
Day Trading Crypto: A Comprehensive Guide to Navigating Volatility for Profits
.png)
Day trading crypto has surged in popularity as investors seek to capitalize on the volatile nature of digital assets. Many traders are attracted to crypto day trading due to its volatility and the potential for quick profits. The global cryptocurrency market operates 24/7 and features rapid price swings, presenting unique trading opportunities and risks for those aiming to make profits within short time frames. However, most day traders lose money, highlighting the importance of understanding the risks involved and recognizing that being a risk taker is often necessary for success in day trading crypto. Day trading requires knowledge of both securities markets and individual brokerage firm’s practices. This comprehensive guide provides a deep dive into the world of crypto day trading, covering essential strategies, tools, platforms, and risk management techniques to help both beginner day traders and experienced retail traders navigate this fast-paced financial market effectively.
What Is Day Trading Crypto?
Day trading crypto involves buying and selling cryptocurrencies within a single trading day, often multiple times, to profit from short-term price movements. A 'day trade' is defined as the act of buying and selling the same security within the same day. Unlike long term investing—where investors hold assets for extended periods—day traders focus on exploiting market inefficiencies, momentum shifts, or news events that cause rapid fluctuations in stock price or token value within minutes or hours. Day trading requires a sound and rehearsed method to provide a statistical edge on each trade.
A key characteristic of day trading is that all positions are typically closed by the end of the trading day to avoid overnight risk. In a day trade, this means opening and closing the same position in the same security on the same day. All positions in day trading are closed before the market closes for the trading day to avoid risks associated with overnight positions. However, since the cryptocurrency market never closes, “day” in crypto trading is more a conceptual timeframe based on session activity rather than fixed stock market hours. This constant market availability offers day traders continuous trading opportunities but also demands a disciplined approach to managing trades and risk. Traders need to be prepared for the risk of losing all their funds.
Why Is Crypto Ideal for Day Trading?
Cryptocurrencies are uniquely suited for day trading for several reasons:
- High Volatility: Major cryptocurrencies like Bitcoin and Ethereum frequently experience daily price swings of 5–10%, while smaller altcoins can exhibit even more dramatic fluctuations. This volatility creates numerous trading opportunities to capitalize on quick profits.
- 24/7 Market: Unlike traditional stock markets that operate during business days, crypto markets run nonstop, providing active traders with the ability to engage in buying and selling securities at any time.
- Liquidity: Top cryptocurrency exchanges offer high liquidity, allowing day traders to enter and exit positions quickly without significantly impacting the stock price. Monitoring order flow in these highly liquid markets can help traders make more informed buy and sell decisions.
- Wide Selection of Assets: Thousands of tokens exist, each with unique price movements and trading ranges, enabling traders to diversify and find the best trading opportunities.
Having more money in your trading account can provide a greater cushion to capitalize on the volatility and trading opportunities in crypto.
These factors combine to make crypto an attractive asset class for day traders seeking fast-paced trading strategies and the potential for quick profits.
Trading Accounts for Crypto Day Trading
Opening the right trading account is the first step for anyone looking to become a successful crypto day trader. A trading account with a reputable brokerage firm or cryptocurrency exchange is essential for executing your investment strategy and managing your buying and selling activities efficiently. When selecting a trading account, look for features such as low transaction fees, high liquidity, and advanced trading tools that support real-time analysis and fast order execution.
As a pattern day trader, it’s important to understand the requirements of a margin account, which can increase your buying power and allow you to take advantage of more trading opportunities. However, be aware of the pattern day trader rule, which may impose certain restrictions or minimum equity requirements on your trading activities, especially if you engage in frequent day trades. Always compare the types of cryptocurrencies offered, the security protocols in place, and the overall user experience before committing to a trading account. By choosing the right account, you can maximize your profit potential and ensure your trading aligns with your overall investment strategy.
Minimum Account Requirements
Before you start day trading crypto, it’s crucial to understand the minimum account requirements set by different brokerage firms and cryptocurrency exchanges. These requirements can include a minimum deposit to open your trading account or a minimum balance that must be maintained to keep your account active. For example, some platforms may require as little as $10 to get started, while others may have higher thresholds depending on the account type.
If you plan to use a margin account, be aware that there are often stricter minimum equity requirements compared to a standard cash account. Margin accounts can provide greater buying power, but they also come with increased risk and the possibility of a margin call if your account falls below the required minimum equity. As a day trader, it’s essential to review and understand these requirements to avoid any interruptions in your trading and to ensure you can meet the obligations of your chosen trading account. Knowing the minimum account requirements helps you plan your trading activities and manage your capital more effectively.
Best Cryptocurrencies for Day Trading
While technically any token can be day traded, some cryptocurrencies are better suited due to their liquidity, volatility, and spread. Popular choices among day traders include:
- Bitcoin (BTC): Known for its high volume and liquidity, Bitcoin offers relatively stable price movements compared to smaller coins, making it a staple for many day traders.
- Ethereum (ETH): Slightly more volatile than Bitcoin but with similar liquidity, Ethereum provides ample trading opportunities for momentum and breakout strategies.
- Solana (SOL), Cardano (ADA), Polygon (MATIC): These popular altcoins often experience frequent price swings, attracting traders looking for dynamic day trading stocks.
- Meme Coins and Low-Cap Altcoins: These can offer huge volatility and rapid price changes but come with higher risks and lower liquidity, requiring careful risk management. When a stock hits a new high or key technical level, it can trigger trading opportunities for day traders, similar to how breakouts in meme coins and low-cap altcoins can signal potential entry points.
Choosing the right cryptocurrency depends on your trading strategy, risk tolerance, and market conditions.
Day Trading Strategies for Crypto
Successful day traders employ a variety of strategies tailored to the fast-moving crypto markets. Here are some of the most common day trading strategies. Day trading strategies should be flexible to adjust techniques that match changing market conditions.
1. Scalping
Scalping is the quickest form of day trading, involving hundreds of trades per day to capture small profits from minimal price changes. Scalping is a trading style that exploits small price gaps created by the bid-ask spread, usually involving quick trades. This approach is also known as spread trading, as it involves profiting from the bid-ask spread by taking advantage of price gaps and market inefficiencies over very short timeframes. This strategy demands high-speed execution, low trading fees, and a deep understanding of market depth and order book dynamics. Scalpers rely heavily on technical analysis and direct access to market data.
2. Momentum Trading
Momentum traders focus on identifying strong news events, pump signals, or technical breakouts to ride a trend until signs of reversal appear. Momentum trading is a strategy used by day traders that assumes financial instruments which have been rising steadily will continue to rise. Key tools include volume indicators and the Relative Strength Index (RSI). This approach requires quick decision-making to position quickly and lock in gains before momentum fades.
3. Range Trading
Range trading involves identifying horizontal support and resistance levels within a trading range and buying low while selling high. This strategy works best in sideways markets where the stock price oscillates between established levels, allowing traders to capitalize on predictable price movements.
4. Breakout Trading
Breakout traders look for key resistance or support levels and open positions when the price breaks through these levels, often accompanied by increased volume and volatility. This strategy aims to capture significant price moves following the breakout.
5. Using Technical Indicators
Day traders commonly use a combination of technical indicators to confirm trading signals and reduce false entries. Popular indicators include:
- Moving Averages (SMA/EMA)
- Bollinger Bands
- MACD (Moving Average Convergence Divergence)
- Relative Strength Index (RSI)
- Volume Oscillators
By combining these tools, traders improve their statistical edge and increase the success rate of their trades.
Market Analysis for Crypto Day Traders
Market analysis is a cornerstone of success for any crypto day trader. To make informed trading decisions and manage the risks involved, day traders rely on both technical analysis and fundamental analysis. Technical analysis involves studying price charts, trading volumes, and historical patterns to predict future price movements. This approach helps day traders identify entry and exit points for their trades and develop a statistical edge in the market.
On the other hand, fundamental analysis focuses on the underlying factors that influence a cryptocurrency’s value, such as news events, regulatory developments, and overall market sentiment. By combining these two types of analysis, successful day traders gain a deep understanding of the market and can adapt their trading strategies to changing conditions. Utilizing market analysis tools and staying updated with the latest data allows day traders to spot trading opportunities and manage the risks involved in each trade.
Best Platforms for Day Trading Crypto
Selecting the right platform is crucial for effective day trading. Important factors include low trading fees, advanced charting tools, high liquidity, and reliable execution. Some of the top platforms for crypto day trading are:
- Binance: Known for low fees, a wide range of assets, and advanced trading tools suitable for both beginner day traders and professionals.
- Coinbase Advanced: Popular among U.S. traders, offering a user-friendly interface though with somewhat higher fees.
- Kraken Pro: Offers reliable performance and API integration for experienced traders.
- Bybit and Bitget: Favored by futures and margin traders looking to leverage their positions. These platforms offer features to increase day trading buying power, allowing traders to maximize the amount they can buy or sell within their margin accounts during active trading days.
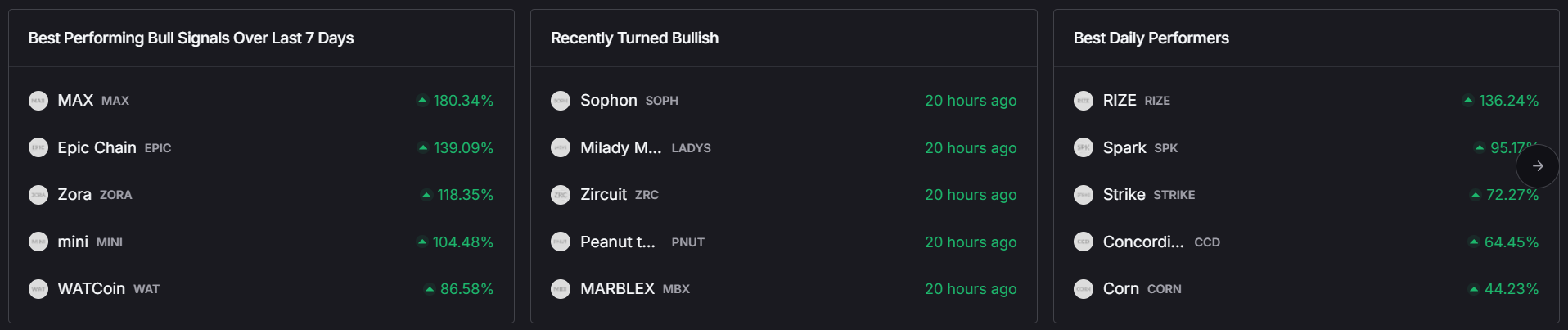
- Token Metrics: Provides AI-driven analytics and trading signals, including Trader Grades, Investor Grades, and Bullish/Bearish Signals, to help traders time their buying and selling activities more effectively.
Choosing a platform that aligns with your trading style and risk tolerance is essential for success.
Long Term vs Short Term Trading in Crypto
When it comes to trading cryptocurrencies, understanding the difference between long-term and short-term trading is essential for developing a good strategy. Long-term trading involves holding onto a cryptocurrency for months or even years, aiming to profit from its overall growth and adoption in the market. This approach is often favored by investors with limited resources or those who prefer a more hands-off investment strategy.
Short-term trading, by contrast, focuses on buying and selling cryptocurrencies within a much shorter time frame—sometimes within the same trading day. Crypto day trading is a prime example of short-term trading, where active traders seek to capitalize on rapid price movements and volatility. As a day trader, you need to be able to monitor the markets closely and react quickly to changes in stock prices. Choosing between long-term and short-term trading depends on your risk tolerance, available time, and investment goals. Both strategies can be profitable, but it’s important to select the one that best fits your resources and trading style.
Skills Required to be a Successful Crypto Day Trader
Becoming a successful crypto day trader requires more than just a willingness to take risks—it demands a specific set of skills and a deep understanding of the market. Mastery of technical analysis is essential for identifying trading opportunities and making quick, informed decisions. Equally important is strong risk management, which helps you protect your trading account and overall profits from unexpected market swings.
A successful day trader must also possess discipline, patience, and emotional control, as the fast-paced nature of crypto trading can be both stressful and unpredictable. Critical thinking and the ability to adapt your trading strategy on the fly are vital, especially when market conditions change rapidly. As a pattern day trader, having a statistical edge and knowing when to hold overnight positions can further enhance your profit potential. Ultimately, the combination of these skills, along with a commitment to continuous learning and self-improvement, is what sets apart the most successful day traders in the crypto market.
Risk Management in Crypto Day Trading
Risk management is a cornerstone of successful day trading, especially in the highly volatile crypto markets. Protecting your trading account and overall portfolio requires disciplined approaches such as:
- Using Stop-Loss Orders: Always set stop-loss levels to limit potential losses on any position.
- Position Sizing: Avoid risking more than 1-2% of your account value on a single trade to preserve capital.
- Take-Profit Targets: Establish clear profit-taking points to lock in gains before market reversals occur.
- Cautious Use of Leverage: While margin accounts can increase buying power and potential profits, leverage also amplifies losses and can trigger margin calls if the account falls below minimum equity requirements. Traders must be aware of margin requirements to avoid forced liquidation or margin calls.
- Short Positions: Taking a short position in crypto can be profitable if prices decline, but it also increases risk and requires strict risk management to avoid significant losses.
- Ensuring Full Payment: Ensuring full payment for securities purchased is essential, especially when using cash accounts, to comply with regulations and manage risk.
- Staying Informed: Monitor market data, news, and on-chain activity to anticipate trading opportunities and risks involved.
By implementing these risk management techniques, day traders can navigate the financial markets more safely and improve their chances of becoming successful day traders.
Common Mistakes to Avoid
Many beginner day traders fall into pitfalls that can lead to losing money quickly. Day traders may practice in a simulator before risking real money in the market. Avoid these common mistakes:
- Overtrading: Making too many trades does not guarantee profits and often results in excessive fees and poor decision-making. Overtrading also increases your total trades, which can have regulatory implications for active traders, such as triggering pattern day trader rules.
- Ignoring the Trend: Trading against the prevailing market trend reduces the statistical edge and success rate.
- FOMO Trading: Entering trades based on hype or fear of missing out without a solid day trading strategy often leads to losses.
- Not Using a Trading Journal: Tracking all trades helps identify what works and what doesn’t, improving future performance.
- Lack of Strategy: Random or impulsive trades without a clear plan increase financial risk and reduce consistency.
Avoiding these errors is crucial for building discipline and achieving long-term success in day trading activities.
Tools to Enhance Your Day Trading Game
Utilizing the right tools can significantly improve trading efficiency and decision-making:
- TradingView: Offers advanced charting, technical analysis, and backtesting capabilities.
- CoinMarketCap and CoinGecko: Provide real-time price data, volume, and market capitalization insights.
- Crypto News Aggregators: Help traders stay updated on market-moving headlines and events.
- Token Metrics Platform: An AI-powered platform delivering trading signals, trader and investor grades, and custom alerts to optimize trade timing.
These tools assist traders in analyzing market conditions, spotting trading opportunities, and managing risks more effectively.
Tax Implications
Day trading crypto generates frequent taxable events as each trade counts as buying and selling securities. Regulatory authorities often use a five business day period or business day period to determine if a trader qualifies as a pattern day trader, which can affect tax classification. Day trading can result in business classification for tax purposes, making profits fully taxable at the nominal tax rate. Traders should keep detailed records of:
- Every trade, which is considered a capital gain or loss.
- Holding periods, to distinguish between short-term and long-term capital gains.
Using tax software like Koinly, TokenTax, or CoinTracker can automate calculations and reporting. Since crypto tax laws can be complex, consulting a crypto-savvy tax professional is highly recommended to ensure compliance.
Final Thoughts: Is Day Trading Crypto Right for You?
Day trading crypto can be highly profitable but involves significant financial risk and requires a deep understanding of market behavior, technical analysis, and risk management. Success demands discipline, emotional control, and a well-defined trading strategy.
If you are a beginner day trader, start with small capital and consider paper trading or demo accounts to build confidence without risking real money. Day trading should not be funded with retirement savings, student loans, or funds required to meet living expenses. As your skills develop, leveraging platforms like Token Metrics can provide AI-driven insights and predictive analytics to gain a statistical edge.
For most investors, combining short-term day trading strategies with long term investing creates a balanced investment strategy that supports wealth building in the dynamic world of cryptocurrencies. Whether you aim to be a pattern day trader or prefer swing trading, understanding the risks involved and maintaining sound risk management practices are essential to achieving consistent profits in the fast-moving crypto markets.

.svg)

Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)










.svg)




.png)