
How to Buy Bitcoins: A Simple Guide for First-Time Investors

Introduction to Digital Currency
Digital currency represents a form of virtual currency that operates using cryptography for enhanced security. Unlike traditional money controlled by governments or financial institutions, digital currency is decentralized, meaning it functions without a central authority overseeing it. The first cryptocurrency, Bitcoin, was introduced in 2009 and has since revolutionized the way people think about money and investing. Many investors purchase Bitcoin for its investment value rather than its ability to act as a medium of exchange. Buying Bitcoin and other cryptocurrencies typically involves using a cryptocurrency exchange or a specialized crypto platform. Before diving into the process of how to buy bitcoins, it is crucial to understand the fundamentals of digital currency, its underlying technology, and how it differs from fiat currency.
Understanding Bitcoin
Bitcoin is a type of digital currency that relies on blockchain technology to securely record transactions and regulate the creation of new units. The blockchain acts as a public ledger that contains every Bitcoin transaction ever made, providing transparency and security for all users. However, Bitcoin prices can be highly volatile, with values fluctuating rapidly due to market trends and investor sentiment. Bitcoin prices are prone to significant fluctuations, caused by market volatility and news events. This volatility means that investing in Bitcoin carries inherent risks, but it also offers the potential for significant rewards. As the most widely recognized and accepted cryptocurrency, Bitcoin often serves as a benchmark for the broader cryptocurrency market, influencing the prices of many other cryptocurrencies.
Buying Bitcoin
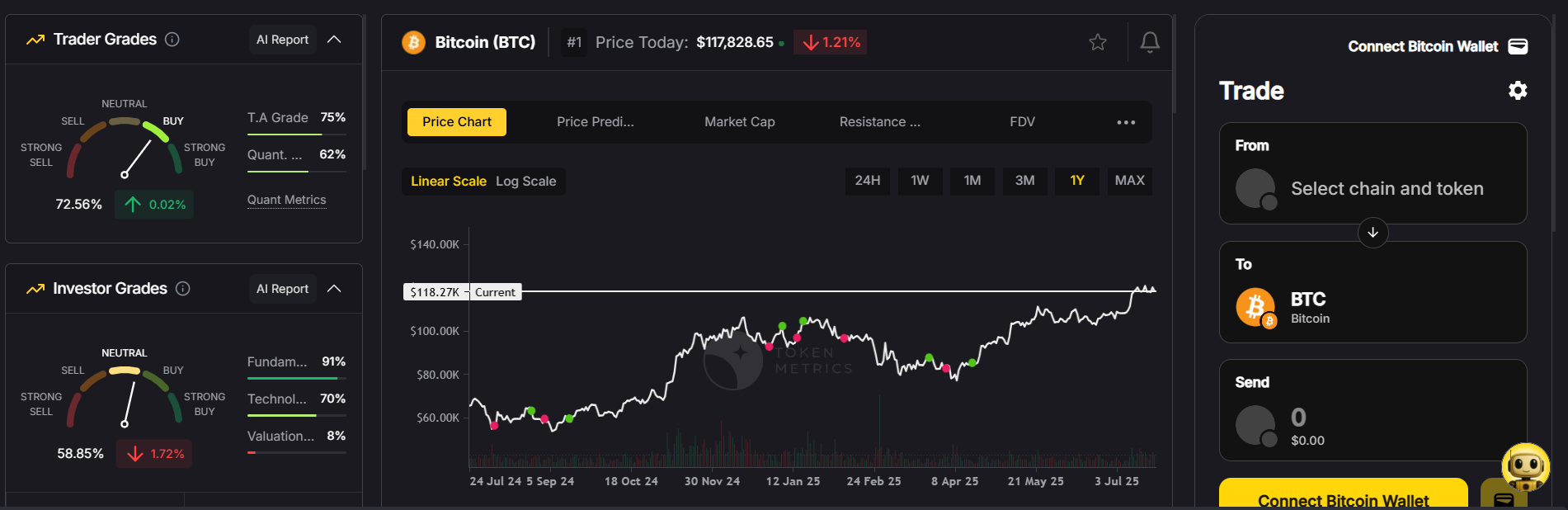
To buy Bitcoin, you typically use a cryptocurrency exchange such as Token Metrics, Coinbase or Binance, or a crypto platform like Cash App or Robinhood. The process begins by creating an account on your chosen platform, followed by verifying your identity to comply with regulatory requirements. After verification, you need to fund your account using a preferred payment method, such as bank transfers or a debit card. Debit cards represent one of the fastest payment methods for buying Bitcoin. Once your account is funded, you can place an order to buy Bitcoin at the current market price. It is important to be aware of the fees involved in buying Bitcoin, which may include transaction fees and exchange fees, as these can affect the overall cost of your investment.
Bitcoin Wallet
A Bitcoin wallet is essential for securely storing your Bitcoin and enabling you to send and receive payments. There are various types of Bitcoin wallets to choose from, including software wallets, hardware wallets, and paper wallets. Software wallets can be accessed via a computer or mobile app, offering quick access to your digital wallet. Hardware wallets, on the other hand, are physical devices designed to store your Bitcoin offline for enhanced security. Paper wallets are physical documents containing your private keys and are often used for long-term storage. Most investors use a mix of both hot and cold wallets for flexibility and security. Regardless of the type, securing your wallet and safeguarding your private keys is critical to protect your investments from theft or loss.
Payment Methods
Several payment methods are available when you buy bitcoin, each with its own advantages and disadvantages. Bank transfers are a popular choice due to their security and relatively low fees, though they can take several days to process. Debit and credit cards offer faster transactions but often come with higher fees. Credit cards are a popular choice for buying Bitcoin and are accepted by most crypto platforms. Some cryptocurrency exchanges also accept alternative payment options such as PayPal or even cash, depending on the platform’s policies. When choosing a payment method, consider factors such as speed, fees, and convenience to find the best fit for your needs.
Regulatory Compliance
The regulatory environment surrounding Bitcoin and other cryptocurrencies is continuously evolving. In the United States, for example, the Securities and Exchange Commission (SEC) provides guidance on cryptocurrency regulations, ensuring that exchanges and platforms adhere to anti-money laundering (AML) and know-your-customer (KYC) standards. These regulations help maintain the integrity of the cryptocurrency market and protect investors from fraud. Investors should be aware that cryptocurrency gains are taxable in the U.S. and that platforms may report transactions to the IRS. When buying Bitcoin, it is vital to select a reputable and regulated cryptocurrency exchange or platform to ensure compliance with these legal requirements and to safeguard your funds.
Step-by-Step Guide to Buying Crypto
If you are wondering how to buy bitcoins, here is a simple step-by-step process to get started:
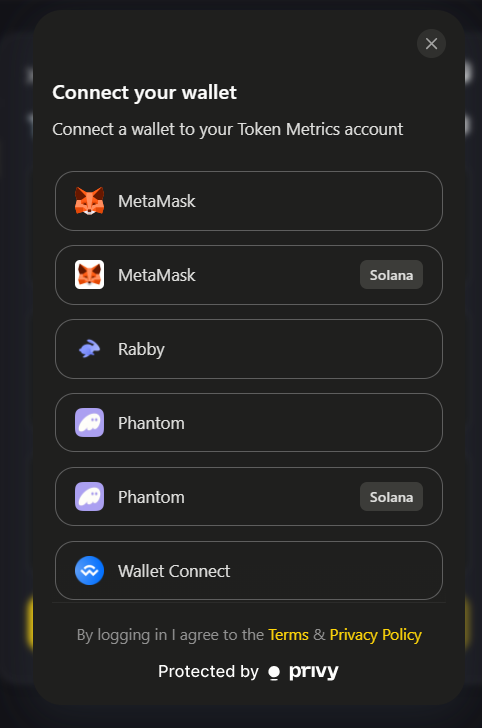
- Choose a reputable cryptocurrency exchange or crypto platform that complies with regulatory standards and offers a user-friendly interface.
- Create an account on the chosen platform and complete the identity verification process to comply with AML and KYC regulations.
- Fund your account using a preferred payment method such as bank transfers or debit cards, ensuring your funds are available for purchases.
- Place an order to buy Bitcoin at the current market price or set a limit order to buy at a specific price.
- Store your Bitcoin securely in a digital wallet, opting for a hardware wallet or a trusted software wallet to protect your private keys and assets.
Following these steps will help you complete the process of buying Bitcoin safely and efficiently.
Managing Risk
Investing in Bitcoin and other cryptocurrencies involves various risks, including market volatility and security vulnerabilities. The cryptocurrency market can experience rapid price swings, so it’s important to understand the risks involved before committing your money. Many experts suggest that new investors should start with small investments in well-known assets like Bitcoin to familiarize themselves with the market. To manage these risks, consider diversifying your portfolio by investing in other cryptocurrencies or traditional assets. Additionally, using risk management tools such as stop-loss orders can help protect your investments from significant losses. Staying informed about market trends and maintaining a cautious approach will help you navigate the risks involved in cryptocurrency investing.

Selling Bitcoin
Selling Bitcoin is a process similar to buying it and can be done through cryptocurrency exchanges or crypto platforms. To sell Bitcoin, you place an order specifying the amount you wish to sell at the current market price or a set price. It is important to be aware of the fees associated with selling Bitcoin, which may include transaction and exchange fees. After the sale, the proceeds can be withdrawn to your bank account or digital wallet, depending on the platform’s options. Understanding the selling process and associated costs is key to maximizing returns from your Bitcoin sales.
Buying Crypto Safely
To buy crypto safely, start by choosing a reputable and regulated cryptocurrency exchange or platform with positive user reviews and strong security measures. Protect your account by using strong, unique passwords and enabling two-factor authentication for an additional layer of security. Be vigilant against phishing scams and fraudulent schemes by verifying the authenticity of websites and communications. Conduct thorough research before selecting a platform, and always keep your private keys and wallet information confidential to prevent unauthorized access to your funds.
Common Mistakes to Avoid
New investors often make mistakes that can jeopardize their cryptocurrency investments. One major error is investing more money than they can afford to lose, which can lead to financial hardship if the market turns unfavorable. Another common mistake is failing to do adequate research and not fully understanding the risks involved in buying and holding Bitcoin. Additionally, accessing your account over unsecured public Wi-Fi networks or shared computers can expose your funds to hacking. Lastly, sharing private keys or seed phrases with others compromises wallet security and should be strictly avoided.
Conclusion
Buying Bitcoin and other cryptocurrencies can seem complex and intimidating at first, but with the right knowledge and precautions, it can be a rewarding investment opportunity. Understanding the risks involved, choosing a regulated and reputable platform, and securing your account with strong passwords and two-factor authentication are essential steps to buy bitcoins safely. By following the guidelines outlined in this article and conducting thorough research, you can confidently enter the world of cryptocurrency investing and manage your digital assets securely.
Additional Tips for Buying Bitcoin
Staying informed about market trends and news is crucial for making smart investment decisions in the cryptocurrency market. Consider leveraging cryptocurrency trading bots or automated trading tools to assist with buying and selling based on market signals. Maintaining a long-term perspective helps avoid emotional decisions driven by short-term price fluctuations. Diversifying your portfolio by investing in many cryptocurrencies or other assets can reduce risk and improve potential returns. These strategies will enhance your ability to navigate the dynamic world of Bitcoin and other digital currencies.
Future of Bitcoin
The future of Bitcoin and cryptocurrencies remains uncertain but promising, as they are poised to continue playing a significant role in the global financial system. Bitcoin and other cryptocurrencies have the potential to disrupt traditional payment systems by offering faster, more secure, and transparent transactions through blockchain technology. Bitcoin rewards are halved approximately every four years, affecting the supply and value of Bitcoin over time. Keeping abreast of regulatory developments and understanding the evolving risks and benefits will empower investors to make informed decisions. By staying educated and adaptable, you can successfully navigate the complex and rapidly changing cryptocurrency landscape.
Investment Strategies
When investing in Bitcoin and cryptocurrencies, various strategies can suit different investor goals. The buy-and-hold approach involves purchasing Bitcoin and holding it long-term, capitalizing on potential appreciation over time. Alternatively, active trading involves buying and selling cryptocurrencies to profit from market volatility, requiring close monitoring of market trends and quick decision-making. Regardless of the strategy chosen, it is vital to understand the associated risks and develop a plan that aligns with your financial situation and investment objectives.
Final Checklist
Before you begin investing in Bitcoin and other cryptocurrencies, ensure you have completed these essential steps:
- Conduct thorough research and understand the risks involved in cryptocurrency investments.
- Select a reputable and regulated cryptocurrency exchange or platform for buying and selling.
- Use strong passwords and enable two-factor authentication to secure your account.
- Diversify your portfolio by investing in multiple cryptocurrencies or other asset classes.
- Stay updated with the latest market trends, news, and regulatory changes, and be prepared to adapt your strategy accordingly.
Following this checklist will help you build a solid foundation for successful and secure cryptocurrency investing.

.svg)

Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)








.svg)




.png)