolio of digital assets. With many crypto exchanges available, it’s important to evaluate each platform based on several key factors:
- Trading Volume and Liquidity: Top crypto exchanges with high trading volumes ensure smoother trades and better price execution, especially for larger orders.
- Fee Structure: Look for exchanges with transparent and competitive fees, including taker fees, maker fees, and any other charges that may apply to your trades.
- Trading Pairs and Advanced Order Types: The best platforms offer a wide selection of trading pairs and advanced order types, giving traders more flexibility and control.
- Payment Methods: Consider the available payment options, such as bank transfer, wire transfer, debit card, or digital wallet, to find what works best for you.
- Security Measures: Prioritize exchanges with strong security protocols, including two-factor authentication and cold storage for digital assets.
- Educational Resources and Copy Trading: Many crypto exchanges now provide educational resources and copy trading features, allowing users to learn from and replicate the strategies of experienced traders.
By carefully comparing these aspects across different exchanges, users can find the platform that best matches their trading style, security preferences, and investment goals.
Types of Exchanges
Understanding the different types of cryptocurrency exchanges can help traders choose the platform that best fits their needs and risk tolerance. The main types include:
- Centralized Exchanges (CEXs): These are managed by a third-party company that oversees the platform and holds users’ funds. Centralized exchanges are popular for their user-friendly interfaces, high liquidity, and comprehensive customer support, making them a go-to choice for many traders.
- Decentralized Exchanges (DEXs): Operating on blockchain technology, DEXs allow users to trade directly with one another without intermediaries. This peer-to-peer approach enhances privacy and control but may come with lower liquidity and fewer trading features compared to centralized platforms.
- Hybrid Exchanges: Combining the strengths of both centralized and decentralized models, hybrid exchanges aim to offer the security and transparency of DEXs with the speed and convenience of CEXs.
Each type of exchange has its own advantages and potential drawbacks, so it’s important for users to assess their trading priorities—such as security, ease of use, and available features—before choosing a platform.
🛠️ How to Buy Altcoins
Purchasing altcoins is straightforward with many crypto exchanges offering access to a wide variety of coins and trading pairs. Users can choose between:
Centralized Exchanges (CEXs)
- Coinbase: User-friendly platform ideal for beginners, known for its sleek user interface.
- Kraken: Known for strong security measures.
- Binance US: Offers low fees and high liquidity.
- Gemini: U.S.-regulated exchange with a focus on compliance and recognized as the top choice for security due to its sound security standards.
- Crypto.com: Best for mobile users who often trade on the go.
Decentralized Exchanges (DEXs)
- Uniswap: Popular on Ethereum and Layer-2 networks.
- PancakeSwap: Leading DEX on the BNB Chain.
- dYdX: Offers perpetual contracts with no KYC requirements.
For enhanced security and control, investors should use self-custody digital wallets like MetaMask or Ledger to store their crypto assets after purchase.
Payment methods vary by platform and include bank transfer, wire transfer, debit card, and other options. Understanding the fee structure, including taker fees and other fees, is essential to minimize costs.
Security and Safety on Exchanges
Security is a top concern for anyone trading or storing digital assets on crypto exchanges. The best crypto exchanges implement multiple layers of protection to safeguard users’ funds and personal information. Common security features include:
- Two-Factor Authentication (2FA): Adds an extra layer of account protection.
- Cold Storage: Keeps the majority of users’ assets offline, reducing the risk of hacks.
- Regular Security Audits and Software Updates: Ensures that the platform remains resilient against emerging threats.
- Insurance Coverage: Some exchanges offer insurance to cover potential losses from security breaches.
Before opening a new account, it’s essential to research an exchange’s security track record and the measures they have in place. Advanced traders, in particular, often prioritize security to protect their crypto portfolio and maintain peace of mind while trading. By choosing exchanges with strong security protocols, users can significantly reduce the risk of unauthorized access or loss of assets.
Fees and Charges
Understanding the fee structure of crypto exchanges is vital for maximizing trading profits and minimizing costs. Many crypto exchanges charge a variety of fees, including:
- Taker Fees and Maker Fees: These are charged when you place trades that either take liquidity from the market (taker) or add liquidity (maker).
- Deposit and Withdrawal Fees: Some platforms charge fees for moving assets in and out of your account, which can vary depending on the payment method, such as debit card, bank transfer, or wire transfer.
- Other Fees: Additional charges may apply for certain services or advanced trading features.
Low fees are a major focus for many traders, especially those who trade frequently or in high volumes. Some exchanges offer discounts or rewards for using their native tokens, holding a certain amount of assets, or participating in loyalty programs. By comparing the fee structures of different platforms, traders can choose the exchange that offers the best value for their trading style and payment preferences, helping them keep more of their profits in the fast-moving crypto market.
Final Thoughts
Altcoins represent the foundation of innovation within the cryptocurrency ecosystem. From enabling smart contracts and decentralized finance to supporting privacy features and AI-powered tools, altcoins offer vast opportunities for investors and developers alike. However, investing in altcoins requires careful research, an understanding of market trends, and awareness of the risks involved.
By leveraging sophisticated platforms like Token Metrics, investors and crypto traders can gain valuable insights, optimize their crypto portfolios, and navigate the complex altcoin market with greater confidence.
Whether you’re looking to buy crypto for the first time or expand your existing holdings, understanding altcoins is key to unlocking the full potential of the crypto market in 2025 and beyond.

.svg)

Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)













.svg)




.png)