
Types of Stablecoins: A Complete Guide for 2025

The cryptocurrency market is famous for volatility—Bitcoin can swing by thousands of dollars in a day, and altcoins can rise or crash in hours. But what if you need price stability? That’s where stablecoins come in.
Stablecoins are digital currencies pegged to stable assets like the US dollar, gold, or even algorithmically maintained price levels. They bridge the gap between the speed and efficiency of blockchain technology and the reliability of traditional money.
As of 2025, stablecoins account for over $140 billion in circulating supply, making them essential for traders, investors, and decentralized finance (DeFi) users. But not all stablecoins are the same—different types use different mechanisms to maintain their stability, each with unique pros and cons.
In this guide, we’ll break down the types of stablecoins, how they work, their risks, and which might be best for your needs.
What Are Stablecoins?
A stablecoin is a cryptocurrency designed to maintain a stable value by pegging its price to a reference asset. Most stablecoins are pegged to fiat currencies like the U.S. dollar (e.g., 1 USDT ≈ $1), but some track commodities (like gold) or are algorithmically balanced to hold value.
They are widely used for:
- Trading: Moving quickly in and out of volatile assets.
- DeFi: Providing liquidity, borrowing, and earning yields.
- Remittances: Sending low-cost, fast cross-border payments.
- Hedging: Protecting against crypto market volatility.
Types of Stablecoins
There are four main types of stablecoins:
- Fiat‑Collateralized Stablecoins
- Crypto‑Collateralized Stablecoins
- Algorithmic (Non‑Collateralized) Stablecoins
- Commodity‑Backed Stablecoins
Each has a different method of maintaining its peg. Let’s break them down.
1. Fiat‑Collateralized Stablecoins
Definition:
These are backed 1:1 by traditional currencies like the U.S. dollar, euro, or yen. For every stablecoin issued, an equivalent amount of fiat is held in reserve by a trusted custodian.
How They Work:
If you buy 1 USDC, Circle (its issuer) holds $1 in a regulated bank account or short-term U.S. Treasury securities. When you redeem that stablecoin, the issuer sends you the equivalent amount in fiat and burns the coin.
Examples:
- Tether (USDT) – Largest stablecoin by market cap; widely used on exchanges.
- USD Coin (USDC) – Issued by Circle, fully regulated and audited.
- TrueUSD (TUSD) – Offers real-time attestation of reserves.
- PayPal USD (PYUSD) – Launched by PayPal for payments and DeFi.
Pros:
- High stability – Pegged directly to fiat.
- Transparent – Many provide audits and attestations.
- Easy adoption – Ideal for traders, merchants, and payment platforms.
Cons:
- Centralization – Custodians control reserves and can freeze accounts.
- Regulatory risks – Subject to government oversight.
- Less transparency for some issuers – (e.g., Tether faced scrutiny over its reserves).
2. Crypto‑Collateralized Stablecoins
Definition:
These are backed by cryptocurrencies like Ethereum or Bitcoin instead of fiat. Because crypto is volatile, these stablecoins are overcollateralized (e.g., $150 in ETH backs $100 in stablecoins).
How They Work:
When you mint a crypto-backed stablecoin like DAI, you deposit collateral (e.g., ETH) into a smart contract. If the collateral value drops too much, the contract automatically liquidates some assets to maintain the peg.
Examples:
- DAI – Issued by MakerDAO, backed by ETH, USDC, and other assets.
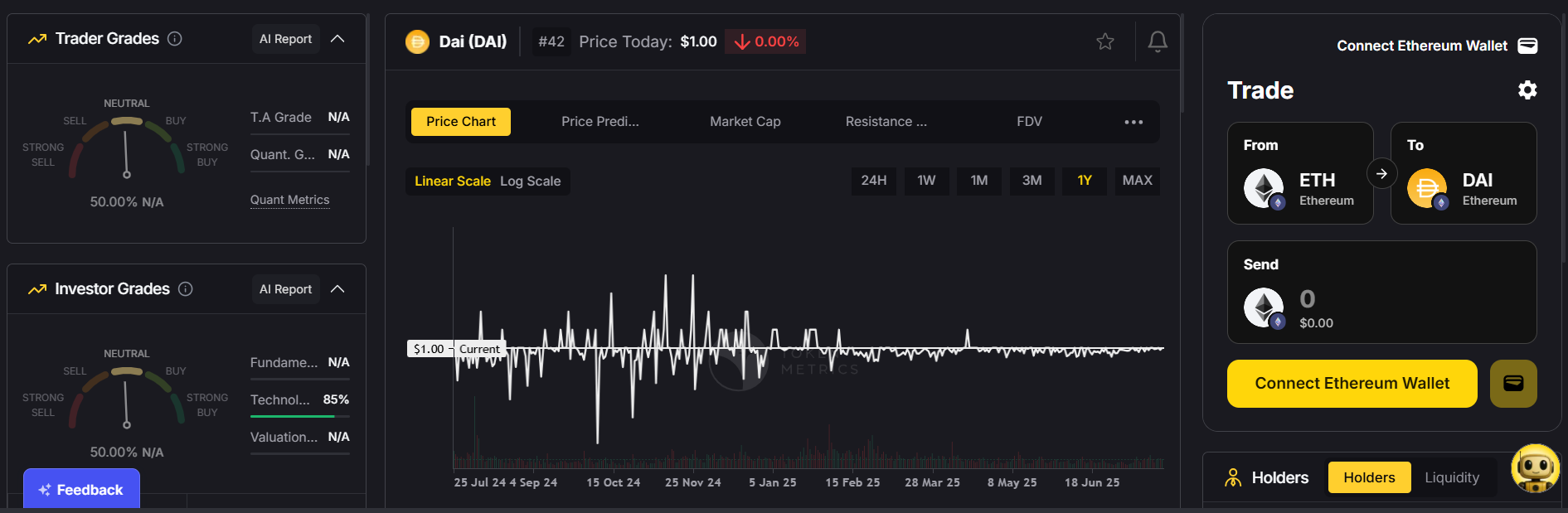
- sUSD – A synthetic USD issued by Synthetix.
- MIM (Magic Internet Money) – Collateralized by multiple crypto assets.
Pros:
- Decentralized – No single company controls reserves.
- Transparent – All collateral balances are viewable on-chain.
- Resistant to censorship – Issuers can’t freeze accounts.
Cons:
- Volatility risk – Collateral can lose value quickly, requiring liquidations.
- Overcollateralization – Ties up more capital than fiat-backed options.
- Complexity – Requires understanding of DeFi mechanics.
3. Algorithmic (Non‑Collateralized) Stablecoins
Definition:
These don’t use physical reserves. Instead, they maintain their peg via algorithmic supply adjustments—minting or burning tokens to balance price around $1.
How They Work:
If demand increases and the price rises above $1, the protocol mints more coins. If it falls below $1, the protocol burns coins or incentivizes users to buy them back.
Examples:
- Ampleforth (AMPL) – Elastic supply adjusts daily.
- UST (TerraUSD) – Infamously collapsed in 2022 after its peg broke.
- Frax (FRAX) – Uses a hybrid model: partly collateralized, partly algorithmic.
Pros:
- Highly capital-efficient – Doesn’t require large reserves.
- Decentralized – Often governed by smart contracts and DAOs.
Cons:
- Peg instability – Prone to “death spirals” when market confidence drops.
- Complex mechanisms – Harder for average users to understand.
- History of failures – UST/LUNA crash eroded trust in algorithmic coins.
4. Commodity‑Backed Stablecoins
Definition:
These stablecoins are pegged to commodities like gold, silver, or oil, giving them intrinsic value beyond fiat.
How They Work:
For every coin issued, an equivalent amount of the commodity is held in a secure vault. For example, owning 1 PAX Gold (PAXG) means you own 1 troy ounce of physical gold stored by the issuer.
Examples:
- PAX Gold (PAXG) – Backed by physical gold.
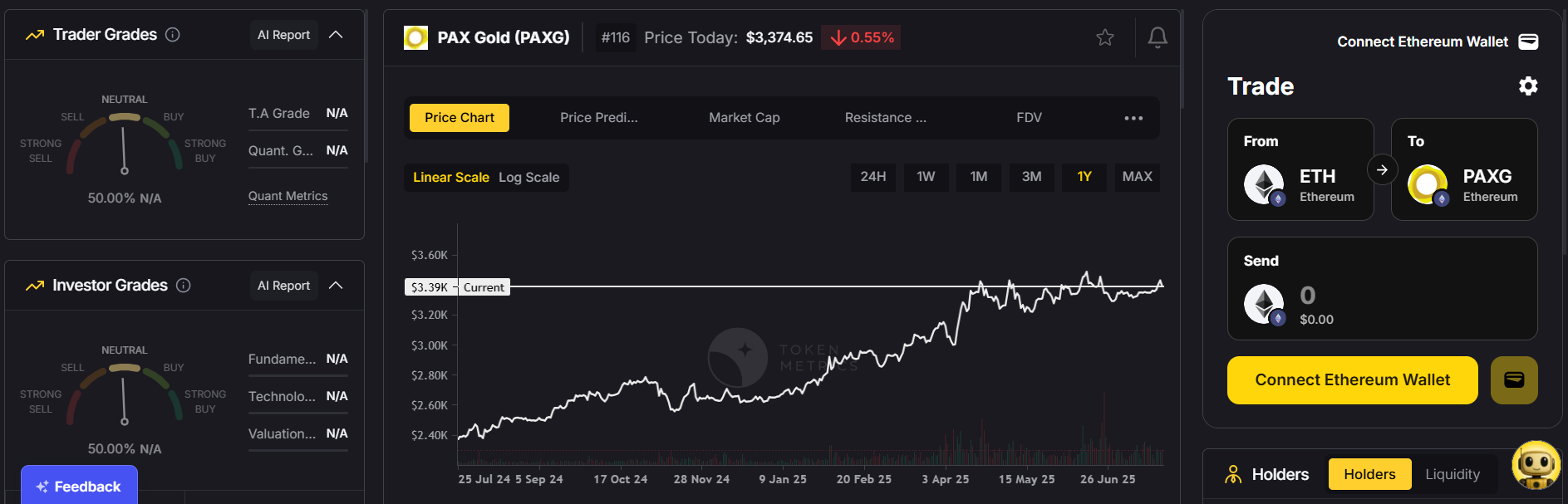
- Tether Gold (XAUT) – Gold-backed token from Tether.
- Digix Gold (DGX) – Pegged to gold bars in Singapore vaults.
Pros:
- Hedge against inflation – Commodities like gold retain value during economic uncertainty.
- Diversification – Offers exposure to both crypto and commodities.
Cons:
- Low liquidity – Less widely used than fiat-backed stablecoins.
- Storage & audit challenges – Requires trust in the issuer to maintain reserves.
Why Do Stablecoins Matter?
Stablecoins are the backbone of DeFi and crypto trading.
- Trading & arbitrage: They provide a quick way to exit volatile positions without converting back to fiat.
- Cross-border payments: Cheaper and faster than SWIFT or remittance services.
- DeFi participation: Essential for lending, borrowing, yield farming, and liquidity pools.
- On-ramp/off-ramp: They simplify converting between traditional finance and blockchain.
Which Type of Stablecoin Should You Use?
If you want simplicity & security: Go with fiat-backed coins like USDC or PYUSD.
If you value decentralization: Choose crypto-collateralized options like DAI.
If you’re comfortable with high risk: Explore algorithmic models like FRAX (but beware of peg risks).
If you want inflation protection: Consider commodity-backed coins like PAXG.
Key Risks of Stablecoins
- Regulation: Governments are increasing oversight of fiat-backed coins.
- Centralization: Some issuers can freeze funds or blacklist wallets.
- Smart contract risks: DeFi-based stablecoins can suffer from bugs or exploits.
- Peg breaks: Algorithmic models are especially vulnerable to confidence loss.
The Future of Stablecoins
In 2025, stablecoins are evolving to meet regulatory and market demands:
- Central Bank Digital Currencies (CBDCs): Governments are issuing digital dollars and euros, potentially competing with stablecoins.
- Regulated issuers: Projects like USDC are working closely with regulators to ensure compliance.
- Hybrid models: Combining fiat and algorithmic elements (e.g., Frax) to enhance stability.
As DeFi expands and global adoption grows, stablecoins will remain at the heart of crypto finance.
Final Thoughts
Stablecoins are more than just “digital dollars.” They’re a critical bridge between traditional finance and blockchain innovation.
- Fiat-backed stablecoins bring stability and ease of use.
- Crypto-collateralized ones offer transparency and decentralization.
- Algorithmic models push innovation but carry higher risks.
- Commodity-backed coins provide a hedge against inflation and diversify exposure.
Choosing the right type depends on your risk tolerance, use case, and trust level. Whether for trading, saving, or participating in DeFi, understanding the types of stablecoins can help you navigate the crypto ecosystem with confidence.

.svg)

Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)








.svg)




.png)