Crypto Lending Explained - Benefits, Risks and Top Lending Platforms in 2023

Are you looking for a new way to invest your cryptocurrency? Or perhaps you're in need of a loan, but tired of dealing with traditional financial institutions. If so, you may want to consider crypto lending.
Crypto lending is a relatively new phenomenon that's gaining popularity among investors and borrowers alike. It's a form of peer-to-peer lending where individuals or institutions can lend or borrow cryptocurrency, such as Bitcoin or Ethereum, using a decentralized platform.
In this article, we will cover a comprehensive overview of crypto lending, including its functionality, benefits, risks, and the leading platforms for crypto lending in 2023.
What is Crypto Lending?
Crypto lending is a service within the decentralized finance (DeFi) ecosystem that enables investors to lend out their cryptocurrency holdings to borrowers. As a lender, you earn regular interest payments on your crypto deposits, similar to how you would earn interest in a traditional savings account.
Crypto lending platforms can either be centralized or decentralized, and they offer varying interest rates depending on the platform and other factors.
On the other hand, borrowers can use cryptocurrency lending platforms to obtain cash loans by collateralizing their crypto holdings. By posting collateral, borrowers can access funds without having to sell their crypto holdings, which can be beneficial during market downturns.
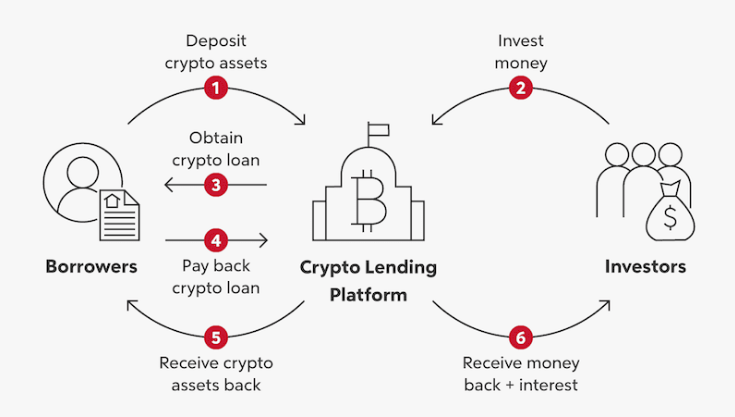
How Does Crypto Lending Work?
To participate in crypto lending, you'll need to find a reputable platform that offers this service. There are several platforms out there, such as Nexo, BlockFi, and Celsius Network, to name a few.
Once you've found a platform you trust, the process is fairly straightforward. Here's a step-by-step guide to how crypto lending works:
Step 1: Create an Account - The first step in crypto lending is to create an account on the platform of your choice. This usually involves providing some personal information (KYC), such as your name and email address, and creating a password.
Step 2: Deposit Cryptocurrency - Next, you'll need to deposit cryptocurrency into your account. This will be the cryptocurrency that you use to lend or borrow funds.
Step 3: Choose a Lending or Borrowing Option - Once your account is set up and your cryptocurrency is deposited, you can choose whether you want to lend or borrow funds. If you're looking to lend, you can select a lending option that meets your needs. This may involve choosing the cryptocurrency you want to lend, the interest rate you want to charge, and the length of the loan term.
If you're looking to borrow, you can select a borrowing option that meets your needs. This may involve choosing the cryptocurrency you want to borrow, the interest rate you're willing to pay, and the length of the loan term.
Step 4: Wait for Approval - Once you've selected your lending or borrowing option, you'll need to wait for approval. This may involve a credit check or other verification process, depending on the platform you're using.
Step 5: Receive Funds - If you're approved, you'll receive the funds in your account. If you're lending, the borrower will receive the cryptocurrency they've borrowed. If you're borrowing, you'll receive the cryptocurrency you've borrowed.
Step 6: Make Payments - If you're borrowing, you'll need to make regular payments to repay the loan. This will usually involve paying interest on a monthly basis. If you're lending, you'll receive regular payments from the borrower, which will include the interest you've charged.
Step 7: Close the Loan - Once the loan term is over, you'll need to repay the full amount of the loan, plus any outstanding interest. If you're lending, you'll receive your cryptocurrency back, along with the interest you've earned. If you're borrowing, you'll need to repay the cryptocurrency you've borrowed.
How to Make Money with Crypto Lending?
Crypto lending can be an effective way to earn passive income with your cryptocurrency holdings. Here are some important things to know, to make money with crypto lending:
- Choose a reputable crypto lending platform: Selecting a reliable platform is crucial for successful crypto lending. Look for platforms with a proven track record, solid security measures, and transparent lending terms.
- Determine your lending strategy: Decide on the amount of crypto you want to lend out and for how long. Longer lending periods often yield higher returns, but also carry more risk.
- Set competitive interest rates: Set an interest rate that's competitive with other lending platforms. A higher rate may attract more borrowers, but also increases the risk of defaults.
- Manage your risk: Conduct thorough due diligence on potential borrowers and keep a diversified portfolio to mitigate risk. Additionally, consider collateral requirements and loan-to-value ratios when selecting borrowers.
- Reinvest your earnings: Reinvesting your earned interest can compound your returns over time, increasing your overall profits.
By following these tips, you can effectively make money with crypto lending while managing your risk and ensuring a stable return on your investment.
Also Read: How to Make Money with Cryptocurrency in 2023
Best Crypto Lending Platforms in 2023
Identifying the ideal lending platform that caters to your requirements can be a daunting task, given the vast number of options available in the market. To help you make an informed decision, we have curated a list of the best crypto lending platforms that you can consider in 2023.
Celsius Network: With over $20 billion in crypto assets under management, Celsius Network is a trusted and well-established platform for crypto lending. It offers competitive interest rates, ranging from 2.5% to 13.99%, depending on the cryptocurrency you lend and the loan duration.
BlockFi: BlockFi is another leading crypto lending platform that offers interest rates ranging from 0.5% to 8.6%, depending on the cryptocurrency and loan terms. It also provides additional services such as crypto-backed loans and a Bitcoin rewards credit card.
Nexo: Nexo is a popular platform for instant crypto loans, and it allows users to earn up to 12% interest on their crypto assets. It also provides a range of other features, such as crypto-backed loans and a credit card.
Crypto.com: Crypto.com is a leading cryptocurrency platform that offers interest rates of up to 8.5% on a range of cryptocurrencies, including Bitcoin, Ethereum, and stablecoins. It also provides other features such as a crypto debit card and an exchange platform.
When choosing a crypto lending platform, it's essential to consider factors such as the interest rates offered, the loan terms, and the platform's overall reputation and security measures. By selecting a reliable and trustworthy platform, you can ensure that your crypto lending investments are safe and profitable.
Benefits and Risks of Crypto Lending
Crypto lending has been gaining significant traction lately due to the potential benefits it offers to both lenders and borrowers. However, like any financial activity, there are also some inherent risks involved.
Lets understand the benefits and risks associated with crypto lending in detail.
Crypto Lending Benefits
Here are some benefits of crypto lending:
High returns: One of the most significant advantages of crypto lending is the potential for high returns. Many lending platforms offer APYs upwards of 10%, which is significantly higher than traditional savings accounts.
Diversification: Crypto lending provides an opportunity for diversification in your investment portfolio, which can help mitigate risks.
Flexibility: Crypto lending platforms offer more flexibility than traditional financial institutions, with features such as short-term lending, early withdrawal options, and customized loan terms.
Risks Associated with Crypto Lending
Here are some risks associated with crypto lending:
Volatility: The crypto market is known for its volatility, which can impact the value of your investments and potentially lead to losses.
Counterparty risk: When lending your crypto assets to borrowers, there is always a risk that they may default on their loan, leading to a loss of your funds.
Security risks: Crypto lending platforms are not immune to hacking attempts, which can result in the loss of your funds.
The Bottom Line
Overall, crypto lending provides a win-win solution for both lenders and borrowers in the DeFi ecosystem. Lenders earn passive income on their crypto deposits, while borrowers can access much-needed funds without liquidating their cryptocurrency investments.
In conclusion, the crypto lending industry is rapidly expanding, and there are plenty of great options available for investors looking to earn passive income on their crypto holdings. Whether you choose Celsius Network, BlockFi, Nexo, YouHodler, or Crypto.com, it's crucial to conduct your due diligence and select a platform that meets your specific needs and goals.
Disclaimer
The information provided on this website does not constitute investment advice, financial advice, trading advice, or any other sort of advice and you should not treat any of the website's content as such.
Token Metrics does not recommend that any cryptocurrency should be bought, sold, or held by you. Do conduct your own due diligence and consult your financial advisor before making any investment decisions.
Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)








.svg)




.png)