
How Do You Purchase Cryptocurrency? A Beginner’s Step-by-Step Guide (2025)
.png)
Cryptocurrency has moved from niche tech circles to the mainstream, with millions of people worldwide investing in Bitcoin, Ethereum, and thousands of other digital assets. Whether you want to trade actively, hold long-term, or explore decentralized finance (DeFi), the first step is understanding how to purchase cryptocurrency safely and efficiently.
In this guide, we’ll walk you through everything you need to know—**from choosing the right platform to securing your crypto—**so you can get started with confidence.
Step 1: Understand What Cryptocurrency Is
Before you dive in, it’s important to understand what you’re buying. Cryptocurrency is a digital asset that uses blockchain technology to enable secure, decentralized transactions. Unlike traditional currencies, crypto isn’t controlled by banks or governments.
Some of the most popular cryptocurrencies include:
- Bitcoin (BTC): The first and most valuable cryptocurrency.
- Ethereum (ETH): A blockchain supporting smart contracts and decentralized applications.

- Stablecoins (USDT, USDC): Pegged to fiat currencies like the US dollar for stability.
- Altcoins: Thousands of other coins with unique use cases (Solana, Cardano, etc.).
Once you know your options, you’re ready to buy.
Step 2: Choose a Cryptocurrency Exchange
To purchase crypto, you’ll need an exchange—a platform that lets you buy, sell, and trade digital assets.
Types of exchanges:
- Centralized Exchanges (CEX): User-friendly and beginner-friendly. Examples: Coinbase, Binance, Kraken, eToro.
- Decentralized Exchanges (DEX): Peer-to-peer trading directly from your wallet (Uniswap, PancakeSwap). Better for experienced users.
- Brokerage Apps: Apps like PayPal, Cash App, Robinhood let you buy crypto, though withdrawals may be limited.
What to look for in an exchange:
- Security: Two-factor authentication (2FA), insurance, and strong history.
- Fees: Look for transparent trading, deposit, and withdrawal fees.
- Supported assets: Ensure your chosen exchange lists the coins you want.
- Regulation: Use platforms compliant with your country’s laws.
Step 3: Create and Verify Your Account
Most centralized exchanges require Know Your Customer (KYC) verification for security and regulatory compliance.
What you’ll need:
- Email & phone number: For account creation.
- Government-issued ID: Passport, driver’s license, or national ID.
- Proof of address: Sometimes required for higher transaction limits.
Once verified, you’ll gain full access to trading and withdrawals.
Step 4: Deposit Funds Into Your Account
You can’t buy crypto without adding funds.
Common payment methods:
- Bank transfers: Usually the cheapest option but may take 1–3 days.
- Debit/Credit cards: Fast but with higher fees (often 2–4%).
- E-wallets & PayPal: Convenient but may have limits.
- P2P transfers: Directly buy from other users (on platforms like Binance P2P).
Pro Tip: Always compare deposit fees before funding your account.
Step 5: Choose Which Cryptocurrency to Buy
Beginners often start with Bitcoin or Ethereum due to their liquidity and stability. However, thousands of altcoins are available—each with unique purposes.
Factors to consider before buying:
- Market cap: Large-cap coins are generally less volatile.
- Project fundamentals: Check the coin’s whitepaper and team.
- Use case & community: Active projects with strong ecosystems are more promising.
- Volatility: Understand the risks of smaller, high-reward tokens.
Step 6: Place Your Order
When you’re ready, navigate to the Buy/Sell section of your exchange.
Order types:
- Market Order: Instantly buys at the current price. Best for beginners.
- Limit Order: Sets a specific price at which to buy. Great for strategic entry.
- Recurring Buy: Automates purchases (also known as dollar-cost averaging).
Example: If Bitcoin is $50,000 and you want to buy $100 worth, your market order will instantly execute at the best available price.
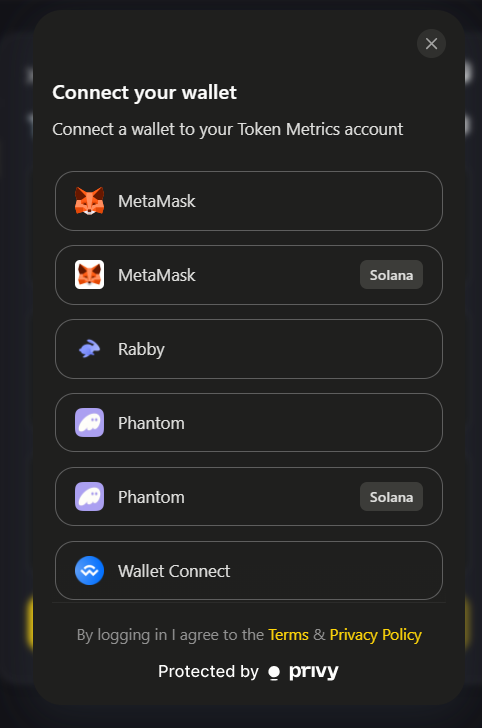
Step 7: Store Your Cryptocurrency Safely
Once purchased, you’ll need a wallet to store your crypto. Leaving assets on an exchange can expose you to hacking risks.
Types of wallets:
- Hot Wallets: Online, exchange-based, or software wallets (MetaMask, Trust Wallet). Easy to use but more vulnerable.
- Cold Wallets: Offline storage like Ledger or Trezor hardware wallets. Ideal for long-term security.
Tip: “Not your keys, not your coins.” If you hold significant funds, transfer them to a private wallet where you control the keys.
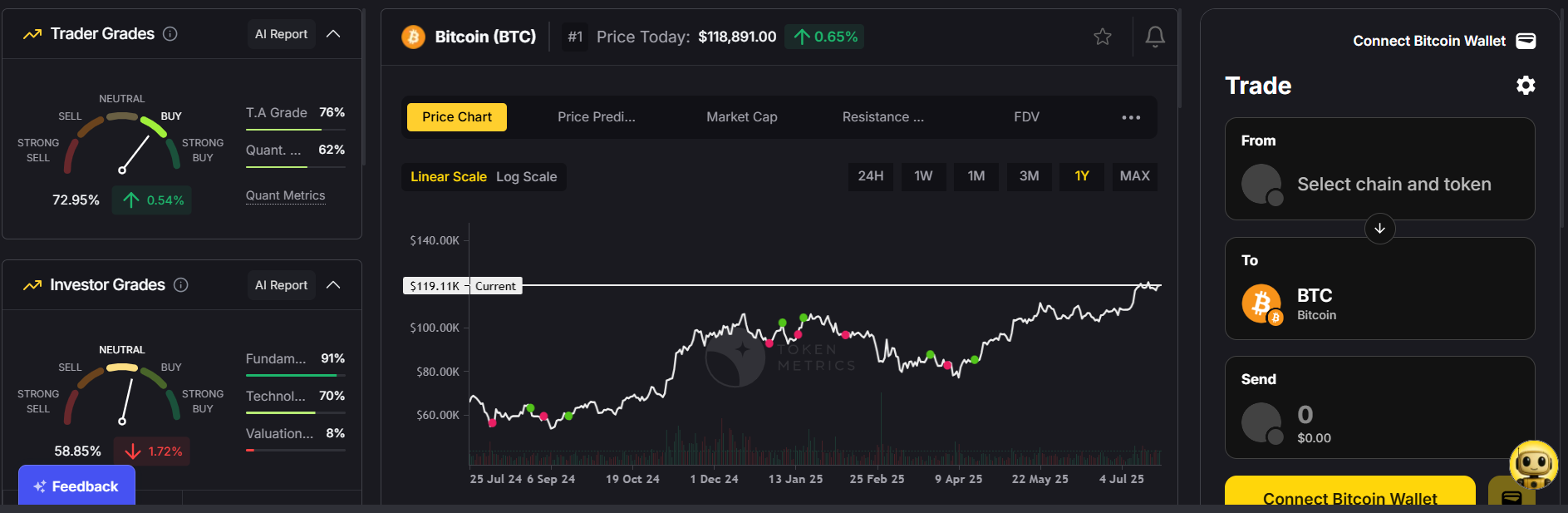
Step 8: Stay Informed and Manage Your Investment
Crypto markets are volatile. Prices can change rapidly, so keep track of market trends and news.
Best practices:
- Set alerts: Use tools like Token Metrics or CoinMarketCap to monitor prices.
- Diversify: Don’t put all your money in one coin.
- Avoid emotional trading: Stick to your plan and avoid panic-buying or selling.
- Use security tools: Enable 2FA and avoid sharing sensitive information.
How Much Should You Invest in Crypto?
Only invest what you can afford to lose. Experts often recommend starting with 1–5% of your portfolio and increasing gradually as you gain confidence.
Common Mistakes to Avoid When Buying Crypto
- Skipping research: Don’t buy a coin just because it’s trending.
- Using unsecured exchanges: Stick to reputable platforms.
- Not securing your wallet: Leaving funds on exchanges long-term.
- Falling for scams: Avoid too-good-to-be-true offers and unverified projects.
- Overtrading: Excessive buying/selling leads to higher fees and losses.
FAQs: Buying Cryptocurrency
1. Can I buy crypto without an exchange?
Yes. You can use peer-to-peer platforms or crypto ATMs, though fees may be higher.
2. Do I need a lot of money to start?
No. Many exchanges let you buy as little as $10 worth of crypto.
3. Is buying crypto legal?
In most countries, yes. Always check your local regulations.
4. What’s the safest way to buy?
Use a regulated exchange and store your funds in a hardware wallet.
Final Thoughts: Getting Started with Cryptocurrency
Purchasing cryptocurrency isn’t complicated—it’s about choosing the right platform, securing your funds, and investing wisely. Whether you’re buying Bitcoin as a long-term investment or exploring altcoins for potential growth, the steps are the same:
- Pick a reliable exchange
- Verify and fund your account
- Select your crypto and buy
- Secure it in a private wallet
The crypto market is full of opportunities—but also risks. Start small, do your research, and approach your investment journey with a long-term mindset.

.svg)

Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)






.svg)




.png)