
Best Crypto Hardware Wallets for Security 2025

Why Crypto Hardware Wallets Matter in September 2025
If you hold crypto, your keys are everything—and the best hardware wallets still offer the strongest defense against malware, phishing, and exchange failures. A hardware wallet is a dedicated, offline signing device that stores private keys and authorizes transactions without exposing secrets to the internet. In 2025, rising on-chain activity and more sophisticated wallet-drainer attacks make physical key management table stakes for both retail and pros.
This guide is for investors, traders, and builders who want maximum security without killing usability. We compare leading devices across security architecture, open-source posture, coin coverage, UX, and ecosystem readiness—so you can match the right wallet to your risk profile and stack. Secondary considerations include “crypto hardware wallet” setup flows, “cold wallet” signing paths, and “secure crypto wallet” recovery options.
How We Picked (Methodology & Scoring)
- Liquidity (30%) → Practical access to ecosystems: native apps, partner integrations, staking/buy features, and compatibility with third-party wallets.
- Security (25%) → Secure elements, open-source/ reproducible builds, air-gapped flows (QR/PSBT), anti-exfiltration, audits, and recovery design.
- Coverage (15%) → Supported chains and tokens (BTC, ETH/L2s, EVM, Solana, etc.).
- Costs (15%) → Device price and any ongoing subscription/feature fees.
- UX (10%) → Screen size, inputs, mobile/Bluetooth, onboarding, backups.
- Support (5%) → Docs, firmware cadence, and customer support options.
We relied on official product and security pages, device docs, and transparency notes, using third-party market datasets only for cross-checks (no third-party links in body). Last updated September 2025.
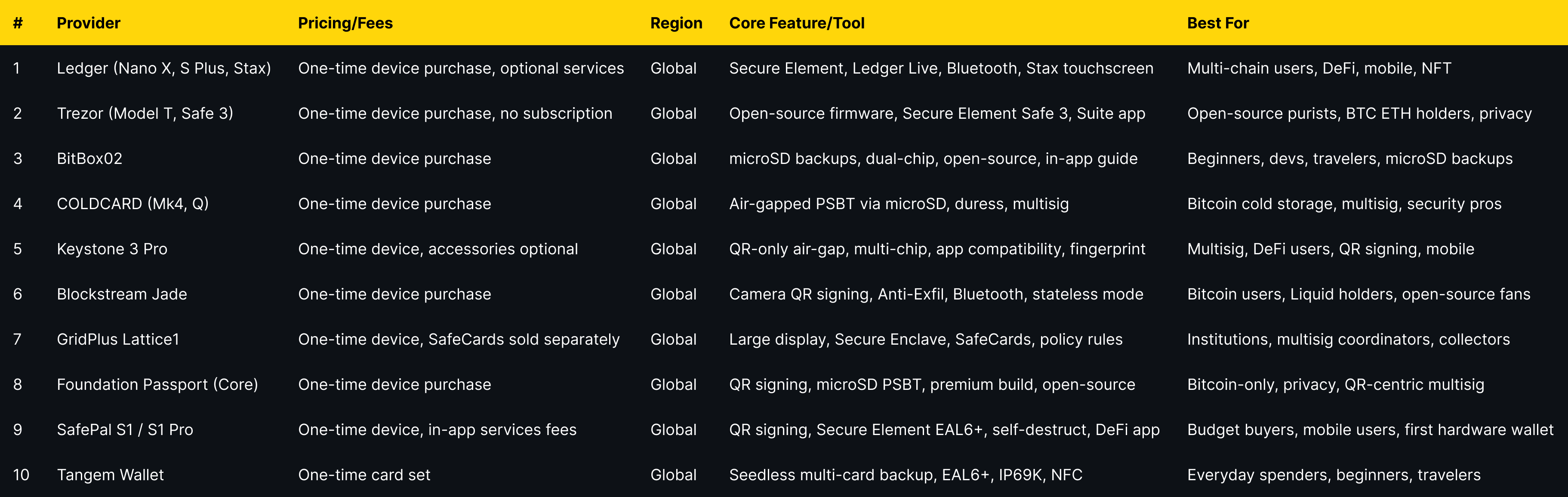
Top 10 Crypto Hardware Wallets for Security in September 2025
1. Ledger (Nano X • Nano S Plus • Stax) — Best for broad ecosystem + Secure Element
- Why Use It: Ledger pairs a Secure Element (CC EAL5+/EAL6+) with its BOLOS OS and a polished Ledger Live app for buy/swap/stake and 3rd-party wallet support. It’s the most ubiquitous stack, which means better app integrations and an easy path from cold storage to dApps when you need it.
- Best For: Multi-chain users, DeFi dabblers, mobile-first holders, NFT collectors.
- Notable Features: Secure Element, Ledger Live ecosystem, Bluetooth (Nano X), Stax E Ink touchscreen, optional Recover, 50+ wallet integrations.
- Consider If: You prefer fully open-source firmware elsewhere.
- Alternatives: Trezor, BitBox02
- Regions: Global
- Fees Notes: One-time device purchase; optional services may have fees.
2. Trezor (Model T • Safe 3) — Best open-source experience
- Why Use It: Trezor prioritizes open-source firmware, transparent security docs, and a clean desktop suite. The Safe 3 adds a Secure Element while keeping passphrase and on-device confirmations simple enough for new users.
- Best For: Open-source purists, long-term BTC/ETH holders, privacy-minded users.
- Notable Features: Trezor Suite, passphrase, open-source firmware, Secure Element (Safe 3), Bitcoin-only variant available.
- Consider If: You need Bluetooth/mobile-first; consider Ledger or Jade.
- Alternatives: Ledger, BitBox02
- Regions: Global
- Fees Notes: One-time device purchase; no subscription.
3. BitBox02 (Shift Crypto) — Best for microSD backups + minimalism
- Why Use It: Swiss-built, open-source, and elegantly simple, BitBox02 uses a secure chip plus epoxy potting and a microSD for fast, offline backups. It’s a great blend of transparent design and sane UX.
- Best For: Beginners who want a short setup, devs who value open code, travelers who like microSD backups.
- Notable Features: microSD backup/restore, dual-chip with secure element, open-source, in-app guide.
- Consider If: You need QR signing; look at Keystone or Passport.
- Alternatives: Trezor, Keystone
- Regions: Global
- Fees Notes: One-time device purchase.
4. COLDCARD (Mk4 / Q) — Best for Bitcoin-only, air-gapped PSBT
- Why Use It: Long favored by security maximalists, Coldcard is designed for fully air-gapped, PSBT-first workflows. Duress/tamper PINs, seed scrambling, and reproducible builds make it a fortress for BTC savings.
- Best For: Long-term Bitcoin cold storage, multisig operators, security pros.
- Notable Features: True air-gapped via MicroSD, PSBT (BIP174), anti-tamper features, duress/multisig tooling.
- Consider If: You need altcoins; choose Ledger, Trezor, or BitBox02.
- Alternatives: Passport, Jade
- Regions: Global
- Fees Notes: One-time device purchase.
5. Keystone 3 Pro — Best for QR signing across many chains
- Why Use It: Keystone focuses on fully air-gapped QR workflows—no USB, Bluetooth, Wi-Fi, or NFC—plus Shamir backups and strong multisig support. The 3 Pro adds three security chips and tight compatibility with leading wallet apps.
- Best For: Multisig setups, DeFi users who prefer QR signing, mobile users.
- Notable Features: QR-only air-gap, multi-chip architecture, wide app compatibility, fingerprint unlock, large screen.
- Consider If: You want a huge desktop screen (see Lattice1).
- Alternatives: Passport, Jade
- Regions: Global
- Fees Notes: One-time device purchase; optional accessories.
6. Blockstream Jade (Classic / Plus) — Best affordable open-source (Bitcoin & Liquid)
- Why Use It: Jade is open-source with optional air-gapped camera signing, Anti-Exfil, and a friendly app. It’s a strong value pick for Bitcoiners who still want modern conveniences like Bluetooth and battery power.
- Best For: Bitcoin users, Liquid asset holders, open-source fans.
- Notable Features: Camera for QR, air-gapped transactions, Anti-Exfil, Bluetooth, optional stateless mode.
- Consider If: You want more chains; consider Ledger/Trezor.
- Alternatives: COLDCARD, Passport
- Regions: Global
- Fees Notes: One-time device purchase.
7. GridPlus Lattice1 — Best for big screen review & SafeCards
- Why Use It: A 5" touchscreen and SafeCards make policy controls and multi-wallet management feel enterprise-grade. The Secure Enclave and card model are great for households, teams, or power users who hate “blind signing.”
- Best For: Institutions, multisig coordinators, collectors with many addresses.
- Notable Features: Large display, Secure Enclave, SafeCards for key portability/limits, policy rules, robust desktop UX.
- Consider If: You want ultra-portable or budget under $150.
- Alternatives: Ledger Stax, Keystone
- Regions: Global
- Fees Notes: One-time device purchase; SafeCards sold separately.
8. Foundation Passport (Core) — Best for QR + Bitcoin privacy flows
- Why Use It: Passport emphasizes QR signing, clean UX, and Bitcoin-only focus. Thoughtful hardware (camera, microSD) and transparent docs make it a favorite for air-gapped, privacy-first workflows.
- Best For: Bitcoin-only users, privacy fans, QR-centric multisig.
- Notable Features: QR signing, microSD for firmware/PSBT, premium build, open-source ethos.
- Consider If: You need altcoins/EVM—choose Ledger or Keystone.
- Alternatives: COLDCARD, Jade
- Regions: Global
- Fees Notes: One-time device purchase.
9. SafePal S1 / S1 Pro — Best budget air-gapped option
- Why Use It: SafePal delivers QR-based, fully air-gapped signing with a Secure Element (CC EAL6+) at a very accessible price point, plus a companion app for swaps and DeFi. Great for newcomers who still want true offline signing.
- Best For: Budget buyers, mobile users, “first hardware wallet.”
- Notable Features: QR signing, Secure Element (EAL6+), self-destruct/anti-tamper, rich app integrations.
- Consider If: You prefer fully open-source firmware (see Trezor/BitBox/Jade).
- Alternatives: Tangem, Ledger Nano S Plus
- Regions: Global
- Fees Notes: One-time device purchase; in-app services may incur fees.
10. Tangem Wallet (2- or 3-card set) — Best card-based, seedless recovery model
- Why Use It: Tangem uses NFC cards with an EAL6+ secure chip and a 25-year warranty, removing seed phrases in favor of multi-card backups. Tap-to-sign is intuitive, and the rugged, battery-free design suits travel and daily carry.
- Best For: Everyday spenders, beginners who fear seed phrases, travelers.
- Notable Features: Seedless multi-card backup, EAL6+ chip, IP69K-rated durability, NFC tap-to-sign, long warranty.
- Consider If: You want a traditional BIP39 seed and broad third-party wallet support.
- Alternatives: SafePal S1, Keystone
- Regions: Global
- Fees Notes: One-time card set; no charging required.
Decision Guide: Best By Use Case
- Broad multi-chain + best ecosystem: Ledger
- Fully open-source first: Trezor, BitBox02, Blockstream Jade
- Bitcoin-only vaulting: COLDCARD, Passport, Jade
- QR / air-gapped multisig: Keystone, Passport, Jade
- Large screen & team workflows: GridPlus Lattice1
- Budget under $100 (often): SafePal S1, Jade (promos), Trezor Safe 3
- Seedless, card-based: Tangem
- Mobile/Bluetooth convenience: Ledger Nano X, Jade
How to Choose the Right Hardware Wallet (Checklist)
- Confirm security model: Secure Element, open-source, air-gap/QR, PSBT.
- Match coverage to your assets (BTC-only vs multi-chain/EVM/Solana).
- Check ecosystem access: companion app, 3rd-party wallet support.
- Weigh UX: screen size, buttons/touch, Bluetooth, mobile pairing.
- Review recovery: BIP39/Shamir vs seedless cards; where you’ll store backups.
- Validate firmware cadence and support.
- Red flags: blind-signing unclear data; closed update channels; no documented security page.
Use Token Metrics With Any Hardware Wallet
Turn cold storage into a smarter strategy:
- AI Ratings to screen tokens you plan to hold.

- Narrative Detection to catch momentum early.
- Portfolio Optimization to size positions and balance risk.
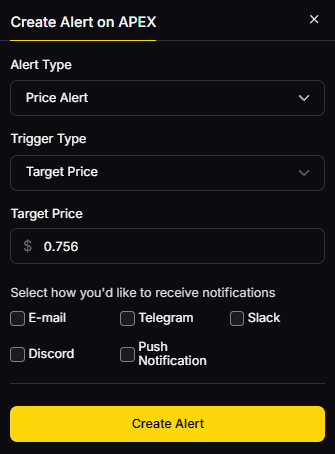
- Alerts & Signals to monitor entries/exits—without moving your keys.
Workflow: Research on Token Metrics → Pick assets → Acquire & secure with your wallet → Track performance + alerts.
Start free trial

Security & Compliance Tips
- Enable PIN + passphrase (where supported) and store backups offline.
- Prefer air-gapped/QR or PSBT flows for high-value moves.
- Verify addresses and amounts on-device; avoid blind signing.
- Keep firmware up to date; download only from official sources.
- Separate daily hot spending from long-term cold storage.
This article is for research/education, not financial advice.
Beginner Mistakes to Avoid
- Keeping the only seed phrase in a single location.
- Re-using the same device for testnets and main funds.
- Blind-signing smart-contract approvals you don’t understand.
- Leaving device uninitialized/unpinned in a desk drawer.
- Buying from unofficial marketplaces or “pre-set up” resellers.
FAQs
What is a hardware wallet?
A hardware wallet is a physical device that stores private keys and authorizes transactions offline, reducing exposure to malware and phishing compared to software wallets.
Do I need a hardware wallet if I use a centralized exchange?
If an exchange is hacked or freezes withdrawals, you can lose access. A hardware wallet lets you self-custody, so you control keys and recovery—many users keep long-term holdings in cold storage and only move funds when needed.
Is a Secure Element required?
Not required, but many devices use a CC EAL5+/EAL6+ Secure Element to resist physical extraction. Open-source firmware and verifiable builds also matter—evaluate the whole model, not just one spec.
What’s the difference between air-gapped QR and USB/Bluetooth?
QR/PSBT keeps signing data offline via camera or microSD. USB/Bluetooth devices can still be safe if the secret keys never leave the secure chip and screens verify data—choose the flow you’ll actually use correctly.
Can I use one wallet for multiple chains?
Yes—multi-chain devices (e.g., Ledger, Trezor, Keystone) support many networks. Bitcoin-focused devices (COLDCARD, Passport, Jade) prioritize BTC security and workflows.
How often should I rotate or back up?
Back up at setup, test recovery once, and review backups quarterly. Rotate seeds if you suspect exposure, or after major life changes.
Conclusion + Related Reads
If you want the widest ecosystem, Ledger is tough to beat. Prefer open-source? Trezor or BitBox02 are excellent defaults. For Bitcoin vaulting, COLDCARD, Jade, or Passport shine. Need team or household management? Lattice1. Budget-friendly air-gap? SafePal. Seedless and ultra-portable? Tangem.
Pick a model you’ll use correctly—then let Token Metrics guide what goes inside it.

.svg)

Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)








.svg)




.png)