
What is Spot Trading in Crypto: A Complete Beginner’s Guide

When you buy Bitcoin on Coinbase and it instantly appears in your wallet, you’ve just completed a spot trade. Unlike complex derivatives or leveraged products, spot trading in crypto represents the most straightforward way to buy and own digital assets at current market prices.
Spot trading refers to the practice of buying and selling cryptocurrencies for immediate delivery and settlement. The term “spot” indicates that transactions happen “on the spot” - you purchase crypto at the current market price and gain immediate ownership without any future obligations or contractual arrangements.
In this comprehensive guide, you’ll discover exactly how crypto spot trading works, how it compares to other trading methods, and whether it’s the right approach for your investment goals. Whether you’re a complete beginner or looking to understand the fundamentals better, this article will give you the knowledge needed to begin spot trading confidently.
What is Spot Trading in Cryptocurrency?
Spot trading is the direct purchase and sale of digital assets at their current market prices with immediate settlement and ownership transfer. When you execute a spot trade, you’re buying the actual cryptocurrency - not a contract or derivative based on its value.
The “on the spot” concept means trades execute instantly at real-time market prices determined by supply and demand on the crypto exchange. Unlike futures contracts or options trading, there are no predetermined price agreements or future delivery dates involved. You pay the current price, receive the digital asset immediately, and gain full control over your cryptocurrency.
Popular trading pairs in spot markets include:
- BTC/USDT (Bitcoin paired with Tether stablecoin)
- ETH/USD (Ethereum paired with US dollars)
- ADA/BTC (Cardano paired with Bitcoin)
- DOT/USDC (Polkadot paired with USD Coin)
The immediate ownership transfer distinguishes spot trading from derivatives trading. Once your buy order executes, the cryptocurrency moves directly into your exchange wallet or can be withdrawn to your personal wallet. This direct asset ownership provides complete control over your digital assets, including the ability to stake, lend, or transfer them as desired.
How Does Crypto Spot Trading Work?
The process of crypto spot trading follows a straightforward sequence that beginners can master quickly:
Step 1: Choose a Crypto Exchange Select a reputable cryptocurrency exchange like Binance, Coinbase Pro, Kraken, or Gemini. Consider factors like security measures, trading volume, supported cryptocurrencies, and fee structures.
Step 2: Register and Verify Your Account Complete the registration process and KYC (Know Your Customer) verification. Most exchanges require identity verification to comply with regulations and implement security measures.
Step 3: Deposit Funds Fund your account using fiat currency (USD, EUR) via bank transfer or credit card, or deposit existing cryptocurrencies from another wallet.
Step 4: Select Your Trading Pair Choose the cryptocurrency you want to buy and the currency you’ll use to purchase it. For example, if you want to buy Ethereum with US dollars, you’d select the ETH/USD trading pair.
Step 5: Place Your Order Submit either a market order or limit order based on your trading strategy and timing preferences.
Market Orders vs Limit Orders
Understanding order types is crucial for effective spot trading:
Market Orders execute immediately at the current market price. When you place a market order to buy Bitcoin, you’ll purchase it at the lowest available ask price. This guarantees execution but not the exact price, especially during periods of high market volatility.
Limit Orders specify the exact price you’re willing to pay. For example, if Bitcoin trades at $45,000 but you only want to buy at $44,000, you’d place a limit order at that specified price. The trade only executes if the market reaches your target price.
Order Book Mechanics
The order book displays all pending buy orders (bids) and sell orders (asks) for a trading pair. Bids appear in descending price order, while asks appear in ascending order. The difference between the highest bid and lowest ask creates the “spread.”
When you place a market order, the exchange’s matching engine pairs your order with the best available opposite order. High liquidity markets with many participants typically have tighter spreads and faster execution, while low liquidity markets may experience price slippage during volatile periods.
The immediate settlement process means ownership transfers instantly upon order execution. Unlike traditional stock markets with T+2 settlement, cryptocurrency spot trades settle in real-time, giving you immediate access to your purchased digital assets.
Spot Trading vs Other Trading Methods
Understanding how spot trading compares to other trading methods helps you choose the right approach for your risk tolerance and investment goals.
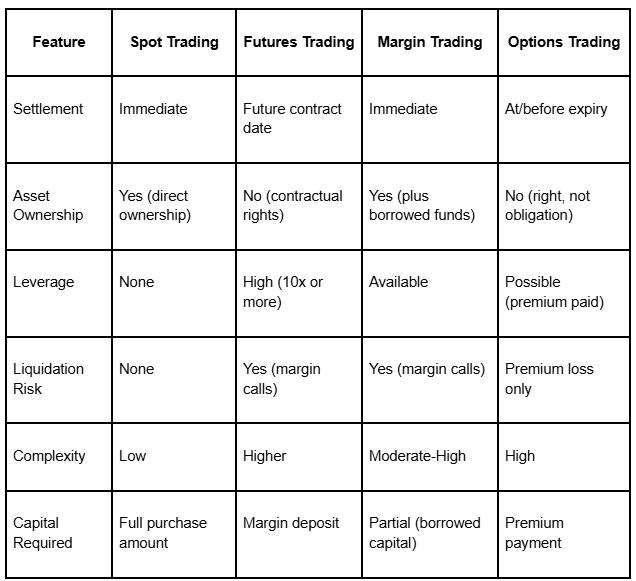
Spot Trading vs Margin Trading
Margin trading allows traders to borrow funds from the crypto exchange to increase their position size beyond their initial investment. While this can amplify potential profits, it also magnifies losses and introduces significant risks that don’t exist in spot trading.
In margin trading, borrowing funds creates leverage that can lead to margin calls when positions move against you. If your trade loses value and approaches the minimum margin requirement, the exchange may forcibly close your position to protect the borrowed funds. This liquidation can result in losing more than your initial investment.
Spot trading eliminates these risks by limiting potential losses to your initial investment. You can’t lose more than you put in because you’re not borrowing money. This makes spot trading the safer choice for beginners and risk-averse traders who want exposure to price movements without the downside risk of liquidation.
Experienced traders might use margin trading to amplify gains, but the commodity futures trading commission and other regulatory bodies consistently warn about the significant risks involved with leveraged products.
Spot Trading vs Futures Trading
Futures contracts obligate traders to buy or sell an underlying crypto asset at a predetermined price on a specific future date. These financial instruments allow speculation on future price movements without immediate purchase or delivery of the digital asset.
Spot trading provides immediate settlement and direct ownership, while futures trading involves contractual obligations and potential leverage. Futures prices can diverge from spot prices based on market expectations, interest rates, and other factors affecting the cryptocurrency market.
Traders speculate on price movements differently in each market. Spot traders profit by buying low and selling at a higher price, while futures traders can profit from both rising and falling markets through long and short positions. However, futures trading requires more sophisticated understanding of market conditions and carries higher risks due to leverage and margin requirements.
Advantages of Spot Trading
Spot trading offers several compelling benefits that make it attractive to both newcomers and experienced traders:
Simplicity and Ease of Understanding Spot trading’s straightforward nature makes it accessible to beginners. You buy cryptocurrency at the current price and own it immediately - no complex contracts, expiration dates, or margin calculations to worry about.
Direct Asset Ownership Unlike derivatives trading, spot trading gives you actual ownership of digital assets. You can withdraw your Bitcoin to a hardware wallet, stake your Ethereum, or use your cryptocurrencies in DeFi protocols. This direct ownership provides complete control over your financial assets.
Transparent Pricing Spot market prices reflect real supply and demand dynamics without the complexity of futures curves or options pricing models. The current market price you see represents what other traders are willing to pay right now.
Lower Risk Profile Spot trading eliminates the risk of margin calls, liquidations, and borrowing costs associated with leveraged products. Your maximum loss equals your initial investment, providing clear risk boundaries for portfolio management.
Wide Availability Major cryptocurrency exchanges like Binance, Coinbase, Kraken, and others offer robust spot markets with high trading volumes. This broad availability ensures you can access spot trading regardless of your location or experience level.
No Time Pressure Unlike options with expiration dates or futures contracts with settlement requirements, spot positions have no time constraints. You can hold your digital assets as long as desired without worrying about contract expiration.
Disadvantages of Spot Trading
Despite its advantages, spot trading has limitations that traders should understand:
Full Market Volatility Exposure Crypto spot trading exposes you to the complete volatility of the cryptocurrency market without built-in hedging mechanisms. When Bitcoin drops 20% in a day, your spot position loses the same percentage with no protection.
No Short Selling Capability Spot trading only allows you to profit from rising prices unless you already own the asset to sell. You cannot profit from falling markets through short selling without using additional financial instruments like futures or margin trading.
Capital Intensive Spot trading requires the full purchase amount upfront. If you want $10,000 exposure to Ethereum, you need $10,000 in capital. Leveraged products allow similar exposure with less capital, though with higher risks.
Limited Profit Potential Without leverage, your profit potential is limited to the actual price movements of the underlying crypto asset. A 50% increase in Bitcoin price generates a 50% profit, while leveraged trading could amplify those gains (and losses).
Price Slippage Risk During periods of high market volatility or low liquidity, large market orders may experience slippage - executing at worse prices than expected. This particularly affects trading in smaller altcoins with lower trading volumes.
No Built-in Risk Management Spot trading lacks the sophisticated risk management tools available in derivatives markets. You cannot easily hedge positions or create complex trading strategies without using multiple instruments.
Popular Spot Trading Strategies
Successful spot traders employ various trading strategies based on their risk tolerance, time horizon, and market analysis approach:
Buy and Hold (HODL) This long-term strategy involves purchasing major cryptocurrencies like Bitcoin or Ethereum and holding them for extended periods. Buy and hold traders believe in the long-term adoption and price appreciation of established digital assets, ignoring short term price fluctuations.
Dollar Cost Averaging (DCA) DCA involves making regular purchases regardless of current market price to smooth out volatility over time. For example, buying $500 worth of Bitcoin every month reduces the impact of timing the market and can lower your average purchase price during volatile periods.
Day Trading Day traders capitalize on short term price movements within a single trading session. They use technical analysis to identify entry and exit points, often making multiple trades per day to profit from intraday volatility in the crypto market.
Swing Trading Swing traders hold positions for days or weeks to capture medium-term trends. This trading strategy requires analyzing both technical indicators and fundamental factors that might drive price movements over several days.
Arbitrage Trading Arbitrage involves exploiting price differences for the same cryptocurrency across different exchanges. If Bitcoin trades at $45,000 on Exchange A and $45,200 on Exchange B, arbitrage traders buy on the cheaper exchange and sell on the more expensive one for risk-free profit.
Range Trading Range traders identify cryptocurrencies trading within specific price ranges and buy near support levels while selling near resistance levels. This strategy works best during sideways market movements when prices oscillate within defined boundaries.
Getting Started with Spot Trading
Beginning your spot trading journey requires careful preparation and a methodical approach:
Choose Reputable Exchanges Start with established cryptocurrency exchanges that prioritize security and regulatory compliance. Binance offers high liquidity and numerous trading pairs, Coinbase Pro provides user-friendly interfaces for beginners, while Kraken and Gemini are known for strong security measures.
Complete Security Setup Implement security measures including two-factor authentication (2FA), strong passwords, and withdrawal whitelist features. Never share your login credentials and consider using a dedicated email address for your crypto exchange accounts.
Start with Major Cryptocurrencies Begin with established digital assets like Bitcoin (BTC) and Ethereum (ETH) before exploring smaller altcoins. These major cryptocurrencies typically have higher liquidity, tighter spreads, and more predictable price movements suitable for learning.
Begin with Small Amounts Start with amounts you can afford to lose while learning platform mechanics and developing your trading strategy. Small initial investments allow you to understand how orders work, how fees impact profits, and how market volatility affects your positions.
Use Limit Orders for Better Control Limit orders help you control entry prices and avoid paying more than intended, especially important during volatile market conditions. While market orders guarantee execution, limit orders provide price protection at the cost of potential missed opportunities.
Educate Yourself Continuously Develop skills in both technical analysis and fundamental analysis. Technical analysis helps identify entry and exit points using price charts and indicators, while fundamental analysis evaluates the underlying value and adoption prospects of different cryptocurrencies.
Practice Risk Management Never invest more than you can afford to lose, diversify across multiple cryptocurrencies, and consider setting stop-loss levels even though spot trading doesn’t require them. Successful trading depends more on managing downside risk than maximizing gains.
Is Spot Trading Profitable?
Spot trading profitability depends on multiple factors including market timing, research quality, risk management, and trading discipline. While the cryptocurrency market has created significant wealth for early adopters and skilled traders, success is never guaranteed.
Factors Affecting Profitability:
Market volatility creates both opportunities and risks. The crypto market experiences significant price fluctuations that can generate substantial profits for well-timed trades, but the same volatility can lead to significant losses if you buy at market peaks.
Your research and analysis capabilities directly impact trading success. Traders who understand fundamental analysis (evaluating project technology, adoption, and competition) combined with technical analysis (chart patterns and indicators) typically achieve better results than those trading on emotions or tips.
Risk management practices separate successful traders from those who lose money. Using proper position sizing, maintaining diversified portfolios, and having clear exit strategies help protect capital during inevitable market downturns.
Short-term vs Long-term Approaches:
Short term trading requires more active management and technical skills but can potentially generate quicker profits during favorable market moves. However, frequent trading increases costs through fees and taxes while requiring significant time investment.
Long-term holding strategies have historically rewarded patient investors in major cryptocurrencies, though past performance doesn’t guarantee future results. Bitcoin and Ethereum have appreciated substantially over multi-year periods despite significant interim volatility.
Risk Considerations:
All crypto trading involves substantial risk of loss. The market can move against positions quickly, and even established cryptocurrencies can lose significant value during market downturns. Regulatory changes, security breaches, and technological issues can also impact cryptocurrency values.
Trading costs including exchange fees, withdrawal fees, and tax implications reduce net profits. High-frequency trading strategies may see profits eroded by cumulative fees, making longer-term approaches more cost-effective for smaller accounts.
Success Requirements:
Profitable spot trading typically requires continuous education about cryptocurrency technology, market dynamics, and trading techniques. Successful traders develop discipline to stick to their strategies during emotional market periods and avoid impulsive decisions based on fear or greed.
Market conditions constantly evolve, requiring adaptation of trading strategies and ongoing learning. What works during bull markets may fail during bear markets, and successful traders adjust their approach based on changing market cycles.
Conclusion
Spot trading in crypto offers the most straightforward path to cryptocurrency ownership, providing immediate settlement, direct asset control, and transparent pricing without the complexity of derivatives or the risks of leverage. While it requires full capital upfront and limits profit potential to actual price movements, spot trading eliminates margin call risks and provides a solid foundation for building cryptocurrency knowledge.
Whether you choose buy-and-hold strategies for long-term wealth building or more active approaches like swing trading, spot trading gives you real ownership of digital assets with clear risk boundaries. The key to success lies in choosing reputable exchanges, starting with established cryptocurrencies, implementing proper risk management, and continuing your education about market dynamics.
For newcomers to the cryptocurrency market, spot trading represents the safest entry point to gain exposure to this revolutionary asset class while learning essential trading skills that can be applied to more sophisticated strategies later.

.svg)

Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)









.svg)




.png)