
What is Web3 and How is it Different from the Current Internet? The Future of Decentralized Digital Experiences

The internet as we know it today is undergoing a major transformation. While most internet users spend their time on Web2 platforms (often referred to as Web 2.0)—scrolling through social media feeds, shopping on centralized e-commerce sites, or streaming videos—an emerging paradigm known as Web3 promises to revolutionize how we interact with digital services. This new model aims to give individual users more control over their data, digital assets, and online identities, fundamentally changing how the internet operates and who holds power within it. There are fundamental differences between Web3 and the current internet that impact interoperability, data management, and openness. Understanding what is Web3 and how is it different from the current internet requires examining the key differences between Web3 and Web 2.0, especially as Web3 introduces new economic models and decentralized governance structures that challenge traditional institutions.
Understanding Web3: Beyond the Buzzword
At its core, Web3 represents the third generation of the internet, often referred to as web 3.0, built on decentralized networks and blockchain technology. A decentralized network distributes data and control across multiple nodes, operating without central authorities and offering advantages like increased security, censorship resistance, and enhanced user control. Unlike the centralized model of today’s internet, where a handful of big tech companies control platforms, user data, and digital interactions, Web3 envisions a decentralized web where users truly own their data, digital assets, and online identities. This shift is not merely a technical upgrade but a fundamental reimagining of how the internet operates and who controls it.
Web3 applications rely on blockchain networks that distribute data and control across multiple nodes, eliminating the need for a central authority or centralized servers. Instead of trusting centralized platforms like Facebook or Amazon to manage and monetize your data, Web3 applications allow users to interact directly on a peer to peer network, empowering individuals to participate in transactions and access decentralized financial tools without intermediaries. This decentralized infrastructure enables decentralized applications (dApps) to function without intermediaries, creating a user driven internet where user ownership and participation are paramount. Unlike Web2, where platforms retain control, Web3 emphasizes data ownership, ensuring users retain rights over their data stored on blockchain networks or crypto wallets.
A key feature of Web3 is the use of smart contracts—self-executing contracts that automatically enforce agreements without the need for intermediaries. These self executing contracts power many Web3 services, from decentralized finance (DeFi) platforms that facilitate financial transactions without banks, to decentralized autonomous organizations (DAOs) that enable community governance and democratic decision-making. Moreover, Web3 supports digital assets such as non fungible tokens (NFTs), which give users verifiable ownership over digital art, collectibles, and virtual goods in the virtual world.
By allowing users to own data and assets directly through private keys, Web3 shifts the internet from a model where data resides on centralized platforms to one where data is distributed and controlled by individual users. This transition to a decentralized internet offers the promise of greater privacy, security, and economic empowerment.
The Evolution: From Web1 to the Semantic Web and Web3
To fully appreciate the potential of Web3, it helps to review the internet’s evolution through its previous phases.
The first generation, Web1, dominated the 1990s and early 2000s. It consisted mainly of static webpages—simple, read-only sites where users could consume information but had little ability to interact or contribute content. These early websites were essentially digital brochures, with limited user engagement or personalization.
The current era, Web2.0, introduced dynamic, interactive platforms driven by user generated content. Social media platforms like Facebook, Twitter, and YouTube empowered users to create and share content, fueling the rise of online communities and social networks. As the web became more complex and interactive, the search engine became an essential tool for users to navigate and find information across these platforms. However, this era also solidified a centralized infrastructure where centralized platforms own and control user data. While users produce content, they do not own their digital identity or the customer data generated from their interactions. Instead, this data is stored on centralized servers controlled by centralized entities, which monetize it primarily through targeted advertising.
This centralized control model has led to significant security risks such as frequent data breaches, privacy violations, and the concentration of power in a few big tech companies. Additionally, users face limited data portability and little ability to monetize their contributions or participate in platform governance.
Web3 aims to address these issues by creating a decentralized web ecosystem where users have more control over their data and digital experiences. By leveraging decentralized technologies and blockchain technology, Web3 introduces new economic models that reward users for their participation and enable user ownership of digital assets, identities, and content.
Key Technologies Powering Web3: Blockchain Technology
Several key technologies underpin the Web3 revolution, each designed to overcome the limitations of the centralized model that dominates today’s internet.
First and foremost, blockchain networks provide the decentralized backbone of Web3. These networks distribute data across multiple locations or nodes, ensuring that no single entity controls the information. This structure enhances security and transparency, as data on the blockchain is immutable and verifiable by anyone. Different blockchain platforms offer unique features—Ethereum is widely used for its ability to execute complex smart contracts, while newer blockchains like Solana prioritize speed and scalability.
Smart contracts are crucial to Web3’s functionality. These are programmable, self executing contracts that automatically enforce the terms of an agreement without intermediaries. A smart contract acts as a self-executing agreement that automates digital transactions or insurance payouts on the blockchain, removing the need for intermediaries and enabling trustless processes in DeFi and decentralized insurance applications. They enable a wide range of applications, from defi platforms that facilitate lending, borrowing, and trading without banks, to decentralized autonomous organizations (DAOs) that allow token holders to govern protocols democratically.
Another important technology is cryptocurrency tokens, which serve as the economic units within Web3. Beyond acting as mediums of exchange, tokens can represent ownership stakes, voting rights, or access to services within decentralized platforms. This tokenization supports new economic models where users can earn rewards, participate in governance, and benefit financially from their contributions.
To avoid reliance on centralized servers, Web3 also utilizes decentralized storage solutions such as the InterPlanetary File System (IPFS). These systems store data across a distributed network of nodes, increasing resilience and reducing censorship risks. This approach contrasts sharply with centralized platforms where user data and digital interactions are stored in single data centers vulnerable to outages or attacks.
Finally, advancements in artificial intelligence, including machine learning and natural language processing, are expected to enhance Web3 by enabling a more intuitive and semantic web experience. This will allow web browsers and search engines to better understand and respond to user intent, further improving seamless connectivity and personalized interactions.
Decentralized Autonomous Organizations (DAOs)
Decentralized Autonomous Organizations (DAOs) are transforming how groups coordinate and make decisions in the digital world. Unlike traditional organizations, which rely on a central authority or management team, DAOs operate on a blockchain network using smart contracts to automate processes and enforce rules. This decentralized structure distributes decision-making power among all members, allowing for transparent and democratic governance.
DAOs are at the heart of many Web3 innovations, powering decentralized finance (DeFi) protocols, social media platforms, and digital art collectives. For example, in DeFi, DAOs enable token holders to propose and vote on changes to financial products, ensuring that the community has greater control over the direction of the platform. In the world of digital art, DAOs can manage shared collections or fund creative projects, with every transaction and decision recorded on the blockchain for full transparency.
By leveraging blockchain technology and smart contracts, DAOs provide a secure and efficient way to manage digital assets and coordinate online interactions. This approach eliminates the need for a single central authority, reducing the risk of censorship or unilateral decision-making. As a result, DAOs empower users to participate directly in governance, shaping the future of decentralized platforms and giving communities unprecedented influence over their digital experiences.
Digital Identity in the Web3 Era
The concept of digital identity is being redefined in the Web3 era, as decentralized networks and blockchain technology give individuals more control over their online identities. Traditional systems often require users to entrust their personal information to big tech companies, where data resides on centralized servers and is vulnerable to misuse or breaches. In contrast, Web3 introduces decentralized identity management, allowing users to store and manage their own data securely across a blockchain network.
With decentralized technologies, users can decide exactly who can access their information, enhancing privacy and security. This shift not only protects personal data but also enables seamless participation in online communities without relying on centralized entities. Non fungible tokens (NFTs) and other digital assets further enrich digital identity, allowing users to represent themselves in unique, verifiable ways—whether through digital art, avatars, or credentials.
Ultimately, Web3’s approach to digital identity puts more control in the hands of individual users, fostering trust and enabling more meaningful digital interactions. As online identities become more portable and secure, users can engage with a wide range of platforms and services while maintaining ownership and privacy over their personal information.
Practical Applications: Web3 in Action
Web3 is no longer just a concept; it is actively reshaping multiple industries and digital experiences.
One of the most developed sectors is decentralized finance (DeFi), where traditional banking services are replaced by blockchain-based protocols. Users can lend, borrow, trade, and earn interest on their cryptocurrency holdings without intermediaries. These defi platforms operate transparently using smart contracts, reducing costs and expanding access to financial services globally.
Another groundbreaking application is the rise of non fungible tokens (NFTs), which have transformed digital art and collectibles by enabling verifiable ownership and provenance on the blockchain. NFTs extend beyond art to include gaming assets, domain names, and even tokenized real-world assets, unlocking new possibilities for creators and collectors.
Decentralized Autonomous Organizations (DAOs) exemplify Web3’s potential for community governance. DAOs allow members to collectively make decisions about project direction, fund allocation, and protocol upgrades through token-weighted voting. This democratic approach contrasts with the centralized control of traditional institutions and platforms.
Gaming is another promising frontier, with play-to-earn models allowing players to earn cryptocurrency and own in-game assets. This integration of digital assets and economic incentives is creating new opportunities, particularly in regions with limited traditional job markets.
Moreover, Web3 supports a broader decentralized web vision where users can store data securely, interact through decentralized apps, and maintain control over their digital identity and online identities. This shift promises to reduce reliance on centralized infrastructure, mitigate security risks, and foster a more open, user-centric digital landscape.
Safety and Security in Web3
As Web3 continues to evolve, safety and security remain top priorities for both users and developers. The decentralized nature of blockchain technology and smart contracts offers robust protection for digital assets and financial transactions, as every action is recorded on an immutable ledger. This transparency helps prevent fraud and unauthorized changes, making decentralized applications (dApps) inherently more secure than many traditional systems.
However, the shift to a decentralized model also introduces new security risks. Vulnerabilities in smart contracts can be exploited by malicious actors, and phishing attacks targeting users’ private keys can lead to significant losses. Unlike centralized platforms, where a central authority might recover lost funds, Web3 users are responsible for safeguarding their own assets and credentials.
To navigate these challenges, users should adopt best practices such as using hardware wallets, enabling two-factor authentication, and staying vigilant against scams. Meanwhile, DeFi platforms and other Web3 projects must prioritize rigorous security audits and transparent communication about potential risks. By fostering a culture of security and shared responsibility, the Web3 community can build a safer environment where users interact confidently and digital assets are protected.
Current Limitations and Challenges
Despite its transformative potential, Web3 faces several key challenges that currently hinder widespread adoption.
Scalability is a major concern. Many blockchain networks suffer from slow transaction speeds and high fees during peak demand, making some Web3 applications expensive and less user-friendly. Although innovations like layer-2 scaling solutions and new consensus algorithms are addressing these issues, they remain a barrier for many users.
The user experience of Web3 platforms also needs improvement. Managing private keys, understanding gas fees, and navigating complex interfaces can be intimidating for newcomers accustomed to the simplicity of Web2 applications. This steep learning curve slows mainstream adoption.
Regulatory uncertainty adds another layer of complexity. Governments worldwide are still formulating approaches to cryptocurrencies, decentralized finance, and digital asset ownership. This uncertainty can deter institutional investment and complicate compliance for developers.
Environmental concerns, particularly around energy-intensive proof-of-work blockchains, have drawn criticism. However, the industry is rapidly transitioning to more sustainable models like proof-of-stake, which significantly reduce energy consumption.
Overcoming these technical challenges and improving accessibility will be critical for Web3 to fulfill its promise of a truly decentralized internet.
Investment and Trading Opportunities
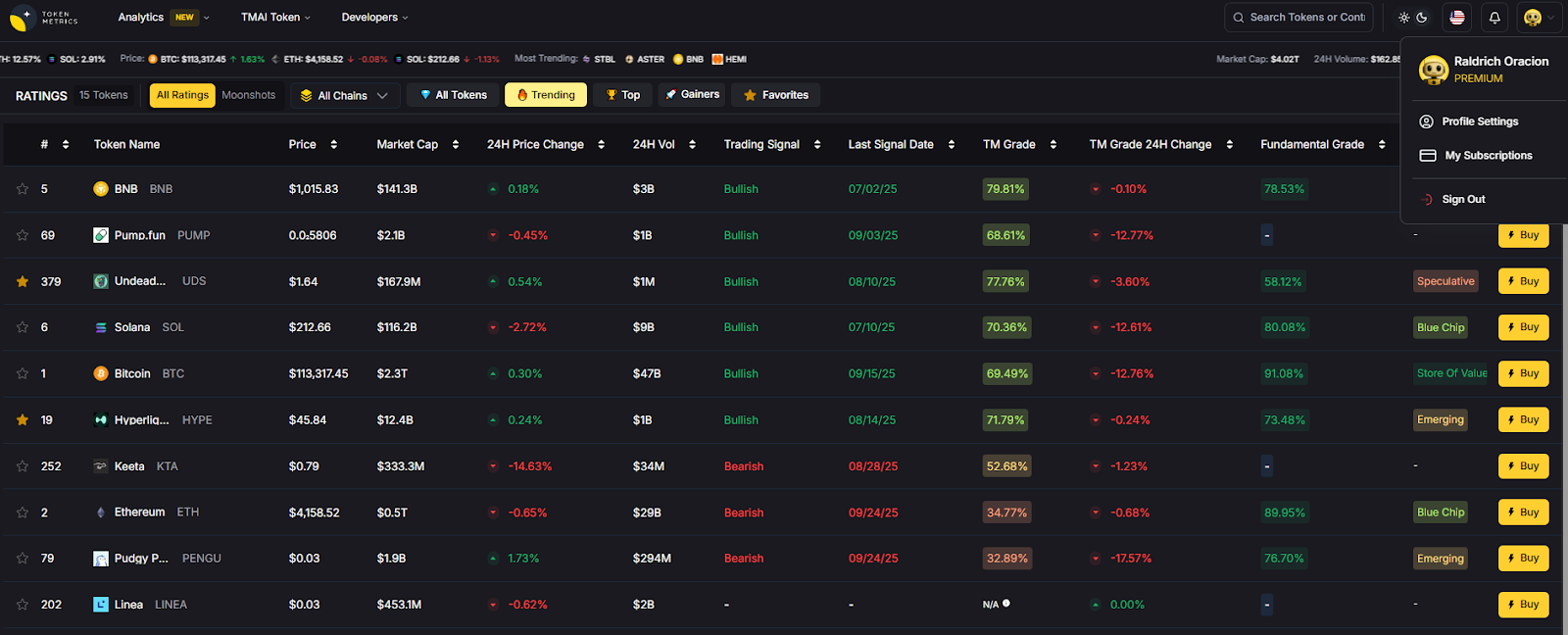
The rise of Web3 is creating exciting investment and trading opportunities across various sectors of the digital economy. From tokens that power blockchain networks to governance tokens in defi platforms and DAOs, investors can participate in the growth of this decentralized ecosystem.
Platforms like Token Metrics provide valuable analytics and insights into Web3 projects, helping investors evaluate token performance, project fundamentals, and market trends. With the Web3 economy evolving rapidly, data-driven tools are essential for navigating this complex landscape and identifying promising opportunities.
Web3 and Society: Social Implications and Opportunities
Web3 is not just a technological shift—it’s a catalyst for profound social change. Decentralized social media platforms are empowering users to create, share, and monetize content without the oversight of centralized authorities, promoting greater freedom of expression and more diverse online communities. By removing intermediaries, these platforms give users a direct stake in the networks they help build.
Blockchain technology and decentralized finance (DeFi) are also unlocking new economic models, making it possible for individuals around the world to access financial services and participate in the digital economy. This democratization of opportunity can drive financial inclusion, especially in regions underserved by traditional banking systems.
The rise of virtual worlds and collaborative online communities further expands the possibilities for social interaction, creativity, and economic participation. However, the decentralized nature of Web3 also presents challenges, such as ensuring effective governance, navigating regulatory landscapes, and promoting social responsibility. Ongoing dialogue and collaboration among stakeholders will be essential to maximize the benefits of Web3 while addressing its complexities, ensuring that the new digital landscape is open, fair, and inclusive for all.
Web3 and the Environment: Sustainability and Impact
The environmental impact of Web3 is a growing concern, particularly as blockchain technology and decentralized applications become more widespread. Early blockchain networks, especially those using proof-of-work consensus mechanisms, have faced criticism for their high energy consumption and associated carbon footprint. This has prompted calls for more sustainable approaches within the Web3 ecosystem.
In response, many projects are adopting energy-efficient consensus algorithms, such as proof-of-stake, which significantly reduce the resources required to maintain blockchain networks. Additionally, the integration of renewable energy sources and the development of decentralized applications focused on sustainability—like tokenized carbon credits and decentralized renewable energy markets—are paving the way for greener economic models.
By prioritizing environmental responsibility and embracing innovative solutions, the Web3 community can minimize its ecological impact while continuing to drive technological progress. Ongoing research, collaboration, and a commitment to sustainability will be crucial in ensuring that the benefits of decentralized technology are realized without compromising the health of our planet.
The Road Ahead: Web3's Future Impact
The future of Web3 depends on overcoming current limitations while staying true to its core principles of decentralization, user ownership, and transparency. As infrastructure matures and user experience improves, Web3 applications could become as seamless and accessible as today's social media platforms and web browsers, but with far greater control and privacy for users.
The transition will likely be gradual, with Web2 and Web3 coexisting for some time. Certain functions may remain centralized for efficiency, while others benefit from the decentralized model’s unique advantages. Ultimately, Web3 represents a major shift toward a more open, user driven internet where individual users can participate fully in the digital economy, govern online communities democratically, and truly own their data and digital lives.
Understanding what is web3 and how is it different from the current internet is not just about technology—it’s about preparing for a new digital era where decentralized technologies reshape how the internet operates and who controls its future. Those who embrace this change will be well-positioned to thrive in the emerging decentralized web ecosystem.

.svg)

Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)












.svg)




.png)