
Best Practices for Storing and Accessing API Keys in Your Applications
API keys are a critical part of modern application development—enabling powerful third-party integrations while also presenting potential security risks. As APIs become the backbone of fintech, crypto, AI, and data applications, developers must ask: what are the safest and most scalable ways to store and access API keys? Let’s explore essential strategies, tools, and risks when handling sensitive API credentials.
Why API Key Security Matters
API keys function like digital passports, granting your application access to valuable services—from price feeds and SMS messaging to trading platforms and blockchain analytics. An exposed API key can lead to data leaks, unauthorized transactions, inflated bills, or even broader system compromise. High-profile data breaches, such as those resulting from public code repositories exposing secrets, underline the real-world impact of poor API key management.
Moreover, regulations and best practices in the crypto and AI industries demand robust security measures. Protecting API keys is not just about your own infrastructure—it’s about the trust your users and partners have in your platform.
Common API Key Storage Mistakes
Many security mishaps stem from common mistakes that are easy to avoid with the right protocols. These include:
- Hardcoding API keys in source code – This exposes keys in version control (e.g., GitHub), making them potentially public.
- Storing keys in client-side code – Any key shipped to the browser or mobile app can be extracted, leading to unauthorized API use.
- Committing .env or config files with secrets – Failing to exclude sensitive files from repositories is a frequent culprit in breaches.
- Sharing keys over unsecured channels – Email, chat, or shared docs aren’t secure environments for exchanging sensitive credentials.
Avoiding these pitfalls is a foundational step in API key security, but more sophisticated controls are often necessary as your application scales.
Proven Methods for Secure API Key Storage
To shield your API keys from breach and misuse, modern applications should utilize several technical best practices and tools:
-
Environment Variables:
- Environment variables keep secrets outside of your source code and can be managed per deployment (development, testing, production).
- Most frameworks (Node.js, Python, Java, etc.) support loading variables from a .env file not checked into git.
-
Secrets Management Platforms:
- Enterprise-grade solutions like AWS Secrets Manager, HashiCorp Vault, Google Secret Manager, or Azure Key Vault offer encrypted secret storage, fine-grained access control, and audit logs.
- Automate credential rotation and tightly restrict which services/components can access keys.
-
Server-Side Storage Only:
- Never expose sensitive API keys in client-side or public code. Keys should reside on a backend server that acts as a proxy or securely facilitates the necessary logic.
-
Configuration Management:
- Utilize configuration files for parameters but reference secrets via environment variables or secret manager APIs.
Additionally, always use least privilege principles: grant API keys only the permissions required for specific actions, and leverage IP allowlists or referrer checks where supported by the API provider.
Secure Methods for Accessing API Keys in Your Applications
How your application retrieves and uses API keys can be just as important as where they’re stored. Consider these approaches:
- Runtime Injection: Use secure deployment workflows (like CI/CD platforms) to inject secrets as runtime environment variables, ensuring they’re not embedded in disk snapshots.
- API Secrets Fetching: Advanced orchestration tools allow your app to fetch secrets at startup from a remote vault using temporary, tightly-scoped access tokens.
- Encrypted Storage: If secrets must reside on disk (e.g., for legacy apps), encrypt both the file and filesystem, and restrict OS-level permissions.
- Monitoring Access: Enable audit logging for each secret access, and set up alerts for anomalies like rapid key usage/rotation attempts.
Developers can further reduce risk by implementing rate limiting, automated key revocation/rotation, and zero trust policies—especially in large-scale or multi-developer environments.
Frameworks and Tools for API Key Management
Choosing the right tools can simplify and strengthen your API key security model. Some popular frameworks and services include:
- dotenv (Node.js), python-dotenv: Read environment variables from files excluded from version control.
- AWS Secrets Manager, Google Secret Manager, Azure Key Vault, HashiCorp Vault: Automated secrets storage, encryption, and access control, ideal for production-scale environments.
- Kubernetes Secrets: Manage secrets in containerized environments with role-based access control and workload isolation.
- CI/CD Secret Management: GitHub Actions, GitLab CI, and similar services let you define secret variables outside your repository for safe deployment workflows.
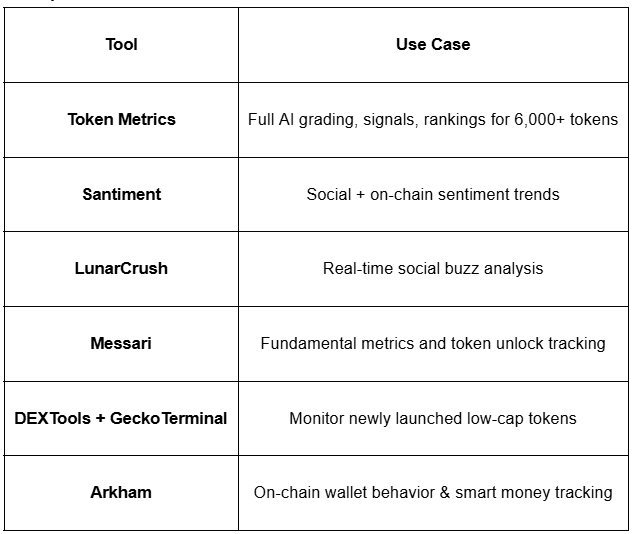
When connecting to crypto or AI services via API—such as Token Metrics—these tools make safe integration straightforward while maintaining regulatory compliance and auditability.
Build Smarter Crypto Apps & AI Agents with Token Metrics
Token Metrics provides real-time prices, trading signals, and on-chain insights all from one powerful API. Grab a Free API Key
FAQs on API Key Storage and Access
What happens if my API key is exposed?
If an API key is leaked, attackers could exploit your account to perform unauthorized transactions, scrape data, or exhaust your API limits. It’s essential to immediately revoke and regenerate compromised keys, audit usage, and identify the exposure vector.
Should I use the same API key in development and production?
No. Always generate separate API keys for each environment. This limits the impact of a potential leak and helps with auditing and troubleshooting.
Is it safe to store API keys in a database?
Only if the keys are encrypted at rest and the database access is strictly controlled. Prefer specialized secrets managers over general-purpose databases for handling sensitive keys.
How often should API keys be rotated?
Regular key rotation reduces risk from undetected exposures. The frequency depends on the sensitivity of the APIs in use—critical infrastructure often rotates every 90 days or less. Always rotate keys after a possible leak.
Can I share API keys with my team?
Share only through secure, auditable channels and never through unsecured messaging or docs. Use role-based permissions so each person has only the access they need, and revoke keys if team members leave.
Disclaimer
This content is provided for educational and informational purposes only. It does not constitute software security advice or an offer to buy or sell any financial product. Always perform your own due diligence and consult with appropriate professionals before implementing sensitive system changes.

.svg)

Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)













.svg)




.png)