
Top RWA Tokenization Platforms (2025)

Who this guide is for. Teams and investors evaluating RWA tokenization platforms—issuers and infrastructure bringing Treasuries, funds, real estate, and other off-chain assets on-chain—across access tiers (retail, accredited, QP) and regions.
Top three picks.
- Securitize — institutional rails (transfer agent/broker-dealer) behind flagship tokenized funds.
- Ondo Finance — tokenized Treasuries and cash-equivalents with clear docs and eligibility flows.
- Franklin Templeton (Benji) — on-chain registered money market fund access for U.S. investors.
One caveat. Fees, eligibility (U.S., EU, APAC), and redemption workflows vary widely—always verify your region and investor status on the official product page before transacting. (Securitize)
Introduction
RWA tokenization platforms issue or enable compliant, on-chain representations of real-world assets such as U.S. Treasuries, money market funds, public securities, real estate, and gold. In 2025, the category matters because it brings 24/7 settlement, composability, and transparent audit rails to traditionally siloed markets—while preserving regulatory guardrails like KYC/AML and transfer restrictions. The primary keyword “RWA tokenization platforms” captures commercial-investigational intent: who issues what, on which chains, in which regions, with what fees and controls.
Definition (snippet-ready): An RWA tokenization platform is an issuer or infrastructure provider that brings off-chain assets on-chain under documented legal, custody, and compliance frameworks, with mint/redeem and transfer controls stated in official materials.
How We Picked (Methodology & Scoring)
We scored each platform using official product, docs, pricing, security/licensing, and status pages (and cross-checked volumes with market datasets when needed). We prioritized current availability and clear disclosures.
Scoring weights (sum = 100):
- Liquidity — 30%: scale, mint/redeem pathways, composability.
- Security — 25%: audits, custodians, transfer agent/broker-dealer status, disclosures.
- Coverage — 15%: asset types (T-bills, funds, gold, stocks, real estate), chains.
- Costs — 15%: stated fees and expense ratios; network fees.
- UX — 10%: onboarding, docs, transparency dashboards.
- Support — 5%: regions, KYC help, contact channels.
Freshness: Last updated November 2025.
Best RWA tokenization platforms in November 2025 (Comparison Table)
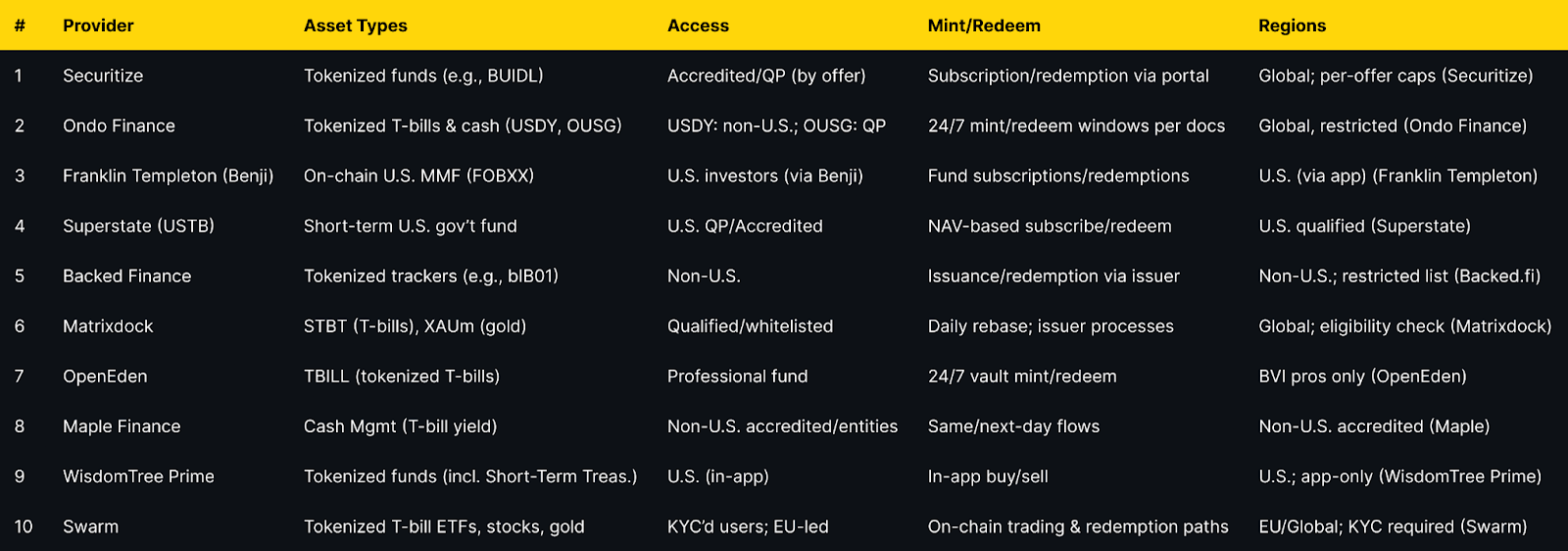
Top 10 RWA tokenization platforms in November 2025
1. Securitize — Best for institutional-grade tokenized funds
Why Use It. Securitize provides regulated rails (transfer agent/broker-dealer) behind marquee tokenized funds like BlackRock’s BUIDL, with investor onboarding, cap-table/TA services, and compliant transfer controls for secondary liquidity where permitted. (Securitize)
Best For. Asset managers, QP/Accredited investors, enterprises wanting full-stack issuance and servicing.
Notable Features. Transfer agent role; broker-dealer marketplace; issuer/investor portals; compliance & reporting. (digitize.securitize.io)
Consider If. You need institutional governance and regulated distribution rather than retail-first access.
Fees Notes. Fund expense ratios and issuer/platform fees vary by offering.
Regions. Global, with per-offering eligibility and disclosures.
Alternatives. WisdomTree Prime; Ondo Finance.
2. Ondo Finance — Best for diversified tokenized Treasuries & cash-equivalents
Why Use It. OUSG gives QPs exposure to short-term Treasuries/money market funds; USDY offers a tokenized note with cash-equivalent backing, with clear eligibility and 24/7 mint/redeem mechanics documented. (Ondo Finance)
Best For. DAOs and treasuries, QPs, non-U.S. entities seeking on-chain cash management.
Notable Features. USDY/ONS products; rTokens (rebasing); detailed fees/tax sections; multi-chain support. (docs.ondo.finance)
Consider If. U.S. persons generally restricted for USDY; confirm status before onboarding. (Ondo Finance)
Fees Notes. Management/operational fees per product docs; plus network fees. (docs.ondo.finance)
Regions. Global with restrictions (e.g., no USDY for U.S. persons). (Ondo Finance)
Alternatives. Superstate; OpenEden.
3. Franklin Templeton — Benji — Best for U.S. on-chain money market access
Why Use It. The Franklin OnChain U.S. Government Money Fund (FOBXX) is a registered fund whose shares are represented on-chain (BENJI), allowing U.S. investors to access a money market fund with blockchain-based recordkeeping. (digitalassets.franklintempleton.com)
Best For. U.S. treasurers and advisors needing a regulated on-chain cash vehicle.
Notable Features. US-registered fund; Stellar/Polygon rails; Benji contracts/app. (digitalassets.franklintempleton.com)
Consider If. Access is via Franklin’s app; availability and eligibility are U.S.-focused. (digitalassets.franklintempleton.com)
Fees Notes. Standard money market fund expense ratio; see fund page. (franklintempleton.com)
Regions. U.S. investors (see Benji). (digitalassets.franklintempleton.com)
Alternatives. WisdomTree Prime; Securitize-hosted offerings.
4. Superstate (USTB) — Best for U.S. Qualified Purchasers
Why Use It. USTB offers U.S. Qualified Purchasers access to short-duration U.S. government securities through a tokenized fund on Ethereum, with institutional processes and NAV-based subscriptions/redemptions. (superstate.com)
Best For. U.S. QPs, fund treasurers, trading firms.
Notable Features. Ethereum issuance; QP onboarding; short-duration Treasury focus. (superstate.com)
Consider If. Available to QPs; verify accreditation and subscription steps. (superstate.com)
Fees Notes. Fund expenses apply; see official page. (superstate.com)
Regions. U.S. (Qualified Purchasers). (superstate.com)
Alternatives. Ondo OUSG; WisdomTree Prime funds.
5. Backed Finance — Best for tokenized trackers of public securities
Why Use It. Backed issues ERC-20 trackers like bIB01 (iShares $ Treasury 0-1yr UCITS ETF) with explicit regional restrictions and product pages that state legal structure and disclosures. (backed.fi)
Best For. Non-U.S. entities seeking tokenized ETF-style exposure with issuer support.
Notable Features. Tokenized trackers and AMCs; legal docs; chain integrations. (backed.fi)
Consider If. Not available to U.S. persons; restricted countries listed. (assets.backed.fi)
Fees Notes. Issuer/admin fees per product; plus network fees. (backed.fi)
Regions. Non-U.S.; sanctions list enforced. (assets.backed.fi)
Alternatives. Swarm; Matrixdock STBT.
6. Matrixdock — Best for T-bills and gold under one issuer
Why Use It. STBT provides short-term U.S. Treasury exposure with a 1:1 USD peg and daily rebasing, while XAUm tokenizes LBMA-grade physical gold—both under a clear issuer framework. (matrixdock.com)
Best For. Treasury management with optional gold allocation on the same rails.
Notable Features. STBT daily rebase; peg policy; gold custodial disclosures. (matrixdock.com)
Consider If. Whitelisting/eligibility apply; confirm region and KYC. (matrixdock.com)
Fees Notes. Issuer fees per product pages; network fees. (matrixdock.com)
Regions. Global with eligibility controls. (matrixdock.com)
Alternatives. OpenEden; Ondo OUSG.
7. OpenEden — Best for professional-grade tokenized T-bills
Why Use It. TBILL is structured as a regulated Professional Fund (BVI) with a 24/7 smart-contract vault for mint/redeem and a transparency dashboard, targeting professional investors. (openeden.com)
Best For. Professional/offshore funds and DAOs requiring programmatic access.
Notable Features. BVI Professional Fund status; real-time transparency; vault UI. (openeden.com)
Consider If. Professional-investor eligibility required; check docs before onboarding. (openeden.com)
Fees Notes. Fund and platform fees; plus network fees. (openeden.com)
Regions. BVI-regulated; cross-border access subject to status. (openeden.com)
Alternatives. Matrixdock; Ondo.
8. Maple Finance — Cash Management — Best for non-U.S. accredited entities seeking T-bill yield
Why Use It. Maple’s Cash Management provides non-U.S. accredited participants on-chain access to T-bill and repo yields, with updates enabling immediate servicing when liquidity is available and next-day withdrawals operationally. (maple.finance)
Best For. Non-U.S. corporates, DAOs, and funds optimizing idle stablecoin cash.
Notable Features. Fast onboarding; immediate interest accrual; no lock-up; institutional borrower SPV. (maple.finance)
Consider If. U.S. investors are excluded; confirm accreditation and entity status. (maple.finance)
Fees Notes. Management/operational fees netted from yield; network fees. (maple.finance)
Regions. Non-U.S. accredited/entities. (maple.finance)
Alternatives. OpenEden; Ondo.
9. WisdomTree Prime (Digital Funds) — Best for app-native tokenized fund access in the U.S.
Why Use It. The Prime app offers tokenized digital funds—including Short-Term Treasury—purchased and held in-app, bringing tokenized funds to retail U.S. users under an SEC-registered umbrella. (WisdomTree Prime)
Best For. U.S. retail/in-app users seeking tokenized fixed income and equity funds.
Notable Features. In-app buy/sell; multiple Treasury maturities; composability paths emerging. (WisdomTree Prime)
Consider If. App-only access; availability subject to U.S. coverage and disclosures. (WisdomTree Prime)
Fees Notes. Fund expense ratios; standard network fees for on-chain interactions. (wisdomtree.com)
Regions. U.S. (Prime app). (WisdomTree Prime)
Alternatives. Franklin Benji; Securitize.
10. Swarm — Best for compliant on-chain trading of tokenized T-bill ETFs and equities
Why Use It. Swarm enables compliant, on-chain access to tokenized U.S. Treasury ETFs, public stocks, and gold, with KYC’d access and DeFi-compatible rails documented in its platform materials and docs. (swarm.com)
Best For. EU-led users, crypto funds, and builders needing tokenized public market exposure.
Notable Features. dOTC protocol; product pages for T-bill ETFs; documented KYC/flows. (swarm.com)
Consider If. Regional and KYC requirements apply; yields are variable per underlying ETF. (swarm.com)
Fees Notes. Platform/product fees; network fees. (swarm.com)
Regions. EU/Global with KYC. (swarm.com)
Alternatives. Backed Finance; Ondo.
Decision Guide: Best By Use Case
- Regulated U.S. access (retail): Franklin Benji, WisdomTree Prime. (digitalassets.franklintempleton.com)
- U.S. Qualified Purchasers: Superstate USTB, Ondo OUSG. (superstate.com)
- Non-U.S. accredited entities: Maple Cash Management, Backed Finance. (maple.finance)
- Always-on T-bill vault with pro fund wrapper: OpenEden TBILL. (openeden.com)
- Treasuries + gold under one roof: Matrixdock (STBT, XAUm). (matrixdock.com)
- Tokenized public stocks & bond ETFs in DeFi: Swarm, Backed Finance. (swarm.com)
- Issuer/infrastructure for enterprises: Securitize (transfer agent + BD). (digitize.securitize.io)
How to Choose the Right RWA Tokenization Platform (Checklist)
- Region eligibility (U.S./EU/APAC and investor status: retail, accredited, QP) is clearly stated.
- Asset coverage matches mandate (T-bills, money market funds, ETFs, gold, real estate).
- Mint/redeem mechanics and settlement windows are documented.
- Fees: expense ratios, issuer fees, spreads, on-chain network costs are explicit.
- Security posture: custodians, audits, transfer agent/broker-dealer status, disclosures.
- Transparency: NAV, holdings, attestation or daily rebasing and dashboards.
- Chain support: EVM/L2s/other; composability needs.
- Support & docs: onboarding, KYC, status pages.
Red flags: vague eligibility, missing fee tables, no custody/disclosure detail.
Use Token Metrics With Any Category
- AI Ratings to screen assets tied to each platform’s tokens.
- Narrative Detection to spot early RWA flows across chains.
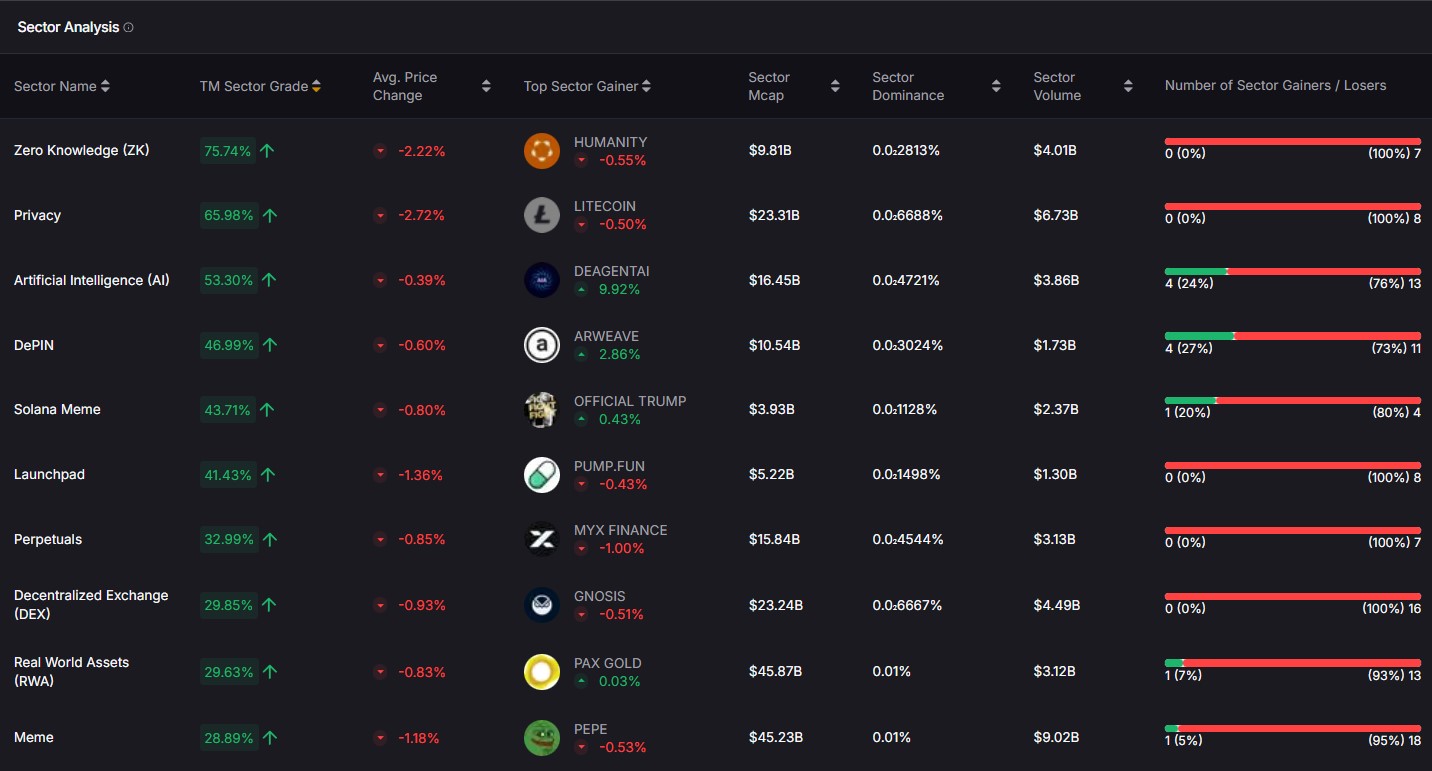
- Portfolio Optimization to size cash-equivalents vs. risk assets.
- Alerts & Signals to time rotations into yield-bearing RWAs.
CTA — Indices Focus: Prefer diversified exposure? Explore Token Metrics Indices.
Security & Compliance Tips
- Transact only via official portals/URLs and verified contracts listed in docs. (digitalassets.franklintempleton.com)
- Confirm eligibility (U.S./non-U.S., accredited/QP) and sanctioned-country restrictions before minting. (assets.backed.fi)
- Review custody and role separation (issuer, TA, broker-dealer) and audit reports where available. (digitize.securitize.io)
- Understand redemption windows, rebase mechanics, and NAV policies. (matrixdock.com)
- Track fund expenses and on-chain network fees; they impact net yield. (franklintempleton.com)
- Bookmark status/docs pages for incident updates and parameter changes.
This article is for research/education, not financial advice.
Beginner Mistakes to Avoid
- Treating all RWA tokens as “stablecoins”—yields, risks, and redemption rights differ.
- Ignoring eligibility rules, then getting stuck at redemption.
- Skipping issuer docs and relying only on dashboards.
- Assuming 1:1 liquidity at all times without reading fund/issuer terms.
- Mixing retail wallets with institutional KYC accounts without a plan.
- Overlooking chain/bridge risks when moving RWA tokens across L2s.
How We Picked (Methodology & Scoring)
We built an initial universe (~20 issuers/infrastructure) and selected 10 based on the SCORING_WEIGHTS above. We verified asset coverage, eligibility, fees, redemption, and regions on official pages only (listed below). Third-party datasets were used for cross-checks but are not linked.
FAQs
What are RWA tokenization platforms?
Issuers or infrastructure that bring real-world assets (like Treasuries, funds, gold, or equities) on-chain under a legal/compliance framework, with stated mint/redeem processes and transfer rules. See each official page for specifics. (Securitize)
Are they safe for retail?
Some are U.S. retail-friendly (e.g., Franklin Benji, WisdomTree Prime), while others are restricted to accredited investors, QPs, or non-U.S. persons. Always check the eligibility page before onboarding. (digitalassets.franklintempleton.com)
What fees should I expect?
Expect fund expense ratios or issuer/admin fees plus on-chain network fees. Some products rebase yield; others adjust NAV. Review each product’s fees section. (docs.ondo.finance)
Where are these tokens available?
Most run on Ethereum or compatible L2s, with some on Stellar/Polygon via app rails. Regions vary (U.S., EU, offshore professional). (digitalassets.franklintempleton.com)
Can I redeem 24/7?
Many have 24/7 mint/redeem requests; actual settlement follows fund terms, banking hours, and liquidity windows. Check each product’s redemption section. (app.openeden.com)
Conclusion + Related Reads
If you want institutional rails and broad issuer support, start with Securitize. For T-bill exposure with clear docs, consider Ondo or Superstate (QP). U.S. retail can explore Franklin Benji or WisdomTree Prime. Diversifiers can add Matrixdock (Treasuries + gold) or OpenEden (pro fund vault). Builders needing tokenized equities/ETFs should evaluate Swarm and Backed.
Related Reads (Token Metrics):

.svg)

Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)







.svg)




.png)