
How to Get Into Cryptocurrency Trading in 2025: A Step-by-Step Beginner’s Guide

Cryptocurrency has evolved from a speculative trend into a mainstream financial ecosystem. More businesses and industries now accept bitcoin as a form of payment, reflecting the growing mainstream adoption of cryptocurrency. In 2025, crypto trading has become one of the most accessible and potentially profitable ways to grow your wealth online. With thousands of tokens available, advanced trading tools, and platforms tailored to every skill level, getting started has never been easier—but it’s important to approach crypto trading thoughtfully and strategically.
Whether you want to build passive income, day trade for profits, or invest in the future of decentralized finance, this guide will walk you through how to get into crypto trading, what you need to know, and how tools like Token Metrics can help you trade smarter using AI-powered insights.
🚀 What Is Crypto Trading?
Crypto trading involves buying and selling cryptocurrencies with the goal of making a profit. Unlike traditional stock markets, the crypto market operates 24/7, allowing traders to respond to opportunities at any time. This constant availability creates a dynamic environment where investors can capitalize on both rising and falling prices depending on their trading strategies.
To buy cryptocurrency, start by selecting a secure and reputable exchange or broker. Next, fund your account using your preferred payment method, review any associated fees, and then place an order to purchase your chosen cryptocurrency.
There are several types of crypto trading to consider:
- Spot Trading: This is the simplest form of trading, where you buy and sell crypto assets at the current market price. The transactions are settled immediately, and the assets are directly transferred to your wallet or exchange account.
- Margin Trading: Margin trading allows you to borrow funds to increase your trading exposure, potentially amplifying gains but also increasing risk. It’s important to understand the risks involved before engaging in margin trading.
- Futures Trading: In futures trading, you speculate on the price of cryptocurrencies at a future date using leverage. This type of trading is more complex and is typically suited for experienced traders.
- Automated/AI Trading: Many investors now use bots or AI-powered agents to execute trades automatically based on pre-set strategies or market signals, reducing the need for constant monitoring.
Understanding these different methods helps you choose the best approach based on your goals and risk tolerance.
🧠 Step-by-Step: How to Get Into Crypto Trading
Step 1: Understand the Basics of Cryptocurrency
Before diving into crypto trading, it’s essential to grasp the fundamentals of what cryptocurrencies are and how they function. At the core is the blockchain, a decentralized public ledger that records every cryptocurrency transaction securely and transparently. Individual coin ownership records are stored in this digital ledger, which uses a consensus mechanism to secure transaction records. Cryptography is used to secure transactions and maintain the integrity of the blockchain, ensuring privacy and trust in the system.
The most well-known digital currency is Bitcoin (BTC), the first cryptocurrency that pioneered the concept of decentralized digital money. Bitcoin was first released as open-source software in 2009, marking the beginning of the cryptocurrency era. Bitcoin and other altcoins are examples of virtual currencies, which are digital representations of value not issued by a central authority. Beyond Bitcoin, there are thousands of altcoins—alternative cryptocurrencies like Ethereum, Solana, and newer tokens such as TMAI—that offer various features and use cases.
You should also familiarize yourself with stablecoins, which are digital currencies pegged to fiat currencies like the U.S. dollar (examples include USDC and USDT). Stablecoins help reduce volatility and are often used for trading and payments within the crypto ecosystem.
Understanding key terms such as wallets (digital wallets used to store crypto assets securely), exchanges (platforms where crypto is traded), gas fees (transaction costs on blockchains), and private keys (secure codes that grant access to your crypto) is crucial for safe and effective trading. Proper management of wallet keys or seed phrases is essential to maintain the security and privacy of your digital wallet.
Step 2: Types of Cryptocurrency and Their Uses
The world of digital currencies is vast, with each cryptocurrency offering unique features and serving different purposes in the crypto market. The most popular cryptocurrency, Bitcoin, was the first cryptocurrency ever created and remains a benchmark for value and security. Bitcoin is widely used for online payments, storing value, and as a hedge against inflation, making it a staple in many investment portfolios.
Beyond Bitcoin, there are numerous other digital currencies, each designed with specific use cases in mind. Ethereum, for example, is renowned for its smart contract capabilities, enabling developers to build decentralized applications and launch new cryptocurrency offerings. Litecoin and Ripple are also well-known for their fast transaction speeds and low fees, making them attractive for everyday payments and cross-border transfers.
Some digital currencies, like Tether (USDT), are stablecoins pegged to the US dollar, providing a stable store of value and facilitating seamless trading within the crypto market. As of June 2023, there are more than 25,000 cryptocurrencies in the marketplace, showcasing the vast diversity and innovation within the digital asset ecosystem. Understanding the different types of cryptocurrencies and their uses is essential for anyone looking to invest, make payments, or participate in the growing world of digital assets. By exploring the various options, you can find the right currencies to match your investment goals and payment needs.
Step 3: Understanding Crypto Market Data and Market Cap
Navigating the cryptocurrency market requires a solid grasp of crypto market data and market capitalization. Market capitalization, often referred to as market cap, is a key metric that represents the total value of a cryptocurrency—calculated by multiplying the current price by the total circulating supply. The cryptocurrency market has become intertwined with the broader capital markets, making it sensitive to the same economic forces. This figure helps investors gauge the size, stability, and overall significance of a digital asset within the crypto market.
In addition to market cap, crypto market data includes vital information such as transaction volume, price fluctuations, and the number of active transactions. Monitoring these data points allows investors to assess the liquidity and momentum of a cryptocurrency, helping them make informed decisions about when to buy, sell, or hold. For instance, a cryptocurrency with a high market cap and robust trading volume is generally considered more established and less susceptible to dramatic price swings than smaller, less liquid assets.
By regularly analyzing market capitalization and other crypto market data, investors can better understand the value and potential risks associated with different cryptocurrencies, ultimately making smarter moves in the fast-paced crypto market.
Step 2: Choose a Reliable Crypto Exchange
To start trading, you need to register on a cryptocurrency exchange—a marketplace where digital assets are bought, sold, and traded. There are many exchanges available, each with different features, fees, and security levels. Some exchanges are regulated by an exchange commission or similar regulatory body, which can provide additional security and oversight.
Best Centralized Exchanges (CEXs) and Crypto Trading Platforms:
- Coinbase: Ideal for beginners in the U.S., Coinbase offers a user-friendly interface and strong regulatory compliance.
- Binance: Known for low transaction fees and a vast selection of tokens, Binance is popular among active traders.
- Kraken: Offers strong security measures and advanced trading tools suitable for more experienced investors.
- Token Metrics: While not an exchange itself, Token Metrics integrates with major exchanges and provides AI-driven insights to help you make smarter trades.
Best Decentralized Exchanges (DEXs):
- Uniswap (Ethereum-based): Allows peer-to-peer trading without a trusted third party.
- PancakeSwap (BNB Chain): Popular for trading BEP-20 tokens with lower fees.
- GMX (Arbitrum/Avalanche): Offers decentralized futures trading with leverage.
When choosing an exchange, consider factors such as security, fees, token availability, and ease of use. After selecting an exchange, create an account, complete any required identity verification, and secure your login credentials carefully.
Step 5: Transaction Fees and Costs Explained
Every time you make cryptocurrency transactions, you’ll encounter transaction fees—an essential part of how blockchains operate. These fees are paid to miners or validators who process and confirm transactions, ensuring the security and integrity of the network. The amount you pay in transaction fees can vary widely depending on the cryptocurrency and the current level of network activity.
For example, Bitcoin transaction fees tend to rise during periods of high demand, sometimes making small transactions less cost-effective. On the other hand, cryptocurrencies like Ethereum may offer lower fees, though these can also fluctuate based on network congestion. Some digital currencies and exchanges even provide fee discounts or zero-fee promotions, which can be especially appealing for frequent traders and investors.
Understanding transaction fees and overall costs is crucial for anyone looking to make efficient and cost-effective cryptocurrency transactions. By factoring in these expenses, you can better plan your trades and avoid unexpected costs that might eat into your investment returns.
Step 3: Secure Your Crypto Wallet
Once you have an account on an exchange, you’ll need a crypto wallet to store your digital assets securely. Cryptocurrency is stored in digital wallets, and proper management of wallet keys is essential to keep your assets secure. Wallets come in two main types:
- Hot Wallets: These are connected to the internet and include software wallets like MetaMask and Trust Wallet. Hot wallets are convenient for frequent trading but are more vulnerable to hacks. Digital assets stored in hot wallets are accessible online, which increases convenience but also risk.
- Cold Wallets: These are offline storage solutions, and include hardware wallets such as Ledger and Trezor. Hardware wallets are a type of cold wallet specifically designed to store cryptocurrency and private keys offline, providing enhanced security. Cold wallets are ideal for long-term holding because they minimize exposure to cyber threats. Digital assets stored in cold wallets are kept offline, reducing the risk of unauthorized access.
For active trading, a hot wallet linked to your exchange account is practical. However, to protect significant holdings, transferring assets to a cold wallet is recommended.
Step 4: Fund Your Trading Account
To begin trading, you must deposit funds into your exchange account. Most platforms accept various deposit methods:
- Fiat Deposits: You can add money via bank transfers or credit cards, which will convert your dollars or other currencies into digital assets.
- Crypto Deposits: If you already own cryptocurrency, you can transfer it from another wallet or exchange.
- Stablecoin Transfers: Using stablecoins like USDC or USDT allows for quick, low-fee trading without exposure to volatility.
Accounts on regulated exchanges are typically subject to identity verification and compliance checks. This regulatory oversight helps prevent fraud and ensures the security and transparency of digital asset trading.
Before funding your account, check the fees, minimum deposit amounts, and processing times to avoid surprises.
Step 5: Start with Spot Trading
For beginners, spot trading is the most straightforward way to enter the crypto market. In spot trading, cryptocurrencies are exchanged directly between buyers and sellers at the current market price. It involves buying a cryptocurrency at the current price and holding or selling it later to realize gains.
For example, you might buy Bitcoin at $30,000 and sell it when the price reaches $35,000. Alternatively, you could purchase Ethereum during a market dip and hold it through a bull run. Some traders also focus on low-cap altcoins aiming for short-term price movements.
Starting small allows you to learn how to read market trends, use order types like market and limit orders, and interpret price charts without risking too much capital.
Step 6: Learn Technical & Fundamental Analysis
To improve your trading decisions, it’s important to combine technical analysis (TA) and fundamental analysis (FA). In fundamental analysis, the cryptocurrency market cap is a key metric used to evaluate the size and significance of a project within the crypto ecosystem.
Technical Analysis:
TA involves studying price charts and trading indicators such as MACD, RSI, and Bollinger Bands. These tools help identify support and resistance levels, volume spikes, and trend reversals, enabling traders to time their entries and exits.
Fundamental Analysis:
FA focuses on evaluating a cryptocurrency project’s underlying value by analyzing the developer team, use case, tokenomics, partnerships, and roadmap progress. Staying updated with crypto news, whitepapers, and project announcements is essential.
Platforms like Token Metrics provide AI-generated grades and signals for thousands of tokens, helping investors filter through the vast number of crypto assets and identify promising opportunities.
👉 Try Token Metrics free to access crypto ratings, bullish and bearish signals, and moonshot token discoveries.
Step 7: Develop a Trading Strategy
Trading without a plan is risky. Developing a strategy aligned with your goals, time availability, and risk tolerance is key. Cryptocurrency investments are speculative and carry unique risks compared to traditional assets, so your strategies should be tailored to address these specific challenges.
Popular trading strategies include:
- Day Trading: Executing multiple trades within a single day to profit from short-term price movements.
- Swing Trading: Holding positions for several days or weeks to capitalize on market momentum.
- HODLing: Buying and holding cryptocurrencies long-term, betting on significant gains over time.
- Automated Trading: Using bots or AI tools to automate trading decisions and execution based on predefined criteria.
Tools like the Token Metrics AI Agent can help automate trades, enabling you to follow systematic strategies without constant monitoring.
Step 8: Manage Risk and Emotions
The crypto market is known for its high volatility, making risk management crucial for preserving capital and sustaining profits.
Here are some essential risk management tips:
- Never invest more money than you can afford to lose.
- Use stop-loss orders to limit potential losses and take-profit orders to secure gains.
- Diversify your portfolio across different crypto assets to reduce exposure.
- Avoid making decisions based on hype or emotional reactions.
- Regularly take profits and review your trades to learn from mistakes.
- Retail investors should be especially cautious, as they are often targeted by scams and are more vulnerable to market volatility. Stay informed about regulatory developments that may impact your access and protection.
- Be wary of any offers or platforms that promise high or guaranteed returns—these are often scams and should be avoided.
Platforms like Token Metrics offer portfolio analytics and backtesting tools to help you understand your risk profile and optimize your investment approach.
Step 12: Avoiding Cryptocurrency Scams and Fraud
The rapid growth of the cryptocurrency market has unfortunately attracted its share of scams and fraudulent schemes. Investors need to be vigilant when dealing with digital currencies, as cryptocurrency scams can take many forms—from phishing attacks and Ponzi schemes to fake exchanges and misleading investment opportunities promising significant gains with little or no risk. Some cryptocurrency exchanges have experienced high-profile hacks resulting in significant financial losses, underscoring the importance of choosing secure platforms and practicing good security habits.
To protect yourself, always conduct thorough research before investing in any cryptocurrency or project. Stick to reputable cryptocurrency exchanges and wallets, and never share your wallet information or passwords with anyone. Be especially cautious of offers that guarantee returns or sound too good to be true, as these are often red flags for fraud. Remember, the cryptocurrency market is inherently risky, and no investment is without potential downsides.
By staying informed and practicing good security habits, you can reduce your exposure to scams and make safer, more confident investment decisions in the world of digital currencies.
Step 9: Track Performance and Improve
Maintaining a trading journal to record your wins, losses, and reasoning behind trades is invaluable. Tracking how your assets are valued in dollars or other currencies helps you assess your trading performance over time. Over time, this practice helps you identify which assets and strategies work best for you.
Analyzing your transaction data and reviewing market trends will enable you to refine your entries and exits. Using analytics platforms to rebalance your portfolio and adjust your strategy based on performance insights can improve your long-term success.
Step 14: Exploring a Wider Range of Cryptocurrencies
While Bitcoin and Ethereum dominate headlines, the cryptocurrency market is filled with a wider range of digital currencies, each offering unique features and investment opportunities. Exploring beyond the most popular cryptocurrencies can help investors diversify their portfolios and tap into new areas of growth.
Alternative cryptocurrencies like Litecoin, Ripple, and Cardano each bring their own strengths—whether it’s faster transaction speeds, innovative consensus mechanisms, or specialized use cases. Additionally, new cryptocurrencies are launched regularly, introducing fresh technologies and business models to the market. By keeping up with the latest developments and exploring a broader selection of currencies, investors can discover promising projects and potentially benefit from early adoption.
Diversifying across a wider range of digital currencies not only helps manage risk but also increases the chances of finding high-performing investments in different market conditions. Staying curious and open to new opportunities is key to long-term success in the ever-evolving cryptocurrency market.
🧠 Why Use Token Metrics for Crypto Trading?
Token Metrics is an AI-powered crypto analytics platform designed to help traders and investors discover high-potential crypto assets and optimize their strategies in the fast-moving cryptocurrency market. The platform also assists users in identifying where to allocate new capital for maximum growth potential, ensuring that investments are directed toward the most promising opportunities.
Features That Help Beginners:
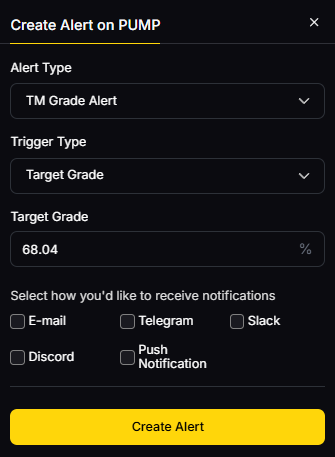
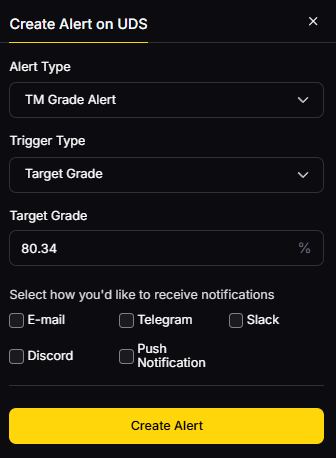
- Investor & Trader Grades for over 6,000 tokens, providing an easy way to assess quality.
- Bullish and Bearish AI signals that indicate potential market moves.
- Custom alerts for price changes, grade updates, and trend shifts.
- A Moonshots section highlighting promising low-cap tokens.
- Backtesting tools to simulate strategies and build smarter portfolios.
Whether you’re new to crypto trading or looking to scale your investments, Token Metrics offers a data-driven edge in a crowded market.
👉 Start your free 7-day trial today and trade with confidence.
Final Thoughts
Getting into crypto trading in 2025 is easier, safer, and more rewarding than ever—if you have the right tools and mindset. With thousands of cryptocurrencies and an always-on market, there are endless opportunities but also inherent risks.
By learning the basics of digital currencies, choosing reliable crypto exchanges, managing your risk carefully, and leveraging advanced tools like Token Metrics, you can start trading crypto smarter, not harder.
Remember, crypto trading isn’t a get-rich-quick scheme—it’s a skill that develops over time. As financial institutions and government agencies continue to shape regulations around securities and virtual currency, staying informed about the evolving landscape is crucial for all crypto traders. Your journey begins with your first trade.

.svg)

Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)













.svg)




.png)