
Best Crypto Exchanges: No KYC Platforms for Anonymous Trading in 2025

As privacy concerns intensify and global regulations around cryptocurrency tighten, many users in 2025 are actively seeking the best no KYC crypto exchanges—platforms that allow them to trade crypto or buy crypto without the need to upload identification documents. Whether motivated by privacy, geographical restrictions, or simply convenience, the demand for anonymous crypto trading has surged significantly. Users are encouraged to avoid storing assets on exchanges unless they are actively trading them to minimize risk.
Know Your Customer (KYC) protocols are designed to prevent fraud and money laundering, but they often come at the cost of user privacy. Fortunately, many decentralized and semi-centralized cryptocurrency exchanges now offer users the ability to buy, sell, and swap a wide range of cryptos without KYC, especially for smaller transactions or when using decentralized protocols. Decentralized exchanges require more technical expertise to navigate than centralized exchanges, but they provide a higher level of privacy. Cryptocurrency trading fees vary by exchange and are categorized as maker and taker fees. In this article, we will explore the best no-KYC crypto exchanges in 2025, highlighting their features, advantages, investing, and why they are ideal for anonymous or pseudonymous crypto trading.
Introduction to Crypto Trading
Crypto trading is the process of buying and selling digital assets—such as Bitcoin, Ethereum, and a wide range of altcoins—on specialized online platforms known as crypto exchanges. As the crypto market has expanded rapidly, many crypto exchanges have emerged to meet the needs of both new and experienced traders. Centralized exchanges usually offer a user-friendly interface suitable for beginners, making it easier for them to start trading. These platforms allow users to trade crypto with ease, offering access to a diverse selection of assets and trading pairs.
Top crypto exchanges are designed to provide high liquidity, low fees, and advanced order types, making it possible for traders to execute strategies efficiently and at scale. Many exchanges now go beyond simple spot trading, offering additional services like futures contracts, copy trading, and margin trading to attract advanced traders and retail investors alike. The average trading costs among top crypto exchanges include both trading fees and spreads, which can significantly impact overall trading expenses. This evolution has made it easier than ever to buy, sell, and manage digital assets, whether you’re looking to build a crypto portfolio, hedge your positions, or simply explore the fast-moving world of digital currencies.
With so many exchanges available, crypto traders can choose platforms that best fit their needs—whether they prioritize low fees, a wide range of supported coins, or innovative trading features. As the industry continues to grow, the competition among platforms ensures that users benefit from better services, improved security, and more opportunities to trade crypto in the global market. Maker fees range typically from 0.00% to 0.40%, while taker fees range from 0.05% to 0.60%, depending on the exchange and user trading volume. Exchanges with higher trading volumes tend to offer lower spreads based on market liquidity, which can be an important factor for cost-conscious traders.
⚠️ A Quick Note on No-KYC Exchanges
Before diving into the list, it’s important to understand a few key points about no-KYC crypto platforms:
- Most no-KYC exchanges are decentralized exchanges (DEXs), which operate without a central authority.
- Some centralized exchanges (CEXs) may allow limited trading without KYC below certain withdrawal or transaction thresholds.
- Regulations are evolving rapidly, so always verify the current compliance status of any platform you use.
- For maximum security and privacy, use a secure, non-custodial digital wallet when interacting with these platforms.
Benefits of No KYC Crypto Exchanges
No KYC crypto exchanges offer a distinct advantage for crypto traders who value privacy and want to access the crypto market without the hassle of identity verification. By removing the requirement to submit personal identification documents, these platforms make it easier for users to buy and sell digital assets quickly and anonymously. However, if your exchange fails, you could lose your investment, as U.S. Securities Investor Protection Corp. insurance does not apply to cryptocurrency. Exchanges protect users from losses due to site-wide hacks, but individual account attacks are the user's responsibility. This is especially appealing for those who wish to trade crypto without leaving a digital footprint or who face restrictions on traditional exchanges.
One of the key benefits of no KYC exchanges is the flexibility they provide. Users can often start trading immediately, using convenient payment methods such as debit card or bank transfer, without waiting for lengthy approval processes. Many exchanges feature a mobile app, which can enhance the user experience for traders on the go. This streamlined access allows traders to respond quickly to market movements and take advantage of new opportunities in the crypto market.
While some no KYC platforms may have higher fees or lower liquidity compared to their fully regulated counterparts, many crypto traders are willing to accept these trade-offs in exchange for greater privacy and control over their assets. The best crypto exchanges in this category are designed to balance ease of use with robust security, giving users the freedom to trade crypto on their own terms. Storing crypto in an exchange's wallet can leave you vulnerable to losses if the exchange suffers a cyberattack or fails. Whether you’re looking to buy, sell, or simply explore new digital assets, no KYC exchanges offer a valuable gateway to the world of anonymous crypto trading.
1. Token Metrics (via Self-Custody Integration)
Best For: Anonymous Traders Who Want AI-Powered Insights Before Using DEXs
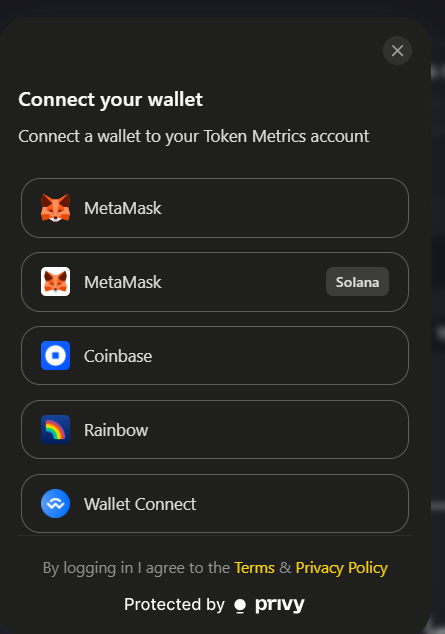
Token Metrics is not a traditional cryptocurrency exchange but rather a cutting-edge crypto analytics and AI trading platform. In 2025, it stands out as one of the most powerful tools for users who prefer no-KYC trading. Token Metrics connects seamlessly with your self-custodial wallet—such as MetaMask, Ledger, or Trust Wallet—allowing you to retain full control of your digital assets while benefiting from AI-powered bullish and bearish signals.
This platform helps traders spot promising crypto assets, including meme coins and emerging altcoins, before they pump in the market. Token Metrics offers comprehensive research, alerts, portfolio suggestions, and educational resources that help users understand crypto trading, all without requiring any personal information, making it an excellent companion for anyone planning to trade on decentralized exchanges like Uniswap or PancakeSwap.
Key Features:
- AI-based trading signals without needing an exchange account
- Compatible with popular self-custody wallets
- Helps identify potential moonshots and trading opportunities
- No KYC required to access core features
- Ideal for privacy-focused traders seeking data-driven insights
By using Token Metrics, crypto traders can make informed decisions while maintaining anonymity and security.
2. Uniswap (Ethereum & Layer-2 DEX)
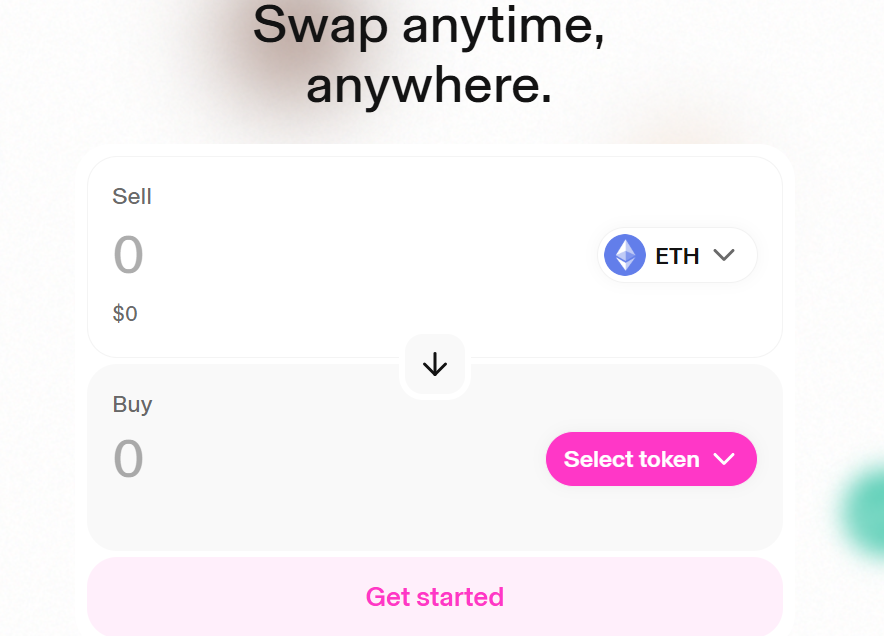
Best For: Anonymous ERC-20 Token Swaps
Uniswap remains the dominant decentralized exchange on Ethereum and its Layer-2 scaling solutions such as Optimism and Arbitrum. It offers users the ability to trade ERC-20 tokens directly from their wallets with no sign-up, no KYC, and no limits—perfect for anonymous crypto trading.
To trade on Uniswap, all you need is a self-custodial wallet like MetaMask or WalletConnect. Trading on Layer-2 chains reduces gas fees significantly, and Uniswap provides deep liquidity across a vast array of assets, including stablecoins, altcoins, and popular meme coins. Uniswap's consistently high trading volume further ensures efficient trades and competitive pricing. This makes it a top choice for users seeking to swap tokens without relying on centralized intermediaries.
Key Features:
- No KYC or account required
- Deep liquidity for ERC-20 tokens
- Available on Ethereum mainnet and Layer-2 networks (Arbitrum, Optimism, Base)
- Supports trading of stablecoins, meme coins, and other coins anonymously
Uniswap offers crypto traders a secure and efficient platform to access a broad range of digital currencies while safeguarding their privacy.
3. PancakeSwap (BNB Chain DEX)
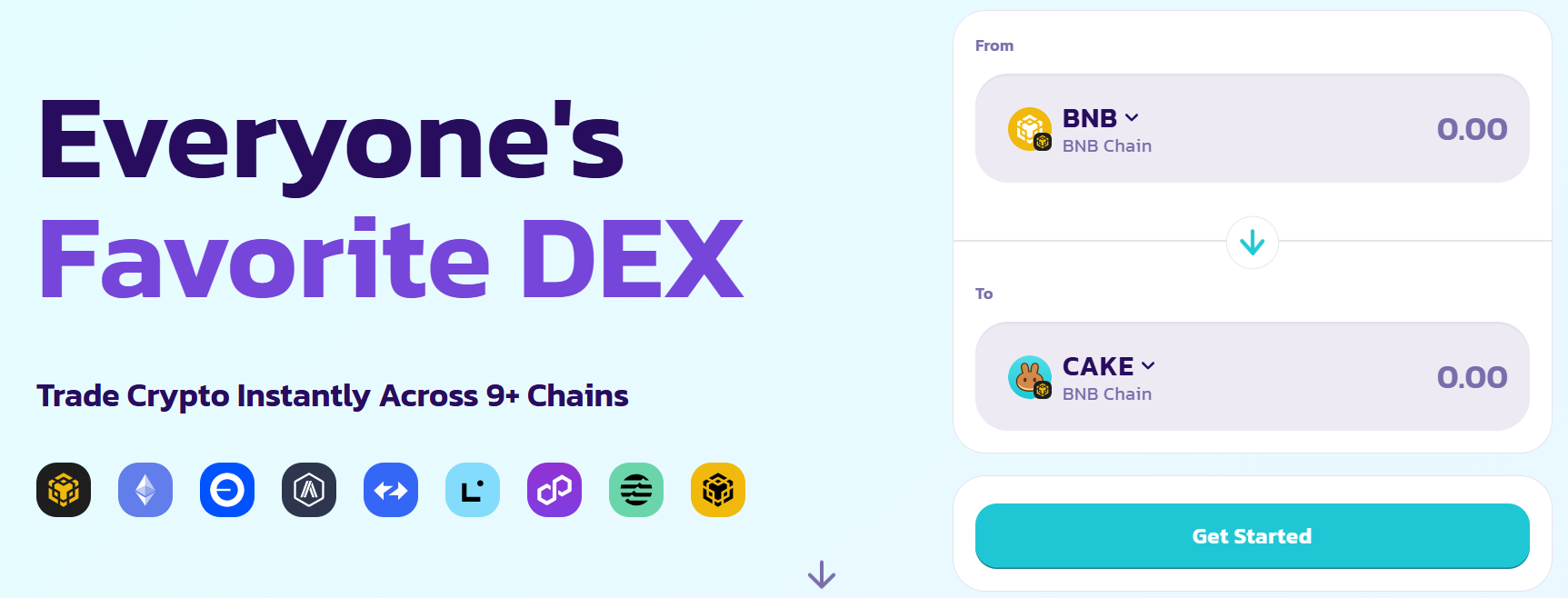
Best For: Fast, Cheap, No-KYC Trading on BNB Smart Chain
PancakeSwap is the leading decentralized exchange on the Binance Smart Chain (BNB Chain), delivering one of the best experiences for anonymous crypto trading with exceptionally low gas fees. No account creation or identity verification is necessary—simply connect your digital wallet and start trading.
PancakeSwap supports a wide variety of tokens, including popular meme coins, NFTs, and synthetic assets. Beyond trading, it offers features such as yield farming, staking, an NFT marketplace, and lottery integrations, making it a versatile platform for users who want to grow their crypto portfolio without compromising privacy.
Key Features:
- No KYC required to trade
- Supports BNB, BUSD, stablecoins, and numerous altcoins
- Extremely low transaction fees on BNB Smart Chain
- Additional crypto services like yield farming and staking
- NFT marketplace and lottery features integrated
PancakeSwap is ideal for users seeking low-cost, no-KYC trading combined with opportunities to earn rewards on the BNB Chain.
4. MEXC

Best For: Centralized Exchange With No KYC for Low Volumes
MEXC is one of the few centralized cryptocurrency exchanges that continues to allow users to trade crypto without completing KYC verification, albeit within certain daily withdrawal limits. In 2025, MEXC remains a favorite among traders who want access to centralized exchange features—such as leverage trading, limit orders, and a wide selection of token listings—without sharing personal identification. MEXC secures user accounts with robust security measures, including multi-factor authentication, to help protect assets and ensure account safety.
While KYC is mandatory for large withdrawals and fiat onramps, MEXC is well-suited for altcoin hunting and leverage trading for users who wish to maintain privacy within the platform’s withdrawal thresholds.
Key Features:
- Spot and futures trading available without KYC (within withdrawal limits)
- Extensive selection of tokens and frequent new listings
- Competitive low fees and taker fees
- Good liquidity on major trading pairs
MEXC offers a balanced solution for crypto traders who want the benefits of a centralized platform without fully compromising their anonymity.
5. dYdX (v4 Decentralized)
Best For: Anonymous Perpetual Trading on a DEX
In 2025, dYdX has transformed into a fully decentralized perpetual trading platform powered by the Cosmos SDK, eliminating reliance on centralized infrastructure. This upgrade enables users to trade with leverage, no KYC, and full custody of their crypto assets.
With dYdX v4, traders can engage in advanced financial instruments and margin trading with up to 20x leverage, all while maintaining privacy by connecting their self-custodial wallets. The platform also allows users to execute trades with high speed and efficiency, and offers professional-level analytics, making it the top choice for advanced traders who prioritize security and anonymity.
Key Features:
- No KYC required for trading
- Perpetual contracts with up to 20x leverage
- Fully decentralized and self-custodial
- High-performance execution on Cosmos infrastructure
- Advanced user interface and analytics tools
dYdX is the best crypto exchange for traders seeking decentralized margin trading without sacrificing privacy or security.
6. Bisq
Best For: Peer-to-Peer Bitcoin Trading with No KYC
Bisq is a peer-to-peer decentralized Bitcoin exchange that enables users to buy and sell bitcoin for fiat currencies or altcoins without any KYC requirements. It supports various payment methods, including bank transfer, Revolut, wire transfer, and even cash, making it highly versatile.
Operating as a desktop application integrated with the Tor network, Bisq offers one of the most privacy-preserving crypto trading experiences available. Its decentralized design means there is no centralized order book, and it incorporates built-in escrow and dispute resolution to protect users.
Key Features:
- Peer-to-peer BTC trading with no KYC
- Payment methods include bank transfers, wire transfer, and cash
- Tor network integration for enhanced privacy
- No centralized order book or control
- Secure escrow and dispute resolution mechanisms
Bisq is especially useful for users who want to buy or sell bitcoin anonymously and securely using traditional payment methods.
Final Thoughts: Choose Wisely When Going No-KYC
While no-KYC exchanges offer enhanced privacy and convenience, they come with certain risks. These include potential scams on decentralized platforms, limited customer support, and lack of recourse if issues arise. No-KYC exchanges may not offer the same level of protection or assistance to customers as regulated platforms. Phishing attacks can lead to individual account compromises, where users may unwittingly reveal passwords to cybercriminals. To minimize these risks, always:
- Use a secure digital wallet such as Ledger, MetaMask, or Rabby.
- Double-check contract addresses before initiating transactions.
- Avoid phishing links and suspicious websites.
- Leverage platforms like Token Metrics for thorough research before buying or selling crypto assets.
By combining informed decision-making with secure practices, you can navigate the no-KYC crypto market safely and effectively.
Top Picks by Use Case
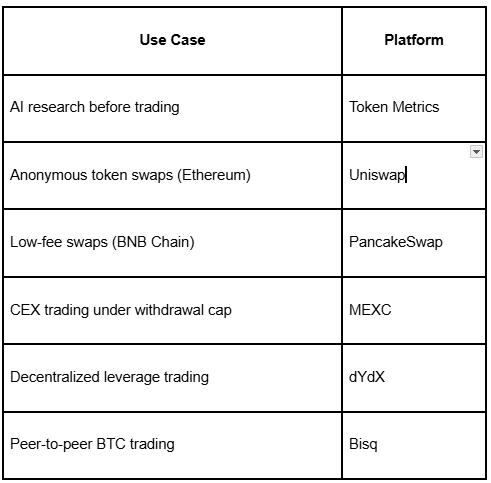
Using Token Metrics alongside one of these top crypto exchanges enables you to make data-backed decisions while preserving your privacy—an ideal strategy for crypto traders and investors in 2025.
By choosing from these best no-KYC crypto exchanges, users can maintain control over their crypto assets, access a diverse range of digital currencies, and enjoy secure, anonymous trading experiences tailored to their needs. Whether you are a retail investor, an advanced trader, or simply privacy-conscious, these platforms offer the tools and services necessary to thrive in the evolving crypto market. These platforms are selected not only for privacy but also for the quality of service they provide to users.

.svg)

Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)









.svg)




.png)