How to Get Into Crypto Trading in 2025: A Step-by-Step Beginner’s Guide

Cryptocurrency trading has surged in popularity, presenting a fast-paced and potentially rewarding avenue for growing your wealth. If you’re wondering how to get into crypto trading, you’re not alone. With thousands of digital assets available, dozens of cryptocurrency exchanges to choose from, and a market that operates 24/7, diving into the crypto market can feel overwhelming at first. This beginner-friendly guide will walk you through the essential steps to confidently start your crypto trading journey in 2025.
What Is Crypto Trading?
Crypto trading refers to the process of buying and selling digital currencies such as Bitcoin (BTC), Ethereum (ETH), and thousands of other crypto assets with the aim of profiting from their price movements. Unlike traditional markets, the cryptocurrency market never sleeps—trading happens around the clock, every day of the week. This continuous operation offers traders greater flexibility and more frequent opportunities to capitalize on market trends.
Moreover, crypto trading leverages blockchain technology, which underpins digital currencies and ensures secure, transparent transactions. Unlike traditional currencies issued by central banks, digital currencies operate on decentralized blockchain networks, making them unique assets that can experience rapid value changes. This volatility can present both lucrative opportunities and significant risks, making it essential for traders to develop a good understanding of the market dynamics before getting started.
Step-by-Step Guide to Get Into Crypto Trading
Step 1: Learn the Basics of Cryptocurrency
Before you start trading, it’s crucial to grasp the fundamentals of what you’re dealing with. Cryptocurrency is a form of digital currency secured by cryptography and often powered by blockchain technology. These digital assets come in various types:
- Coins like Bitcoin and Ethereum, which operate on their own blockchains.
- Tokens, which can represent assets or utilities within decentralized finance (DeFi) projects or non-fungible tokens (NFTs).
- Stablecoins such as USDC or USDT, designed to maintain a stable value by pegging to fiat currencies like the US dollar.
The crypto market is known for its high volatility, meaning prices can swing dramatically in short periods. This volatility creates opportunities for profits but also increases risk. To build a solid foundation, explore educational resources such as Token Metrics’ blog, YouTube tutorials, and crypto-focused communities on Reddit and Twitter (now X). These platforms can help you understand key concepts and stay updated on market conditions.
Step 2: Choose the Right Exchange
A crypto exchange is your gateway to the market, enabling you to buy, sell, and trade digital assets. Selecting the right crypto platform is essential for a smooth trading experience. In 2025, some of the top cryptocurrency exchanges include:
- Binance, known for its low fees and extensive selection of crypto assets.
- Coinbase, which offers a beginner-friendly interface ideal for new traders.
- Kraken, favored for its advanced trading tools and robust security.
- Token Metrics, which combines research, AI-powered trading signals, and AI crypto trading.
When choosing an exchange, consider factors like high liquidity (ensuring you can buy and sell assets easily), strong security measures, regulatory compliance, and a wide range of trading pairs. These elements help ensure your trades execute efficiently and your funds remain safe.
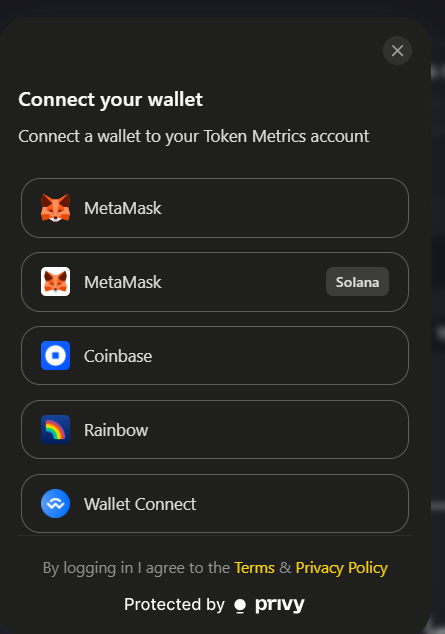
Step 3: Create and Secure Your Account
Once you’ve selected an exchange, the next step is to create your crypto account. This typically involves:
- Signing up with your email and creating a secure password.
- Completing KYC (Know Your Customer) verification to comply with regulatory standards.
- Enabling 2-Factor Authentication (2FA) to add an extra layer of security.
After setting up, you can fund your account using fiat currency such as US dollars or euros through bank transfers, debit cards, or other payment methods supported by the platform. Having a secure and verified account is vital to protect your assets and ensure smooth transactions.
Step 4: Choose a Trading Style

Your trading style should align with your financial goals, available time, and risk tolerance. Common approaches include:
- Day Trading: Making multiple trades within a single day to capitalize on short-term price fluctuations.
- Swing Trading: Holding positions for several days or weeks to benefit from medium-term trends.
- Scalping: Executing rapid trades to profit from small price movements.
- HODLing: Long-term holding based on confidence in a project’s future.
- AI-Powered Trading: Utilizing platforms like Token Metrics that use artificial intelligence to automate and optimize trading decisions.
Understanding your preferred style helps you develop a consistent strategy and manage risk effectively.
Step 5: Learn Technical and Fundamental Analysis
Successful cryptocurrency trading hinges on your ability to analyze the market. Two primary methods are:
- Technical Analysis (TA): This involves studying charts, indicators like RSI (Relative Strength Index), MACD (Moving Average Convergence Divergence), and Bollinger Bands to recognize patterns, support and resistance levels, and predict price movements based on historical data and volume.
- Fundamental Analysis (FA): This focuses on evaluating the underlying value of a crypto asset by examining the project’s use case, team, tokenomics (such as supply and utility), and overall market sentiment influenced by news and developments.
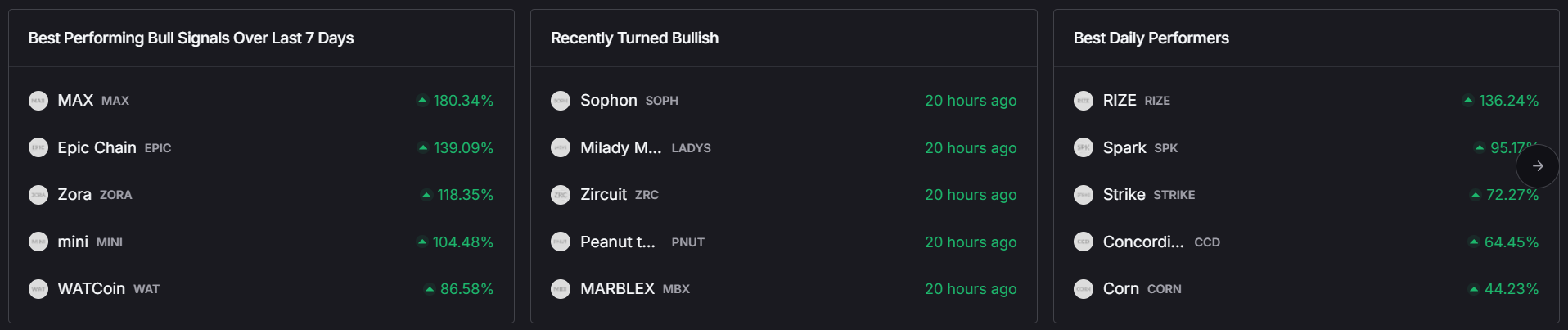
Platforms like Token Metrics simplify these analyses by providing AI-generated grades and insights that combine technicals, fundamentals, and sentiment, helping traders make informed decisions.

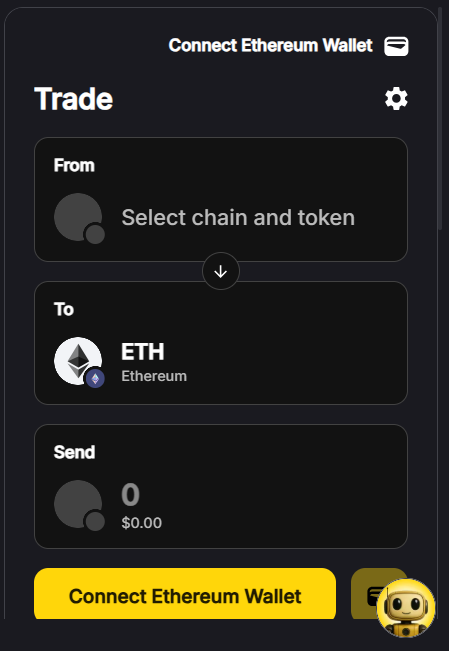
Step 6: Place Your First Trade
With your research complete and your crypto account funded, you’re ready to place your first trade. Start by selecting a trading pair, such as ETH/USDT, depending on the assets you want to buy or sell. Then, choose an order type:
- Market Order: Executes instantly at the current market price.
- Limit Order: Executes only when the price reaches a specified level.
- Stop-Limit Order: Triggers a limit order once a certain price condition is met.
To manage risk, set a stop-loss order to automatically sell if the price drops to a certain point, and consider take-profit orders to lock in gains when the price reaches your target. It’s wise to start small, using only funds you can afford to lose while you learn the ropes.
Step 7: Track Performance and Learn from Mistakes
Trading is a continuous learning process. Keep a trading journal or use analytics tools to record your entry and exit points, profits and losses, and emotions or events that influenced your decisions. This practice helps you identify patterns in your behavior and refine your strategy over time. Tools like Token Metrics offer backtesting features, AI signal alerts, and portfolio performance tracking to support your growth as a trader.
Tools That Make Crypto Trading Easier in 2025
Token Metrics
Token Metrics stands out as a powerful crypto research and trading platform designed to assist both beginners and experienced traders. It uses AI to grade crypto assets, sends bullish or bearish alerts, and offers auto-managed portfolios known as Indices. Users gain access to real-time market insights and advanced features like the Moonshots tab and AI Agent (crypto chatbot), which help identify optimal entry points and predict price movements. A 7-day free trial allows you to explore these premium tools risk-free.
Wallets
Securing your digital currency is crucial. Hot wallets like MetaMask and Trust Wallet provide easy access for regular trading, while cold wallets such as Ledger and Trezor offer maximum security by storing assets offline, protecting them from hacks and theft.
Tips for Success as a New Crypto Trader
- Start Small: Begin with modest investments and gradually increase as you gain confidence.
- Manage Risk: Never invest more than you can afford to lose, and always use stop-loss orders.
- Avoid Emotional Trading: Stick to your plan and avoid impulsive decisions driven by fear or greed.
- Stay Informed: Keep up with market trends, news, and macroeconomic factors that affect the cryptocurrency market.
- Leverage AI Tools: Utilize platforms like Token Metrics to reduce guesswork and enhance your trading strategies.
Common Mistakes to Avoid
New traders often fall into pitfalls such as:
- Chasing Pumps: Buying after a cryptocurrency’s price has already surged, which can lead to losses.
- Overtrading: Making excessive trades without a clear strategy, increasing fees and risk.
- Neglecting Security: Failing to use 2FA or hardware wallets can expose your funds to theft.
- FOMO and Panic Selling: Reacting emotionally to price swings instead of following a disciplined approach.
By relying on research-backed tools and maintaining discipline, you can navigate the crypto market more effectively.
Final Thoughts
Entering the world of crypto trading in 2025 is more accessible than ever but also highly competitive. Success requires more than enthusiasm; it demands strategy, the right tools, and disciplined execution. Whether you’re aiming to trade full-time or simply capitalize on market opportunities, platforms like Token Metrics provide AI-powered research, real-time alerts, and dynamic indices that simplify decision-making and enhance your ability to trade smarter.
Are you ready to begin your crypto journey? Sign up for Token Metrics today and unlock the power of AI-driven cryptocurrency trading to maximize your potential profits in this exciting digital market.
Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)








.svg)




.png)