In the rapidly evolving cryptocurrency market, investors face unprecedented challenges in tracking and managing their digital asset portfolios. Cryptocurrency market capitalization, representing the total value of all cryptocurrencies combined, serves as a crucial metric for assessing overall market performance and investor sentiment, with its fluctuations providing key insights for market analysis. With prices fluctuating wildly and market narratives shifting weekly rather than quarterly, staying ahead requires more than just luck—it demands smart, systematic approaches. The crypto market cap index 2025 ushers in a new era of investment strategy by combining comprehensive Top 100 tracking with automatic risk management through a stablecoin safety net. This innovative approach offers investors broad market exposure while preserving capital during downturns, addressing many of the traditional pitfalls of crypto investing, and significantly improving efficiency in portfolio management and risk mitigation.
The Problem with Traditional Crypto Investing
The cryptocurrency market has expanded dramatically, now boasting a total market capitalization exceeding $4 trillion and encompassing over 20,000 distinct tokens worldwide. The cryptocurrency market cap is calculated by multiplying the price of each coin by its circulating supply, providing a key metric for ranking and assessing the overall market value. This explosive growth has made the investment landscape incredibly complex and volatile. Trading volume in the market often reaches billions of dollars daily, with BTC/USD pairs leading in liquidity and fair price discovery.
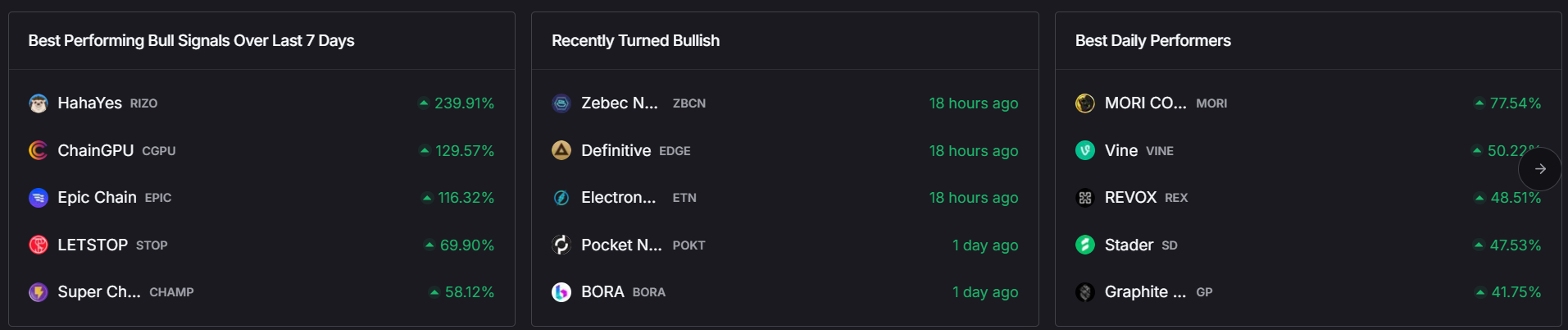
Past market cycles, such as the ICO boom of 2017 or the DeFi and NFT surges of 2020-2021, lasted for months, allowing investors some predictability. However, the 2024-2025 period is defined by rapid narrative rotations measured in weeks, not quarters.
For example, the market might see AI agent tokens surge 100-300% in the first three weeks of a quarter following major OpenAI announcements. Shortly after, attention shifts to blockchain gaming as industry giants announce integrations. Then, decentralized physical infrastructure networks (DePIN) gain traction with enterprise partnerships, followed by a focus on Real World Assets as regulatory clarity improves. This relentless pace renders traditional buy-and-hold strategies inadequate. Investors must either spend countless hours tracking over 100 tokens across multiple exchanges or risk missing the next major opportunity. In such a volatile environment, millions of dollars can be gained or lost in a matter of hours due to sudden price swings and market sentiment shifts.
Moreover, conventional crypto indices focusing on the top 10 assets offer limited diversification. Bitcoin and Ethereum typically dominate these portfolios, comprising 60-75% of holdings, which means these indices largely move in tandem with just two assets. This concentration misses the asymmetric returns and innovation emerging from mid-cap and emerging tokens. According to Token Metrics data analyzing over 6,000 cryptocurrencies, the top 100 tokens by market capitalization—calculated by multiplying each token's price by its circulating supply—outperformed the top-10 concentrated portfolios by an average of 34% in 2024, with this gap widening during periods of rapid narrative shifts. Volume and liquidity are also critical factors in the ranking and performance of these tokens, as higher trading volume often signals stronger market legitimacy and fairer pricing.
Introducing Automatic Top 100 Tracking
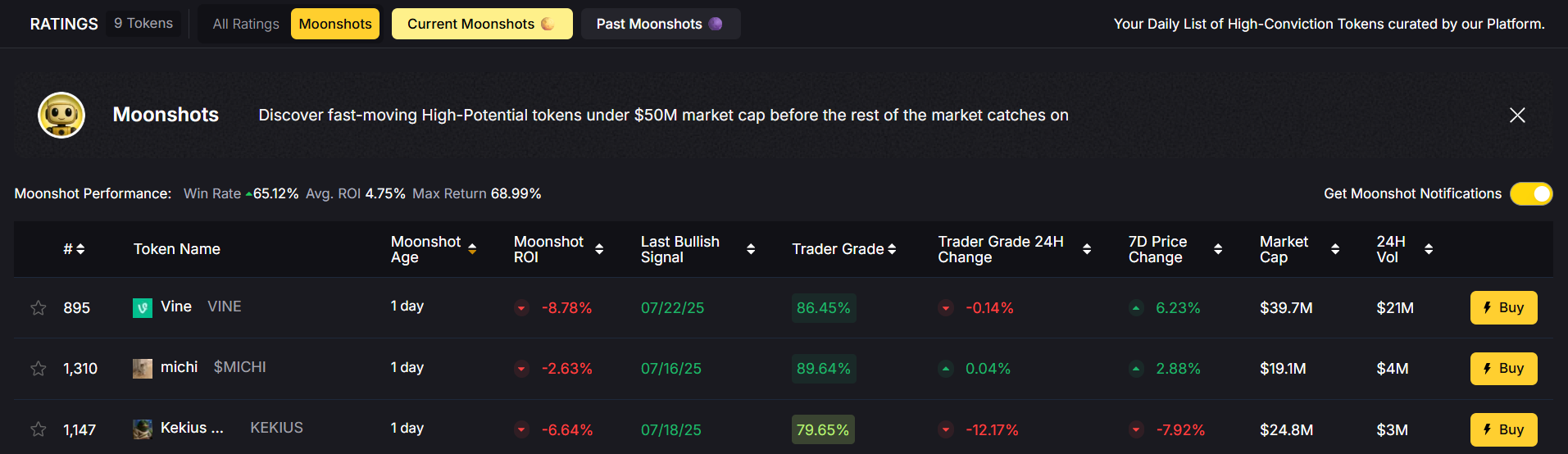
A smarter solution is to adopt systematic Top 100 market cap tracking, a methodology designed to capture the full breadth of the cryptocurrency market while maintaining disciplined, rules-based execution. This approach addresses several key challenges simultaneously. The index also serves as a measure of overall market performance and investor sentiment.
First, it provides comprehensive market coverage. Tracking the Top 100 cryptocurrencies by market capitalization offers exposure to Bitcoin and Ethereum for stability (around 40% of holdings), established large-cap tokens like Solana, XRP, and Cardano for proven track records, and mid-cap innovators in sectors such as AI, gaming, DeFi, and blockchain infrastructure where asymmetric returns often emerge. The platform provides tools for tracking and analyzing a wider range of assets, and it also captures emerging narratives before they reach mainstream attention.
Second, this strategy incorporates automatic rebalancing. The crypto market operates 24/7, and portfolios must adapt accordingly. Weekly automatic rebalancing ensures that as token values shift and rankings fluctuate, investors maintain alignment with current market dynamics. If a promising mid-cap token enters the Top 100, exposure is gained automatically. Conversely, if a token falls below the threshold, it is exited without emotional bias. Users also have the ability to customize certain settings or preferences within the platform.
Third, elimination of selection bias is a major benefit. Market cap weighting removes subjective decision-making—investors no longer need to predict which narrative will dominate next quarter. Instead, they hold a diversified basket weighted by market capitalization, allowing capital to flow naturally toward tokens gaining market significance. This systematic approach attracts a wider range of investors, including retail investors seeking systematic exposure, and prevents costly mistakes such as holding onto underperforming assets too long or missing out on emerging winners.
Token Metrics TM Global 100: Setting the Standard
While Top 100 tracking is not a new concept, Token Metrics has pioneered its optimal implementation through the TM Global 100 Index, blending institutional-grade execution with retail accessibility. The TM Global 100 Index was created to address the need for systematic, transparent crypto investing, and has attracted growing interest from financial institutions seeking exposure to digital assets. Token Metrics is a cryptocurrency investment research firm that leverages AI, machine learning, and crypto-native analysts to analyze over 6,000 projects, providing unparalleled depth in index construction.
The TM Global 100 Index employs weekly rebalancing every Monday at 00:00 UTC, striking the ideal balance between capturing sustained market moves and avoiding overreaction to daily volatility. Each rebalancing cycle follows a transparent, well-defined process: querying current market cap data for all cryptocurrencies, determining the Top 100 rankings using proprietary data feeds, calculating weights based on market capitalization proportions, identifying required trades with full transaction logs, and executing these trades via optimized smart contract batching. The process used to create the index involves rigorous data sourcing and selection criteria, ensuring only the most relevant and compliant assets are included. The issuance of new digital assets is also considered in the index's methodology to maintain regulatory compliance and reflect the evolving market landscape.
What sets Token Metrics apart is its commitment to radical transparency. Users receive notifications 12 hours before rebalancing, detailed transaction logs explaining each portfolio adjustment, and, for every adjustment, detailed transaction data is provided to ensure full traceability. Real-time updates are available through interactive charts and tables, and comprehensive documentation of the index’s methodology is provided. Unlike traditional index providers that only show current holdings, Token Metrics exposes every change and the rationale behind it.
Additionally, Token Metrics enhances basic market cap weighting with intelligent filtering. Each token is assigned a Trader Grade reflecting short-term momentum and technical strength, and an Investor Grade assessing long-term fundamentals and viability. This dual-rating system ensures that constituents of the Top 100 are not just large by market cap but also quality projects with solid fundamentals, reducing exposure to pure speculation. To view premium data and manage subscriptions, users are required to create an account, ensuring secure access to advanced features.
The Game-Changer: Stablecoin Safety Net
The most innovative aspect of the crypto market cap index 2025 is its integration of regime-switching logic with automatic defensive positioning via a stablecoin safety net. The TM Global 100 Index doesn’t merely track the Top 100 tokens—it actively manages risk by knowing when to step aside.
The index continuously analyzes proprietary market signals to classify conditions as either “bullish” or “bearish.” During bullish regimes, the portfolio holds the full Top 100 crypto basket, capturing upside potential across the cryptocurrency market. When signals indicate a bearish environment, the index automatically shifts entirely into stablecoins such as USDC, preserving capital during downturns. Stablecoins are often used as a store of value during market downturns, allowing investors to protect their wealth. Once bullish conditions return, the portfolio redeploys into the Top 100 basket at more attractive prices.
This approach addresses crypto’s hallmark extreme volatility and frequent market corrections exceeding 80%. No matter how promising a cryptocurrency’s technology or network, participating in severe drawdowns erodes both financial and psychological capital, hindering long-term profit and compounding. By moving into stablecoins during downturns, investors maintain liquidity and purchasing power, ready to capitalize on recoveries. The movement into and out of stablecoins involves financial transactions that require secure execution and compliance.
For instance, a hypothetical $100,000 portfolio might grow to $150,000 during a bullish period in early 2025 by participating in a 50% gain across the Top 100. When bearish signals trigger in April, the portfolio shifts to stablecoins, preserving $150,000 in USDC while the broader crypto market declines by 35%. Upon re-entry in June, the portfolio redeploys at lower prices, now controlling approximately $230,000 in crypto assets with the same original capital. During defensive positioning, the assets held may include both digital coins and tokens, which are securely stored on the blockchain or digital ledger.
The explosive growth of the stablecoin market in 2025—surpassing $232 billion in market cap with USDT processing over $1 trillion in monthly transactions—provides deep liquidity and security for these transitions. Major financial institutions like JPMorgan and PayPal have integrated stablecoins into their payment infrastructure, reinforcing their role as legitimate cash equivalents in the digital asset ecosystem. To ensure the security of the index, a majority of network nodes is required to validate transactions and maintain the integrity of the blockchain. It is also essential to verify the legitimacy of transactions and the identity of participants to comply with regulatory standards and prevent fraud.
Why Weekly Rebalancing Hits the Sweet Spot
Rebalancing frequency profoundly affects returns, costs, and risk management in crypto portfolios. Token Metrics’ choice of weekly rebalancing is the result of careful analysis balancing these factors.
Daily rebalancing captures more immediate price action but incurs excessive transaction costs, including blockchain gas fees, bid-ask spreads, and potential tax events, with minimal net performance gains over weekly schedules. Additionally, frequent trading can generate taxable income that must be accurately tracked and reported for regulatory compliance, adding complexity to portfolio management. Monthly rebalancing reduces costs but allows significant allocation drift, potentially missing 20-30% moves in fast-growing tokens. Quarterly rebalancing is too slow for crypto’s rapid narrative shifts and can cause portfolios to lag market changes substantially.
Weekly rebalancing captures meaningful sustained moves without reacting to daily noise that often mean-reverts. It remains efficient through automation and prevents emotional decision-making by enforcing discipline. In 2025’s fast-moving crypto market, where mid-cap tokens can surge 100-300% in weeks, weekly adjustments enable investors to participate in these moves while avoiding the whipsaw of daily changes.
Integrated Execution: From Research to Trade
Token Metrics has further streamlined crypto investing by integrating research and execution into a single platform. Prior to March 2025, investors had to research tokens on one website, then manually execute trades across multiple exchanges, leading to delays, errors, and fatigue. Now, Token Metrics provides an end-to-end solution: AI-powered algorithms process crypto market data 24/7, continuously update market cap rankings, and execute the TM Global 100’s weekly rebalancing automatically. Regime-switching signals trigger defensive stablecoin positioning seamlessly, all within a unified interface.
Users benefit from full transparency on estimated gas costs, platform fees, maximum slippage, and minimum expected portfolio value before confirming any transaction. This eliminates surprises and hidden costs, providing institutional-grade rigor with retail-friendly access.
Security and Safety Measures for Index Investors
In the fast-paced world of the crypto market, security is a top priority for investors looking to protect their crypto assets and investment portfolios. As the cryptocurrency market continues to grow, so do the risks associated with digital assets, making it essential for investors to adopt robust safety measures. Diversification remains a key strategy—by spreading investments across a variety of cryptocurrencies, including bitcoin, ethereum, and promising altcoins, investors can reduce exposure to the volatility of any single asset.
Choosing reputable exchanges and wallets is equally important. Leading platforms implement advanced security protocols such as two-factor authentication, multi-signature wallets, and cold storage solutions to safeguard assets from unauthorized access and cyber threats. Investors should also remain vigilant against phishing attempts and hacking incidents by regularly updating passwords and enabling security alerts. Staying informed about the latest developments in the cryptocurrency market and potential security threats empowers investors to make proactive decisions. By combining diversification, secure storage, and ongoing vigilance, investors can confidently navigate the crypto market and protect their assets against evolving risks.
Regulatory Environment and Compliance in 2025
The regulatory landscape for cryptocurrency is rapidly evolving, and 2025 is shaping up to be a pivotal year for compliance in the market. Regulatory authorities worldwide are intensifying their focus on anti-money laundering (AML) and know-your-customer (KYC) requirements, ensuring that every coin, token, and transaction adheres to strict security and transparency standards. This heightened scrutiny extends to new cryptocurrency offerings, with initial coin offerings (ICOs) and security token offerings (STOs) facing more rigorous oversight to protect investors and maintain market integrity.
For investors, staying compliant means keeping up with the latest regulations, understanding the legal status of their investments, and ensuring that all transactions are properly documented and reported. This includes being aware of the tax implications of trading and holding crypto assets, as well as adhering to local and international laws governing digital assets. By prioritizing regulatory compliance, investors not only safeguard their investments but also contribute to the legitimacy and long-term stability of the cryptocurrency market.
Taxation and Accounting Considerations
Navigating the tax landscape is a crucial aspect of successful crypto investing. In most countries, crypto assets are classified as property or assets rather than traditional currencies, making them subject to capital gains tax when bought, sold, or traded. Investors must keep meticulous records of all cryptocurrency transactions, including dates, prices, trading volumes, and the value of assets at the time of each transaction, to accurately calculate tax liabilities.
Proper accounting ensures that investors remain compliant with local tax authorities and avoid costly penalties or fines. As the cryptocurrency market matures, tax agencies in various countries are increasing their scrutiny of crypto transactions, making transparency and accuracy more important than ever. By understanding the tax implications of their investments and maintaining detailed records, investors can optimize their capital gains, minimize liabilities, and maximize returns from their crypto portfolios.
Education and Research: Empowering Smarter Crypto Investing
In the ever-changing cryptocurrency market, education and research are the foundation of smart investing. Investors who stay informed about the latest market trends, price movements, and technological advancements are better equipped to assess risk and identify high-potential opportunities. Understanding the fundamentals of blockchain technology, the mechanics of digital assets, and the factors influencing cryptocurrency prices—such as supply, demand, and network activity—enables investors to make data-driven decisions.
Access to reliable information is key. Investors can leverage a wide range of resources, including webinars, tutorials, market analysis, and online forums, to deepen their knowledge and stay ahead of market developments. By committing to continuous learning and thorough research, investors can navigate the complexities of the crypto market, manage risk effectively, and build resilient investment strategies for long-term success.
Who Benefits Most from Automatic Top 100 Tracking?
The automatic Top 100 tracking approach with a stablecoin safety net serves a broad spectrum of investors:
- Hands-Off Allocators gain broad crypto market exposure without daily management headaches, thanks to systematic portfolio construction and automatic rebalancing.
- Active Traders use the TM Global 100 as a disciplined core holding, allowing them to place satellite bets on specific narratives while benefiting from the index’s defensive positioning during uncertain periods.
- New to Crypto Investors appreciate the embedded wallet, clear fee structures, and transparent transaction logs, which reduce operational complexity and risk.
- Institutional Investors value the rules-based methodology, comprehensive documentation, and regime-switching risk management that align with professional mandates and compliance requirements.
Community and Networking: Building the Future of Index Investing
The strength of the crypto market lies not only in its technology but also in its vibrant community. Investors who actively engage with the broader cryptocurrency network gain access to a wealth of knowledge, insights, and opportunities. Participating in online forums, attending industry conferences, and joining social media groups dedicated to crypto investment allows investors to connect with peers, share experiences, and stay informed about emerging trends.
Networking within the cryptocurrency community fosters collaboration and innovation, helping investors discover new projects, assess market sentiment, and refine their investment strategies. By building relationships with other investors, developers, and thought leaders, individuals can position themselves at the forefront of the market, ready to capitalize on the next wave of digital asset growth. In the world of index investing, community engagement is a powerful tool for staying informed, inspired, and ahead of the curve.
The Broader Context: Crypto Indices in 2025
Token Metrics is part of a broader industry movement toward intelligent, automated crypto investing. As one recent analysis noted, “One of the top crypto indices in 2025 is the Token Metrics AI Indices. This actively managed index uses AI-driven technology with over 80 data points per token… Token Metrics has pioneered a new generation of crypto indices that actively trade based on AI insights.” Different regions have varying regulations and demand for crypto indices and ETFs, influencing how these products are created and adopted globally.
The market now offers a range of index products—from Bitwise’s Top 10 funds to CoinShares’ quarterly-rebalanced offerings and various AI-powered alternatives. The introduction of cryptocurrency ETFs has contributed to mainstream adoption, allowing investors to gain exposure to digital assets through traditional brokerage accounts. Each ETF is identified by a unique ticker, making it accessible to a broad range of investors on exchanges such as the NYSE. However, critical differentiators separate leaders from followers: rebalancing frequency (weekly vs monthly vs quarterly), universe breadth (Top 10 vs Top 100), quality filtering (market cap only vs fundamental screening), defensive positioning (always invested vs regime switching), and execution transparency (black box vs full documentation).
Token Metrics excels across all these dimensions, delivering the most comprehensive, transparent, and intelligent Top 100 tracking available in 2025.
Conclusion: The Future of Disciplined Crypto Exposure
In 2025, the challenge for crypto investors is not whether to diversify, but how to do so systematically while managing downside risk. Automatic Top 100 tracking combined with a stablecoin safety net addresses both challenges with sophistication. The idea behind the crypto market cap index 2025 is rooted in the principles of transparency, decentralization, and broad market access, reflecting the foundational philosophies that have created a new paradigm in digital asset investing.
By providing broad market exposure through Top 100 market cap weighting, capturing narrative rotations with weekly rebalancing, ensuring quality through AI-enhanced fundamental filtering, and preserving capital during downturns via regime-switching into stablecoins, investors gain a powerful tool impossible to replicate manually.
Token Metrics’s TM Global 100 Index represents years of platform development, bringing institutional-grade infrastructure to retail users. In a market where Bitcoin flirts with new highs and mid-caps rotate through explosive growth phases, systematic exposure to the entire crypto opportunity set—with built-in risk management—is not just convenient; it’s essential.
Ultimately, the best trade in crypto is not always a single transaction. Sometimes, it’s building a system that makes optimal trades automatically. That is the promise of the crypto market cap index 2025: automatic Top 100 tracking with a stablecoin safety net, empowering investors to navigate the digital asset world with confidence and discipline.



.svg)


.png)




%201.svg)
%201.svg)


%201.svg)










.svg)




.png)