
What Is Proof of Stake? A Complete Guide to PoS in 2025
Introduction: Why Proof of Stake Matters
In the world of blockchain, consensus mechanisms are what keep networks secure and functional. One of the most important of these is Proof of Stake (PoS)—a model that has become the standard for next‑generation blockchains like Ethereum, Cardano, and Solana.
In 2025, PoS dominates the crypto landscape, offering a more energy‑efficient, scalable, and inclusive alternative to the older Proof of Work (PoW) model. This article breaks down how PoS works, why it matters, its benefits and risks, and how platforms like Token Metrics can help investors optimize staking strategies.
What Is Proof of Stake?
Proof of Stake is a consensus mechanism that allows blockchains to validate transactions and create new blocks based on the number of tokens held (or “staked”) by network participants.
Instead of using powerful computers to solve complex puzzles (as in Proof of Work), PoS relies on validators—individuals or entities who lock up tokens as collateral to help maintain the network.
In return, these validators earn staking rewards, making PoS not only an essential part of blockchain operations but also a way for investors to generate passive income.
How Does Proof of Stake Work?
- Staking Tokens:
Participants lock up their tokens (e.g., ETH, ADA) in a wallet or staking pool. - Validator Selection:
The network algorithm selects validators to propose and confirm new blocks based on their stake size and other factors (sometimes including randomness). - Block Validation:
Validators verify transactions and add new blocks to the chain. - Reward Distribution:
Validators earn rewards in the form of newly minted tokens or transaction fees. - Penalties (Slashing):
Misbehavior—such as double‑signing or being offline—can result in losing a portion of the staked tokens, ensuring network security and accountability.
Proof of Stake vs. Proof of Work
Proof of Work (PoW):
- Used by Bitcoin.
- Requires high‑energy mining operations.
- Limited scalability.
Proof of Stake (PoS):
- Used by Ethereum (post‑Merge), Cardano, Solana, and many others.
- Energy‑efficient—uses 99% less energy than PoW.
- More scalable, enabling faster and cheaper transactions.
In 2025, PoS is considered the future of blockchain consensus thanks to its efficiency and accessibility.
Major PoS Blockchains in 2025
- Ethereum (ETH):
Transitioned to PoS in 2022 during The Merge, allowing ETH holders to stake and earn rewards. - Cardano (ADA):
Pioneered a research‑driven PoS model (Ouroboros) for secure and sustainable blockchain growth. - Solana (SOL):
Combines PoS with Proof of History for high‑speed, low‑cost transactions. - Polkadot (DOT):
Uses a Nominated Proof of Stake (NPoS) model, letting token holders nominate validators for network security. - Token Metrics AI (TMAI):
Integrates PoS into its ecosystem while leveraging AI analytics for blockchain intelligence.
Benefits of Proof of Stake
- Energy Efficiency:
PoS drastically reduces environmental impact compared to PoW mining. - Accessibility:
Anyone can stake tokens—no need for expensive mining hardware. - Passive Income:
Token holders earn rewards by participating in staking pools or running validator nodes. - Decentralization & Security:
PoS encourages broader participation, strengthening network security.
Risks of Proof of Stake
While PoS is revolutionary, it’s not without challenges:
- Slashing Penalties: Validators who act maliciously or go offline risk losing their stake.
- Centralization Risks: Large holders may dominate staking pools, reducing decentralization.
- Liquidity Issues: Staked tokens are often locked for a period, limiting flexibility.
- Regulatory Uncertainty: As staking becomes more widespread, governments are exploring potential regulations.
Platforms like Token Metrics help mitigate these risks by offering in‑depth analytics on validators, staking pools, and network activity.
How to Earn with PoS: Staking in 2025
1. Solo Staking:
Run your own validator node. This requires technical expertise and meeting minimum staking requirements (e.g., 32 ETH for Ethereum).
2. Pooled Staking:
Join staking pools that combine funds from multiple users, making it easier for beginners to participate.
3. Liquid Staking:
Use platforms like Lido or Rocket Pool to stake while maintaining liquidity through derivative tokens you can trade or use in DeFi.
4. Exchange Staking:
Centralized exchanges (e.g., Coinbase, Binance) offer simple staking options, though they often take a fee.
Using Token Metrics for PoS Insights
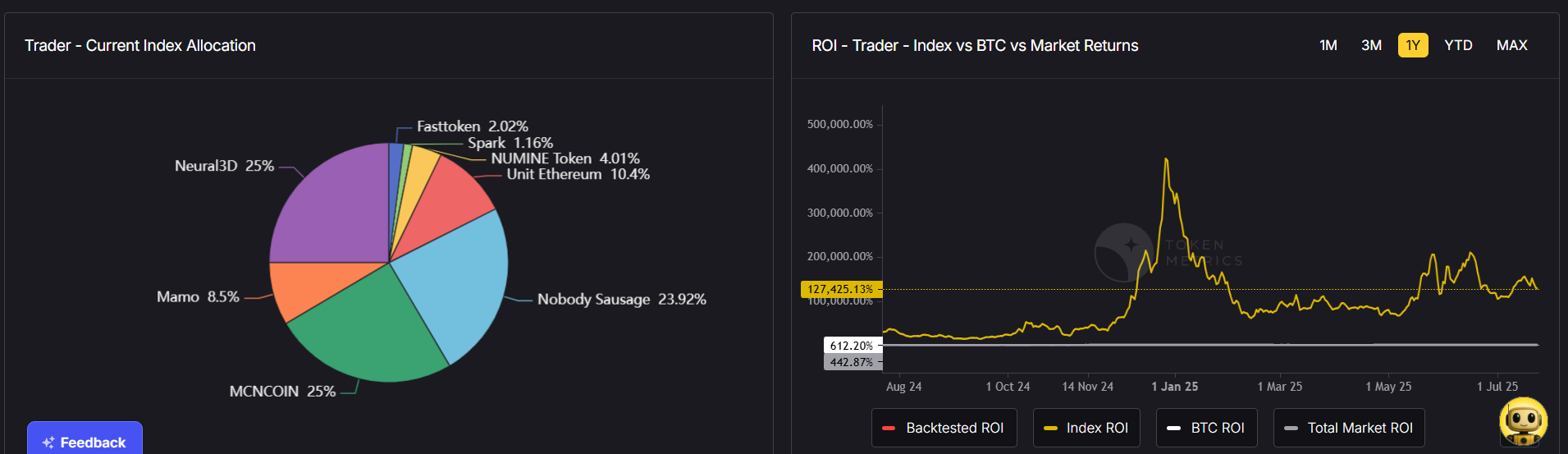
Token Metrics empowers PoS investors with:
- AI‑Driven Analytics: Identify the most profitable staking opportunities.
- Validator Ratings: Evaluate validators based on performance, uptime, and security.
- Portfolio Optimization: Balance your staked assets across multiple blockchains.
- Market Signals: Get alerts when staking yields or network conditions change.
This makes staking easier, safer, and more profitable for both beginners and experienced investors.
Practical Tips for PoS Investors
- Diversify: Stake across multiple blockchains to minimize risk.
- Research Validators: Choose validators with strong reputations and consistent uptime.
- Stay Liquid: Use liquid staking platforms for flexibility.
- MonitorRewards: Use Token Metrics to track real‑time staking yields and make adjustments.
The Future of Proof of Stake
In 2025, PoS is expected to power the majority of leading blockchains, supporting innovations in DeFi, NFTs, AI‑driven ecosystems, and real‑world asset tokenization.
Its combination of efficiency, scalability, and accessibility makes it the go‑to consensus mechanism for the next era of Web3 development.
Conclusion
Proof of Stake has redefined how blockchains achieve consensus, making networks more sustainable, secure, and inclusive. For investors, PoS offers an exciting opportunity to earn passive income while supporting blockchain ecosystems.
By leveraging AI‑powered analytics from Token Metrics, you can maximize staking rewards, identify top‑performing validators, and manage risk effectively.
In 2025, understanding PoS isn’t just for developers—it’s an essential tool for every crypto investor.

.svg)

Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)








.svg)




.png)