
How to Sell Large Amounts of Crypto: Essential Tips and Strategies

Selling large amounts of crypto requires careful planning, a solid understanding of the market, and knowledge of the different trading methods available. Whether you want to sell bitcoin or other digital assets, it’s important to consider factors such as the current market price, tax implications, and security measures to ensure a smooth and profitable transaction. In this article, we will explore how to sell large amounts of crypto effectively, covering everything from centralized exchanges to peer-to-peer platforms and over-the-counter (OTC) trading.
Introduction to Crypto Sales
When it comes to how to sell large amounts of crypto, understanding the market landscape is the first step. There are several trading methods to choose from, including centralized exchanges, peer-to-peer platforms, and OTC trading desks. Each option offers unique advantages and challenges, so selecting the right approach depends on your specific needs and the amount of bitcoin or other crypto assets you intend to sell.
Tax implications also play a crucial role in crypto sales. Selling digital assets like Bitcoin often triggers a taxable event, subject to capital gains tax. Knowing how these taxes apply in your jurisdiction and maintaining accurate transaction records can help you stay compliant and avoid unexpected liabilities.
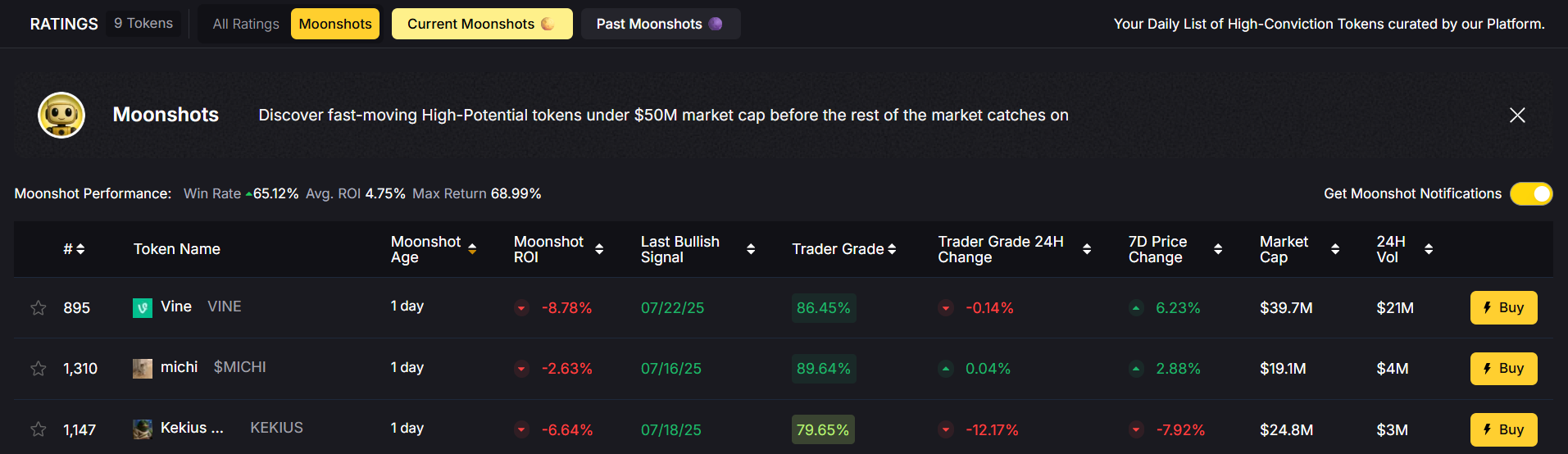
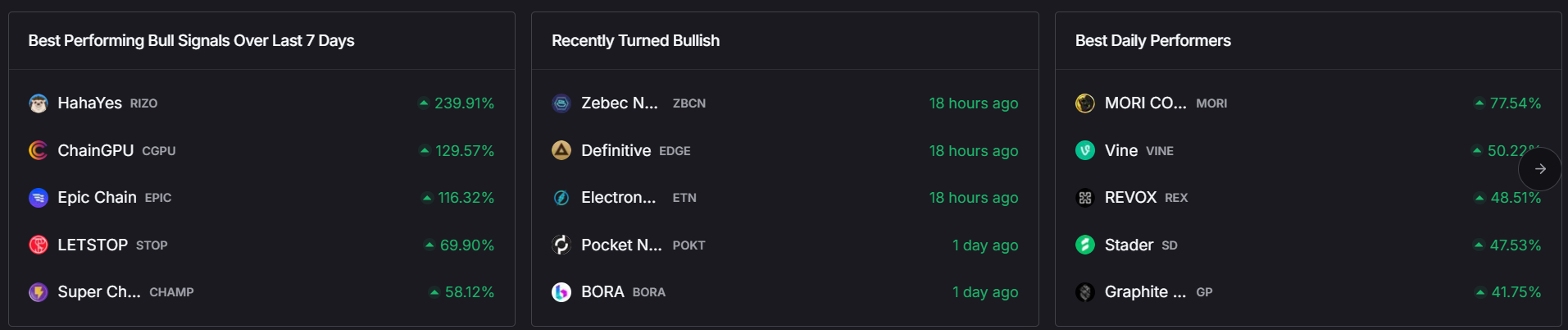
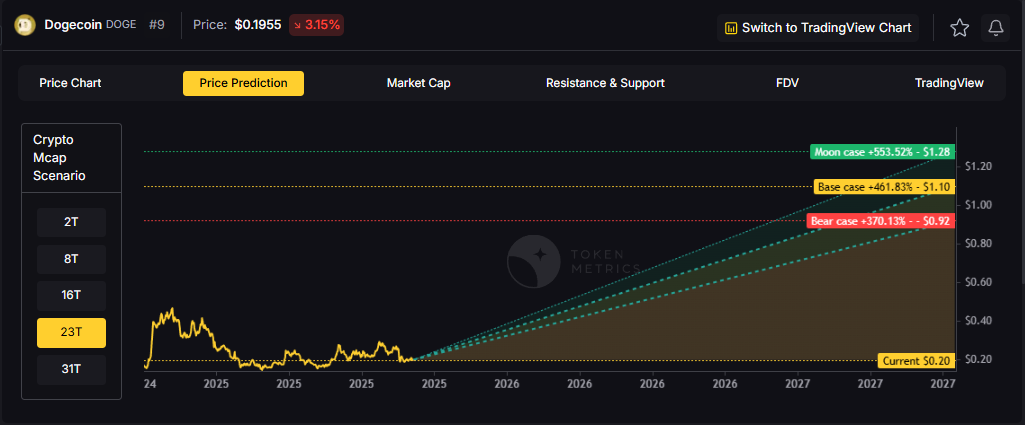
Another key consideration is the current market price and price fluctuations. Since cryptocurrencies are volatile assets, large transactions can impact the market price, leading to price slippage and unfavorable rates. Therefore, minimizing market impact by using strategic selling methods is essential to maximize returns.
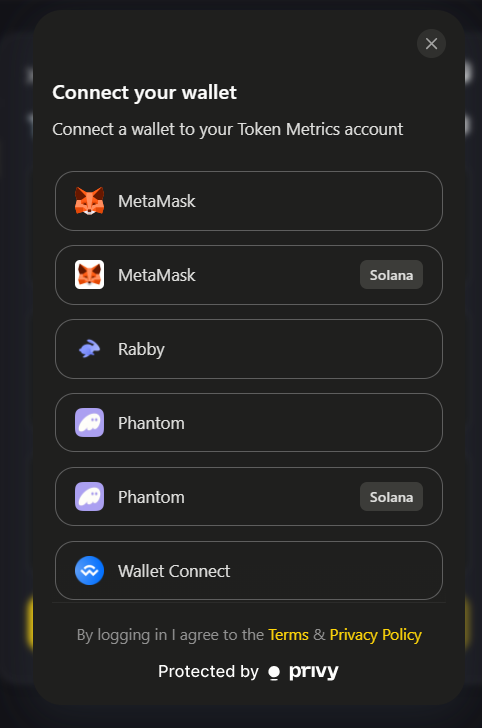
Finally, opting for a user-friendly platform with low trading fees and robust security measures ensures a straightforward process. Features like two-factor authentication and withdrawal limits help protect your holdings while providing flexibility in managing large transactions.
Trading Methods
Centralized exchanges are a popular choice for selling bitcoin due to their convenience and liquidity. Platforms like Token Metrics, Binance and Coinbase allow users to sell crypto quickly, but they often come with high transaction fees and withdrawal limits that can affect large transactions. Additionally, these exchanges have a verification process and security protocols such as two-factor authentication to safeguard user accounts.
Peer-to-peer trade platforms offer an alternative by enabling you to sell bitcoin directly to other users. This method often involves lower fees and more flexible payment methods, including bank transfers and cash. Peer-to-peer platforms facilitate trade directly between parties, reducing the market impact and providing a more personalized service. However, they require caution to avoid security risks when dealing with other users.
For substantial amounts of bitcoin, OTC trading desks are particularly suitable. OTC services allow buyers and sellers to conduct large transactions privately, avoiding the price fluctuations and market impact associated with regular exchange orders. OTC desks offer personalized service and often have lower withdrawal fees and transaction costs compared to major exchanges. Using OTC trading can help you sell crypto safely and efficiently without affecting the overall market price.
Another option is using crypto debit cards, which allow you to convert bitcoin to fiat currency and spend it directly. While convenient, these cards may have high fees and limited withdrawal options, making them less ideal for very large sums.
Crypto Exchange Options
When selecting where to sell crypto, major exchanges and crypto trading platforms like Token Metrics, Binance, Coinbase, and Kraken stand out due to their extensive payment methods and strong security measures. These platforms support bank transfers, credit cards, and sometimes even crypto debit cards, providing flexibility in how you receive funds.
Security is paramount on centralized exchanges. Reputable exchanges implement rigorous security measures, including cold storage for digital currencies, regular security audits, and mandatory two-factor authentication. Enabling two-factor authentication on your exchange account is essential to prevent unauthorized access and protect your crypto holdings.
Some major exchanges offer personalized services tailored for large transactions. These services can help minimize market impact by facilitating limit orders or OTC transactions through their internal desks. Choosing an exchange with low trading fees and withdrawal fees can significantly improve your net proceeds when selling large amounts of crypto.
Alternative Sales Methods
Bitcoin ATMs provide a quick and convenient way to sell bitcoin directly for cash. Using a bitcoin ATM, you can send bitcoin to a deposit address or scan a QR code to complete the transaction within a few hours. However, bitcoin ATMs often charge high fees and have limited withdrawal limits, making them less suitable for selling large sums.
Peer-to-peer platforms like LocalBitcoins or Paxful allow you to sell bitcoin directly to other users. These platforms offer a variety of payment methods and typically have lower fees than centralized exchanges. Peer-to-peer trade can be a straightforward process, but it requires vigilance to avoid scams or security risks when dealing with other users.
OTC trading services are the preferred choice for handling large transactions. OTC desks provide a personalized experience, allowing you to negotiate a specific price and avoid price slippage. These services are designed to handle amounts of bitcoin that would otherwise disrupt the market if sold on regular exchanges.
Additionally, some crypto exchange services such as TransFi’s Ramp offer comprehensive solutions for selling large amounts of bitcoin. They combine the benefits of OTC trading with streamlined payment and withdrawal options, making it easier to convert bitcoin to fiat currency securely and efficiently.
Payment and Withdrawal Options
Choosing the right payment and withdrawal methods is crucial when selling large amounts of crypto. Bank transfers are commonly used for receiving fiat currency after selling bitcoin. While bank transfers are generally secure, they can involve high fees and may take several days to process, which could delay access to your funds.
Crypto debit cards provide an alternative by allowing you to withdraw cash or make purchases directly using your crypto balance. However, these cards often come with high fees and are not accepted everywhere, which limits their usefulness for large transactions.
Peer-to-peer platforms usually support a wide range of payment methods, including cash deposits, bank transfers, and online payment services. Selecting a payment method with low fees and fast processing times helps optimize your sale and reduces the risk of delays.
When using centralized exchanges, be mindful of withdrawal limits and withdrawal fees. Some exchanges impose daily or monthly limits that could restrict how much fiat currency you can access at once. Understanding these limits ahead of time ensures you can plan your sales accordingly.
Security and Safety
Security is a top priority when selling large amounts of bitcoin or other crypto assets. Enabling two-factor authentication on your exchange account and wallets is essential to protect against unauthorized access. This added layer of security helps safeguard your digital assets from hacking attempts.
Reputable exchanges and platforms implement advanced security measures such as cold storage, where the majority of funds are kept offline, and regular security audits to identify vulnerabilities. Using these platforms reduces the risk of losing your crypto due to security breaches.
In addition to platform security, using a secure wallet to store your bitcoin before and after the sale is critical. Hardware wallets or trusted software wallets with strong encryption provide the best protection.
Regularly monitoring your account activity and being aware of potential security risks, such as phishing attacks or suspicious transactions, can help you respond quickly to threats and prevent losses.
Taxes and Regulations
Understanding the tax implications of selling digital assets is vital. In many jurisdictions, selling bitcoin constitutes a taxable event subject to capital gains tax. The amount of tax owed depends on factors like how much bitcoin you sold, the holding period, and your local tax laws.
Tax regulations for cryptocurrencies vary significantly between countries, so it’s important to familiarize yourself with the rules that apply to you. Keeping detailed records of your transactions, including dates, amounts, and prices, will make tax reporting easier and more accurate.
Some countries have specific regulations governing cryptocurrency exchanges and OTC transactions. Compliance with these laws ensures your sales are legitimate and reduces the risk of legal issues.
Consulting a tax professional experienced in digital currencies can provide guidance tailored to your situation, helping you navigate complex tax laws and optimize your tax liabilities.
Avoiding Common Mistakes
Many sellers face challenges when handling large crypto transactions. One common mistake is not understanding the tax implications, which can lead to unexpected capital gains tax bills and financial losses.
Failing to use two-factor authentication leaves accounts vulnerable to hacking and unauthorized access, risking the loss of your crypto holdings.
Choosing an unreliable or unregulated exchange can result in high fees, poor customer service, and even security breaches. Always select reputable exchanges with a solid track record.
Neglecting to monitor your account activity regularly increases the risk of unnoticed fraudulent transactions or security breaches. Staying vigilant helps protect your assets.
Staying Informed and Adapting
The cryptocurrency market is highly volatile and subject to rapid changes. Staying informed about market trends and price fluctuations enables you to time your sales effectively, minimizing market impact and maximizing profit.
Regulations and tax laws surrounding crypto are continually evolving. Keeping up-to-date with these changes ensures you remain compliant and avoid legal complications.
Regularly reviewing and enhancing your security measures, such as updating passwords and enabling new security features, helps protect your accounts from emerging threats.
Adapting your trading strategies in response to market conditions and regulatory changes is key to successful crypto sales over time.
Best Practices for Crypto Sales
To sell large amounts of crypto successfully, choose a reputable exchange or platform that offers low fees, strong security measures, and flexible payment options. Understanding the tax implications and maintaining accurate transaction records will keep you compliant and prepared for tax season.
Always enable two-factor authentication and use secure wallets to safeguard your crypto assets. Regularly monitor your accounts for suspicious activity to prevent losses.
Finally, stay informed about market trends, regulatory updates, and security best practices. By adapting your approach to changes in the crypto landscape, you can maximize profits, minimize risks, and sell bitcoin or other digital currencies with confidence.

.svg)

Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)

















.svg)




.png)