
Web3 Wallets: Complete Guide to Digital Asset Management in 2025

The digital asset landscape has evolved dramatically, with web3 wallets becoming the essential gateway for managing cryptocurrencies, NFTs, and interacting with decentralized applications. As the cryptocurrency market reaches a staggering $2.3 trillion valuation in 2025, understanding how to securely store and manage your digital assets has never been more critical.
Unlike traditional banking apps that merely display account balances, web3 wallets provide users complete control over their crypto assets while enabling direct interaction with blockchain networks and smart contracts. This revolutionary approach to digital asset management has attracted over 150 million users globally, fundamentally changing how we think about ownership and financial sovereignty.
Whether you’re new to cryptocurrency or looking to enhance your Web3 security practices, this comprehensive guide will help you navigate the complex world of web3 wallets, understand the different types available, and choose the right solution for your needs.
What Are Web3 Wallets and Why You Need One
A web3 wallet serves as your digital gateway to the decentralized web, functioning as both a secure storage solution for valuable digital assets and an interface for interacting with blockchain-based services. Unlike custodial wallets managed by centralized exchanges, these digital wallet solutions give users direct control over their private keys and, consequently, their funds.
The key difference between web3 wallets and traditional financial apps lies in their ability to connect directly with decentralized applications. When you use a crypto wallet to interact with DeFi protocols, NFT marketplaces, or blockchain games, you’re not relying on intermediary services. Instead, your wallet software communicates directly with smart contracts on various blockchain networks.
This direct interaction capability has made web3 wallets indispensable in today’s crypto ecosystem. Users can collect NFTs, participate in decentralized finance protocols, vote in DAOs, and manage multiple digital assets across multiple chains—all from a single interface. The wallet serves as your digital identity on the blockchain, allowing you to sign transactions and authorize interactions with complete autonomy.
The gateway function extends beyond simple asset storage. Modern web3 wallets support multichain operations, enabling users to manage assets across multiple networks like Ethereum, Solana, Polygon, and dozens of other blockchain networks. This multi-chain support has become essential as the Web3 ecosystem has expanded beyond Ethereum to include diverse blockchain protocols optimized for different use cases.

How Web3 Wallets Function
Understanding the technical mechanics behind web3 wallets helps users make informed decisions about security and functionality. At their core, these wallets operate using cryptographic key pairs: a public key that serves as your wallet address for receiving funds, and a private key that proves ownership and enables you to sign transactions.
The seed phrase, typically consisting of 12 to 24 randomly generated words, serves as the master backup for wallet recovery. This recovery phrase mathematically generates your private keys, meaning anyone with access to your seed phrase can recreate your entire wallet on any compatible device. This system ensures that users maintain access to their assets even if their original device is lost or damaged.
When you initiate a transaction, your wallet software creates a digital signature using your private key. This signature proves to the network that you own the assets being transferred without revealing your private key itself. The transaction is then broadcast to the relevant blockchain network, where miners or validators verify and process it according to the network’s consensus rules.
Smart contract interaction represents one of the most powerful features of modern web3 wallets. When you connect to a decentralized application, the wallet doesn’t just send simple transactions—it can interact with complex programmable contracts that execute automatically based on predefined conditions. This enables sophisticated DeFi operations like yield farming, liquidity provision, and automated trading strategies.
Connection to blockchain nodes ensures real-time data synchronization and transaction verification. Most wallet software connects to multiple node providers to ensure reliability and prevent single points of failure. This distributed approach maintains the decentralized ethos while providing users with fast, reliable access to blockchain data.
Types of Web3 Wallets
The web3 wallet ecosystem offers three primary categories, each designed for different user needs and security requirements. Understanding these distinctions is crucial for choosing the right solution for your digital asset management strategy.
Non-Custodial Wallets
Non custodial wallets represent the purest form of Web3 asset management, providing users complete control over their private keys and eliminating reliance on third-party services. This self-custody approach aligns with Web3’s core principles of decentralization and user sovereignty.
MetaMask leads this category with over 30 million monthly active users, primarily serving the Ethereum ecosystem and EVM-compatible networks. Its browser extension design makes it the preferred choice for DeFi interactions, while its mobile app extends functionality to on-the-go asset management.
Phantom has captured the Solana ecosystem with 7 million users, offering specialized features for the high-speed, low-cost blockchain. The wallet’s integration with Solana’s unique architecture provides users with near-instant transactions and access to the growing Solana DeFi ecosystem.
Trust Wallet appeals to mobile-first users with support for 65+ blockchain networks and 60 million users worldwide. Its mobile apps for iOS and Android prioritize ease of use while maintaining non custodial principles, making it an excellent entry point for users transitioning from custodial solutions.
The primary advantage of non custodial wallets lies in true ownership—no company or government can freeze your assets or restrict your access. Users enjoy enhanced security practices through direct private key control and can interact with any compatible decentralized application without permission.
However, this freedom comes with significant responsibility. Users must secure their private keys offline and manage their own recovery options. Losing access to your seed phrase means permanently losing your assets, with no customer support team available to help recover lost funds.
Custodial Wallets
Custodial wallets bridge the gap between traditional finance and Web3, offering familiar login systems while providing access to blockchain networks. Major providers like Coinbase Wallet, Binance, and Kraken manage private keys on behalf of users, implementing enterprise-grade security measures and regulatory compliance protocols.
These platforms typically require KYC verification, collecting personal information to comply with financial regulations. While this reduces privacy compared to non custodial alternatives, it enables features like password recovery, customer support, and integration with traditional financial services.
The customer support availability represents a significant advantage for users who prefer having assistance when problems arise. Lost passwords can be recovered through email verification, and customer service teams can help resolve account issues—luxuries unavailable with self-custody solutions.
Integration with centralized exchanges provides seamless trading experiences, allowing users to move between spot trading, derivatives, and DeFi interactions without complex wallet connections. This unified experience appeals to users who want comprehensive crypto services from a single provider.
However, custodial solutions contradict Web3’s core principles of self-sovereignty. Users must trust the platform’s security measures and remain vulnerable to company policies, regulatory actions, and potential platform failures.
Smart Contract Wallets
Smart contract wallets represent the next generation of digital asset management, utilizing account abstraction technology to provide programmable wallet features that traditional wallets cannot offer. These innovative solutions address many pain points associated with conventional wallet designs.
Multi-signature security allows users to set customizable approval thresholds, requiring multiple parties to sign transactions before execution. This feature proves invaluable for organizations, families, or individuals managing significant digital asset portfolios who want enhanced security without sacrificing functionality.
Social recovery options eliminate dependency on seed phrases by allowing users to designate trusted contacts who can help recover wallet access. This system significantly reduces the risk of permanent asset loss while maintaining decentralized principles.
Gasless transactions and batched operations improve user experience by allowing wallet providers or dApps to sponsor transaction fees. Users can interact with blockchain networks without holding native tokens for gas, removing a major barrier to mainstream adoption.
Leading examples include Safe (formerly Gnosis Safe), which has secured billions in digital assets for organizations and power users. Argent focuses on mobile-first smart contract wallets with social recovery, while ZenGo implements Multi-Party Computation (MPC) technology to eliminate private keys entirely.
The enhanced security features come with increased complexity in setup and operation. Smart contract wallets often require more technical understanding and may have higher transaction costs due to their programmable nature.
Top Web3 Wallets in 2025
The current wallet landscape offers diverse solutions tailored to different blockchain ecosystems and user preferences. Understanding each wallet’s strengths helps users make informed decisions based on their specific needs and primary blockchain networks.
MetaMask: Leading Ethereum Wallet

MetaMask dominates the Ethereum ecosystem with over 30 million monthly active users accessing its browser extension and mobile apps. The wallet’s early entry into the market and consistent development have made it synonymous with Web3 interactions for many users.
The wallet supports Ethereum, Polygon, Arbitrum, Optimism, and over 500 other networks, making it the most versatile option for users active across multiple blockchain networks. Its extensive network support enables users to access virtually any EVM-compatible dApp or protocol.
Built-in token swaps through aggregators like 1inch and Paraswap provide competitive rates without leaving the wallet interface. This integration streamlines the trading process and helps users avoid the complexity of connecting to multiple decentralized exchanges.
Hardware wallet integration with Ledger and Trezor devices allows users to maintain maximum security for long term storage while enjoying the convenience of hot wallet interactions. This hybrid approach appeals to users managing significant digital asset portfolios.
Portfolio tracking and NFT gallery features help users monitor their holdings across multiple networks and view their digital collectibles in an organized interface. These features have become essential as users accumulate diverse digital assets across various protocols.
Phantom: Solana Ecosystem Leader

Phantom has established itself as the primary wallet for Solana with over 7 million users, capitalizing on the blockchain’s high-speed, low-cost transactions to create a superior user experience. The wallet’s design prioritizes speed and simplicity, reflecting Solana’s technical advantages.
Multi-chain expansion to Ethereum and Polygon in 2024 has broadened Phantom’s appeal beyond Solana natives. This strategic expansion allows users to manage assets across multiple networks while maintaining the wallet’s signature user experience.
The integrated NFT marketplace and staking interface provide native access to Solana’s vibrant NFT ecosystem and staking opportunities. Users can stake SOL directly from their wallet interface and browse trending NFT collections without connecting to external platforms.
Low transaction fees averaging $0.00025 on Solana make Phantom particularly attractive for users who frequently interact with dApps or trade frequently. This cost advantage has driven significant adoption among DeFi power users and NFT traders.
Built-in DeFi protocol connections and token swaps leverage Solana’s ecosystem of high-performance applications. The wallet’s integration with Jupiter aggregator ensures users receive competitive swap rates across Solana’s various DEXs.
Trust Wallet: Mobile-First Multi-Chain Solution

Trust Wallet serves 60 million users with comprehensive support for 65+ blockchain networks, positioning itself as the leading mobile-first wallet solution. Its acquisition by Binance has provided resources for continuous development while maintaining its decentralized, non custodial approach.
The mobile-first design philosophy prioritizes smartphone usability, recognizing that many users prefer managing their crypto assets on mobile devices. The iOS and Android apps offer intuitive interfaces optimized for touch interactions and mobile security features.
Integrated DEX aggregator and staking options for 20+ cryptocurrencies provide comprehensive DeFi access without requiring complex external connections. Users can stake popular tokens directly from their mobile interface and access liquidity across multiple networks.
WalletConnect support enables seamless connections to dApps across the web, allowing mobile users to interact with desktop-based protocols and services. This standard has become essential for mobile wallet functionality as the dApp ecosystem has expanded.
The recently launched browser extension in late 2024 has expanded Trust Wallet’s reach to desktop users, providing a unified experience across devices while maintaining the wallet’s mobile-optimized design principles.

Web3 Wallet Security Best Practices
Securing digital assets requires understanding and implementing multiple layers of protection. With over $50 billion in user assets at stake across various wallet platforms, following established security practices becomes critical for preventing loss through hacks, scams, or user error.
Private Key and Seed Phrase Protection
The fundamental rule of crypto security centers on protecting your private key and seed phrase—the cryptographic elements that provide access to your funds. These sensitive pieces of information should never be shared with anyone, regardless of their claims about wallet validation, technical support, or investment opportunities.
Store seed phrases offline in secure physical locations, avoiding digital storage methods that could be compromised by hackers. Consider using metal backup plates for important wallets, as these resist fire, water, and physical damage better than paper storage methods.
Use hardware wallets for holdings above $10,000, as these devices keep private keys offline and require physical confirmation for transactions. Leading hardware wallet providers like Ledger offer enhanced security for valuable digital assets through specialized secure elements and offline transaction signing.
Create multiple backup copies of your seed phrase and store them in different secure locations. This redundancy protects against localized disasters or theft while ensuring you maintain access to your assets if one backup becomes unavailable.
Avoid storing seed phrases in cloud services, email accounts, or smartphone photos, as these digital storage methods remain vulnerable to hacking, account compromise, or accidental exposure. Even encrypted cloud storage introduces unnecessary risk for such critical information.
Transaction Security
Always verify transaction details before signing, including recipient addresses, token amounts, and gas fees. Modern wallet software provides transaction previews, but users must develop habits of careful review before approving any blockchain interaction.
Use test transactions for large transfers above $1,000, sending small amounts first to verify addresses and network compatibility. This practice helps prevent costly mistakes and ensures successful delivery for significant transfers.
Check contract addresses on blockchain explorers like Etherscan before interacting with new protocols or tokens. Scammers frequently deploy fake contracts with similar names to legitimate projects, targeting users who don’t verify contract authenticity.
Enable transaction simulation features when available, as these tools predict transaction outcomes and identify potential issues before execution. Wallet guard features and simulation services help users understand complex smart contract interactions.
Monitor wallet activity regularly for unauthorized transactions or suspicious approvals. Many security breaches remain undetected for extended periods, allowing attackers to gradually drain funds or wait for optimal timing to exploit approvals.
Phishing and Scam Prevention
Only download wallets from official websites and app stores, verifying publisher information and reading user reviews before installation. Fake wallet apps on unofficial stores often contain malware designed to steal private keys or redirect funds to attacker-controlled addresses.
Verify URLs before connecting wallets to dApps, as phishing sites frequently use similar domain names to legitimate protocols. Bookmark trusted DeFi protocols and NFT marketplaces to avoid accidentally connecting to malicious copies.
Be cautious of unsolicited direct messages offering crypto opportunities, technical support, or claiming to represent wallet companies. Legitimate companies do not initiate contact through social media or messaging platforms to request sensitive information.
Never enter seed phrases on websites claiming to “validate” wallets, sync accounts, or resolve technical issues. Legitimate services never require seed phrase entry through web interfaces, and such requests always indicate scam attempts.
Use bookmarks for trusted DeFi protocols and NFT marketplaces rather than searching for them repeatedly. This practice reduces exposure to malicious advertisements and fake websites that may appear in search results.
Choosing the Right Web3 Wallet for Your Needs
Selecting an appropriate wallet requires evaluating your experience level, asset value, intended use cases, and technical requirements. The decision framework should prioritize security for significant holdings while considering convenience factors for frequent interactions.
Blockchain compatibility requirements vary significantly based on your preferred ecosystem. Ethereum users need robust EVM support, while Solana enthusiasts benefit from native integration with that ecosystem’s unique features. Multi-chain users should prioritize wallets offering seamless network switching and broad protocol support.
Feature prioritization depends on your primary activities within Web3. DeFi users benefit from integrated DEX aggregators and protocol connections, while NFT collectors need robust gallery features and marketplace integration. Traders might prioritize low fees and fast transaction processing.
Cost considerations include transaction fees, hardware wallet prices, and potential premium features. Ethereum’s higher gas costs make efficient transaction batching important, while Solana’s low fees enable more frequent interactions. Hardware wallets represent significant upfront costs but provide essential security for substantial holdings.
For Beginners
Start with custodial wallets like Coinbase Wallet for easy recovery and customer support while learning Web3 fundamentals. These platforms provide training wheels for the crypto ecosystem, allowing users to gain experience before taking on full self-custody responsibilities.
Use small amounts initially to learn wallet mechanics and understand transaction processes. Practice sending small amounts between addresses, connecting to simple dApps, and managing basic portfolio activities before committing significant funds.
Focus on major cryptocurrencies like Bitcoin and Ethereum during the learning phase, avoiding complex DeFi protocols or exotic tokens until you understand basic wallet operations. This conservative approach reduces risk while building foundational knowledge.
Gradually transition to non custodial options as confidence grows and understanding improves. This progression allows users to benefit from Web3’s self-sovereignty while developing necessary security habits and technical skills.
Take advantage of educational resources and tutorials provided by wallet companies and Web3 education platforms. Many wallet providers offer comprehensive guides and practice environments for learning safe usage patterns.
For Advanced Users
Implement a multi-wallet strategy combining hot and cold storage solutions based on usage frequency and security requirements. This approach optimizes both convenience for frequent interactions and security for long-term holdings.
Use hardware wallets for significant holdings and long term storage, keeping only necessary amounts in hot wallets for daily transactions and dApp interactions. This segmentation significantly reduces exposure to online threats while maintaining operational flexibility.
Consider smart contract wallets for DeFi activities and DAO participation, as these solutions provide enhanced security features and programmable functionality that benefit power users managing complex interactions.
Maintain multiple wallet addresses for privacy and security segmentation, using different addresses for different activities or protocols. This practice improves privacy and reduces the impact of potential security compromises.
Conduct regular security audits and wallet rotation practices, reviewing permissions granted to dApps and revoking unnecessary approvals. Many users accumulate hundreds of token approvals over time, creating unnecessary security risks.

Web3 Wallet Integration with Trading Platforms
Modern web3 wallets serve as more than storage solutions—they function as comprehensive interfaces for accessing the broader crypto ecosystem, including advanced trading platforms and research tools like Token Metrics. Understanding how wallets connect to various services helps users maximize their crypto experience while maintaining security.
WalletConnect protocol enables secure dApp interactions by creating encrypted connections between wallets and decentralized applications. This standard allows mobile users to connect their non custodial wallet to desktop dApps through QR code scanning, maintaining security while enabling complex interactions.
The integration capabilities extend beyond simple asset swaps to include sophisticated trading strategies and portfolio management. Advanced users can connect their wallets to platforms that provide comprehensive market analysis, trading signals, and portfolio optimization tools.
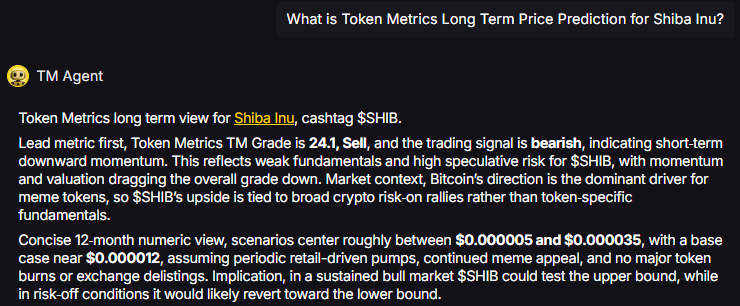
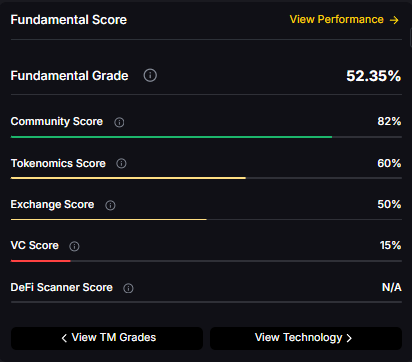
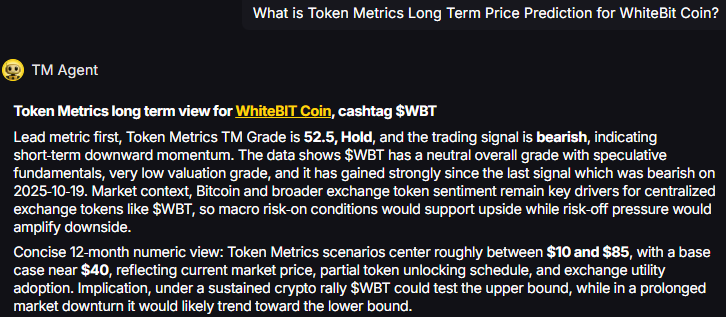
Token Metrics stands out as the leading cryptocurrency trading and research platform, offering AI-powered analytics that help users make informed decisions about their digital asset investments. The platform’s integration with web3 wallets provides seamless access to professional-grade research tools, including real-time market analysis, trading signals, and portfolio tracking features.
When connecting your wallet to trading platforms, Token Metrics offers unique advantages through its comprehensive research capabilities. The platform analyzes thousands of cryptocurrencies using artificial intelligence and machine learning algorithms, providing users with actionable insights that significantly improve trading outcomes.
The portfolio tracking features available through Token Metrics integration help users monitor their wallet holdings across multiple networks and protocols. This comprehensive analysis includes profit/loss calculations, risk assessment, and optimization recommendations based on current market conditions.
For users serious about cryptocurrency trading and investment, Token Metrics provides unparalleled research depth through its wallet integrations. The platform’s AI-driven approach to market analysis, combined with secure wallet connectivity, creates an optimal environment for making informed trading decisions while maintaining full control over your digital assets.
Future of Web3 Wallets
The evolution of web3 wallets continues accelerating as developers address current limitations and expand functionality. Several key trends are shaping the next generation of digital asset management solutions, promising improved user experiences and enhanced security.
Account abstraction adoption is reducing user experience friction by implementing smart contract-based wallets that eliminate many technical barriers to Web3 participation. This technology enables gasless transactions, social recovery options, and programmable wallet features that traditional wallets cannot provide.
Cross-chain interoperability improvements in 2025 are making multi-chain asset management more seamless and intuitive. New protocols and bridging solutions allow users to move assets between blockchain networks with minimal friction, while wallets integrate these capabilities natively.
Social recovery mechanisms are gradually replacing seed phrases as the primary backup method for wallet access. These systems allow users to designate trusted contacts who can help recover wallet access without compromising security or decentralization principles.
Biometric authentication and Multi-Party Computation (MPC) technology advancement is eliminating the need for traditional private key management while maintaining security. These approaches distribute cryptographic operations across multiple parties or devices, reducing single points of failure.
Integration with traditional financial services and Central Bank Digital Currencies (CBDCs) is expanding wallet utility beyond pure crypto applications. This convergence enables seamless interactions between traditional finance and decentralized protocols through unified wallet interfaces.
Mobile-first design trends and Web3 mobile app ecosystems are prioritizing smartphone experiences as the primary interface for blockchain interactions. This shift recognizes that mobile devices serve as the primary internet access point for many global users.
Frequently Asked Questions
Can I lose my crypto if I lose my wallet?
The answer depends on your wallet type and backup procedures. With non custodial wallets, losing your device doesn’t mean losing your crypto if you have your seed phrase safely stored. The seed phrase can recreate your wallet on any compatible device. However, if you lose both your device and seed phrase, your funds become permanently inaccessible. Custodial wallets typically offer account recovery through email or customer support, but you’re trusting the platform’s security and policies.
What happens if a wallet company shuts down?
For non custodial wallets, the company shutting down doesn’t affect your access to funds since you control the private keys. You can import your seed phrase into any compatible wallet software and continue accessing your assets. Custodial wallets present more risk—if the company fails, you might lose access to your funds unless they have proper bankruptcy procedures for returning user assets. This fundamental difference highlights the importance of understanding custody models.
How much does it cost to use web3 wallets?
Wallet software itself is typically free, but using wallets involves various costs. Transaction fees (gas costs) vary by blockchain network—Ethereum fees range from $5-50+ during peak times, while Solana transactions cost under $0.001. Some wallets charge small fees for built-in swap features. Hardware wallets cost $50-200+ upfront but provide enhanced security. Smart contract wallets may have higher transaction costs due to their programmable features.
Can I use multiple wallets?
Yes, using multiple wallets is a common and recommended security practice. Many users maintain separate wallets for different purposes—one for long term storage, another for DeFi interactions, and perhaps another for experimental or higher-risk activities. This segmentation improves security and privacy while allowing specialized configurations for different use cases. You can use the same seed phrase across multiple wallet apps or create entirely separate wallets for maximum security.
How do I transfer assets between wallets?
Transferring assets between wallets involves sending them from one address to another, just like sending to any other recipient. Copy the receiving wallet’s address, paste it into the sending wallet’s transfer interface, specify the amount, and confirm the transaction. Always verify the address carefully and consider sending a test amount first for large transfers. Ensure both wallets support the same blockchain network—you cannot send Ethereum tokens to a Bitcoin address, for example.
The landscape of web3 wallets offers unprecedented opportunities for financial sovereignty and participation in the decentralized internet. Whether you choose a simple custodial solution for convenience or embrace full self-custody for maximum control, understanding these tools is essential for navigating the modern crypto ecosystem.
Success in Web3 requires balancing security, functionality, and usability based on your individual needs and experience level. Start conservatively, educate yourself continuously, and gradually expand your capabilities as you become more comfortable with the technology.
For users serious about cryptocurrency trading and portfolio management, platforms like Token Metrics provide the research depth and analytical tools necessary for making informed decisions in this rapidly evolving space. Combined with proper wallet security practices, these resources create a foundation for successful long-term participation in the crypto economy.
Remember that Web3 technology continues evolving rapidly, with new security features, user experience improvements, and functionality enhancements constantly emerging. Stay informed about developments in your chosen wallet platforms and be prepared to adapt your strategies as the ecosystem matures.

.svg)

Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)




















.svg)




.png)