
Top Low Cap Altcoins of 2024 - Token Metrics Moon Awards

Welcome to the Token Metrics Moon Awards, a prestigious accolade in the cryptocurrency industry, recognizing platforms and projects that have made substantial contributions to the space.
As a data-driven investment research platform, Token Metrics meticulously conducts these awards to acknowledge the best crypto platforms of the year, utilizing extensive survey data from its robust crypto community.
Today, we will look into a new category of Moon Awards and honor the top Low-cap Altcoins projects of 2024 that have garnered significant support from crypto enthusiasts and investors in our survey.
How We Select These Low-cap Altcoins?
At Token Metrics, we highly value our audience and consider them our most valuable asset. This community-driven approach ensures that the awards reflect real-world opinions and experiences of crypto enthusiasts.
Through the Moon Awards, Token Metrics amplifies the voice of its community, offering a transparent and user-centric evaluation of platforms that are driving the industry forward.
In collaboration with our community members and users' votes, we have curated a comprehensive list of the top Low-cap Altcoins 2024 based on survey input and votes.
In this article, we will explore the best Low-cap Altcoins that have great potential. These projects have been carefully selected based on their technology, potential, and community votes. We'll dive deep into each project, highlighting their unique features and the reasons why they deserve your attention.
Low-cap Altcoins - An Overview
Low-cap Altcoins refers to alternative cryptocurrencies with relatively low market capitalization compared to larger, more established digital currencies like Bitcoin and Ethereum. These coins are often considered high-risk, high-reward investments due to their potential for significant price swings.
While Low-cap Altcoins can offer substantial returns, they also carry greater volatility and liquidity risks. Investors are drawn to these assets for their potential to outperform larger cryptocurrencies, albeit with higher uncertainty.
Researching the technology, team, and use case of Low-cap Altcoins is crucial before considering the investment, as thorough due diligence is essential in this often speculative market.
List of Top Low-cap Altcoins of 2024

1. Astra DAO
In the Moon Awards survey, Astra DAO secured the top position with 21.8% of the total votes.
Astra DAO is a blockchain platform that offers crypto indices and launchpads. With its exclusive partnership with Token Metrics, Astra DAO provides investors with access to AI indices and curated token sales.
As a Token Metrics Ventures portfolio company, Astra DAO has the backing of experienced investors and a strong network.
With a low market cap of $6 million, Astra DAO presents an opportunity for early investors looking to capitalize on the growing demand for crypto indices and curated token sales. The platform's unique features and strategic partnerships make it an attractive investment option.
2. GameSwift
In the Moon Awards survey, GameSwift secured the 2nd position with 12.7% of the total votes.
GameSwift is a Token Metrics Ventures portfolio company that has seen remarkable growth. With a 50x return in just one year, GameSwift is a prime example of the potential of Low-cap Altcoins.
The project aims to revolutionize the gaming industry by leveraging blockchain technology. With its innovative approach, GameSwift has gained traction in the market and offers investors the opportunity to be part of the gaming revolution.
While the gaming industry is highly competitive, GameSwift's early success and strong fundamentals make it a promising investment.
3. Connext
In the Moon Awards survey, Connext secured the 3rd position with 11.6% of the total votes.
Connext is an Altcoin that has garnered considerable attention in the cryptocurrency market. It stands out due to its unique approach to decentralized finance (DeFi) and offers users a seamless and efficient way to transact and interact with digital assets.
By utilizing layer-two scaling solutions, Connext addresses the scalability challenges faced by blockchain networks, resulting in faster and more cost-effective transactions.
Moreover, Connext's architecture enables cross-chain compatibility, allowing for the smooth transfer of assets between different blockchains. With a dedicated team and a forward-thinking roadmap, Connext has the potential to make a significant impact on the decentralized finance landscape.
4. SuiPad
In the Moon Awards survey, SuiPad secured the 4th position with 8% of the total votes.
SuiPad is a launchpad built on the Sui blockchain, offering exposure to the Sui ecosystem. With a market cap of just $2 million, SuiPad is a high-risk, high-reward investment opportunity.
The project allows users to participate in token sales and get involved in the Sui ecosystem's growth. With a strong investor list, including NGC Ventures and Cogitent Ventures, SuiPad has the potential to attract quality projects and provide investors with access to promising token sales.
While this investment carries significant risk, SuiPad offers a unique opportunity to be part of the Sui ecosystem's success.
5. SuiSwap
In the Moon Awards survey, Suiswap secured the 5th position with 5.9% of the total votes.
Suiswap is a decentralized cryptocurrency exchange operating on the SUI blockchain, focusing on providing a secure, efficient, and user-friendly platform for cryptocurrency trading.
It aims to overcome the limitations of traditional centralized exchanges by leveraging blockchain technology for peer-to-peer transactions. The platform's native token, SSWP, holds key functions within the Suiswap ecosystem:
The SSWP token holders have the ability to influence the platform's direction through governance votes on operational and developmental proposals. Additionally, users providing liquidity are rewarded with SSWP tokens, enhancing the trading experience.
Token holders can also stake SSWP for rewards, aiming to promote platform stability. Furthermore, SSWP tokens will be utilized for transaction fees in the SUI blockchain, thereby enriching their value.
Suiswap aims to be a sustainable protocol contributing to the broader SUI blockchain ecosystem, offering a unique decentralized trading experience.
6. Eclipse Fi
In the Moon Awards survey, Eclipse Fi secured the 6th position with 4.9% of the total votes.
Eclipse Fi is a modular launch and liquidity solution designed to transform token launches and support innovation on the Cosmos platform and beyond. This innovative protocol is ushering in a new era for sustainable token launches and community-aligned token distribution.
Despite its relatively low market cap of around $6 million, Eclipse Fi has already demonstrated significant growth potential, positioning itself as a promising but risky investment opportunity within the evolving landscape of token launches and liquidity solutions.
7. Joystream
In the Moon Awards survey, Joystream secured the 7th position with 4.1% of the total votes.
Joystream is a blockchain video platform and DAO (Decentralized Autonomous Organization) that aims to revolutionize content creation and sharing.
With its market cap hovering around $37 million, this low-cap gem has already shown significant growth potential. Joystream allows creators to earn revenue by sharing their videos and offers video NFTs for added value.
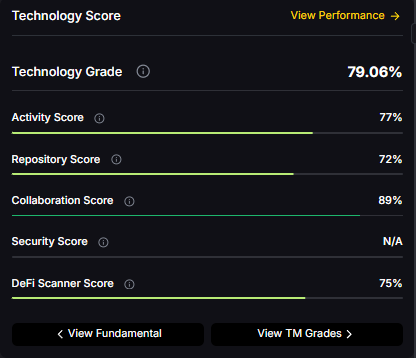
By competing with traditional video platforms like YouTube and Theta, Joystream aims to disrupt the industry with its innovative approach. With a technology score of 75% JoyStream presents an exciting opportunity for investors seeking exposure to the booming video and NFT markets.
8. Velas
In the Moon Awards survey, Velas secured the 8th position with 3.5% of the total votes.
Velas stands out as the leading EVM Blockchain globally, boasting an unparalleled transaction speed of up to 75,000 transactions per second, all processed instantaneously and with the highest level of security at an almost negligible cost.
The Velas Ecosystem comprises decentralized products that leverage its blockchain to deliver a seamless user experience with decentralized, open-source offerings.
Despite its current market cap of approximately $55 million, Velas has shown remarkable growth potential, solidifying its position as a promising investment opportunity in the ever-evolving crypto space.
9. Iron Fish
In the Moon Awards survey, Iron Fish secured the 9th position with 3.1% of the total votes.
Iron Fish is a privacy coin that has gained attention due to its strong backing from top VCs like A16Z and Sequoia Capital. With a market cap of $25 million, this Low-cap Altcoin offers an opportunity for investors looking for privacy-focused projects.
Iron Fish leverages zero-knowledge technology to ensure anonymity and security for transactions. While it may not surpass established privacy coins like Monero, Iron Fish's solid technology score of 85% makes it an intriguing investment option.
10. Script Network
In the Moon Awards survey, Script Network secured the 10th position with 2.8% of the total votes.
Script Network, a 24/7 free-to-air television platform, operates on Script blockchain, offering Script TV and Script Video NFTs. Its diverse content spans film, sports, and documentaries across 30+ channels.
Users can earn rewards on and off-chain by watching TV and participating in the network as a node. It features dual tokens - SCPT for governance and SPAY for transactions.
With a market capitalization of approximately $3 million, Script Network shows promising growth potential, positioning itself as an appealing investment prospect in the dynamic cryptocurrency sector.
11. Nexa
In the Moon Awards survey, Nexa secured the 11th position with 2.6% of the total votes.
Nexa is a scalable layer one blockchain that supports EVM (Ethereum Virtual Machine) contracts. With its market cap under $60 million, Nexa is primed for growth.
It aims to be the next-generation Ethereum, offering a solution for decentralized applications that require scalability and efficiency.
Competing with established projects like Ethereum Classic, Nexa has a solid technology score of 81%, making it an intriguing investment opportunity.
12. Swarm Markets
In the Moon Awards survey, Swarm Markets secured the 12th position with 2.2% of the total votes.
Swarm Markets is a regulated blockchain platform that enables tokenizing and trading real-world assets. With a market cap of $17 million, this Low-cap Altcoin has significant growth potential.
Swarm Markets aims to disrupt traditional financial markets by providing a decentralized asset tokenization and trading solution.
With a technology score of 81% and a strong narrative around real-world assets, Swarm Markets presents an exciting opportunity for investors looking to tap into the growing demand for tokenized assets.
13. Picasso
In the Moon Awards survey, Picasso secured the 13th position with 2% of the total votes.
Picasso and PICA play significant roles in the expanding ecosystem and future of Composable. PICA is the native token for two blockchains - Picasso on Kusama and the Composable Cosmos Chain on Cosmos.
PICA functions as the token that powers cross-ecosystem IBC. For instance, Picasso currently facilitates cross-ecosystem IBC transfer activities between the Polkadot, Kusama, and Cosmos ecosystems. Plans to connect other ecosystems, such as Ethereum and Solana, present a substantial value proposition.
With a current market capitalization of approximately $62 million, Picasso has displayed considerable potential for growth, solidifying its position as an appealing investment opportunity.
14. Across Protocol
In the Moon Awards survey, Across Protocol secured the 14th position with 1.9% of the total votes.
Across Protocol is a cross-chain bridge for L2s, and rollups are secured by UMA's optimistic oracle, ensuring transaction accuracy. It prioritizes capital efficiency with a single liquidity pool and a competitive relayer landscape.
The protocol's interest rate fee model and one liquidity pool design lower user costs and increase liquidity provider yields. By keeping the majority of its LP assets on the secure L1 mainnet, Across operates bots to rebalance assets between destinations.
It leverages a permissionless relayer ecosystem, enabling faster asset bridging and healthy competition. Utilizing UMA's optimistic oracle, Across ensures transaction correctness and employs smart asset management to maintain price balance without relying solely on arbitrageurs.
With a current market capitalization of around $17 million, Across has demonstrated significant potential for growth, consolidating its standing as an attractive investment prospect within the continuously evolving cryptocurrency sector.
15. Nolus
In the Moon Awards survey, Nolus secured the 15th position with 1.6% of the total votes.
Nolus is a DeFi borrowing and lending platform that stands out from the crowd. With a market cap of $7 million, this Low-cap Altcoin can potentially deliver significant returns. Nolus allows users to borrow more than 150% of their collateral, thanks to its unique closed ecosystem built on the Cosmos network.
With Cosmos being one of the most promising ecosystems in the crypto space, Nolus offers exposure to the growing DeFi market within this thriving ecosystem.
With a technology score of 81% and a base case ROI prediction of 50x, Nolus presents an attractive opportunity for investors looking to capitalize on the DeFi lending and borrowing trend.
16. Taraxa
In the Moon Awards survey, Taraxa secured the 16th position with 1.6% of the total votes.
Taraxa is an EVM-compatible smart contract platform that focuses on solving real-world problems. With a market cap of $61 million, this Low-cap Altcoin has huge growth potential.
The project utilizes a block DAG (Directed Acyclic Graph) for Web3, enabling developers to build scalable decentralized applications.
With a solid technology score of 81%, Taraxa offers investors the opportunity to be part of a project that aims to drive blockchain adoption in practical use cases.
Conclusion
In conclusion, the crypto market is filled with opportunities for investors willing to explore beyond the mainstream cryptocurrencies.
These best Low-cap Altcoins with high growth potential offer a chance to multiply your investment and be part of the next big thing in the crypto world.
However, it's important to remember that investing in cryptocurrencies carries risks, and thorough research and due diligence are essential.
Disclaimer
The information provided on this website does not constitute investment advice, financial advice, trading advice, or any other advice, and you should not treat any of the website's content as such.
Token Metrics does not recommend buying, selling, or holding any cryptocurrency. Conduct your due diligence and consult your financial advisor before making investment decisions.

.svg)

Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)





















.svg)




.png)