
Top 10 Crypto Portfolio Trackers - Complete List
Click here to trade cryptos at MEXC!
Contact us at promo@tokenmetrics.com for marketing and sponsorship programs.
Cryptocurrencies have gained significant popularity in recent years, attracting both investors and enthusiasts. As the crypto market continues to expand, it becomes essential for individuals to effectively manage and track their crypto portfolios.
This article explores the top 10 crypto portfolio trackers available in the market, providing insights into their features, benefits, and functionalities. Let's start with the basics -
What is a Crypto Portfolio Tracker?
Crypto portfolio trackers are software applications or online platforms that allow users to manage and monitor their cryptocurrency investments in a centralized and organized manner.
These trackers provide real-time information on portfolio performance, asset allocation, transaction history, and market trends.
By using a crypto portfolio tracker, investors can make informed decisions, track profits, and streamline their crypto investment strategies.
Importance of Tracking Crypto Portfolios
Tracking a crypto portfolio is crucial for several reasons. Firstly, it provides an overview of the performance of different cryptocurrencies within the portfolio, enabling users to identify which assets are performing well and which ones may require adjustments.
Secondly, it helps investors stay updated with the latest market trends, news, and price fluctuations, allowing them to make timely investment decisions. Lastly, tracking portfolios simplifies tax reporting, as it provides accurate records of transactions and holdings.
Click here to trade cryptos at MEXC!
List of Best Crypto Portfolio Trackers
In recent time, several crypto portfolio trackers gained significant popularity and widespread usage among investors. Here is the list of few popular crypto portfolio trackers -
1. Token Metrics
Token Metrics crypto portfolio tracker is a comprehensive and sophisticated tool designed to help crypto investors effectively manage and track their digital assets.
With its intuitive interface and robust features, the portfolio tracker enables users to seamlessly monitor their investments across multiple exchanges and wallets in real-time.
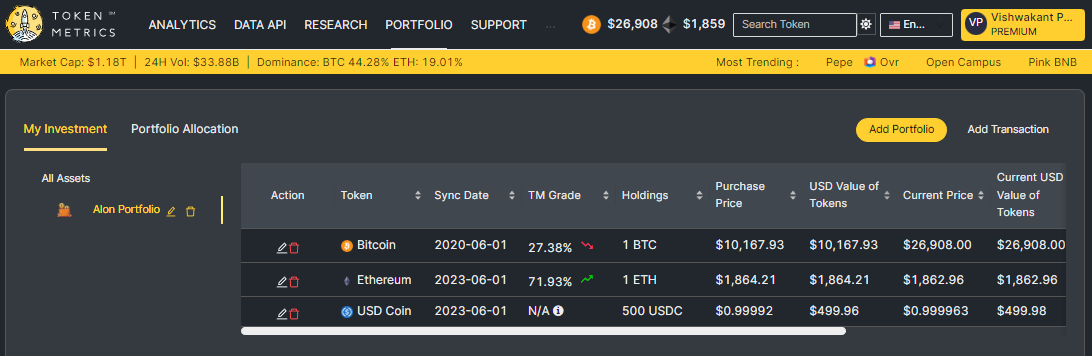
This powerful platform offers detailed analytics, performance metrics, and customizable alerts, empowering investors to make informed decisions based on accurate and up-to-date data.
The portfolio tracker also provides deep insights into individual cryptocurrency holdings, including historical performance, allocation breakdowns, and risk analysis.
2. Coingecko
CoinGecko is more than just a portfolio tracker; it's a comprehensive cryptocurrency platform that provides market data, news, and insights.
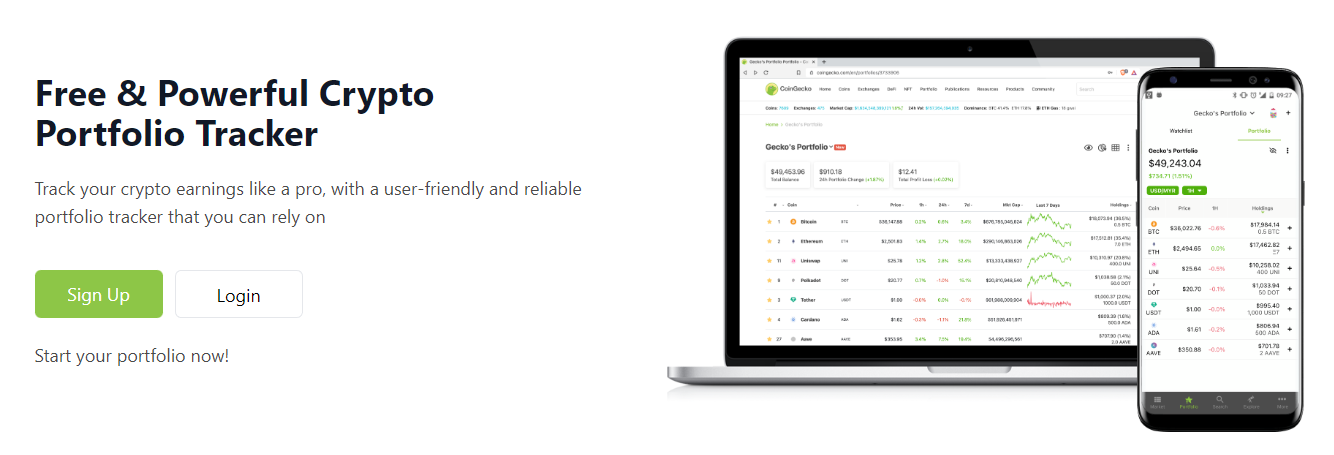
With its portfolio management feature, users can track their investments and monitor performance in real-time. CoinGecko also offers a wide range of metrics and charts to help users make informed decisions.
3. CoinMarketCap
CoinMarketCap stands as a highly reputable cryptocurrency price-tracking platform globally. Additionally, the company provides investors with a portfolio tracking solution.

Although the platform's functionality is somewhat limited, it presents a viable choice for budget-conscious traders who prefer the manual input of their cryptocurrency holdings.
4. Crypto.com
Crypto.com is primarily a crypto exchange but also offers portfolio tracking for hosted wallets. Users can track the past and real-time prices of their invested coins through the mobile app or website.

The platform allows tracking of top gainers and losers, newly added coins, and watchlist coins, providing comprehensive data such as price, volume, and market cap with a 7-day chart. It is available on both iOS and Android, and supports NFTs.
5. CoinTracker
CoinTracker simplifies crypto portfolio management by automatically syncing transactions from exchanges and wallets.

It offers tax calculation tools, performance tracking, and insightful analytics. CoinTracker supports over 300 exchanges and integrates with popular wallets like Coinbase and MetaMask.
6. CryptoCompare
CryptoCompare is a reliable and user-friendly portfolio tracker that offers a holistic view of your crypto holdings.

It provides detailed information on prices, market trends, and trading volumes, allowing users to make data-driven decisions. CryptoCompare also offers a wide range of educational resources, making it a valuable tool for beginners.
7. CoinStats
CoinStats is a comprehensive portfolio tracker that offers real-time data on over 3,000 cryptocurrencies. With its intuitive interface and advanced features, CoinStats allows users to monitor their portfolio performance, set price alerts, and track market trends.
Its integration with various exchanges and wallets makes it a convenient choice for crypto enthusiasts.
8. Kubera
Kubera presents itself as a portfolio tracker specifically designed to cater to a wide range of assets, including cryptocurrencies and NFTs. Unlike offering a free option, Kubera offers personal plans starting at $150 per year.

Kubera also offers features like track multiple assets, automatic and manual import options and identifying top performers.
9. Delta Investment Tracker
Delta is a powerful portfolio management tool that supports over 300 exchanges and cryptocurrencies.

Its sleek design and customizable features make it a popular choice for both beginners and experienced traders. With Delta, users can sync multiple wallets and exchanges, set price alerts, and access comprehensive analytics.
10. Crypto Pro
Crypto Pro, originally launched in 2015 as a Bitcoin ticker for the Apple Watch, has evolved into a comprehensive cryptocurrency tracking app.

With support for over 5,000 cryptocurrencies and compatibility with the entire Apple ecosystem, users can conveniently monitor their portfolios, receive live price updates, read news, and set price alerts.
The app ensures privacy by encrypting user data stored locally on each device, without employing any user analytics or tracking solutions.
How to choose the best crypto portfolio tracker?
When selecting a crypto portfolio tracker, it's essential to consider several factors to ensure it meets your specific needs. Some key factors to consider include:
Security: Look for trackers that prioritize strong security measures, such as encryption, two-factor authentication, and cold storage options.
Supported Exchanges: Check if the tracker supports the exchanges you use to trade cryptocurrencies.
User Interface and Experience: Choose a tracker with an intuitive interface that provides a user-friendly experience.
Compatibility: Ensure the tracker is compatible with the devices and operating systems you use.
Alerts and Notifications: Look for trackers that offer customizable alerts and notifications for price changes, portfolio milestones, and market news.
Reporting and Analytics: Consider trackers that provide detailed reports, analytics, and visualizations to help you understand your portfolio's performance.
Portfolio Synchronization: Opt for trackers that can sync with your wallets and exchanges to automatically update portfolio data.
Customer Support: Check if the tracker offers responsive customer support channels in case you encounter any issues.
Click here to trade cryptos at MEXC!
FAQs
Q1. Which crypto portfolio tracker is best for beginners?
For beginners, CoinMarketCap and CoinGecko are excellent choices. Both offer user-friendly interfaces, comprehensive features, and educational resources to help beginners navigate the crypto world with ease.
Q2. Can I track my portfolio across multiple exchanges?
Yes, many portfolio trackers like CoinStats, Delta, and CoinTracker support syncing transactions from multiple exchanges, allowing you to conveniently track your holdings in one place.
Q3. Do these portfolio trackers offer mobile apps?
Yes, most of the top portfolio trackers mentioned in this article, including CoinStats, Delta, and CoinGecko, offer mobile apps for both iOS and Android devices, enabling you to track your portfolio on the go.
Q4. Are these portfolio trackers secure?
Yes, reputable portfolio trackers prioritize security and employ various measures like encryption, two-factor authentication, and data protection protocols to ensure the safety of your portfolio data.
Q5. Can I use these portfolio trackers for tax reporting?
Yes, portfolio trackers like CoinTracker provide tax reporting features, allowing you to generate reports and calculate your cryptocurrency gains or losses for tax purposes.
Q6. Are there any free portfolio tracker options available?
Yes, several portfolio trackers offer free versions with basic features and limited capabilities. However, most also offer premium plans with additional features for users who require more advanced portfolio management tools.
Conclusion
In conclusion, tracking and managing your cryptocurrency portfolio is crucial for successful investing. These portfolio trackers offer a range of features and benefits to help you stay on top of your investments.
Whether you're a beginner or an experienced trader, these portfolio trackers offer user-friendly interfaces, real-time data, customizable features, and integration with exchanges and wallets.
By choosing the right portfolio tracker, you can effectively monitor your holdings, analyze market trends, set alerts, and make informed decisions to maximize your crypto investment potential.
Disclaimer
The information provided on this website does not constitute investment advice, financial advice, trading advice, or any other sort of advice and you should not treat any of the website's content as such.
Token Metrics does not recommend that any cryptocurrency should be bought, sold, or held by you. Do conduct your own due diligence and consult your financial advisor before making any investment decisions.
Click here to trade cryptos at MEXC!
Contact us at promo@tokenmetrics.com for marketing and sponsorship programs.

.svg)

Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)







.svg)




.png)