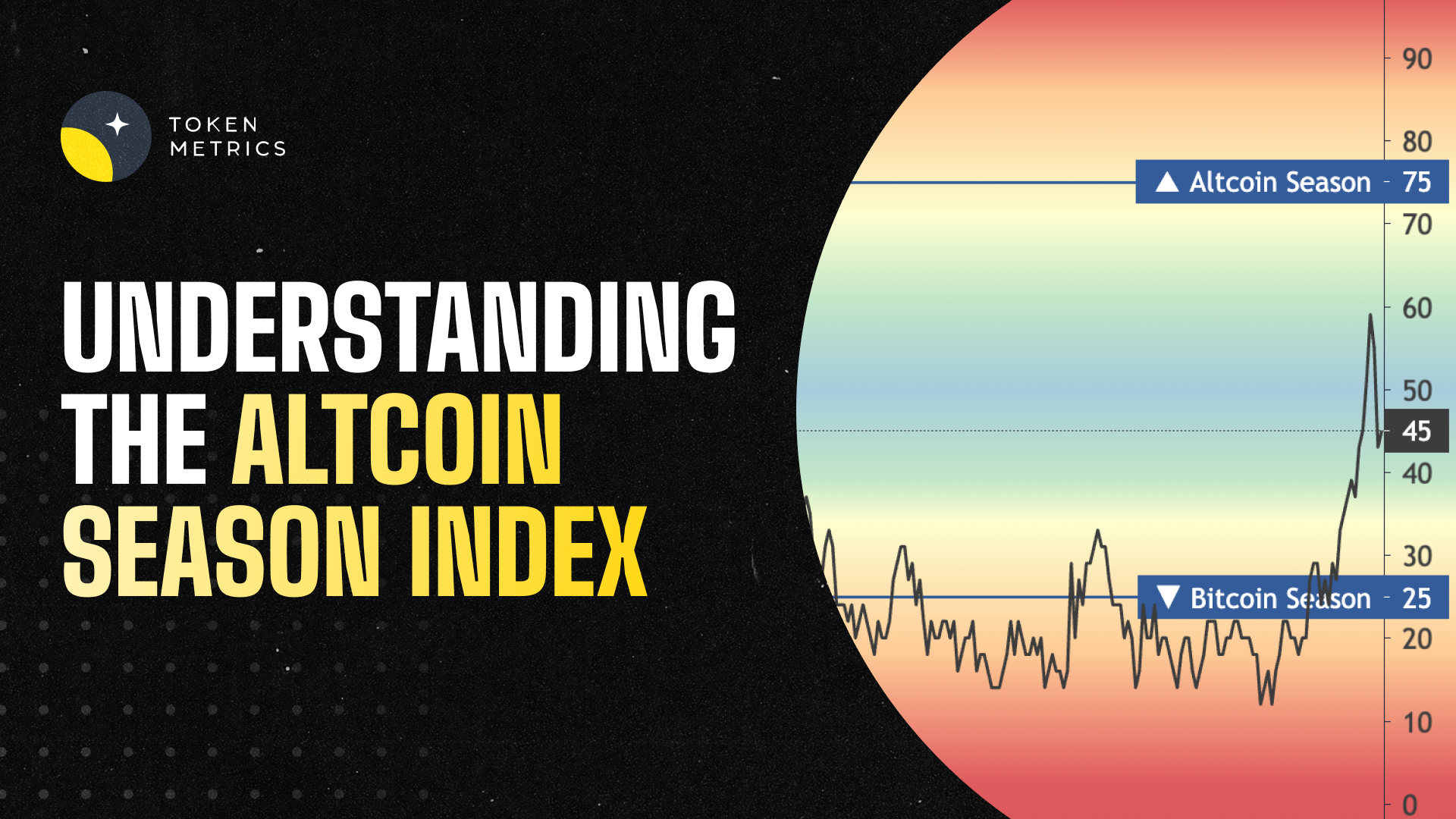
Understanding the Altcoin Season Index: Your Complete Guide to Altcoin Market Dominance
The cryptocurrency market operates in distinct cycles, with periods where Bitcoin dominates and others where alternative cryptocurrencies (altcoins) take center stage. Understanding when these shifts occur is crucial for successful crypto trading and investment. The Altcoin Season Index has emerged as the definitive metric for identifying these market transitions, providing traders and investors with essential insights into optimal timing for altcoin investments.
What is the Altcoin Season Index?
The Altcoin Season Index is a sophisticated metric that measures the relative performance of altcoins compared to Bitcoin over specific time periods. This indicator serves as a market sentiment gauge, helping traders identify when alternative cryptocurrencies are outperforming Bitcoin and whether the market has entered what's known as "Altcoin Season."
The index uses the top 100 coins ranked on CMC (excluding stablecoins and wrapped tokens) and compares them based on their rolling 90-day price performances. If 75% of the top 100 coins outperform Bitcoin in the last 90 days, it's Altcoin Season. Conversely, if only 25% or fewer altcoins outperform Bitcoin, the market is considered to be in "Bitcoin Season."
The methodology behind this index is straightforward yet effective. By analyzing the performance of the top-ranked cryptocurrencies against Bitcoin's price movements, the index creates a percentage score ranging from 0 to 100. A score above 75 indicates strong altcoin dominance, while a score below 25 suggests Bitcoin is leading the market.
How the Altcoin Season Index Works?
The calculation process involves several key components that ensure accuracy and relevance. Stablecoins like Tether and DAI, as well as asset-backed tokens (e.g., WBTC, stETH, cLINK), are excluded. This exclusion ensures that the index focuses on genuine price appreciation rather than pegged assets or derivatives.
Different platforms may use slightly varying methodologies. If 75% of the Top 50 coins performed better than Bitcoin over the last season (90 days) it is Altcoin Season. Some platforms focus on the top 50 cryptocurrencies, while others extend to the top 100, but the core principle remains consistent across all implementations.
The 90-day rolling window provides sufficient data to identify meaningful trends while remaining responsive to recent market movements. This timeframe helps filter out short-term volatility and focuses on sustained performance patterns that indicate genuine market shifts.
Current Market Status and Recent Trends
As of mid-2025, the cryptocurrency market is experiencing significant dynamics that reflect the utility of the Altcoin Season Index. The cryptocurrency market shows strong bullish momentum halfway through 2025, with Bitcoin reaching record highs near $122,946.00. This unprecedented Bitcoin performance has created interesting market conditions for altcoin investors.
Recent data shows varying altcoin performance across different categories. As of July 21, 2025, Stellar (XLM) is leading the pack, surging 74% for the week to trade at $0.527. Cardano (ADA) is up 23% at $1.004, and Ripple (XRP) has gained 21% this week to reach $3.92. These gains demonstrate that certain altcoins can achieve significant outperformance even during periods of strong Bitcoin dominance.
The market appears to be in a transitional phase. BTC dominance: ~60–61.5%—declining but not yet low enough. There is a strong interest in major alternative cryptocurrencies (alts) and large-cap coins. Into early/mid-phase alt season, not for quick whale-level meme pumps yet. This suggests that while we're not in full altcoin season, the conditions are developing for increased altcoin outperformance.
Historical Context and Market Cycles
Understanding historical altcoin seasons provides valuable context for current market conditions. The most notable altcoin season occurred in 2021, when the convergence of multiple factors created optimal conditions for alternative cryptocurrency growth. During this period, BTC's market dominance dropped from 70% to 38%, while the total market capitalization doubled from 30% to 62%. The altcoin season index hit 98 on April 16, 2021.
This historical precedent demonstrates the potential magnitude of altcoin seasons. When market conditions align, the shift from Bitcoin dominance to altcoin outperformance can be dramatic and sustained. The 2021 altcoin season was fueled by institutional adoption, decentralized finance (DeFi) growth, and the NFT boom, creating a perfect storm for alternative cryptocurrency appreciation.
Recent market activity has shown signs of renewed altcoin interest. The Altcoin Season Index, a widely tracked metric on CoinMarketCap (CMC), surged seven points to reach 84 on December 3, 2024. While this was a temporary spike, it demonstrated that altcoin seasons can emerge quickly when market conditions shift.
The Role of AI and Advanced Analytics in Altcoin Trading
Modern altcoin trading has been revolutionized by artificial intelligence and advanced analytics platforms. Token Metrics stands at the forefront of this technological evolution, providing traders with unprecedented insights into altcoin markets. Trade and invest crypto with Token Metrics—your AI-powered platform for crypto trading, research, and data analytics.
The platform's sophisticated approach to market analysis sets it apart from traditional trading tools. Token Metrics scans 6,000+ tokens daily and gives each one a score based on technical analysis, on-chain data, fundamental metrics, sentiment and social data, and exchange data. This comprehensive analysis ensures that traders have access to multi-dimensional insights that go far beyond simple price movements.
Token Metrics' AI-driven methodology provides particular value during altcoin seasons. Token Metrics has developed an AI-powered rating system that scans the market 24/7, analyzing over 80 data points per token. Their Moonshots tab is designed specifically for users looking to spot early-stage altcoins before they break out. This capability is crucial for capitalizing on altcoin season opportunities, as the window for maximum gains often occurs in the early stages of market shifts.
Strategic Applications for Traders and Investors
The Altcoin Season Index serves multiple strategic purposes for different types of market participants. For swing traders, the index provides timing signals for portfolio rebalancing. When the index begins climbing toward 75, it may signal an opportune time to increase altcoin exposure while reducing Bitcoin allocation.
Long-term investors can use the index to identify accumulation opportunities. During Bitcoin seasons (index below 25), quality altcoins often trade at relative discounts, presenting attractive entry points for patient investors. This contrarian approach can be particularly effective when combined with fundamental analysis of individual projects.
Day traders benefit from understanding index trends to gauge market sentiment and momentum. Token Metrics' AI-driven platform exemplifies this shift, enabling traders to analyze market sentiment and identify patterns that human traders might overlook. Real-time sentiment analysis becomes crucial during transitional periods when the index hovers around the 50 mark.
Portfolio managers can use the index as a risk management tool. Sharp increases in the index during established bull markets may signal overheated conditions, suggesting the need for profit-taking or risk reduction. Conversely, low index readings during bear markets might indicate oversold conditions and potential accumulation opportunities.
Risk Management and Market Considerations
While the Altcoin Season Index provides valuable insights, it should not be used in isolation. Market conditions can change rapidly, and the 90-day rolling window means the index may lag sudden market shifts. Traders should combine index signals with other technical and fundamental analysis tools for comprehensive market assessment.
Regulatory developments, macroeconomic factors, and technological breakthroughs can all influence altcoin performance independently of historical patterns. The index should be viewed as one component of a broader analytical framework rather than a definitive trading signal.
Market manipulation and coordinated activities can temporarily skew individual altcoin performance, potentially affecting index calculations. This risk is mitigated by focusing on the top-ranked cryptocurrencies, but traders should remain aware of potential anomalies in index readings.
The Future of Altcoin Season Analysis
The evolution of altcoin markets continues to accelerate, driven by technological innovation and institutional adoption. AI-powered platforms like Token Metrics are becoming essential tools for navigating this complexity. Token Metrics, an AI-powered platform, consolidates research, portfolio management, and trading signals into a unified ecosystem.
As the cryptocurrency market matures, the dynamics underlying altcoin seasons may evolve. Increased institutional participation, regulatory clarity, and technological developments in blockchain infrastructure could create new patterns in altcoin performance cycles. The Altcoin Season Index will likely adapt to incorporate these changing market dynamics.
The integration of artificial intelligence and machine learning into market analysis represents the next frontier in cryptocurrency trading. These technologies can process vast amounts of data in real-time, identifying subtle patterns and correlations that human analysts might miss. This capability becomes particularly valuable during volatile market conditions when rapid decision-making is crucial.
Conclusion
The Altcoin Season Index has established itself as an indispensable tool for cryptocurrency traders and investors seeking to optimize their market timing and portfolio allocation. By providing clear, quantifiable metrics for measuring altcoin performance relative to Bitcoin, the index removes much of the guesswork from market cycle identification.
Success in altcoin trading requires more than just understanding market cycles; it demands sophisticated analytical tools and real-time data processing capabilities. Token Metrics represents the pinnacle of AI-driven cryptocurrency analysis, offering traders the advanced insights necessary to capitalize on altcoin season opportunities.
As the cryptocurrency market continues to evolve and mature, the combination of proven indicators like the Altcoin Season Index with cutting-edge AI analysis platforms will become increasingly important for sustained trading success. The future belongs to traders who can effectively combine traditional market wisdom with modern technological capabilities, positioning themselves to capture the significant opportunities that altcoin seasons provide.
Whether you're a seasoned trader or new to cryptocurrency markets, understanding and utilizing the Altcoin Season Index, supported by advanced analytics platforms like Token Metrics, will be crucial for navigating the complex and rewarding world of altcoin investing. The key lies in combining these powerful tools with sound risk management principles and a deep understanding of the underlying market dynamics that drive cryptocurrency performance cycles.
Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)







.svg)




.png)