
Upcoming Crypto Airdrops - The Gateway to Wealth Generation

Welcome to the world of crypto airdrops! In this article, we will explore the exciting space of upcoming crypto airdrops and how they have the potential to generate massive wealth.
As the crypto market continues to evolve and mature, airdrops have become an integral part of the ecosystem, offering investors and enthusiasts the opportunity to receive free tokens and participate in groundbreaking projects.
We will delve into the details of 16 highly anticipated projects that are set to make waves in the coming months. So buckle up and get ready for a wild ride into the world of upcoming crypto airdrops!
The Crypto Bull Run and Altcoin Season
Before we dive into the specific projects, let's take a moment to understand the context in which these airdrops are taking place. The crypto market is currently experiencing an unprecedented bull run, with Bitcoin leading the way.
As we approach the Bitcoin halving and the anticipated approval of the Bitcoin ETF, experts predict that we are on the brink of the biggest altcoin season ever. This means that while the returns on Bitcoin may start to diminish, there is still ample opportunity to make significant gains in altcoins.
The market has already surpassed the 1.7 trillion mark, and with the Bitcoin halving and ETF approval on the horizon, it is estimated that the market cap could reach as high as 14 trillion. This presents a golden opportunity for investors to capitalize on the altcoin frenzy and potentially achieve life-changing returns.
The Biggest Free Crypto Airdrops of All Time
Now, let's take a moment to reflect on some of the biggest free crypto airdrops in history. These airdrops have proven to be extremely lucrative for those who were fortunate enough to participate.
The most notable examples include Arbitrum, which distributed a staggering 12.6 billion dollars worth of tokens, with the average user receiving $2,200. Another highly successful airdrop was Uniswap, where the average participant received almost $30,000.
These figures are simply mind-boggling and highlight the immense potential of airdrops to generate wealth. However, it is important to note that not all airdrops are created equal, and careful selection is crucial to maximizing your returns.
How to Choose Promising Airdrops?
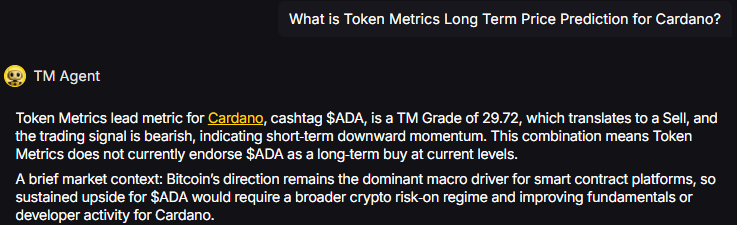
With over 600 projects to choose from, it can be overwhelming to determine which ones have the potential for significant returns. That's where Token Metrics comes in. Token Metrics is a leading platform that utilizes AI and data-driven analysis to evaluate and identify promising projects.
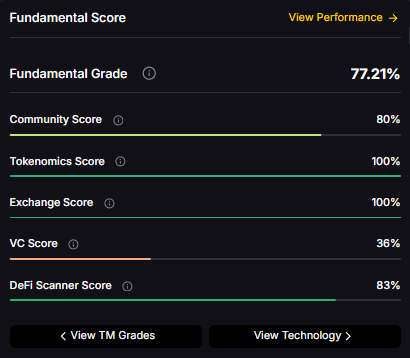
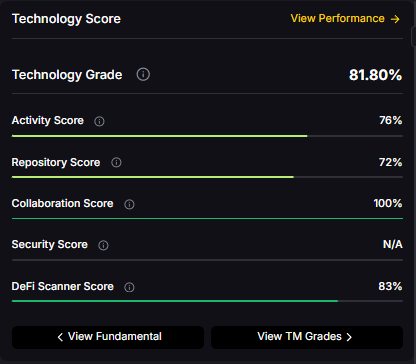
Their blockchain engineers and analysts have meticulously reviewed over 600 projects in the past year, focusing on two key criteria: technology and fundamentals.
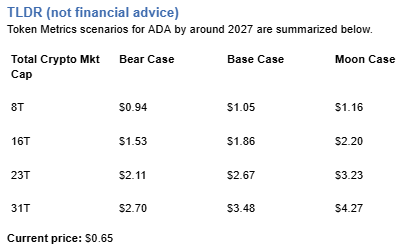
Only projects that score 80% or higher in technology or have solid fundamentals are considered for inclusion in their list of potential 100x airdrops.
By leveraging their expertise and track record, you can make informed decisions and increase your chances of participating in highly lucrative airdrops.
Confirmed Crypto Airdrops
Now, let's dive into the projects that have been confirmed to have upcoming airdrops. These projects have met Token Metrics' stringent criteria and have the potential to deliver substantial returns. Here are a few projects-
1. Starknet - Starknet is a scalability solution that operates as an Ethereum ZK rollup. With a tech score of 92%, this project is as legitimate as they come. The main narrative surrounding Starknet revolves around ZK rollups and layer two solutions.
It competes with other notable projects such as Linear, Scroll, Tyco, and Polygon ZKEVM. Having raised over $100 million at an $8 billion valuation, Starknet has garnered support from prominent investors like Paradigm, Sequoia, and Taka Global. The project has also witnessed significant growth in developer activity, making it one to watch closely for its upcoming airdrop.
2. Peaq - Peaq is a layer one blockchain for depin, boasting a tech score of 89%. This project aims to compete with leading L1 solutions like Solana by offering depin layer one functionalities.
With $6 million raised and notable investors such as Fundamental Labs backing the project, Peaq has already gained traction in the market.
Their testnet, Crest, further demonstrates their commitment to delivering a robust blockchain solution. If you are bullish on depin technologies, Peaq's upcoming airdrop is one you cannot afford to miss.
3. Dymension - Dymension is a blockchain platform for rollups, specializing in building modular rollup chains. With a tech score of 87%, Dymension has proven to be a solid contender in the space.
Its key narratives revolve around rollups, modular blockchains, and appchains. Competitors such as Caldera, Outlayer, and Opside keep the project on its toes, driving innovation and growth.
With $6.7 million raised and notable investors like Big Brain Holdings and Cognitive Ventures on board, Dymension's upcoming airdrop presents an exciting opportunity for investors looking to participate in the rollup revolution.
4. Movement - Movement is another promising project that has caught the attention of Token Metrics. As an investor in Movement's seed round, Token Metrics Ventures recognizes its potential for significant returns.
Movement is a modular blockchain that utilizes the Move VM and Move programming language. With a tech score of 85%, Movement offers developers the ability to launch their own blockchain or app chain quickly and efficiently.
Its key narratives revolve around Aptos and Sui ecosystems, making it an attractive option for those bullish on these technologies. With $3.4 million raised and investors like Borderless Capital and Token Metrics Ventures backing the project, Movement's upcoming airdrop is one to watch.
5. LayerZero - The LayerZero protocol, renowned for its unique approach to interoperability, has taken the crypto community by storm with its latest strategic move – the LayerZero Airdrop.
This event represents not just a chance for enthusiasts and supporters to receive a token of appreciation but also serves as a pivotal moment for increased network participation and adoption.
The platform serves as a protocol to facilitate interoperability, employing an innovative method to simplify the integration of various blockchain networks. LayerZero Labs, the creator of this protocol, successfully secured $120 million in funding, achieving a valuation of $3 billion in April.
As the buzz continues to build, participants eagerly await further details, underscoring the community's excitement and the protocol's potential to revolutionize cross-chain communication.
Likely Crypto Airdrops
In addition to the confirmed airdrops, there are also several projects that have incentive programs in place, making their airdrops highly likely to happen.
While these projects may not have met all the criteria for a confirmed airdrop, they still present enticing opportunities for investors. Here are a few projects that fall into this category:
1. Scroll - Scroll is a native ZK-EVM Layer 2 solution for Ethereum designed to enhance scalability. With a tech score of 89%, Scroll has proven its technical prowess. Key narratives surrounding Scroll include ZK rollups and Layer 2 solutions.
Competitors such as Starknet, Tyco, and Polygon ZK-EVM keep Scroll on its toes, fostering healthy competition and driving innovation.
Having raised over $120 million at a $3 billion valuation, Scroll has garnered support from prominent investors like A16Z Crypto, Sequoia, and OpenSea. With a significant developer community and growing traction, Scroll's upcoming airdrop is definitely one to watch.
2. Linea - Linea is a project from the team behind ConsenSys, the company behind Metamask. With a tech score of 90%, Linea is a force to be reckoned with in the ZK rollup space. Its key narratives revolve around ZK rollups and Layer 2 solutions.
Competing with projects like Starknet, Tyco, and Polygon ZK-EVM, Linear has raised $450 million in a series D funding round. With over 30 million monthly active users, Linea's upcoming airdrop presents an exciting opportunity for investors looking to participate in the ZK rollup revolution.
3. Ten - Ten is an upcoming airdrop that is definitely worth keeping an eye on. Obscuro, now firmly known as Ten, is a fully encrypted layer two Ethereum rollup.
This technology essentially aids in the scalability of Ethereum. It's somewhat of a hybrid between Optimistic and ZK, utilizing trusted execution environments (essentially hardware) to encrypt transactions.
With a tech score of 89%, it was a compelling investment for us. The major narratives surrounding Ten are privacy, rollups, and L2s.
Its competitors include Askec, Secret Network, and Railgun. Other investors in Ten are Qcoin Labs, Republic Capital, Big Brain, and Cogent Ventures. I'd like to draw a comparison within the privacy space of blockchains, specifically in terms of their flexibility and robustness.
On one end of the spectrum, we have Zcash, Monero, and Aztec, which are highly robust. Then we have Ten (formerly Obscuro) and Secret Network, which offer more flexibility. This comparison provides a sense of where these entities fit within the privacy spectrum.
4. Avail - Avail is a project that spun out of Polygon, making it a part of the Polygon ecosystem. With a tech score of 87%, Avail is poised to make waves in the crypto world. Its key narratives revolve around modular and data availability.
Competing with projects like Celestia and EigenLayer. Avail has already raised significant funding, including a valuation of $1.8 billion. With a growing ecosystem of builders and developers, Avail's upcoming airdrop is one you don't want to miss.
5. Parcl - Parcl is an innovative trading platform that allows users to engage in the real estate market across various cities in real-time, offering a unique approach to property investment.
Despite being a fundamental project with limited open-source code for technical review, it has garnered a credibility score of 77%, signaling its legitimacy.
The platform's arrival is timely, especially for those who may have missed out on previous Solana airdrops, and it's certainly worth monitoring.
Parcl stands out by tapping into the derivatives space of real-world assets, particularly real estate, which distinguishes it within the market, Parcl operates within its own niche with relatively little direct competition.
The project has successfully raised $4.1 million from noteworthy investors, including Archetype, Coinbase Ventures, Shema Capital, Tribe Capital, Dragonfly Capital, and NotBoring Capital.
Parcl's platform caters to both bullish and bearish sentiments in the real estate markets of major cities like London, Miami, Dallas, or Austin, Texas, enabling users to go long or short on real estate indices without engaging in physical property transactions.
This feature particularly appeals to crypto investors seeking to diversify their portfolios into real estate while remaining within the cryptocurrency ecosystem.
Moreover, the recent launch of a community points program by Parcl has sparked speculations about a potential airdrop, drawing parallels with the strategies of FrontTech, and increasing the platform's appeal among users and investors.
Possible Crypto Airdrops
Lastly, let's explore some projects that fall into the realm of speculation and excitement. These projects have not yet confirmed an airdrop, but they are certainly worth mentioning due to their potential. Here are a few projects that have caught our attention:
1. Eclipse - Eclipse is a Layer 2 blockchain that integrates Solana's virtual machine with Ethereum. Boasting a tech score of 94%, it's an exceptionally promising project.
Its main themes involve Solana, Layer 2 solutions, and modular blockchains. After securing $15 million in funding, it has attracted backing from notable investors such as Tribe Capital and Coin List.
Given its innovative approach and the potential to bridge Solana and Ethereum, this potential airdrop is worth watching.
2. Taiko - Taiko is a decentralized Ethereum equivalent type-one ZKEVM. With a tech score of 90%, Taiko has established itself as a solid contender in the ZK rollup space. Its key narratives revolve around ZK rollups and Layer 2 solutions.
Competitors like Scroll, Linea, and Polygon ZKEVM keep Taiko on its toes, fostering healthy competition and driving innovation. With $22 million raised and investors like Qcoin Ventures and GSR backing the project, Taiko's possible airdrop presents an exciting opportunity for investors looking to participate in the ZK rollup revolution.
3. Aztec - Aztec is a private ZK rollup on Ethereum that offers privacy at scale. With a tech score of 89%, Aztec is a strong contender in the privacy space. Its key narratives revolve around ZK rollups and Layer 2 solutions.
Competitors like Ten (formerly Obscura) and Railgun keep Aztec on its toes, fostering healthy competition and driving innovation.
With $100 million raised and investors like A16Z Capital and SV Angel backing the project, Aztec's possible airdrop is worth watching.
4. ZkSync - ZkSync is a Layer 2 Zk rollup that offers scalability and privacy. With a tech score of 89%, ZkSync is a force to be reckoned with in the Zk rollup space. Its key narratives revolve around Layer 2 solutions and Zk rollups.
Competitors like Scroll, Linea, and Starknet keep ZkSync on its toes, fostering healthy competition and driving innovation. With $200 million raised and prominent investors like Dragonfly and Lightspeed backing the project, ZkSync's possible airdrop presents an exciting opportunity for investors looking to participate in the Layer 2 revolution.
5. Zetachain - Zetachain is one such project that hasn't garnered much attention. While it's purely speculative at this point, it's worth considering. Zetachain is a layer-1 blockchain designed for Omnichain interoperability.
It has a tech score of 89% and is a layer-1 and cross-chain platform. Its competitors include Cosmos, IBC, Polkadot, and Bisham Network.
Zetachain has raised $27 million to develop an interoperable layer one blockchain that can connect all chains, including Bitcoin, Cosmos, and ETH.
Its investors include blockchain.com and other investors such as Jane Street and GSR. He provides a comparison table showing how Zetachain stacks up against Cosmos, Polkadot, ThorChain, and other bridges in messaging.
It's important to note that this information is from their project, so they claim to have all capabilities. This gives an idea of its competitiveness. It's worth monitoring for a potential airdrop. This is a project that hasn't been widely discussed.
6. Astria - Astria is a decentralized shared sequencer, addressing the growing concern about the centralization of sequencers. Astria aims to resolve this issue by decentralizing and sharing them. The technology is highly credible, with an 87% legitimacy rating. The key narratives here are modular rollups.
Astria, a modular blockchain, has raised $5.5 million to construct a shared C-concern network. Its investors include Maven 11, Delphi Digital, Figment, and Robot Ventures.
But how does it operate? Astria aims to fit into the modular narrative, share a sequencer, and decentralize it. This is similar to how Celestia attempted to do the same with data availability or EigenLayer.
Now, different parts of the blockchain are being taken, in this case, the sequencer, and turned into a shared and decentralized resource.
Token Metrics: Going Fully Web3
Now, let's shift our focus to an exclusive announcement that has never been shared before. Token Metrics, a leading platform for AI-driven crypto analysis, is going fully web three in early 2024.
This means that Token Metrics embraces decentralization and offers an airdrop exclusively for their customers. As a customer of Token Metrics, you will have the opportunity to participate in their airdrop and become part of their Web Three ecosystem.
This exciting development will bring together various products, including a trading bot, indices, and a mobile application, all connected through the Token Metrics token. Look for further details and instructions on qualifying for this exclusive future airdrop.
Conclusion
In conclusion, upcoming crypto airdrops offer an incredible opportunity for investors to generate substantial wealth. By carefully selecting promising projects and leveraging the expertise of platforms like Token Metrics, you can increase your chances of participating in highly lucrative airdrops.
Whether you choose to invest in confirmed airdrops, likely airdrops, or explore the realm of speculation, it is important to do your own research and make informed decisions.
The crypto market is full of exciting opportunities, and airdrops are just one of the many ways to take advantage of this rapidly evolving ecosystem. So buckle up and prepare for the wild ride of upcoming crypto airdrops!
Disclaimer
The information provided on this website does not constitute investment advice, financial advice, trading advice, or any other advice, and you should not treat any of the website's content as such.
Token Metrics does not recommend buying, selling, or holding any cryptocurrency. Conduct your due diligence and consult your financial advisor before making investment decisions.

.svg)

Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)













.svg)




.png)