
What is Copy Trading and How to Use it for Better Returns?

In the world of cryptocurrency trading, a strategy has been gaining popularity among traders of all experience levels - copy trading.
By leveraging the expertise of other successful traders, copy trading allows you to replicate their trades automatically and potentially earn profits without having to make trading decisions on your own.
In this guide, we will delve into the concept of crypto copy trading, how it works, the pros and cons, and how you can develop an effective copy trading strategy.
What is Copy Trading?
Copy trading is a form of investment that allows you to mirror the trades of successful traders. Instead of conducting extensive market research and analysis, copy trading enables you to identify profitable traders on a copy trading platform and automatically replicate their trades in your own trading account.
This strategy particularly appeals to those new to trading or lacking the time and expertise to make trading decisions. Copy trading lets you choose the traders you want to follow based on their trading style, risk tolerance, and past performance.
Once you have selected a trader to copy, their trades will be executed in your account in real-time, proportionally to the amount of capital you have allocated to them. This means that if the trader you are copying opens a buying position on Bitcoin, the same trade will be executed in your account.
How Does Crypto Copy Trading Work?
Crypto copy trading is a universal concept that can be applied to various financial markets, including cryptocurrencies. Cryptocurrencies have gained significant popularity in recent years, attracting both experienced traders and newcomers to the market.
Copy trading in the crypto space allows you to leverage the expertise of successful cryptocurrency traders and potentially profit from their trading strategies.
To start copy trading in the crypto market, you need to open an account with a copy trading provider that offers access to cryptocurrencies.
Once you have opened an account, you can browse through the available traders on the platform and choose the ones that best match your trading goals and risk appetite.
After selecting the traders you want to copy, the copy trading platform will automatically replicate their trades in your trading account. It's important to note that while copy trading allows you to benefit from the expertise of other traders, it does not guarantee profits.
The success of your copy trading strategy will depend on the performance of the traders you choose to follow and the overall market conditions.
Copy Trading Strategy
Developing an effective copy trading strategy is crucial for maximizing your chances of success in the market. While copy trading eliminates the need for extensive market analysis, it's important to carefully select the traders you want to copy and manage your risk effectively.
Here are some key points to consider when developing your copy trading strategy:
- Tradeable Markets: Consider the markets that the traders you are copying focus on. Some traders may specialize in specific cryptocurrencies, while others may have a more diversified approach. Choose traders whose trading style aligns with your preferred markets.
- Risks: Determine how much capital you will allocate to each trader and how you will manage your overall risk. Many copy trading platforms allow you to set a maximum loss or allocate a specific percentage of your trading account to each trader. Diversification is important to mitigate risks.
- Market Analysis: Although you are copying the trades of successful traders, it's still important to monitor your copied trades and make adjustments if market conditions change. Stay informed about the market trends and news that may impact the trades you are copying.
- Leverage: Decide whether you want to copy trades on leverage. While leverage can amplify profits, it also increases the risk. Only invest what you can afford to lose and be aware of the potential risks associated with leveraged trading.
Pros and Cons of Copy Trading
Like any trading strategy, copy trading has its own set of advantages and disadvantages. Here are some of the pros and cons to consider before engaging in copy trading:
Pros:
- Automated Trading: Copy trading allows you to automate your trading by following successful traders. Once you have selected the traders you want to copy, their trades will be executed in your account automatically, saving you time and effort.
- Learning Opportunity: Copy trading provides an excellent learning opportunity for traders. By observing their trading decisions and strategies, you can gain valuable insights into the market and improve your trading skills.
- Diversification: Copy trading allows you to diversify your portfolio by following multiple traders with different trading styles. This can help reduce the overall risk and potentially increase your chances of profiting in various market conditions.
Cons:
- Dependency on Trader Performance: Your trading results in copy trading are directly tied to the performance of the traders you follow. If a trader makes a bad trade, it will also affect your account. Choosing traders with a proven track record and monitoring their performance regularly is important.
- Market Risk: Copy trading exposes you to market risks like any other form of trading. Fluctuations in cryptocurrency prices and market conditions can impact the profitability of the trades you copy.
- Execution Risk: There is a risk of slippage and execution delays in copy trading. If the market moves rapidly, there may be a difference between the price at which a trader opens a trade and the price at which it is executed in your account.
How to Use Copy Trading Strategy?
Using a copy trading strategy is relatively straightforward. Here's a step-by-step guide to getting started with copy trading:
- Choose a Copy Trading Provider: Open an account with a reputable copy trading provider that offers access to cryptocurrencies.
- Select Traders to Copy: Browse through the available traders on the platform and choose the ones that align with your trading goals and risk appetite. Consider factors such as their past performance, risk level, and trading style.
- Allocate Funds: Decide how much capital you want to allocate to each trader you are copying. Diversifying your allocation and not putting all your eggs in one basket is important. Many copy trading platforms allow you to set a maximum loss or allocate a specific percentage of your trading account to each trader.
- Monitor Performance: Regularly monitor the performance of the traders you are copying. Monitor their trading results, risk management strategies, and overall market conditions. Consider adjusting your copy trading strategy if a trader's performance deteriorates or market conditions change.
- Adjust Allocation: As you gain more experience and confidence in copy trading, you can adjust your allocation to different traders. You may choose to increase or decrease the amount of capital allocated to a specific trader based on their performance.
Remember that copy trading is not a guaranteed path to profits. It's essential to conduct thorough research, choose traders wisely, and continuously monitor your copy trading strategy to ensure its effectiveness.
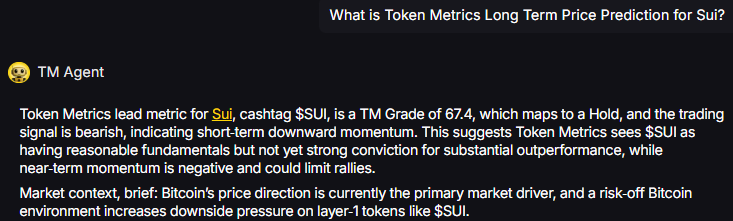
How Token Metrics Can Help You?
If you want to invest in crypto passively, you can copy the alpha of other traders. So Token Metrics was an early contributor to an open-source project called Astradao.
With Astradao, an open-source project operating as an index marketplace, investors gain access to a diversified portfolio effortlessly.
Token Metrics Ventures, a fund with multiple indices on Astradao, encourages investors to explore and copy trade these indices. Furthermore, investors can create and launch their indices, allowing others to invest in the same digital assets.
Is Copy Trading Profitable?
The profitability of copy trading depends on various factors, including the performance of the traders you are copying, market conditions, and your risk management strategies. While copy trading can potentially lead to profits, it is not without risks.
To increase your chances of profitability in copy trading, it's important to:
- Choose Traders Wisely: Select traders with a proven track record of success and a trading style that aligns with your goals.
- Diversify Your Portfolio: Allocate your capital to multiple traders with different trading strategies to reduce the overall risk.
- Monitor Performance: Regularly review the performance of the traders you are copying and make adjustments if necessary.
- Stay Informed: Stay updated on market trends, news, and events that may impact the trades you are copying.
By following these guidelines and continuously improving your copy trading strategy, you can potentially increase your profitability in the crypto market.
Frequently Asked Questions
Q1. How do I choose traders to copy?
When choosing traders to copy, consider factors such as their past performance, risk level, trading style, and market expertise.
Q2. Can I adjust my allocation to traders?
Yes, you can adjust your allocation to different traders based on their performance and your risk management strategies.
Q3. What should I consider when monitoring trader performance?
When monitoring trader performance, consider factors such as their trading results, risk management strategies, and overall market conditions.
Q4. Are there any fees involved in copy trading?
Some copy trading platforms may charge fees for using their services, and you may also need to pay fees to the traders you are copying.
Q5. Can I manually close a copied trade?
Depending on the copy trading platform, you may have the option to manually close a copied trade if you feel it is necessary.
Q6. Is copy trading suitable for beginners?
Copy trading can be suitable for beginners as it allows them to leverage the expertise of successful traders without extensive market knowledge.
Q7. Can I copy trade on leverage?
Some copy trading platforms offer the option to copy trades on leverage, but it's important to understand the risks involved and only invest what you can afford to lose.
Q8. How can I get started with copy trading?
To get started with copy trading, open an account with a copy trading provider, choose traders to copy, allocate funds, and monitor performance.
Q9. Is copy trading a guaranteed way to make profits?
Copy trading is not a guaranteed way to make profits. Success in copy trading depends on various factors, including trader performance and market conditions.
Conclusion
Copy trading offers an accessible and potentially profitable way to engage in cryptocurrency trading. By leveraging the expertise of successful traders, you can learn from their strategies and potentially earn profits without extensive market knowledge.
However, it's essential to understand the risks involved and develop a well-defined copy trading strategy. With proper research, risk management, and continuous monitoring, you can make the most of copy trading in the crypto market.
Remember, copy trading is a strategy that requires continuous monitoring and adjustment. It's important to stay informed, manage your risk effectively, and choose traders wisely to increase your chances of success in the market.
Disclaimer
The information provided on this website does not constitute investment advice, financial advice, trading advice, or any other advice, and you should not treat any of the website's content as such.
Token Metrics does not recommend buying, selling, or holding any cryptocurrency. Conduct your due diligence and consult your financial advisor before making investment decisions.

.svg)

Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)
















.svg)




.png)