Moonshot Tokens in 2025: High-Risk, High-Reward Plays in the Crypto Market

Introduction
The crypto market has always been fertile ground for high-risk, high-reward opportunities. While blue-chip assets like Bitcoin and Ethereum dominate headlines, the real thrill — and sometimes the highest returns — often comes from what the industry calls “moonshots.”
These are small-cap tokens, often under $50 million in market cap, with explosive potential and equally high volatility. In 2025, moonshots remain a core part of speculative trading strategies. But what exactly are they? How do you find them? And most importantly, how can you manage the outsized risks they carry?
Let’s dive into the world of moonshots, drawing insights from recent market trends and real-world data.
What Are Moonshot Tokens?
Moonshot tokens are early-stage, low-cap cryptocurrencies that carry massive upside potential. They often represent experimental ideas or emerging narratives — think AI integration, meme culture, or social tokens — that haven’t yet been fully recognized by the broader market.
Because they trade at relatively low valuations, even small inflows of capital can cause outsized price swings. It’s not uncommon for a moonshot to deliver 10x or even 50x gains within a short time. But the flip side is brutal: these same tokens can plummet to zero just as quickly.
Key characteristics of moonshots:
- Market cap: Typically under $50 million.
- Narrative-driven: Often tied to strong trends like AI, gaming, or DeFi experiments.
- Volatility: Sharp, frequent price swings.
- Liquidity: Thin order books, making large trades difficult without impacting price.
Why Are Moonshots Gaining Traction in 2025?
The current market environment — with crypto market capitalization hovering around $4 trillion — has created room for risk-taking. Investors who missed early gains on Bitcoin or Ethereum are now searching for the next big thing, leading to renewed interest in small-cap tokens.
Emerging narratives also fuel the fire:
- AI-Crypto Fusion: Projects like Sahara AI and Mobi AI are proving that the AI narrative isn’t slowing down.
- Social Tokens & Web3 Platforms: Zora’s creator-focused token model demonstrates how social media and crypto can intersect.
- Community-First DeFi: Protocols like Blackhole DEX show the power of grassroots tokenomics.
These narratives often spill over into the moonshot arena, as smaller projects attempt to replicate the success of these headline-grabbing platforms.
How to Identify Promising Moonshots
Identifying moonshots is part research, part intuition, and part risk tolerance. Here’s what to look for:
1. Strong Narrative Alignment
The most successful moonshots ride on current narratives. In this cycle, AI agents, decentralized social platforms, and community-owned DeFi projects are leading themes. Projects in these categories often experience rapid hype-driven adoption.
2. On-Chain Data
Tools like Dune Analytics and on-chain scanners can reveal whale accumulation, new liquidity pools, or spikes in active addresses — all early indicators of growing interest.
3. Tokenomics
Evaluate supply schedules:
- How many tokens are in circulation?
- Are there large unlocks coming soon?
- Does the project have mechanisms like buybacks or burns to support price stability?
4. Developer & Investor Backing
While many moonshots are grassroots projects, strong teams or backing from reputable funds (e.g., Polychain, Binance Labs) can boost credibility.
Case Studies: Recent Moonshots to Watch
1. Vine (Meme Token):
A meme coin leveraging the Vine brand, this token has gained traction despite limited documentation. Its appeal lies largely in nostalgia and speculative hype.
2. Moby AI: What started as an AI-driven whale-tracking agent has evolved into Mobi Screener, a Dexscreener competitor with integrated social features. The token model ties platform usage to token value — a promising experiment in utility-driven moonshots.
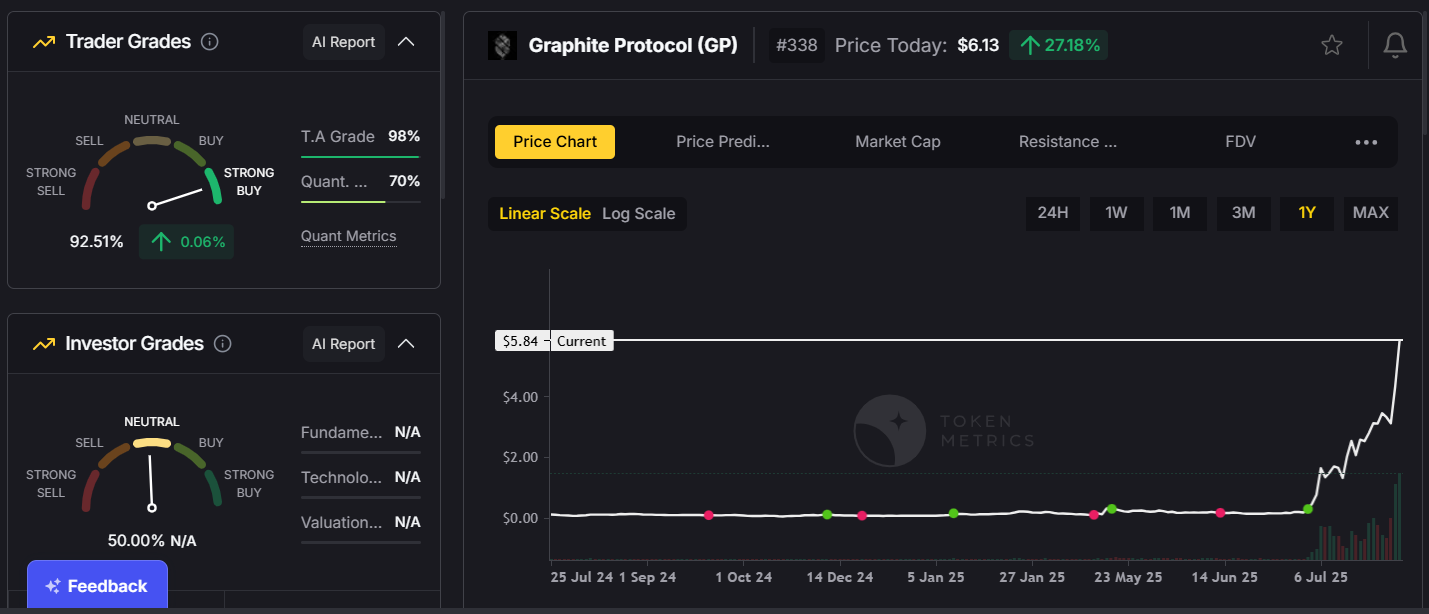
3. Graphite Protocol:
Developers behind Bonk Fun (a leading meme token platform), Graphite has created a buyback and burn model linked to Bonk’s success, aligning token value directly with ecosystem growth.
4. CookieDAO:
Initially positioned as an AI agent platform, CookieDAO is now expanding into proof-of-belief systems, adding new utilities and campaign features for Web3 projects.

The Risk Side: Why Moonshots Can Go to Zero
Moonshots are inherently speculative. Common pitfalls include:
- Team Abandonment or Rug Pulls: Some projects vanish overnight.
- Unsustainable Hype: Many moonshots rely on short-term narratives that fade.
- Low Liquidity: Thin markets make it difficult to enter or exit without significant slippage.
A recent example is SpaceMesh, once hyped as a “next Bitcoin.” Despite strong tech, internal disputes and poor execution led to a near-total collapse — a stark reminder that good code doesn’t always equal good investment.
Managing Risk: A Practical Approach
If you’re trading moonshots, risk management is everything.
1. Position Sizing:
Never allocate more than 1% of your portfolio to any single moonshot. Spreading capital across multiple small positions reduces the impact of one token collapsing.
2. Diversification:
Balance moonshots with higher-cap tokens to stabilize overall portfolio performance.
3. Predefined Exits:
Set clear take-profit and stop-loss levels before entering a trade. Emotional decisions often lead to losses.
4. Time Your Entries:
Consider entering after initial hype cools but before major announcements or roadmap milestones.
The Future of Moonshots: Are They Worth It?
While moonshots can be risky, they remain an integral part of crypto’s DNA. For many traders, they serve as lottery tickets in a market where early discovery can lead to life-changing gains.
In 2025, moonshots are evolving. They’re no longer just meme-driven gambles. Increasingly, they represent experimental innovation — blending DeFi models, AI integrations, and community governance in ways that push the boundaries of blockchain technology.
Conclusion
Moonshots are not for the faint-hearted. They require research, timing, and above all, discipline. In 2025, with themes like AI-driven platforms, decentralized social networks, and community-focused DeFi reshaping the market, the next breakout token could be hiding in plain sight.
Whether you’re a seasoned trader or a curious newcomer, understanding the dynamics of moonshots — and respecting their risks — is essential for navigating this volatile but potentially rewarding segment of crypto.
Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)








.svg)




.png)