
What's the Safest Way to Store Large Crypto Holdings? A 2025 Security Guide

As cryptocurrency portfolios grow in value, understanding what’s the safest way to store large crypto holdings becomes a critical concern for investors. In 2024 alone, over $2.2 billion was stolen through various crypto hacks and scams, highlighting the vulnerabilities in digital asset protection. These incidents reveal the significant risks associated with storing large amounts of cryptocurrency, including potential vulnerabilities and hazards that can lead to loss or theft. Recent high-profile incidents, such as Coinbase’s May 2025 cyberattack that exposed customer information, underscore the urgent need for robust crypto security measures and the importance of following the safest ways to protect your assets. Unlike traditional bank accounts that benefit from FDIC insurance and fraud protection, stolen cryptocurrency cannot be refunded or insured through conventional means. This reality makes choosing the right cryptocurrency storage method to store your cryptocurrency essential for anyone holding significant crypto assets.
Understanding the Storage Landscape: Hot vs. Cold
When it comes to crypto storage, the fundamental distinction lies in whether wallets are connected to the internet. There are different types of crypto wallets, each offering unique benefits and security features. Hot wallets are always online, making them convenient for trading, transactions, and quick access to funds. However, their constant internet connection makes them inherently vulnerable to hacking, phishing, and malware attacks. Examples include mobile, desktop, and web-based wallets, which are often used for daily spending or quick access to tokens.
On the other hand, cold wallets—also known as cold storage—store private keys completely offline. This means they are disconnected from the internet, drastically reducing the risk of remote attacks. Cold wallets are ideal for long term storage of large crypto assets, where security takes precedence over convenience. A custodial wallet is another option, where a third-party provider, such as an exchange, manages and holds your private keys on your behalf, offering convenience but less direct control compared to non-custodial wallets.
Think of hot wallets as your checking account: convenient but not meant for holding large sums. Cold wallets function like a safety deposit box, providing secure storage for assets you don’t need to access frequently. Crypto wallets use a public key as an address to receive funds, while the private key is used to sign transactions. For large holdings, experts recommend a tiered approach: keep only small amounts in hot wallets for active use, while storing the majority in cold storage. This balances security, access, and the risk of funds being compromised. Cold wallets keep private keys offline and store your private keys and digital assets securely, reducing the risk of theft.
Hardware Wallets: The Gold Standard for Individual Investors
Among cold storage options, hardware wallets are widely regarded as the safest and most practical solution for individual investors managing large cryptocurrency holdings. These physical devices, often resembling USB drives, securely store your private keys offline and only connect to the internet briefly when signing transactions.
Leading hardware wallets in 2025 include the Ledger Nano X, Ledger Flex, and Trezor Model Safe 5. These devices use secure element chips—the same technology found in credit cards and passports—to safeguard keys even if the hardware is physically compromised. By keeping private keys offline, hardware wallets protect your assets from malware, hacking, and remote theft.
To maximize safety when using hardware wallets, always purchase devices directly from manufacturers like Ledger or Trezor to avoid tampered products. When you create your wallet, securely generate and store your seed phrase or recovery phrase by writing it on paper or metal backup solutions. Another option is a paper wallet, which is a physical printout of your private and public keys, used as a form of cold storage for cryptocurrencies. Store these backups in multiple secure locations such as fireproof safes or safety deposit boxes. For example, you might keep one copy of your paper wallet or backup phrase in a home safe and another in a bank safety deposit box to reduce the risk of loss. Never store recovery phrases digitally or photograph them, as this increases the risk of theft.
Enable all available security features, including PIN protection and optional passphrases, for an extra layer of encryption. For very large holdings, consider distributing assets across multiple hardware wallets from different manufacturers to eliminate single points of failure. The main limitation of hardware wallets is their physical vulnerability: if lost or destroyed without proper backup, your funds become irretrievable, making diligent backup practices essential.
Multi-Signature Wallets: Distributed Control for Enhanced Security
For even greater protection, especially among families, businesses, and institutional investors, multi-signature (multisig) wallets provide distributed control over funds. Unlike traditional wallets that require a single private key to authorize transactions, multisig wallets require multiple keys to sign off, reducing the risk of theft or loss.
A common configuration is a 2-of-3 setup, where any two of three keys are needed to sign a transaction. In this setup, the concept of 'two keys' is fundamental—two keys must be provided to authorize and access the funds. This means that funds can only be accessed when the required number of keys are available, ensuring both redundancy and security. If one key is lost, the other two can still access funds—while maintaining strong security since an attacker would need to compromise multiple keys simultaneously. More complex configurations like 3-of-5 are common for very large holdings, allowing keys to be geographically distributed to further safeguard assets.
Popular multisig wallet providers in 2025 include BitGo, which supports over 1,100 digital assets and offers insurance coverage up to $250 million for funds stored. BitGo’s wallets combine hot and cold storage with multisig security, meeting regulatory standards for institutional clients. Other notable solutions include Gnosis Safe (now known as Safe) for Ethereum and EVM-compatible chains, and Unchained, which manages over 100,000 Bitcoin using 2-of-3 multisig vaults tailored for Bitcoin holders. While multisig wallets require more technical setup and can slow transaction processing due to the need for multiple signatures, their enhanced security makes them ideal for large holdings where protection outweighs convenience.
Multi-Party Computation: The Emerging Institutional Standard
An innovative advancement in crypto storage is Multi-Party Computation (MPC) technology, rapidly becoming the standard for institutional custody. Unlike multisig wallets where multiple full private keys exist, MPC splits a single private key into encrypted shares distributed among several parties. The full key never exists in one place—not during creation, storage, or signing—greatly reducing the risk of theft.
MPC offers advantages over traditional multisig: it works seamlessly across all blockchains, transactions appear identical to regular ones on-chain enhancing privacy, and it avoids coordination delays common in multisig setups. Leading MPC custody providers like Fireblocks have demonstrated the security benefits of this approach. However, Fireblocks also revealed vulnerabilities in competing threshold signature wallets in 2022, highlighting the importance of ongoing security audits in this evolving field.
For individual investors, MPC-based wallets like Zengo provide keyless security without requiring a seed phrase, distributing key management across secure locations. Nevertheless, MPC solutions are primarily adopted by institutions, with firms like BitGo, Fireblocks, and Copper offering comprehensive custody services for family offices and corporations.
Institutional Custody Solutions: When Professional Management Makes Sense
For extremely large holdings—often in the millions of dollars—professional institutional custody services offer unparalleled security infrastructure, insurance coverage, and regulatory compliance. These platforms typically facilitate not only secure storage but also the buying and selling of crypto assets as part of their comprehensive service offerings. Institutional custody solutions are commonly used to store bitcoin and other major cryptocurrencies securely, protecting them from theft, loss, and unauthorized access.
Regulated custodians implement multiple layers of protection. They undergo regular third-party audits and SOC certifications to verify their security controls. Many maintain extensive insurance policies covering both hot and cold storage breaches, sometimes with coverage reaching hundreds of millions of dollars. Professional key management minimizes user errors, and 24/7 security monitoring detects and responds to threats in real-time.
Despite these advantages, institutional custody carries counterparty risk. The Coinbase cyberattack in May 2025, which exposed customer personal information (though not passwords or private keys), served as a reminder that even the most secure platforms can be vulnerable. Similarly, the collapse of platforms like FTX, Celsius, and BlockFi revealed that custodial services can fail catastrophically, sometimes taking customer funds with them.
Therefore, thorough due diligence is essential when selecting institutional custodians. Verify their regulatory licenses, audit reports, insurance coverage, and operational history before entrusting significant funds.
The Critical Role of Analytics in Secure Portfolio Management
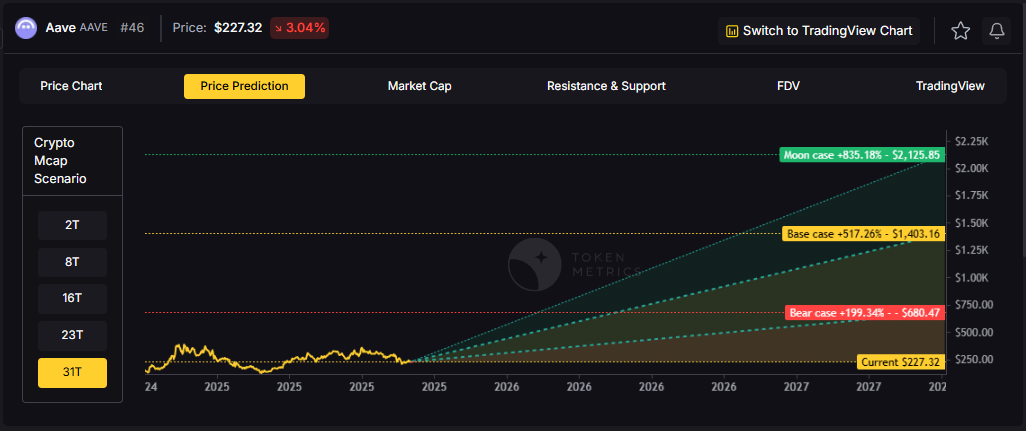
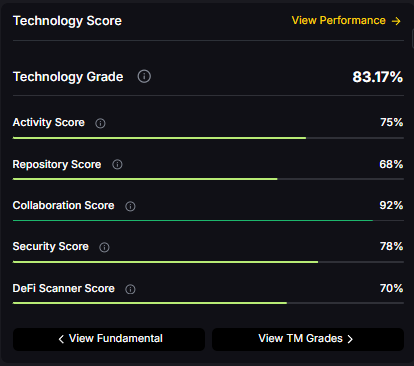
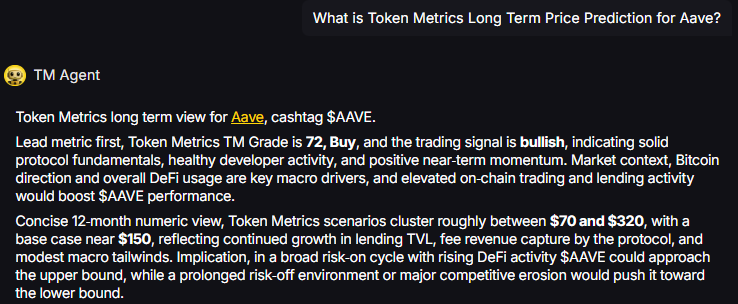
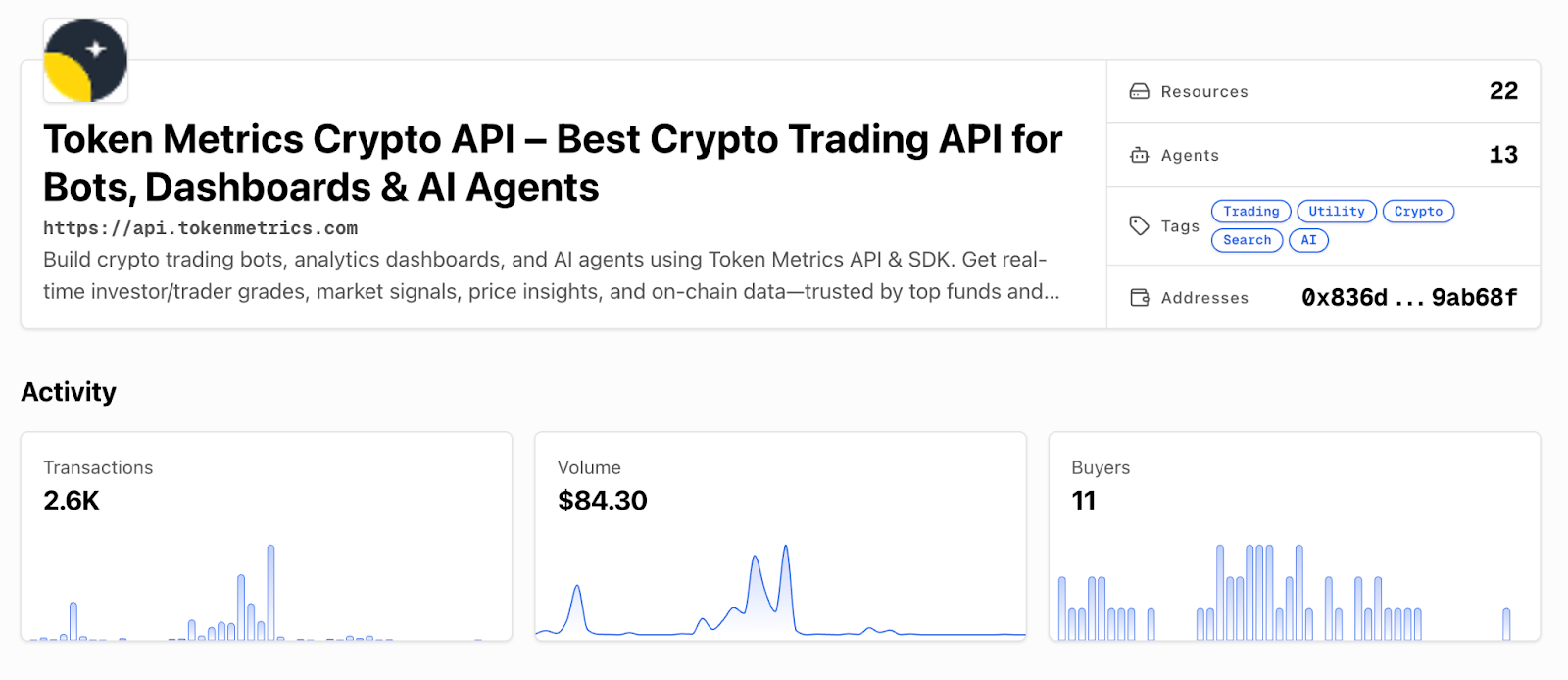
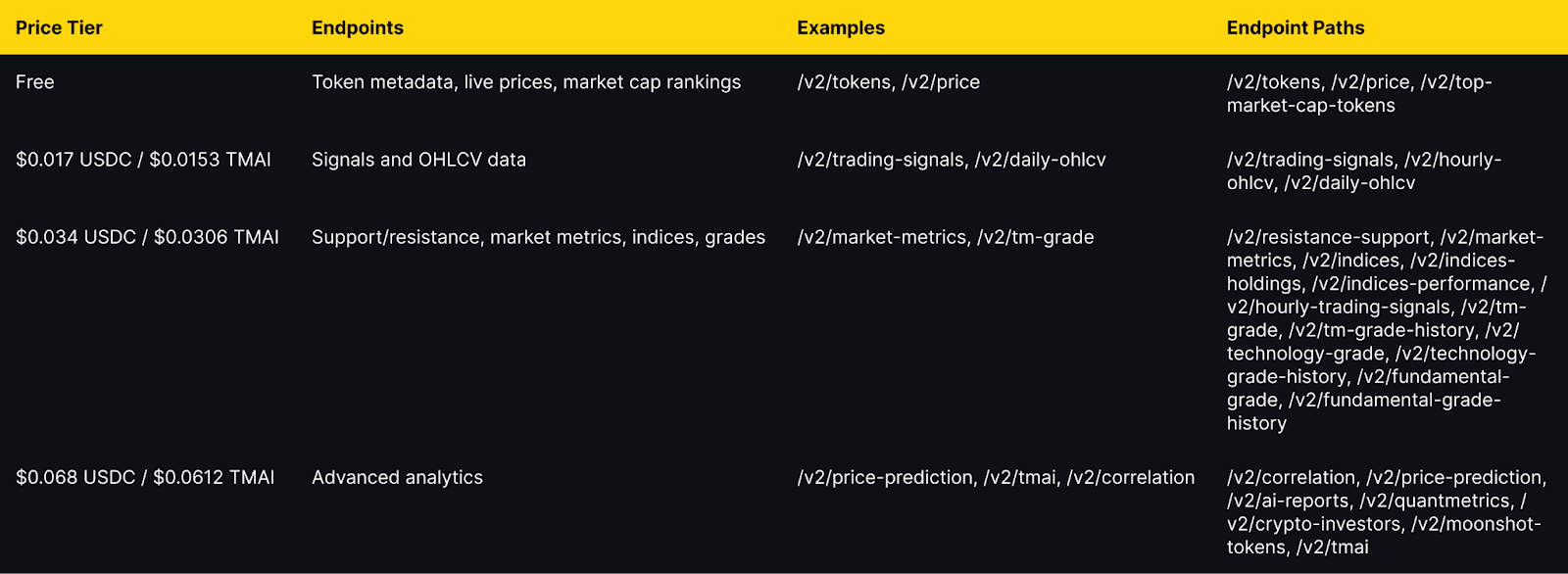
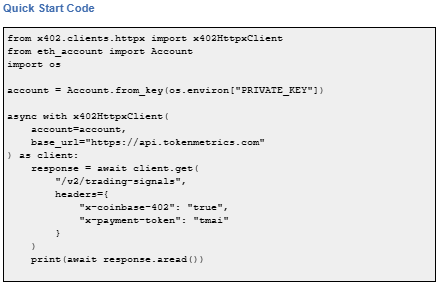
Securing large crypto holdings is not just about storage—it also involves smart portfolio management and timely decision-making. Sophisticated analytics platforms have become essential tools for this purpose. Token Metrics stands out as a leading AI-powered crypto trading and analytics platform designed to help users manage large cryptocurrency portfolios effectively. While hardware wallets and multisig solutions protect your keys, Token Metrics provides real-time market intelligence across hundreds of cryptocurrencies, enabling holders to make informed decisions about when to move assets between hot wallets and cold storage. The platform also assists users in determining the optimal times to buy crypto as part of their overall portfolio management strategy, ensuring that purchases align with market trends and security considerations.
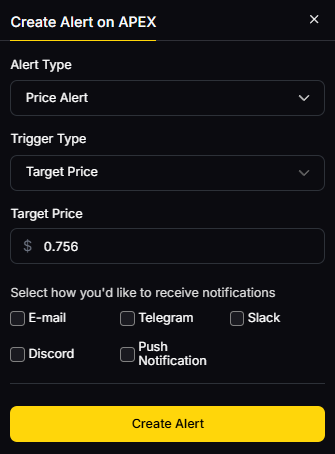
The platform’s AI-driven analysis helps investors identify market conditions that warrant moving assets out of cold storage to capitalize on trading opportunities or to secure profits by returning funds to cold wallets. This strategic timing can significantly enhance portfolio performance without compromising security. Token Metrics also offers customizable risk alerts, allowing holders to respond quickly to significant market movements without constant monitoring. Since launching integrated trading capabilities in March 2025, the platform provides an end-to-end solution connecting research, analysis, and execution. This is especially valuable for users managing hot wallets for active trading while keeping the bulk of their crypto assets securely stored offline. With AI-managed indices, portfolio rebalancing recommendations, and detailed token grades assessing both short-term and long-term potential, Token Metrics equips large holders with the analytical infrastructure necessary to safeguard and optimize their holdings.
Essential Security Practices Beyond Storage Technology
Even the most secure storage methods can fail without proper security hygiene. Regardless of your chosen storage solution, certain best practices are essential:
- Never share your private keys or recovery phrases with anyone. Legitimate services will never ask for this information. Requests for keys are always scams.
- Enable two-factor authentication (2FA) on all accounts using authenticator apps or hardware security keys (e.g., YubiKey) rather than SMS-based 2FA, which is vulnerable to SIM-swap attacks.
- Use a password manager to generate and store unique, complex passwords for every exchange and wallet service, avoiding password reuse.
- Whitelist withdrawal addresses on exchanges to restrict withdrawals to pre-approved addresses, reducing the risk of unauthorized transfers.
- Verify transaction addresses carefully before confirming. Malware can alter clipboard contents to replace legitimate addresses with attacker-controlled ones. Manually check the first and last characters.
- Keep all software updated on devices used for managing crypto, as updates often include critical security patches.
- Plan for inheritance and incapacity by securely documenting custody arrangements, key locations, and access procedures. Consider specialized services for cryptocurrency estate planning.
Backup and Recovery: Safeguarding Access to Your Assets
When it comes to crypto storage, having a robust backup and recovery plan is just as essential as choosing the right wallet. No matter how secure your hardware wallet, hot wallet, or cold wallet may be, losing access to your private keys or recovery phrase can mean losing your crypto assets forever. That’s why safeguarding your ability to restore access is a cornerstone of crypto security.
For users of hardware wallets like the Ledger Nano or Trezor Model, the most critical step is to securely record your recovery phrase (also known as a seed phrase) when you first set up your device. This unique string of words is the master key to your wallet—if your hardware wallet is lost, stolen, or damaged, the recovery phrase allows you to restore your funds on a new device. Write your seed phrase down on paper or, for even greater protection, use a metal backup solution designed to withstand fire and water damage. Never store your recovery phrase digitally, such as in a note-taking app or cloud storage, as these methods are vulnerable to hacking and malware.
It’s best practice to store your backup in a location separate from your hardware wallet—think a safe deposit box, a home safe, or another secure, private spot. For added security, consider splitting your backup between multiple locations or trusted individuals, especially if you’re managing significant crypto assets. This way, even if one location is compromised, your funds remain protected.
Non-custodial wallets, whether hardware or software-based, give you full control over your private keys and, by extension, your crypto. With this control comes responsibility: if you lose your recovery phrase or private key, there’s no customer support or password reset to help you regain access. That’s why diligent backup practices are non-negotiable for anyone serious about storing bitcoin or other digital assets securely.
For those seeking even greater protection, multi-signature wallets add another layer of security. By requiring multiple keys to authorize transactions, multi-signature setups make it much harder for hackers or thieves to access your funds—even if one key or device is lost or compromised. This method is especially valuable for families, businesses, or anyone managing large holdings who wants to reduce single points of failure.
If you ever suspect your wallet or recovery phrase has been compromised, act immediately: transfer your funds to a new wallet with a freshly generated seed phrase, and update your backup procedures. Similarly, if a hot wallet on your mobile device or desktop is hacked, move your assets to a secure cold wallet as quickly as possible. Ultimately, backup and recovery are not just technical steps—they’re your safety net. Whether you use hardware wallets, hot wallets, cold wallets, or even paper wallets, always create and securely store a backup of your recovery phrase. Regularly review your backup strategy, and make sure trusted individuals know how to access your assets in case of emergency. By taking these precautions, you ensure that your crypto assets remain safe, secure, and accessible—no matter what happens.
Implementing a Comprehensive Storage Strategy
For large cryptocurrency holdings, a multi-layered storage strategy offers the best balance of security and accessibility. A common approach for portfolios exceeding six figures includes:
- Tier 1: Deep Cold Storage (70-80%) – Use hardware wallets or multisig vaults for long-term holdings. These assets remain untouched except for major portfolio moves. Backup phrases and devices should be stored in geographically dispersed, secure locations.
- Tier 2: Accessible Cold Storage (15-20%) – Maintain a secondary hardware wallet or multisig setup for intermediate-term positions, accessible within hours but still offline.
- Tier 3: Hot Wallet for Active Trading (5-10%) – Keep a small portion of funds in exchange accounts or software wallets for daily transactions and trading, accepting higher risk for liquidity.
This tiered framework ensures that even if one layer is compromised, the entire portfolio remains protected. Combined with platforms like Token Metrics for market intelligence and risk management, this strategy offers both security and operational flexibility.
The Bottom Line
In 2025, securing large cryptocurrency holdings requires a deep understanding of various storage technologies and the implementation of layered security strategies. Hardware wallets remain the gold standard for individual investors, while multisig wallets and MPC solutions provide enhanced protection for very large or institutional holdings.
There is no one-size-fits-all answer to what's the safest way to store large crypto holdings. The ideal approach depends on factors like portfolio size, technical skill, transaction frequency, and risk tolerance. Most large holders benefit from distributing assets across multiple storage methods, keeping the majority in cold storage and a smaller portion accessible for trading.
Ultimately, cryptocurrency security hinges on effective private key management. Protecting these keys from unauthorized access while ensuring you can access them when needed is paramount. By combining robust storage solutions, disciplined security practices, and advanced analytics tools like Token Metrics, investors can safeguard their crypto assets effectively while maintaining the flexibility to seize market opportunities.
As the cryptocurrency landscape evolves, so will storage technologies. Stay informed, regularly review your security setup, and never become complacent. In the world of digital assets, your security is your responsibility—and with large holdings, that responsibility is more essential than ever.

.svg)

Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)

















.svg)




.png)