
XDC Price Prediction 2025, 2030 - Forecast Analysis
.png)
Click here to buy Cryptocurrencies from Gate.io
Contact us at promo@tokenmetrics.com for marketing and sponsorship programs.
Cryptocurrency investors are always on the lookout for promising projects that have the potential to deliver significant returns.
One such project is XDC Network (XDC), a hybrid blockchain that aims to revolutionize the trade and finance sectors globally.
In this article, we will explore the XDC price prediction for 2025 and 2030, exploring the factors that may influence its future growth and evaluating whether XDC is a good investment.
XDC Network Overview
Before diving into the price prediction, let's first understand what XDC Network is all about. Launched in March 2017, XDC Network is an enterprise-ready blockchain combining the best public and private blockchains.
It offers a decentralized infrastructure solution that enhances efficiency, removes intermediaries, and increases system transparency. Headquartered in Singapore, XDC Network was founded by Karan Bharadwaj, Atul Khekade, and Ritesh Kakkad.
With their expertise and vision, XDC Network has overcome numerous obstacles in the global trading and financial space, bringing together buyers, suppliers, financiers, trade unions, and banks on a peer-to-peer platform.
Historical Performance of XDC
To understand the future potential of XDC, it's crucial to analyze its historical performance. XDC Network has experienced significant fluctuations in its price since its inception.
In April 2018, the price of XDC reached its highest point at $0.0280, but it didn't sustain this upward momentum and fell to $0.0240.

By November 2018, XDC hit a peak of $0.011, only to drop to its support level of around $0.00067 in December 2018.
The bearish momentum continued until the beginning of 2020. However, XDC Network recovered and reached an all-time high of $0.1939 in August 2021.
Since then, the price of XDC has experienced some corrections and currently trades around $0.055. Despite the mixed trend, XDC Network holds the potential to recover and reach new highs in the upcoming years.
XDC Current Fundamentals
XDC Network's current fundamentals are crucial in determining its investment potential.

XDC has a market cap of $774,631,428 and a circulating supply of 13,875,309,131 XDC; the trading volume for XDC is around $4,231,293.
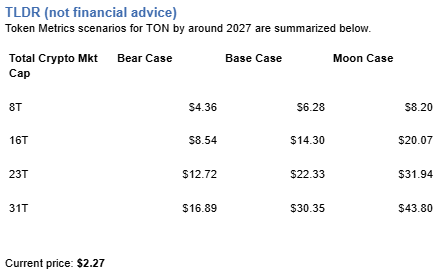
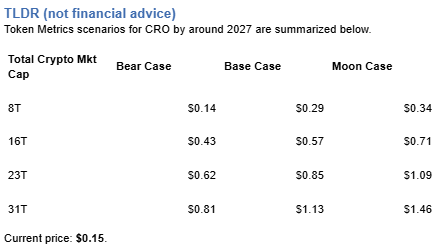
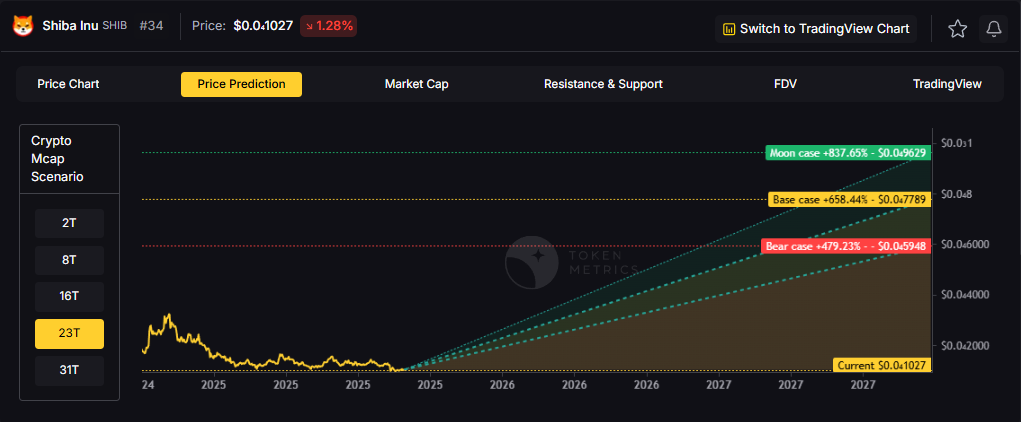
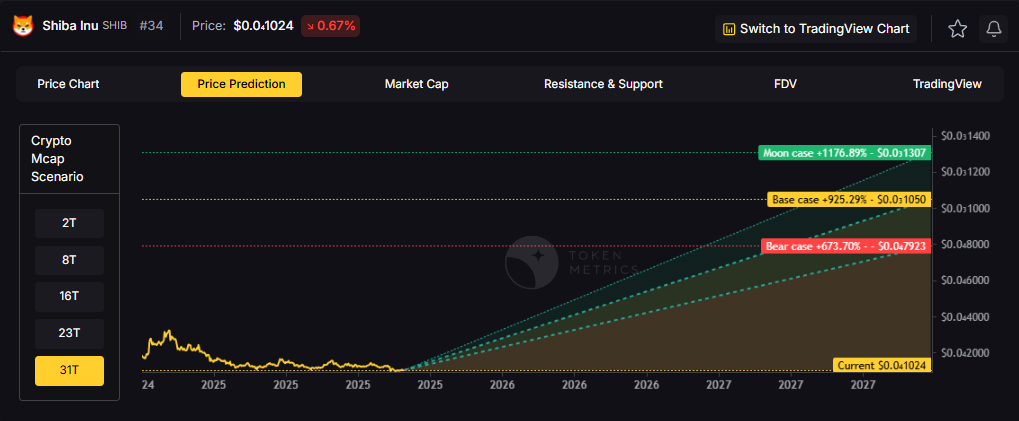
XDC Price Prediction: Scenario Analysis
To predict XDC's future price, it is imperative to consider various scenarios that may influence its value.
In this analysis, we will explore both a bullish and bearish scenario to offer a comprehensive outlook on XDC's potential price movements.
XDC Price Prediction - Bullish Scenario
In an optimistic market scenario where the total crypto market cap reaches $3 trillion and XDC maintains its current 0.05% market dominance, we could anticipate its price surging to $0.11.
In a more bullish projection, with the crypto market expanding to $10 trillion, XDC's value might skyrocket to an impressive $0.38, potentially yielding a 7x return for investors.

XDC Price Prediction - Bearish Scenario
Conversely, in a bearish setting characterized by unfavorable market conditions or intensified competition, XDC's price may face downward pressure, decreasing its market dominance to 0.026%.
In such circumstances, even if the total crypto market cap reaches $3 trillion, XDC could trade around $0.058 in the short term, struggling to surpass $0.19 by 2030, even if the total crypto market cap exceeds $10 trillion.
It's essential to emphasize that these scenarios are speculative in nature and should not be construed as financial advice. The cryptocurrency market is inherently volatile, and prices can exhibit rapid fluctuations.
Therefore, investors should exercise caution and conduct thorough research before making investment decisions.
Click here to buy Cryptocurrencies from Gate.io
Contact us at promo@tokenmetrics.com for marketing and sponsorship programs.
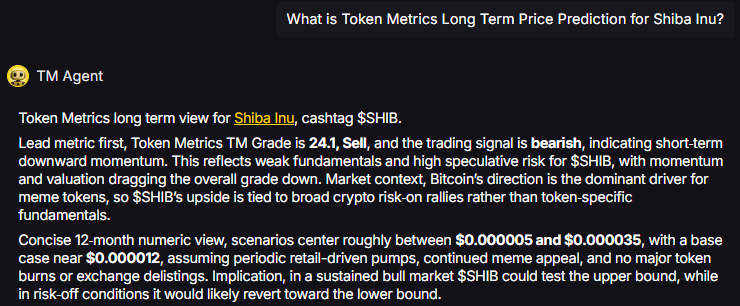
XDC Price Prediction: Industry Expert Opinion
To comprehensively analyze XDC's future potential, we gathered industry experts' insights and conducted in-depth research. Here are some expert opinions on the XDC price prediction for 2025:
- Coincodex.com: According to Coincodex.com XDC price prediction, the price of XDC crypto is expected to be somewhere between $ 0.057229 on the lower end and $ 0.208644 on the high end by the end of 2025, and price prediction for 2030 could be between $ 0.098399 on the lower end and $ 0.138895 on the high end.
- Ambcrypto.com: Ambcrypto predicts that the significant upgrades in the XDC Network ecosystem could attract more investors, potentially leading to a price of $0.13 to $0.2 by 2030.
- BitcoinWisdom: According to BitcoinWisdom's XDC coin price prediction for 2025, XDC could reach a price of $0.121731 if the upward trend continues. However, if the market experiences a decline, the target might not be met.
Based on these expert opinions, XDC Network can potentially deliver significant returns in the long term. However, as with any investment, conducting thorough research and considering the risks is crucial.
Note - Start Your Free Trial Today and Uncover Your Token's Price Prediction and Forecast on Token Metrics.
XDC Current Developments and Future Potential
XDC Network has been actively working on enhancing its ecosystem and expanding its partnerships. The project aims to provide user-friendly interaction and transparent transactions through its open-source DeFi protocol.
With the increasing adoption of blockchain technology in various industries, XDC Network can attract more users and investors.
Will XDC Hit $100?
No, considering the current fundamentals and market trends, reaching the $100 mark before 2030 is nearly impossible.
While it's difficult to predict the precise future price of any cryptocurrency, the likelihood of XDC hitting $100 in the foreseeable future is relatively low.
However, it's worth noting that the cryptocurrency market is highly volatile, and unexpected events can significantly impact prices.
Also Read - XRP Price Prediction
Conclusion
XDC Network (XDC) has shown promising growth potential, with industry experts predicting a bullish trajectory for its price in the coming years.
While XDC's historical performance and current fundamentals support a positive outlook, it is crucial to remember that investing in cryptocurrencies carries risks.
Conduct thorough research, assess your risk tolerance, and consult with a financial advisor before making any investment decisions.
Frequently Asked Questions
Q1. Is XDC a good investment in 2025?
Based on the market data and expert opinions, XDC has the potential to be a good investment in 2025. However, conducting thorough research and considering the risks is important before making investment decisions.
Q2. Where can I buy XDC crypto?
XDC is available on several reputable exchanges, including Bitfinex, KuCoin, Huobi, Bittrex, and Gate.io. Choosing a reliable crypto exchange for purchasing XDC is advisable.
Q3. What is the future potential of XDC Network?
XDC Network has a bright future with its hybrid blockchain architecture and focuses on enhancing trade and finance sectors. As blockchain technology continues to gain adoption, XDC Network has the potential to attract more users and investors, further driving its growth.
Q4. Is XDC Network a reliable project?
XDC Network has shown promising growth and has gained recognition in the industry. However, conducting thorough research and assessing the project's fundamentals, team, and partnerships is essential to determine its reliability.
Q5. How can I assess the risk tolerance for investing in XDC?
Assessing your risk tolerance involves considering your investment goals, financial situation, and willingness to accept potential losses. It is advisable to consult with a financial advisor to determine an appropriate risk tolerance level for your investment portfolio.
Q6. What factors can impact the price of XDC?
Several factors can impact the price of XDC, including market sentiment, overall cryptocurrency market conditions, regulatory developments, technological advancements, and adoption rates. It's important to stay informed about these factors and their potential impact on the project.
Disclaimer
The information provided on this website does not constitute investment advice, financial advice, trading advice, or any other advice, and you should not treat any of the website's content as such.
Token Metrics does not recommend that any cryptocurrency should be bought, sold, or held by you. Conduct your due diligence and consult your financial advisor before making investment decisions.
Click here to buy Cryptocurrencies from Gate.io
Contact us at promo@tokenmetrics.com for marketing and sponsorship programs.

.svg)

Create Your Free Token Metrics Account

.png)




%201.svg)
%201.svg)


%201.svg)




















.svg)




.png)