How Does Crypto Trading Work? A Complete Beginner’s Guide (2025)
.png)
Cryptocurrency trading has rapidly evolved into one of the most dynamic and potentially rewarding forms of digital asset investing. Cryptocurrencies are rooted in blockchain technology, which serves as a public ledger that is distributed across a decentralized network. As a form of virtual currency, cryptocurrency exists entirely online and is not the same as physical money, meaning it cannot be held or exchanged in person like cash. The encryption used in cryptocurrency ensures that transactions are secure and the data exchanged is verified. For many newcomers, however, the question remains: how does crypto trading work? This comprehensive guide will break down the essential mechanics, strategies, risks, and platforms involved in crypto trading, providing you with a clear understanding of how to get started and trade smart in 2025. Additionally, we will explore the different types of cryptocurrency available in the market.
Introduction to Cryptocurrency
Cryptocurrency is a revolutionary form of digital currency that relies on advanced cryptography to secure financial transactions and control the creation of new units. Since the launch of the first cryptocurrency, Bitcoin, in 2009, the cryptocurrency market has expanded rapidly, introducing a wide variety of digital currencies and investment opportunities. Crypto trading, or cryptocurrency trading, involves buying and selling these digital currencies on a crypto exchange, with the aim of profiting from price fluctuations. For anyone interested in cryptocurrency investing, understanding how the cryptocurrency market operates and recognizing emerging trends is essential. At the heart of this innovation is blockchain technology, which ensures that every transaction is secure, transparent, and resistant to tampering. As digital currencies continue to reshape the financial landscape, learning the basics of cryptocurrency and how to navigate the crypto market is the first step toward successful investing.
Understanding the Cryptocurrency Market
The cryptocurrency market operates as a decentralized ecosystem, free from the direct control of central banks and traditional financial institutions. In this market, crypto trading involves exchanging digital assets like Bitcoin, Ethereum, and other digital currencies for fiat currency or other cryptocurrencies. One of the defining features of the crypto market is its high volatility—price movements can be swift and dramatic, creating both risks and opportunities for traders. To navigate these fluctuations, many traders rely on technical analysis and trend trading strategies to predict price movements and identify optimal entry and exit points. Staying informed about market trends, news, and global events is crucial for anyone trading cryptocurrency, as these factors can significantly impact the value of digital assets. By understanding the unique dynamics of the cryptocurrency market, traders can make more informed decisions and better manage their investments.
Blockchain Technology Explained
Blockchain technology is the backbone of the cryptocurrency market, providing a secure and transparent way to record and verify transactions. At its core, blockchain is a distributed ledger system that stores transaction data across a network of computers, making it nearly impossible to alter or tamper with records. Each transaction is verified using sophisticated cryptographic techniques, ensuring the integrity and authenticity of the data. This decentralized approach eliminates the need for a central authority, reducing the risk of censorship and fraud. For anyone interested in cryptocurrency, understanding how blockchain technology works is essential—not only does it enable secure transactions, but it also underpins the trust and transparency that make digital currencies possible. As blockchain technology continues to evolve, it remains a critical component of the cryptocurrency ecosystem and a key driver of innovation in the financial sector.
What are Crypto Transactions?
Crypto transactions are the process by which digital assets, such as cryptocurrencies, are exchanged between parties. Every crypto transaction is recorded on a public ledger known as the blockchain, where it is verified by a decentralized network of computers. This system ensures that each transaction is secure, transparent, and resistant to tampering. Cryptographic techniques, including the use of private keys and public keys, play a vital role in maintaining the integrity of crypto transactions. When trading cryptocurrency, it’s important to understand how to verify transactions and safeguard your digital assets. By mastering the basics of crypto transactions, traders can participate confidently in the cryptocurrency market and ensure that their trades are both secure and reliable.
Security Measures for Crypto Traders
Protecting your digital assets is a top priority when trading cryptocurrency. To keep your investments safe, always use a secure digital wallet—hardware wallets are especially effective for long-term storage, as they keep your private keys offline and out of reach from hackers. Enable two-factor authentication (2FA) on your crypto exchange accounts to add an extra layer of security, and make sure your software and devices are regularly updated to guard against vulnerabilities. It’s also crucial to choose a reputable crypto exchange with a strong track record for security and to remain vigilant against phishing scams and suspicious links. By following these security measures, crypto traders can significantly reduce the risk of theft and ensure their digital assets remain protected throughout their trading journey.
Transaction Security: Keeping Your Trades Safe
Ensuring the security of each trade is essential when trading cryptocurrency. Always access your crypto exchange through a secure, encrypted connection (look for HTTPS in your browser’s address bar) to prevent unauthorized interception of your data. Before making a trade, verify the legitimacy of both the exchange and your counterparty to avoid falling victim to scams. Store your digital assets in a secure digital wallet, and consider using cold storage solutions for added protection, especially for larger holdings. Stay alert for unusual price movements or unexpected transactions, as these can be signs of suspicious activity. By prioritizing transaction security and following best practices, you can safeguard your digital assets and enjoy a safer, more reliable trading experience in the cryptocurrency market.
What Is Crypto Trading?
At its core, crypto trading involves buying and selling digital assets such as Bitcoin, Ethereum, and various altcoins with the goal of profiting from price movements. A cryptocurrency exchange is a digital marketplace where users can buy, sell, and trade cryptocurrencies. Bitcoin is the most commonly traded cryptocurrency, but traders also seek out valuable cryptocurrency assets like Ethereum and other altcoins. Cryptocurrencies represent a new class of financial assets. Each transaction in a blockchain represents a ‘block’ of data about ownership and is linked to the previous block, forming a chain. Cryptocurrency is considered a non-fiat medium of exchange functioning independently of any government or central bank. Unlike traditional stock markets, the cryptocurrency market operates 24/7 and is accessible globally, often through decentralized or centralized platforms. Users can trade cryptocurrencies on various exchanges, and choosing reputable cryptocurrency exchanges is essential for safe and secure transactions.
There are two primary types of crypto trading to be aware of:
- Spot Trading: This involves the immediate purchase or sale of crypto assets, with settlement happening instantly. When you buy Bitcoin on a spot market, you own the actual digital coins. Traders often seek out valuable cryptocurrency assets. Trading pairs may include BTC/ETH or BTC/USDC, with USD Coin (USDC) being a stablecoin commonly used in such pairs.
- Derivatives Trading: Instead of owning the underlying crypto asset, traders buy contracts such as futures, options, or perpetual swaps that derive their value from the price of the cryptocurrency. These contracts are based on the underlying asset, such as Bitcoin or Ethereum. This allows for strategies like leverage trading without holding the actual crypto.
Understanding these key distinctions helps clarify the different ways you can engage with the crypto market.
How Crypto Trading Works: Step-by-Step
1. Choose a Crypto Exchange or Platform
To begin trading, you first need to gain access to a crypto exchange or trading platform. Binance, Coinbase, and Kraken are examples of centralized exchanges, which function as middlemen between buyers and sellers and hold your deposited money. These exchanges often list a wide range of cryptocurrency projects, giving users access to various digital assets. When choosing a platform, it's important to compare transaction fees, as centralized exchanges may charge higher fees than other options. Some platforms also support cryptocurrency payments for goods and services, adding flexibility for users. Be aware that regulations may differ for virtual currencies in different jurisdictions, and users should understand local regulations and reporting requirements related to trading activity. Popular choices in 2025 include Binance, Coinbase, Kraken, and innovative platforms like Token Metrics that incorporate AI-powered research and trading signals with AI crypto trading. The first cryptocurrency ever created was Bitcoin, launched in 2009.
Opening a trading account typically requires you to register, complete identity verification (known as KYC), and deposit funds—either fiat currency like USD or digital coins. You should verify your identity to fund your account on an exchange or broker. When funding your account, ensure the security of your online payments to protect your digital assets. Users store cryptocurrencies in digital wallets that require a private key to access. This process grants you the ability to trade crypto assets securely and efficiently.
2. Pick a Trading Pair
In the crypto market, assets are traded in pairs, meaning you exchange one digital asset for another. Common pairs include:
- BTC/USD (Bitcoin to US Dollar)
- ETH/BTC (Ethereum to Bitcoin)
- SOL/USDT (Solana to Tether)
Trading pairs allow you to speculate on the relative value between two assets, whether between a cryptocurrency and a traditional fiat currency or between two different digital coins. Each cryptocurrency transaction is recorded and cannot be counterfeited, providing a secure method for asset transfer.
3. Understand the Order Book
The order book is a real-time list of all buy (bid) and sell (ask) orders on the exchange. It shows the demand and supply dynamics for a given trading pair.
You can place different types of orders:
- Market Orders: Buy or sell immediately at the current market price.
- Limit Orders: Set a specific price at which you want to buy or sell, which executes only when the market reaches that level. Traders often use average prices, such as moving averages, to help determine optimal price levels for placing these orders.
- Stop-Limit or Stop-Market Orders: Automated orders triggered when the price hits a certain point, helping manage risk or lock in profits.
For traders who place frequent orders, such as scalpers, low fees are important to maximize gains by minimizing transaction costs.
Mastering these order types allows you to control your entry and exit points in the market, crucial for effective trading.
4. Analyze the Market with Technical Analysis
Successful traders use a blend of approaches to predict price movements and identify profitable opportunities: The value of a cryptocurrency is influenced by the quality of its underlying technology and market demand.

- Technical Analysis (TA): This involves studying price charts, indicators like MACD and RSI, and recognizing patterns in candlestick charts to forecast future price trends. Day traders rely heavily on technical indicators and the ability to recognize patterns to make quick decisions. Understanding price movement is especially important in range trading, where identifying support and resistance zones helps traders operate in stable, non-trending markets.
- Fundamental Analysis (FA): Evaluating the underlying value of a project by examining its technology, tokenomics, use cases, broader market news, and factors such as mining cryptocurrency, which plays a key role in the creation and sustainability of many digital assets.
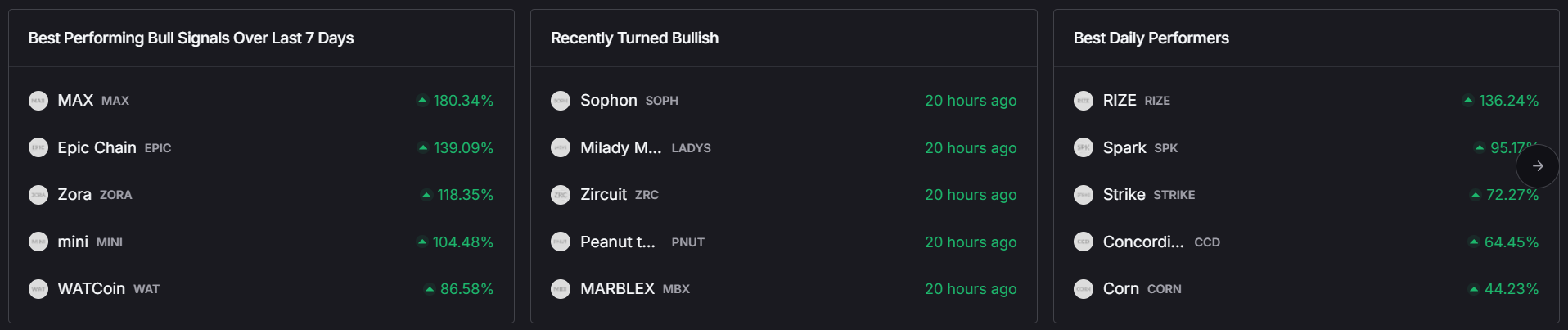
- AI-Powered Tools: Platforms such as Token Metrics leverage machine learning to grade cryptocurrencies and generate real-time trading signals, offering an edge beyond traditional analysis.
By combining these methods, traders make informed decisions rather than relying solely on speculation or hype. In addition, opportunities arise for arbitrage when price differences exist across exchanges, allowing traders to capitalize on these discrepancies. Effective risk management also involves monitoring for price drops and setting rules to limit losses.
5. Make the Trade
After thorough analysis and identifying an optimal entry point, you can execute your trade. Key considerations include:
- Position sizing: Determine how much capital to allocate.
- Risk-to-reward ratio: Assess potential gains relative to possible losses.
- Stop-loss and take-profit targets: Set automated exit points to manage risk.
For example, if you anticipate Ethereum rising from $3,000 to $3,500, you might place a buy order and set a stop-loss at $2,900 to limit potential losses.
6. Monitor and Manage Risk
Given the high volatility of the crypto market, managing risk is essential:
- Limit exposure to 1–2% of your total capital per trade.
- Use stop-loss orders to prevent significant losses.
- Regularly rebalance your portfolio based on evolving market trends.
- Track your capital gains from cryptocurrency transactions for tax purposes, as proper reporting is crucial for legal compliance.
High volatility creates opportunities for profit within short periods in cryptocurrency trading. Effective risk management is crucial for successful crypto investments, helping you achieve your financial goals while minimizing potential losses.
AI-driven platforms like Token Metrics can assist by offering automated portfolio management tailored to different risk profiles and trading styles.
Types of Crypto Trading Strategies
There are various trading styles suited to different goals and risk appetites: Day trading strategies are based on technical analysis, awareness of market sentiment, and perception of news that may affect volatility. These strategies allow users to trade cryptocurrencies in various ways depending on their preferences and objectives.
- Day Trading: Involves multiple trades within a single day to capitalize on short-term price fluctuations. This style requires discipline, fast decision-making, and strong technical analysis skills.
- Swing Trading: Traders hold positions for days or weeks, aiming to profit from medium-term trends by analyzing support and resistance levels, trading volume, and market sentiment.
- Scalping: A rapid-fire strategy targeting small price changes, with trades lasting seconds or minutes.
- HODLing: A long-term strategy where investors hold crypto assets believing they will appreciate significantly over time. It's important to know how to store cryptocurrency securely for the long term, using appropriate crypto wallets to protect your assets.
- AI-Based Trading: Emerging in 2025, AI-powered platforms like Token Metrics automate strategy execution by detecting trend shifts, scanning thousands of tokens, and issuing real-time bullish or bearish alerts. Understanding how cryptocurrency work can help in choosing the right automated strategy and interpreting AI-driven signals.
Understanding these strategies helps you choose the approach that aligns best with your investment goals.
Where Does Crypto Trading Happen in the Cryptocurrency Market?
Crypto trading takes place on several types of platforms:
- Centralized Exchanges (CEXs): These are traditional, regulated platforms like Binance and Coinbase. They offer high liquidity, user-friendly interfaces, and the ability to deposit and withdraw fiat currency.
- Decentralized Exchanges (DEXs): Platforms such as Uniswap and PancakeSwap operate on blockchain technology using smart contracts. They allow users to trade directly from their digital wallets without needing to create accounts, promoting secure transactions and privacy.
- AI Trading Platforms: Innovative services like Token Metrics provide advanced tools including AI-generated grades, real-time trading signals, and dynamic indices that adapt to market trends.
Each platform type offers unique advantages depending on your trading preferences and security requirements.
Benefits of Crypto Trading
Engaging in crypto trading offers several advantages:
- High Potential Returns: The volatility of digital assets creates opportunities for significant profits.
- 24/7 Market Access: Unlike traditional markets, the crypto market never closes, allowing trading at any hour.
- Global Participation: Anyone with internet access can open a crypto account and participate, democratizing investing. Users can make cryptocurrency payments without needing a traditional bank account, making it easier for the unbanked to access financial services. Virtual currency enables participation from anywhere in the world, removing geographic barriers.
- Technological Innovation: The integration of AI, blockchain technology, and decentralized finance (DeFi) protocols enhances trading capabilities and strategies.
These benefits make crypto trading an attractive option for both novice and experienced investors.
Risks of Crypto Trading
Despite its appeal, crypto trading carries inherent risks: * High Volatility: Sudden and unpredictable value changes can result in rapid losses. * Regulatory Uncertainty: Many regions lack clear oversight, and some exchanges operate without stringent regulation. * Security Threats: Exchanges and wallets can be vulnerable to hacks, risking your crypto holdings. While blockchain technology offers tamper-proof records and features like two-factor authentication, the question "is cryptocurrency safe?" remains, as risks such as hacking incidents, market volatility, and compromised cryptocurrency transactions on exchanges persist. * Emotional Trading: Fear of missing out (FOMO) and panic selling can lead to poor decisions. Proper research on exchanges and storage methods is essential to protect cryptocurrency investments from theft and loss. Investors should only invest what they can afford to lose due to the high risk of investment loss. Virtual currencies are also frequently targeted by scammers, making vigilance against fraud crucial.
- High Volatility: Sudden and unpredictable value changes can result in rapid losses.
- Regulatory Uncertainty: Many regions lack clear oversight, and some exchanges operate without stringent regulation.
- Security Threats: Exchanges and wallets can be vulnerable to hacks, risking your crypto holdings. Blockchain security features like tamper-proof transaction records and two-factor authentication help, but cryptocurrency transactions on exchanges remain at risk from hacking and other threats.
- Emotional Trading: Fear of missing out (FOMO) and panic selling can lead to poor decisions.
Utilizing AI-powered platforms like Token Metrics can help mitigate these risks by providing data-driven insights and reducing emotional bias.
How Token Metrics Enhances Crypto Trading
For traders seeking an edge in 2025, platforms like Token Metrics are transforming the way people trade cryptocurrency by:
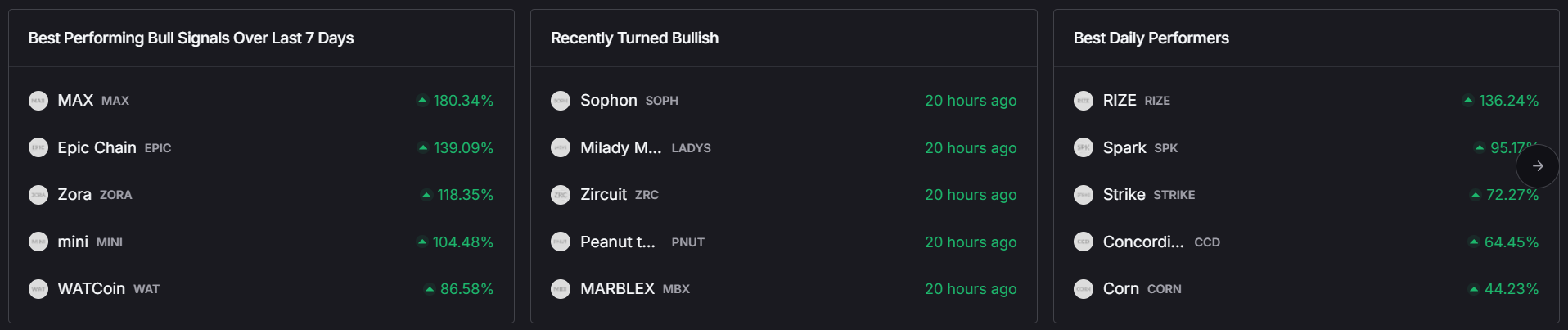
- Offering AI grades that evaluate coins based on technical indicators, fundamentals, and market sentiment.
- Delivering real-time alerts for significant price movements and trend changes.
- Providing auto-managed indices that automatically rebalance portfolios according to token performance and market conditions.
- Integrating seamlessly with your wallet or exchange to execute trades efficiently.
Whether you’re a beginner or a seasoned day trader, leveraging AI can simplify complex analysis and improve your trading outcomes.
Final Thoughts
Understanding how crypto trading works—from selecting exchanges and order types to adopting effective strategies and managing risk—is essential for trading smarter in the fast-paced digital currency landscape. While the crypto market remains volatile, tools like Token Metrics empower traders to make informed, data-driven decisions, helping to reduce risk and enhance profitability.
Ready to explore AI-powered crypto trading? Start your 7-day free trial with Token Metrics today and experience how smart trading works in 2025.
Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)










.svg)




.png)