
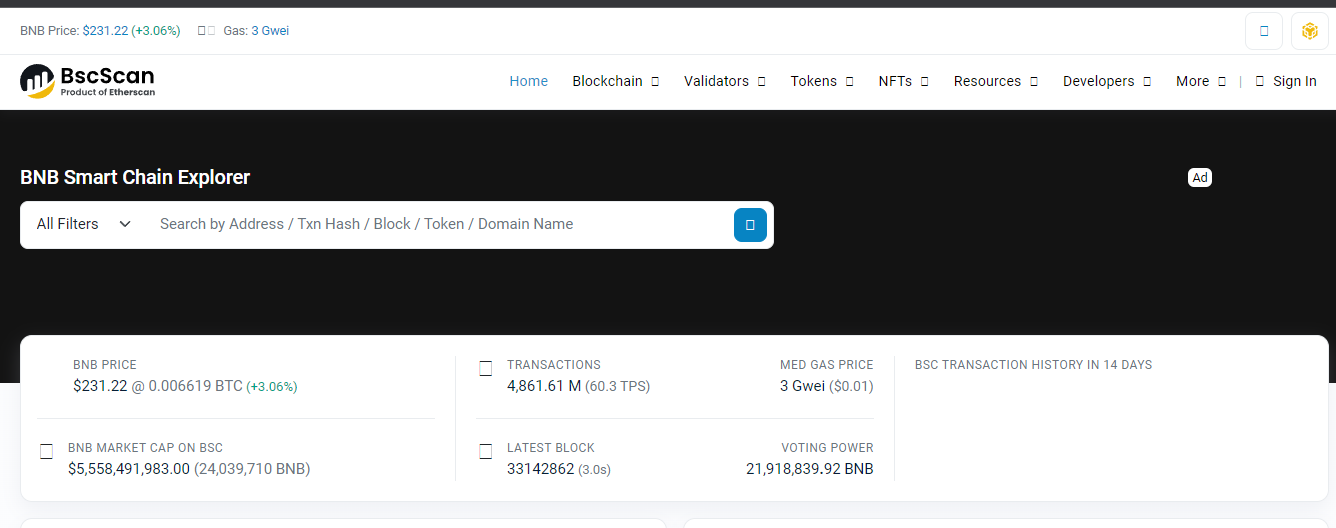
What is BscScan and How Does it Work?

Click here to buy Cryptocurrencies from Gate.io
Blockchain technology has revolutionized the world of finance and decentralized applications. As the popularity of cryptocurrencies grows, so does the need for reliable tools to navigate and explore different blockchain networks.
BscScan is a tool designed explicitly for the Binance Smart Chain (BSC). In this comprehensive guide, we will delve into the intricacies of BscScan, its functionalities, and how to make the most of this powerful blockchain explorer.
What is BscScan?
BscScan is the premier blockchain explorer for the Binance Smart Chain (BSC), developed by the same team responsible for creating Etherscan. Launched in 2020, BSC has rapidly gained popularity as a scalable and efficient blockchain network for decentralized applications and digital assets.
BscScan provides users with a comprehensive view of the BSC ecosystem, allowing them to explore wallet addresses, track transactions, verify intelligent contracts, and analyze token data.
As a blockchain explorer, BscScan acts as a search engine for the BSC network, providing real-time information about transactions, blocks, addresses, and smart contracts.
It offers a user-friendly interface that makes navigating and extracting valuable insights from the BSC blockchain accessible. Whether you are a developer, investor, or blockchain enthusiast, BscScan is an indispensable tool for interacting with the BSC network.
Understanding BscScan's Features
Real-Time Transaction Tracking
One of the core functionalities of BscScan is its ability to track transactions on the Binance Smart Chain in real time. By entering the transaction hash or wallet address, users can retrieve detailed information about a specific transaction, including the transaction amount, date, block number, balances, transaction fees, and status.
This feature is handy for individuals who want to monitor the progress of their transactions or verify the authenticity of a particular transaction on the BSC network.
Exploring Wallet Addresses
BscScan allows users to explore wallet addresses on the Binance Smart Chain, providing a comprehensive overview of transaction history, token balances, and other relevant information.
Users can access details such as BNB balance, BEP-20 token holdings, transaction data, and more by entering a wallet address into the search bar.
This feature enables users to gain insights into the activity of specific wallets and track the movement of digital assets on the BSC network.
Smart Contract Verification
Smart contracts are an integral part of the Binance Smart Chain ecosystem, enabling the creation and execution of decentralized applications.
BscScan offers an intelligent contract verification feature, allowing users to verify the authenticity and integrity of smart contracts deployed on the BSC network.
By comparing the compiled code of a smart contract with the code running on the blockchain, users can ensure that the contract functions as intended and mitigate the risk of potential vulnerabilities or malicious activities.
Token Tracking and Analysis
BscScan allows users to track and analyze tokens on the Binance Smart Chain. Users can access information about the top BEP-20 tokens, including prices, volume, market capitalization, number of holders, and cross-chain compatibility.
Additionally, BscScan supports ERC-721 and ERC-1155 tokens, making it possible to explore and track non-fungible tokens (NFTs) on the BSC network.
This feature is invaluable for investors and traders looking to stay updated on the performance and trends of different tokens within the BSC ecosystem.
Gas Price Monitoring
Gas fees are essential to any blockchain network, including Binance Smart Chain. BscScan offers a gas price monitoring feature, allowing users to view real-time information about gas fees on the BSC network.
By monitoring gas prices, users can make informed decisions about transaction fees and navigate the network efficiently. This feature is handy during periods of high network congestion when gas fees tend to fluctuate.
Using BscScan: Step-by-Step Guide
BscScan provides a user-friendly interface that makes it easy for users to navigate and extract valuable information from the Binance Smart Chain. In this step-by-step guide, we will walk you through using BscScan's key features.
Checking Transactions on BscScan
- Visit the BscScan website at bscscan.com.
- In the search bar at the top of the page, enter the transaction hash or wallet address you want to investigate.
- BscScan will query its database and display detailed information about the transaction, including the transaction amount, date, block number, balances, transaction fees, and status.
- Take note of the transaction status, which can be pending, successful, or failed. This information will help you determine the progress and outcome of the transaction.
- You can also explore additional details about the transaction by clicking on specific sections, such as the sender's address, recipient's address, or transaction hash.
Exploring Wallet Addresses
- On the BscScan homepage, locate the search bar at the top of the page.
- Enter the wallet address that you want to explore and press Enter or click the search icon.
- BscScan will provide an overview of the wallet address, including the BNB balance and the balances of any BEP-20 tokens held in the wallet.
- Scroll down to view the transaction history associated with the wallet address, including incoming and outgoing transactions.
- You can click on individual transactions to access more detailed information, such as the transaction hash, block number, and transaction fee.
Verifying Smart Contracts
- Navigate to the BscScan website and locate the "Verify Contract" section.
- Enter the smart contract address that you want to verify.
- Select the appropriate compiler type and open-source license type.
- Copy and paste the Solidity contract code into the designated field.
- Enable optimization by selecting "Yes" in the optimization dropdown menu if applicable.
- Click the "Verify and Publish" button to initiate the contract verification process.
- BscScan will compare the submitted code with the code running on the BSC network and provide a verification result indicating whether the contract code matches.
Tracking Tokens on BscScan
- Access the BscScan website and navigate to the "Tokens" section.
- Explore the top BEP-20 tokens listed on BscScan, including their prices, volume, market capitalization, and number of holders.
- Use the search bar to find specific tokens by their contract address or token symbol.
- Click on individual tokens for more detailed information, such as the token's contract address, token holders, transaction history, and related smart contracts.
- BscScan also supports ERC-721 and ERC-1155 tokens, allowing users to explore and track non-fungible tokens (NFTs) on the BSC network.
Monitoring Gas Prices
- Visit the BscScan website and locate the "Gas Tracker" section.
- Monitor the average gas price displayed on the page.
- Check the block size and average utilization to understand the current network congestion.
- Scroll down to view the BSC network's top gas guzzlers and spenders.
- Use this information to make informed decisions about gas fees and optimize your transactions on the Binance Smart Chain.
Click here to buy Cryptocurrencies from Gate.io
BscScan vs. Etherscan: Key Differences
While BscScan and Etherscan share similarities as blockchain explorers, the two platforms have some key differences. Here are the main distinctions:
- Supported Wallets: BscScan supports a limited number of wallets (e.g., MetaMask, TrustWallet) compared to Etherscan, which supports a broader range of wallets.
- Features: Etherscan has the advantage of offering Blockchain APIs and Crypto APIs, providing developers with more advanced functionalities for interacting with the Ethereum blockchain.
- Focus: BscScan is designed explicitly for the Binance Smart Chain, while Etherscan caters to the Ethereum network. Each explorer prioritizes features and data relevant to its respective blockchain.
BscScan and Etherscan are reputable and reliable explorers, offering valuable insights into their respective blockchain networks.
BscScan Alternatives
While BscScan is the leading blockchain explorer for the Binance Smart Chain, several alternative explorers are available for users. Here are a few notable options:
- Binance Chain Explorer: Developed directly by Binance, this explorer provides information about blocks, transactions, wallet balances, and BNB metadata. It is available both as a web and mobile application.
- BitQuery Explorer: BitQuery is a comprehensive explorer that supports multiple blockchains, including Binance Smart Chain. It offers advanced search and analytics capabilities for developers and researchers.
- Binance Explorer: Binance also provides its explorer for the Binance Smart Chain, offering similar functionalities to BscScan. It is a reliable alternative for users seeking a different interface or additional features.
These alternatives provide users with different interfaces and functionalities, allowing them to choose the explorer that best suits their needs.
Is BscScan Safe?
As a leading blockchain explorer, BscScan is developed by the same team behind Etherscan, which has established a strong reputation in the blockchain community.
BscScan is safe to use, as it does not require a connection to your BSC wallet and cannot access or acquire your funds. However, it is essential to exercise caution and verify that you are using the official BscScan website (bscscan.com) to avoid potential phishing attempts.
Always double-check the URL and ensure that you are on the correct website before entering any sensitive information.
Is BscScan Compatible with NFTs?
Yes, BscScan is fully compatible with non-fungible tokens (NFTs). Like Ethereum, the Binance Smart Chain hosts various NFT projects, taking advantage of its lower fees and higher efficiency.
Users can track their NFTs on BscScan using the transaction hash, NFT intelligent contract address, or wallet address. However, it is essential to note that BscScan does not display the artwork contained within an NFT.
Users must connect to a compatible marketplace or service provider supporting the specific NFT token standard to view the artwork.
Frequently Asked Questions
Q1. How to check if liquidity is locked on BscScan?
To determine if liquidity is locked for a specific token on BscScan, you can follow these steps:
- Go to the BscScan website and navigate to the "Tokens" section.
- Search for the token by its contract address or token symbol.
- Scroll down to the "Transfers" section and click on the transaction hash associated with the liquidity addition.
- Check if the liquidity pool tokens or a burn address were sent to the development wallet.
- Verify that the development wallet does not hold any liquidity pool tokens or check if they have been transferred to a burn address.
Q2. Can BscScan be used for other blockchain networks?
No, BscScan is designed explicitly for the Binance Smart Chain and cannot be used to explore other blockchain networks. Each blockchain has its dedicated explorer, such as Etherscan for Ethereum or Blockchain for Bitcoin.
If you need to explore a different blockchain, using the corresponding blockchain explorer for accurate and relevant information is recommended.
Q3. What are the advantages of using BscScan for yield farming?
BscScan offers several advantages for users engaged in yield farming on the Binance Smart Chain:
- Access the latest yield farming opportunities through the "Yield Farms List" feature.
- Detailed information about different farms, including their locations and how they work.
- The ability to track your yield farming activities, including the tokens you have staked and the rewards you have earned.
- Lower transaction fees compared to alternative platforms like Ethereum, making yield farming on BSC more cost-effective.
Q4. Can I revoke token approvals using BscScan?
Yes, BscScan provides the "Token Approval Checker" tool that allows users to review and revoke token approvals for decentralized applications (DApps).
Connecting your wallet to BscScan and using the Token Approval Checker lets you see which DApps can access your tokens and revoke their permissions if desired. This feature gives users more control over their token holdings and helps ensure the security of their assets.
Q5. How does BscScan ensure contract verification?
BscScan's contract verification process involves comparing the source code of a smart contract with the compiled code running on the Binance Smart Chain.
This process ensures that the code deployed on the blockchain matches the source code provided by the developer.
BscScan's verification process enhances transparency and security by allowing users to verify intelligent contracts' functionality and integrity independently.
Q6. What are the risks of using BscScan?
While BscScan is a reputable and reliable blockchain explorer, some risks are associated with using any online tool. It is essential to be cautious and follow best security practices when using BscScan or any other blockchain explorer:
- Ensure you use the official BscScan website (bscscan.com) to avoid phishing attempts.
- Double-check the URL and ensure that you are on the correct website before entering any sensitive information.
- Be wary of fake or malicious contracts, tokens, or DApps. Always conduct thorough research and due diligence before interacting with unknown projects.
- Keep your personal information and wallet details secure. Avoid sharing sensitive information with unknown individuals or platforms.
Q7. How can I contribute to the BscScan community?
If you are interested in contributing to the BscScan community, there are several ways to get involved:
- Participate in discussions on the BscScan forums or social media channels.
- Report any bugs or issues you encounter using BscScan to the development team.
- Provide feedback and suggestions for improving the platform's features and user experience.
- Contribute to the BscScan open-source project on GitHub if you have programming skills.
Your contributions can help enhance the functionality and usability of BscScan for the entire Binance Smart Chain community.
Conclusion
BscScan is a powerful and essential tool for navigating the Binance Smart Chain ecosystem. Whether you are an investor, developer, or blockchain enthusiast, BscScan provides valuable insights into the BSC network's transactions, smart contracts, tokens, and gas prices.
By leveraging BscScan's features, you can make more informed decisions, track your investments, and ensure the security of your digital assets. Explore BscScan today and unlock the full potential of the Binance Smart Chain.
Disclaimer
The information provided on this website does not constitute investment advice, financial advice, trading advice, or any other advice, and you should not treat any of the website's content as such.
Token Metrics does not recommend that any cryptocurrency should be bought, sold, or held by you. Conduct your due diligence and consult your financial advisor before making investment decisions.
Click here to buy Cryptocurrencies from Gate.io

.svg)

Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)





















.svg)




.png)