
Top 10 Crypto Exchanges in USA in 2025 | Secure and Affordable Trading

As the crypto market continues to expand rapidly across the United States, crypto traders and investors are on the lookout for the best crypto exchanges that combine security, low fees, a wide range of digital assets, and intelligent trading tools to optimize their investment strategies. These exchanges operate as business entities that facilitate the trading, buying, and custody of cryptocurrencies, playing a crucial role in the financial ecosystem. In 2025, the competition among U.S.-based cryptocurrency exchanges is fiercer than ever. From well-established platforms like Coinbase and Kraken to innovative AI-powered solutions such as Token Metrics, users have a wealth of options—and compelling reasons to choose carefully.
This article explores the best cryptocurrency exchanges in the USA in 2025, highlighting their standout features, benefits, and what differentiates each platform. Whether you are a retail investor just starting to buy crypto or an advanced trader seeking sophisticated analytics, this guide will help you find the right exchange to meet your needs by focusing on how these platforms serve their customers, emphasizing the importance of customer support and safety.
Introduction to Crypto Trading
Crypto trading is the process of buying and selling digital assets—such as bitcoin and other cryptocurrencies—on specialized online platforms known as crypto exchanges. As the crypto market has matured, many crypto exchanges have emerged, each offering unique features to meet the needs of a diverse range of traders. Whether you’re a newcomer or a seasoned trader, selecting the best crypto exchange is essential for maximizing your trading potential and safeguarding your assets.
Top crypto exchanges provide access to a wide variety of trading pairs, allowing users to trade between different cryptocurrencies and even fiat currencies. These platforms are designed to offer high liquidity, ensuring that trades can be executed quickly and at competitive prices. Security is a major focus, with leading exchanges implementing advanced protocols to protect users’ assets and personal information.
Another key consideration is the fee structure. The best crypto exchanges are transparent about their fees, offering low fees for trading and withdrawals to help traders keep more of their profits. Many exchanges also provide advanced order types, such as limit and stop orders, giving traders greater control over their trades. For those looking to expand their knowledge, educational resources are often available, covering everything from basic trading strategies to in-depth market analysis.
Ultimately, understanding the fundamentals of crypto trading, the available trading pairs, and the fee structure of each exchange will empower you to make informed decisions and succeed in the dynamic world of digital assets.
Token Metrics: One of the Best Crypto Exchanges and AI-Powered Trading Platforms in the USA (2025)
Token Metrics is not a conventional cryptocurrency exchange but rather a comprehensive crypto research, analytics, and AI trading platform. In 2025, it has emerged as a top choice among crypto traders and investors who prioritize smart insights before making any trade. Unlike many crypto exchanges that compete mainly on token listings or low fees, Token Metrics distinguishes itself by empowering users with data-driven decision-making.
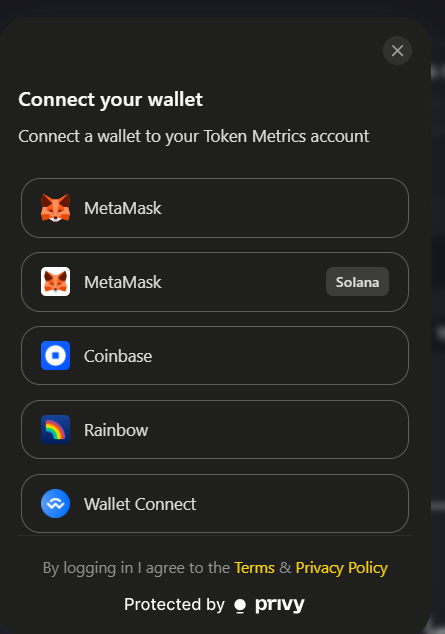
The platform connects to your preferred cryptocurrency exchange accounts via API or wallet integration, offering seamless compatibility with major exchanges such as Coinbase and Binance US. Token Metrics offers access across web, desktop, and mobile devices for maximum convenience. It provides AI-generated bullish and bearish signals, investor and trader grades, and custom alerts for thousands of tokens, covering a broad spectrum of crypto assets and a wide variety of cryptos available for analysis and trading. The spectrum of assets includes those with varying market cap, an important metric for assessing the prominence of different digital assets. This powerful approach helps users avoid hype traps and spot moonshots before they pump, enhancing the potential for profitable trades.
Key Features of Token Metrics:
- AI signals and token ratings based on over 80 on-chain and off-chain data points
- Embedded secure wallet giving users full control over their digital assets
- 24/7 Telegram alerts delivering real-time trade setups and market signals
- Integration with multiple crypto exchanges for easy trade execution
- Cross-device and regional access for maximum convenience
- Educational webinars and in-depth research reports to support informed investing
- Portfolio builder and backtesting tools to refine trading strategies
Token Metrics is best suited for traders and investors who want to supercharge their trading decisions with AI analytics and comprehensive crypto services. The platform offers a free plan, while premium subscriptions start at $199.99 per month with a 7-day free trial.
Coinbase – The Most Beginner-Friendly U.S. Crypto Exchange
Coinbase remains the most popular cryptocurrency exchange for beginners and casual investors in the USA due to its intuitive user interface, stringent U.S. regulatory compliance, and strong security protocols. As one of the best crypto exchanges widely used across the country, Coinbase’s public listing has helped it gain mainstream credibility and trust, supported by a large customer base. The platform places a strong emphasis on serving and protecting its customers, offering reliable customer support and robust safety measures.
In 2025, Coinbase continues to expand its offerings with features like Coinbase Advanced, catering to pro traders, and Coinbase Wallet, a secure digital wallet for storing and managing your crypto assets. Users can safely store their cryptocurrencies in Coinbase Wallet, ensuring their assets are protected. The platform also supports staking options, allowing users to earn rewards on their holdings. Integration with analytical platforms like Token Metrics enables users to analyze tokens before buying, enhancing decision-making.
Key Features of Coinbase:
- Simple buy/sell interface for major cryptocurrencies with multiple payment methods
- Supports bank transfers and debit card payments for buying cryptocurrencies
- Fully regulated and compliant with U.S. laws
- FDIC-insured USD storage for added security
- Access to staking, DeFi, and NFTs through Coinbase Wallet
- Extensive educational resources and crypto rewards for learning
Coinbase is best for first-time crypto buyers and long-term holders in the U.S. It charges no subscription fees, with trading fees starting around 1.49% per transaction.
Robinhood Crypto – Zero-Fee Crypto Trading for U.S. Investors

Robinhood Crypto has made a significant impact by offering zero-commission crypto trading, making it an attractive option for retail investors seeking to trade crypto without incurring high fees. In 2025, Robinhood supports a growing list of coins, offers recurring buys, and provides access to its self-custody wallet introduced in 2024.
Users can quickly sign up or sign in to their Robinhood accounts to start trading crypto right away. The platform regularly experiences high trading volume, reflecting its popularity among both beginners and advanced users. While Robinhood lacks advanced analytics and complex order types, its clean interface and no-fee model make it ideal for cost-conscious traders who want to start
Key Features of Robinhood Crypto:
- Commission-free trading for bitcoin, Ethereum, and other major digital currencies
- Fractional investing and recurring buy options
- Integrated self-custody wallet with NFT support
- Instant deposits and withdrawals for verified users
- Unified UI synced with stock and options accounts
Robinhood Crypto is best for retail traders who want zero-fee crypto trading and who may already use Robinhood for stocks. The platform is completely free for basic crypto trades.
Gemini – Regulated and Security-First U.S. Crypto Exchange
Gemini has earned a reputation as one of the most compliant and security-focused cryptocurrency exchanges in the U.S. It stands out in 2025 as a preferred platform for institutional investors and users who prioritize regulatory transparency and peace of mind.
Gemini offers a comprehensive suite of crypto services, including spot trading, staking, a crypto credit card with rewards, and high-yield accounts. Its user-friendly mobile app and secure custody solutions cater to both retail and institutional clients. Users can trade cryptocurrencies with varying market caps, gaining access to both established and emerging digital assets.
Key Features of Gemini:
- NYDFS-regulated exchange with strong compliance standards
- Gemini Earn for generating yield on crypto holdings (subject to regulations)
- Cold storage with insurance-backed custody for enhanced security
- Full range of crypto services including staking and custody
- Gemini Credit Card offering crypto rewards on purchases
- Industry-leading security protocols including two-factor authentication (2FA)
Gemini is best for users and institutions seeking top-tier security and regulatory assurance. Its fee structure is competitive, with discounts available for high-volume traders.
Kraken – Advanced Crypto Trading with a Trusted U.S. Exchange
Kraken is a long-standing favorite among professional traders in the U.S. due to its robust trading engine, deep liquidity, and extensive range of advanced order types. The platform consistently sees a large volume of digital assets traded, reflecting high activity and liquidity across its markets. In 2025, Kraken supports staking, futures, and margin trading, positioning itself as a full-service platform for experienced users.
Kraken Pro offers high-speed trading, API integrations, and customizable dashboards, appealing to advanced traders and institutions alike. The exchange is renowned for its top-tier security and regulatory transparency. Kraken also has a strong global presence, serving users in key international markets such as Singapore and South Korea.
Key Features of Kraken:
- Support for over 200 cryptocurrencies and numerous trading pairs
- High-yield staking options for major tokens
- Advanced charting tools, order types, and API access
- 24/7 customer support and extensive educational resources
- Fully regulated and compliant with U.S. laws
Kraken is best suited for advanced traders, institutions, and staking enthusiasts. Kraken Pro offers low fees, typically 0.16% maker and 0.26% taker fees, with minimal additional costs.
Binance US – Low Fees and Broad Access for American Traders

Binance US, the American branch of the global Binance exchange, is known for offering some of the lowest fees in the U.S. crypto market along with a broad selection of cryptocurrencies. The platform offers access to a wide variety of cryptos, including some that may be difficult to find elsewhere. While more limited in features than its global counterpart, Binance US provides a powerful platform for traders seeking low trading costs and extensive asset availability.
In 2025, Binance US continues to enhance its mobile app, expand coin listings, and add support for staking and recurring buys. It also integrates well with third-party analytics platforms such as Token Metrics, allowing users to combine smart research with execution.
Key Features of Binance US:
- Among the lowest fees in the U.S. crypto market (0.1% maker/taker fees)
- Large selection of cryptocurrencies for spot trading
- Advanced charting and trading tools for active traders
- Multiple payment methods including ACH, wire transfer, and debit cards
- Integration with analytics platforms for enhanced decision-making
Binance US is ideal for active traders looking for low fees and a wide variety of tokens. Discounts are available for users holding the BNB token.
Institutional Investors and Crypto Trading in the USA
Institutional investors are playing an increasingly prominent role in the U.S. crypto market, bringing significant capital and credibility to the space. With the rise of digital assets like bitcoin and Ethereum, many institutions are seeking new ways to diversify their portfolios and tap into the growth potential of crypto trading. The integration of crypto services by established names in traditional finance, such as Fidelity Crypto, has made it easier than ever for institutions to access and trade crypto.
These investors benefit from platforms that offer advanced trading features, including copy trading, futures, and robust security measures tailored to large-scale operations. High trading volumes and deep liquidity on leading exchanges ensure that institutions can execute large trades efficiently without impacting market prices. Additionally, specialized services such as dedicated account management, enhanced reporting, and compliance support are often available to meet the unique needs of institutional clients.
However, institutional investors must also navigate a complex regulatory environment and address security concerns to protect their assets. Despite these challenges, the potential for strong returns and portfolio diversification continues to drive institutional interest in digital assets. As more institutions enter the market, their participation is expected to boost overall trading volumes and liquidity, further solidifying the role of crypto trading in the broader financial ecosystem. The ongoing evolution of the crypto market suggests that institutional investors will remain key players in shaping its future.
Final Thoughts: Which U.S. Crypto Exchange Is Best in 2025?
With many crypto exchanges available in the U.S., choosing the best cryptocurrency exchange depends on your specific needs and trading style. Here’s a quick summary to help you decide:
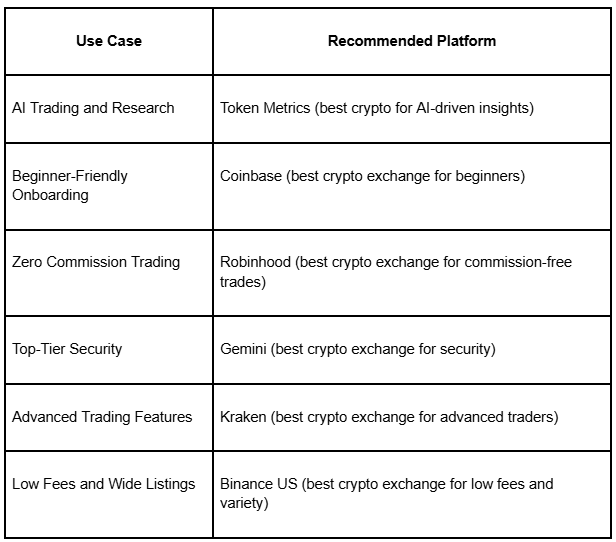
For optimal performance, many U.S. crypto traders combine Token Metrics with one or more of these best crypto exchanges. Token Metrics acts as a decision engine, using AI to identify top tokens, while the exchanges provide the execution layer for trades.=
In a landscape with many crypto exchanges to choose from, selecting the best crypto platform based on your individual goals is critical. Pairing your favorite exchange with powerful research tools like Token Metrics may well be the smartest move you make in 2025, helping you navigate the dynamic crypto market with confidence and success.

.svg)

Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)








.svg)




.png)