What Is a Moonshot? The Ultimate Guide to High-Risk, High-Reward Gems in Crypto (2025)

The term “moonshot” is everywhere in the crypto world—but what does it really mean? In 2025, as the search for the next 100x token intensifies, understanding the concept of a crypto moonshot is more important than ever. Moonshots offer massive upside potential, but they also come with high risk. So how do you find them, and more importantly, how do you separate hype from real opportunity?
In this guide, we’ll break down what a moonshot is, why it matters, how to identify one, and how tools like Token Metrics are helping investors discover the next big thing in crypto—before it takes off.
🚀 What Is a Moonshot in Crypto?
In crypto, a moonshot refers to a low-cap, high-potential cryptocurrency that could deliver outsized returns, typically 10x, 50x, or even 100x your initial investment. The term comes from the idea that a token is going “to the moon”—crypto slang for an explosive price increase.
Unlike established cryptocurrencies like Bitcoin and Ethereum, moonshots are usually early-stage projects with small market caps, limited trading volume, and a high level of speculation. These tokens often sit under the radar, only gaining traction once a specific narrative, innovation, or market trend brings them into the spotlight.
🧠 Characteristics of a Moonshot Token
While no one can guarantee a moonshot, successful ones often share several key traits:
1. Low Market Cap
Most moonshots start with a market cap under $50 million, sometimes even under $10 million. This gives them room to grow exponentially as adoption increases.
2. Strong Narrative or Trend Alignment
Moonshots usually align with emerging crypto narratives, such as:
- AI in crypto (e.g., TMAI)
- Real-world assets (RWA)
- Decentralized infrastructure (DePIN)
- ZK rollups and Layer-2s
- On-chain gaming and modular blockchains
3. Innovative Technology or Unique Use Case
They bring new ideas or solve real problems, giving them the potential to disrupt existing models.
4. Early Community Traction
Even if small, moonshots typically have loyal, vocal communities that drive awareness and support adoption.
5. Token Utility
Tokens that play a critical role in a product’s functionality (staking, access, governance) are more likely to gain value as adoption grows.
6. Exchange Listings
Getting listed on a major CEX (centralized exchange) or DEX (decentralized exchange) often serves as a catalyst for price surges.
⚠️ Moonshot = High Risk, High Reward
While the upside is massive, moonshots come with serious risks:
- Volatility: Prices can swing wildly in hours or minutes.
- Scams and rug pulls: Many low-cap tokens are created with malicious intent.
- Illiquidity: It may be hard to buy or sell large amounts.
- Overhype: Narratives can fizzle out quickly, leaving bag holders behind.
- Lack of product-market fit: Many projects never deliver a working product.
Risk management is essential. Only allocate a small portion of your portfolio to moonshots and always do your own research.
🔍 How to Identify Crypto Moonshots
Finding true moonshots is part art, part science. Here are practical steps to help spot them:
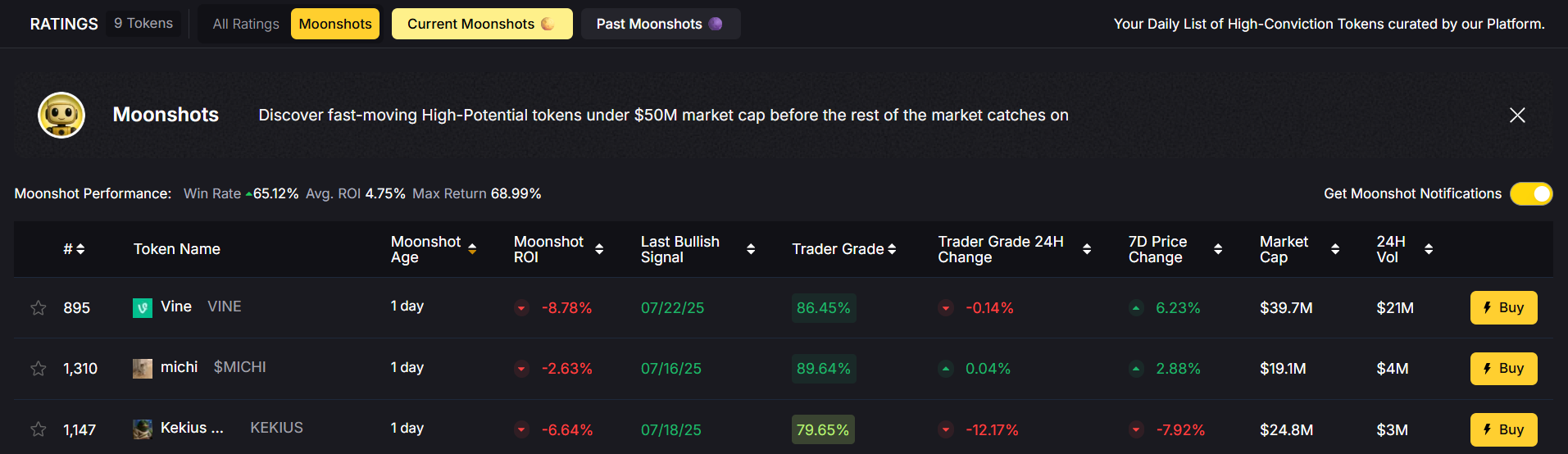
1. Use Token Metrics Moonshots Feature
Token Metrics, the leading AI-powered crypto research platform, features a dedicated Moonshots tab that helps users discover early-stage altcoins with massive potential.
Token Metrics uses AI models to:
- Scan over 6,000+ tokens
- Analyze 80+ on-chain and off-chain data points
- Score tokens based on Investor Grade (long-term) and Trader Grade (short-term)
- Highlight tokens before they hit mainstream radar
2. Follow Emerging Narratives
Pay attention to sectors gaining momentum—AI, DePIN, L2s, gaming, and RWA are hot in 2025. Moonshots often emerge at the intersection of narrative and innovation.
3. Explore Crypto Twitter and Discord
Many early-stage gems are discussed by small communities, KOLs (key opinion leaders), and early investors before any mainstream media coverage.

4. Check Tokenomics
A great idea can’t succeed with poor tokenomics. Look for:
- Fair initial distribution
- Deflationary or limited supply
- Lock-up periods for team/investors
- Strong incentive alignment with users
5. Monitor DEX Launchpads and On-Chain Metrics
Platforms like Uniswap, Camelot, or Base-native DEXs are where most moonshots launch first. Analyze:
- Wallet distribution (whale vs retail)
- Volume and liquidity
- Holder growth
🔬 How Token Metrics Helps You Find the Next Moonshot
Token Metrics is the ultimate tool for discovering and validating moonshot opportunities. Here’s how:
🧠 AI-Driven Token Ratings
Get real-time Investor Grade and Trader Grade scores, generated by AI models trained on historical altcoin performance.
📈 Bullish & Bearish Signals
Get alerts when a token shows strong upside or downside momentum based on quantitative signals.
🚀 Moonshots Section
A curated feed of low-cap, high-potential tokens filtered by market cap, sector, risk level, and on-chain traction.
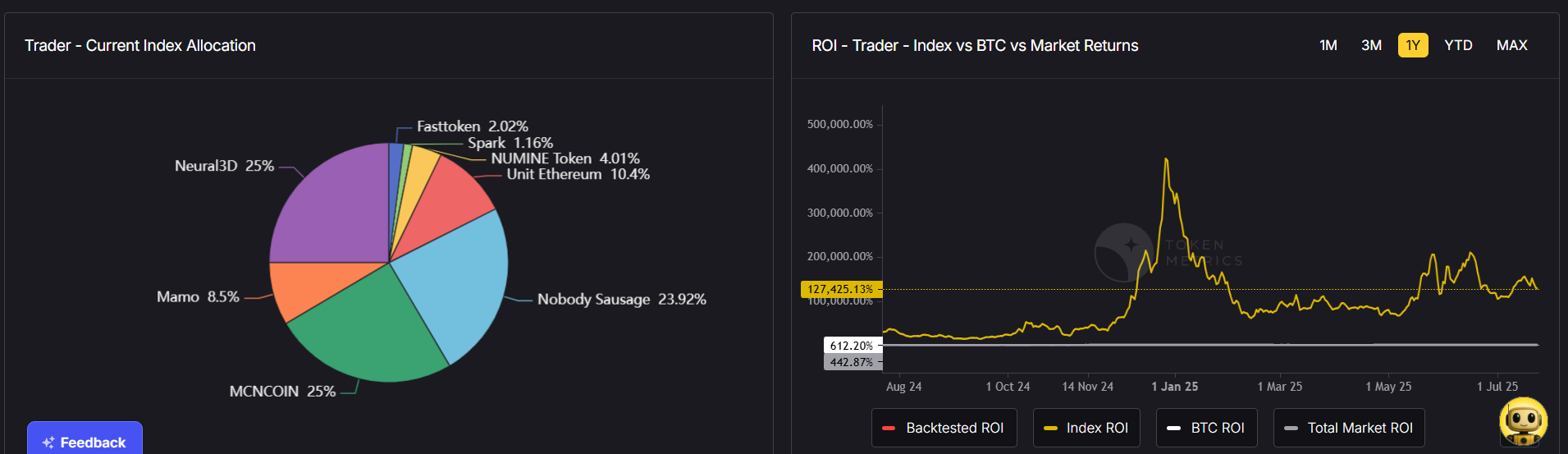
📊 Backtesting & Risk Analysis
Use simulation tools to see how a moonshot would have performed in different market conditions, helping you gauge timing and position sizing.
👉 Try Token Metrics with a 7-day free trial and start exploring moonshots with data, not just hype.
✅ Examples of Real Moonshots
In previous years, several tokens started as moonshots and delivered massive gains:
- Polygon (MATIC) – Launched below $0.01, surged to over $2.50 at peak
- Axie Infinity (AXS) – Went from cents to $165 during the 2021 gaming boom
- Pepe (PEPE) – Meme coin that turned thousands into millions in 2023
- VIRTUAL (SPX6900) – Token Metrics alerted this 55x trade before the crowd
In 2025, emerging moonshots include AI-powered tokens like $TMAI (Token Metrics AI)—positioned at the forefront of AI + crypto convergence.
🛡️ Tips for Safely Investing in Moonshots
- Only use risk capital (money you can afford to lose)
- Start small and scale positions after traction
- Set profit targets and stop-losses
- Diversify across 5–10 moonshot tokens
- Use non-custodial wallets and keep private keys secure
- Don’t chase pumps—enter early or not at all
Moonshot investing isn’t about certainty—it’s about asymmetrical bets with defined downside and massive upside.
Final Thoughts
Moonshots are the heartbeat of crypto innovation. They represent the bold, risky, and visionary projects that could reshape entire industries—or fade into obscurity.
In 2025, the opportunity to find the next Solana, MATIC, or PEPE still exists—but success comes from informed decisions, not hype-driven FOMO. That’s why platforms like Token Metrics are critical. With AI-powered research, curated moonshot lists, and real-time trading signals, Token Metrics helps you spot the gems before they moon.
So, what’s your next moonshot?
Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)









.svg)




.png)