
How Does Tokenizing AI Services Work? The Complete Guide to AI Tokenization in 2025
The convergence of artificial intelligence and blockchain technology has sparked a significant evolution in the digital economy: the tokenization of AI services. As we progress through 2025, this innovative approach is reshaping how AI capabilities are accessed, distributed, and monetized worldwide. By converting AI services into blockchain-based digital tokens, tokenization is democratizing artificial intelligence and creating entirely new economic models that empower users and developers alike.
Tokenizing AI services marks a fundamental shift away from centralized AI platforms toward decentralized, community-owned ecosystems. In these ecosystems, AI capabilities become tradeable assets, enabling broader participation and fostering innovation. This transformation is more than theoretical—it is driving billions of dollars in market activity and redefining the relationship between businesses, individuals, and artificial intelligence.
Understanding AI Service Tokenization
To grasp how does tokenizing AI services work, it’s essential to understand the core concept of AI tokenization. Tokenizing AI services involves converting artificial intelligence capabilities, including AI models and computational resources, into digital tokens that exist on blockchain networks. These tokens represent ownership, access rights, or usage credits for specific AI functionalities, effectively bridging traditional AI services with decentralized finance ecosystems.
Tokenization in AI is the foundational process of converting data, such as text or computational resources, into smaller, manageable tokens that AI models can analyze and utilize.
At its foundation, tokenization is the process of issuing a unique, digital, and anonymous representation of a real-world asset or service. In Web3 applications, tokens operate on blockchains—often private or permissioned—allowing them to be utilized within specific protocols. When applied to AI services, this process creates programmable assets that can be traded, staked, or used to access computational resources securely and transparently. Understanding AI tokenization is crucial for effectively managing and securing data, especially as AI systems handle increasingly large and sensitive datasets.
Tokenization fundamentally transforms AI service operation by introducing several key characteristics:
- Fractional Ownership: Instead of requiring large upfront investments for AI access, tokenization enables fractional ownership of AI models and services, making advanced AI capabilities accessible to smaller investors and businesses.
- Programmability: Tokens can embed smart contract functionality, enabling automated execution of AI services based on predefined parameters and conditions.
- Composability: Tokenized AI services can interact seamlessly with other blockchain-based assets and applications, fostering synergies and unlocking new use cases across decentralized ecosystems.
- Transparency: All transactions and interactions involving tokenized AI services are immutably recorded on the blockchain, providing accountability and auditability.
- Building Blocks: Tokens serve as the fundamental building blocks of AI service tokenization, enabling modular and flexible integration of AI capabilities within decentralized systems.
In summary, tokenizing AI services leverages the process of tokenization in AI to create secure, programmable, and accessible digital assets—tokens matter because they directly impact the performance, security, and efficiency of AI service deployment and utilization.
The Tokenization Process: From AI to Asset
Transforming traditional AI services into tokenized assets involves a multi-step tokenization process that ensures both technical functionality and economic viability. Model processes in AI tokenization break down data into tokens, allowing AI models to analyze and process information efficiently within their context window.
Managing tokens effectively is crucial for optimizing model performance, enhancing security, and reducing operational costs in tokenized AI services. Strategic token management helps prevent semantic fragmentation, mitigates security vulnerabilities, and improves computational efficiency.
Asset Identification and Preparation
The initial phase requires identifying which AI services or capabilities are suitable for tokenization. These may include:
- AI Models: Machine learning models, neural networks, and specialized algorithms that deliver specific functionalities.
- Computing Resources: GPU power, processing capacity, and storage resources dedicated to AI operations.
- Data Assets: Curated datasets, training data, and specialized knowledge bases that underpin AI systems.
- AI Agents: Autonomous software entities capable of performing tasks and making decisions independently.
Smart Contract Development
Smart contracts form the backbone of tokenized AI services. These self-executing agreements define the terms, conditions, and functionalities of tokenized assets. Written as code on a blockchain, smart contracts enable AI algorithms to autonomously execute predefined strategies, eliminating intermediaries and reducing operational costs. In this model, artificial intelligence makes decisions, and the blockchain ensures their execution—creating powerful automation capabilities previously unattainable in traditional AI systems.
Token Creation and Distribution
Following smart contract development, tokens are created according to established blockchain standards. These standards dictate the rules for token creation and management, ensuring interoperability across platforms. Each token is assigned as a unique token or included in a set of unique tokens to represent specific assets or rights. Common standards include:
- ERC-20: Fungible tokens ideal for utility tokens and currency-like applications.
- ERC-721: Non-fungible tokens (NFTs) suited for unique AI models or specialized services.
- ERC-1155: Multi-token standards capable of handling both fungible and non-fungible assets, allowing for the creation and management of multiple tokens within a single contract.
Once created, tokens are distributed to users, investors, or stakeholders, enabling access to AI services or ownership rights. One token can represent a single access right or asset, while multiple tokens can represent broader ownership or usage rights.
Marketplace Integration
The final step involves integrating tokenized AI services into decentralized marketplaces where they can be discovered, evaluated, and utilized by end users. These marketplaces provide infrastructure for trading, governance, and community interaction around tokenized AI assets, facilitating the growth of vibrant AI ecosystems.
Types of Tokenized AI Services
AI Model Tokenization
AI models trained on extensive training data can be tokenized to represent their value and ownership rights.
Large language models (LLMs) use tokenization to process and generate text by breaking input text into smaller units called tokens. These individual tokens can be words, subwords, or even characters, and each is assigned a unique ID by the large language model to represent text as sequences of token IDs. GPT models utilize byte pair encoding (BPE) for efficient subword tokenization, which merges frequent character pairs to handle vocabulary limitations and unknown words. Word tokenization splits text into words, while subword and character-level tokenization break text into even smaller units, each with different trade-offs for handling special characters and out-of-vocabulary terms. Tokenization enables AI models to analyze semantic relationships and patterns in the input sequence, supporting tasks like parsing, translation, and content generation. Breaking text into tokens is essential for processing input text and generating output tokens, as it allows models to understand and generate human language. Input tokens and output tokens are counted for pricing and rate limiting, with the number of tokens and token limits directly affecting model usage and costs. The context window defines the maximum number of tokens a model can process at once, setting a token limit for both input and output. During text generation, models predict the next token to generate human like text and generate responses. Detokenization converts numerical representations of tokens back into textual information for human interpretation. Tokenization methods also handle unknown words using special tokens like <|unk|> and manage special characters during preprocessing. Other tokens can represent data types beyond text, such as when models process images in multimodal AI applications. Tokenization bridges human language and machine processing, and token based methods are fundamental in AI applications for tasks like chatbots, translation, and predictive analytics. Understanding the token limit and token limits is crucial for optimizing AI applications and managing costs.
Tokenized AI models foster innovation and collaboration by allowing researchers, developers, and businesses to monetize their intellectual property. For example, a natural language processing model could be tokenized, enabling multiple organizations to purchase access rights while original developers retain ownership and receive royalties based on token usage.
Computational Resource Tokenization
Computing resources such as GPU power and storage are essential for training AI models and running inference tasks. These resources can be tokenized to represent their availability and utilization in decentralized AI marketplaces. Tokenizing computational resources optimizes resource allocation, reduces operational costs, and increases efficiency. Some platforms leveraging this model report cost reductions of up to 70% compared to traditional cloud computing services.
Data Asset Tokenization
High-quality training data is the foundation of effective AI systems. Tokenizing data assets enables secure sharing and monetization of datasets while protecting sensitive information. Techniques like federated learning and secure multi-party computation allow data owners to monetize tokenized data without compromising privacy or regulatory compliance, thus addressing concerns related to sensitive data and potential data breaches.
AI Agent Tokenization
AI agents—autonomous software entities capable of decision-making—are increasingly tokenized to represent ownership stakes. These tokens facilitate community governance and provide economic incentives for agent development and improvement. Token issuance creates digital tokens on blockchain platforms that encapsulate ownership rights, access privileges, or revenue-sharing potential for AI agents.
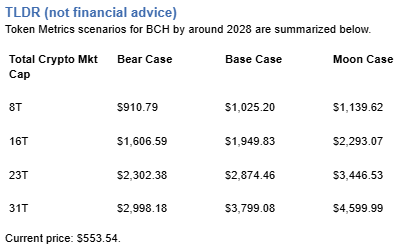
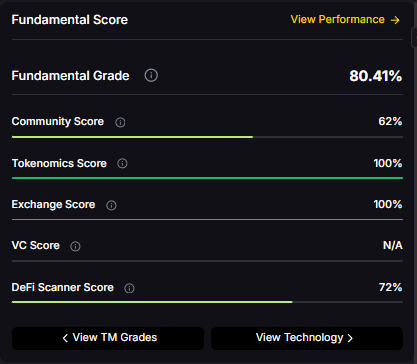
Token Metrics: The Premier Example of AI Service Tokenization
Token Metrics exemplifies the successful tokenization of AI services in the cryptocurrency analytics space, demonstrating how sophisticated AI capabilities can be effectively tokenized to create value for both providers and users.
The TMAI Token Ecosystem
Token Metrics AI (TMAI) is a groundbreaking token that empowers the crypto community with advanced AI tools and insights. The TMAI token acts as the gateway to the platform’s comprehensive suite of AI-powered services, including:
- AI-Powered Trading Bots: Token holders gain access to AI-driven trading bots compatible with various exchanges. These bots leverage machine learning models trained on cryptocurrency market dynamics to automate trading strategies.
- Comprehensive Analytics Platform: The TMAI Agent provides AI-driven market analysis across platforms such as Twitter (X), Telegram, and Discord, ensuring users receive real-time insights wherever they trade.
- Tokenized Governance: TMAI holders participate in governance through the Token Metrics DAO, influencing platform development and strategic direction.
Advanced Tokenomics Model
TMAI employs a sophisticated vote-escrowed (veTMAI) system that exemplifies best practices in AI service tokenization:
- Staking Mechanisms: Holders lock TMAI tokens for durations up to 12 months, earning a Staking Score that determines access to platform benefits. Longer commitments yield higher multipliers, incentivizing long-term engagement.
- Revenue Sharing: Stakers earn a proportional share of platform revenue, distributed by the Token Metrics DAO, with options for direct payouts or reinvestment.
- Early Access Benefits: Stakers receive early access to investment deals through Token Metrics Ventures Fund, with larger allocations for higher Staking Scores.
Developer-Friendly Infrastructure
Token Metrics offers a modular, scalable crypto API for real-time ratings, sentiment analysis, indices, and AI signals. The official SDK allows developers to build AI-powered trading agents without extensive AI expertise, democratizing access to advanced AI tools.
Market Performance and Adoption
With over 50% of TMAI’s supply airdropped to the community, Token Metrics emphasizes collective ownership and governance. The platform has raised $8.5 million from over 3,000 investors, reflecting strong market traction and user engagement.
Technical Implementation and Architecture
Blockchain Integration
Tokenizing AI services demands robust blockchain infrastructure capable of handling complex computations securely and at scale. While Ethereum remains dominant due to its mature smart contract ecosystem, emerging layer-2 solutions and AI-focused blockchains are gaining traction for their improved performance and scalability.
Oracle Integration
Oracles connect blockchains to external data sources, providing real-time information essential for AI service execution. Reliable oracle integration ensures smart contracts receive accurate data feeds, enabling AI algorithms to analyze market trends, optimize token pricing, and automate decision-making.
Interoperability Standards
Interoperability is crucial for tokenized AI services to function across diverse platforms. Multi-chain protocols enable AI tokens to operate on different blockchains, maximizing utility and market reach. Standardizing token ids and formats ensures seamless communication between AI systems and blockchain applications.
Market Growth and Economic Impact
Market Size and Projections
The tokenization market is projected to reach $4 trillion by 2025, highlighting the transformative potential of AI tokens. Fueled by advances in machine learning, natural language processing, and blockchain interoperability, tokenized AI services are becoming foundational components of decentralized AI infrastructure.
Investment and Funding Trends
Significant investments from both traditional and crypto-native sources are fueling projects that tokenize AI services. Many have achieved unicorn valuations by pioneering innovative approaches to AI democratization and tokenized data sharing.
Real-World Economic Benefits
Tokenized AI services deliver tangible advantages:
- Cost Reduction: By eliminating intermediaries and enabling peer-to-peer transactions, tokenization reduces operational costs by 30-70%.
- Increased Accessibility: Fractional ownership models allow smaller businesses and developers to access enterprise-grade AI capabilities.
- Revenue Diversification: Developers monetize AI tools and data assets, while users share in economic gains.
Challenges and Solutions
Technical Challenges
- Scalability: Blockchain networks face scalability limits that can hinder AI-powered smart contracts. Layer-2 solutions and AI-optimized blockchains offer promising remedies.
- Energy Consumption: Both AI and blockchain are energy-intensive. Innovations in consensus mechanisms and efficient AI algorithms aim to reduce environmental impact.
- Oracle Reliability: Ensuring accurate data feeds requires multiple oracle providers and AI-driven validation to prevent errors or exploits.
Regulatory Considerations
Legal frameworks around tokenized assets remain uncertain. Regulatory scrutiny, especially concerning securities laws and PCI DSS compliance, poses risks. However, institutions like the Federal Reserve are exploring how tokenization and AI can enhance payment systems, suggesting clearer regulations will emerge.
Security Concerns
Blockchain systems are vulnerable to hacks. Robust security protocols, regular audits, and AI-driven vulnerability detection tools are essential to safeguard tokenized AI services and protect sensitive information.
Future Trends and Developments
Enhanced AI Capabilities
The future will see more advanced AI services tokenized, including:
- Autonomous AI Agents: Self-improving systems that adapt based on user feedback and market conditions.
- Specialized Industry Solutions: Tailored AI services for healthcare, finance, manufacturing, and more.
- Multi-Modal AI: Systems processing text, images, audio, and video through unified tokenized interfaces.
Improved User Experience
User-friendly platforms will emerge, featuring:
- No-Code Interfaces: Enabling non-technical users to deploy AI services effortlessly.
- Mobile-First Designs: Accessing tokenized AI tools on smartphones and tablets.
- Integration with Existing Tools: APIs and plugins connecting tokenized AI services with popular business software.
Cross-Chain Compatibility
Seamless operation across multiple blockchains will become standard, allowing users to leverage AI capabilities regardless of their preferred blockchain ecosystem.
Conclusion: The Future of AI is Tokenized
Understanding how does tokenizing AI services work is essential for anyone engaged in the evolving AI landscape. By converting AI capabilities into blockchain-based assets, tokenization is creating democratic, transparent, and efficient systems that serve a global community rather than a few centralized entities.
Token Metrics exemplifies this transformative potential, showcasing how AI analytics can be tokenized to create value for millions worldwide. Through its TMAI token ecosystem, it provides a blueprint for community-owned, governance-driven AI platforms.
The benefits of AI service tokenization are clear: democratized access, economic efficiency, community governance, revenue sharing, and accelerated innovation. As tokenization becomes the dominant model for AI distribution and monetization, businesses, developers, and investors must engage early to remain competitive.
The future of artificial intelligence is no longer centralized within tech giants. It is tokenized, distributed, and owned by the communities that build and use it. This shift represents one of the most significant technological transformations since the internet’s inception, with profound implications across industries and economies worldwide.

.svg)

Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)















.svg)




.png)