Top Crypto Trading Platforms in 2025







%201.svg)
%201.svg)
Big news: We’re cranking up the heat on AI-driven crypto analytics with the launch of the Token Metrics API and our official SDK (Software Development Kit). This isn’t just an upgrade – it's a quantum leap, giving traders, hedge funds, developers, and institutions direct access to cutting-edge market intelligence, trading signals, and predictive analytics.
Crypto markets move fast, and having real-time, AI-powered insights can be the difference between catching the next big trend or getting left behind. Until now, traders and quants have been wrestling with scattered data, delayed reporting, and a lack of truly predictive analytics. Not anymore.
The Token Metrics API delivers 32+ high-performance endpoints packed with powerful AI-driven insights right into your lap, including:
Getting started with the Token Metrics API is simple:
At Token Metrics, we believe data should be decentralized, predictive, and actionable.
The Token Metrics API & SDK bring next-gen AI-powered crypto intelligence to anyone looking to trade smarter, build better, and stay ahead of the curve. With our official SDK, developers can plug these insights into their own trading bots, dashboards, and research tools – no need to reinvent the wheel.
%201.svg)
%201.svg)
DeepSeek API has emerged as a specialized toolkit for developers and researchers who need granular, semantically rich access to crypto-related documents, on-chain data, and developer content. This article breaks down how the DeepSeek API works, common integration patterns, practical research workflows, and how AI-driven platforms can complement its capabilities without making investment recommendations.
The DeepSeek API is designed to index and retrieve contextual information across heterogeneous sources: whitepapers, GitHub repos, forum threads, on-chain events, and more. Unlike keyword-only search, DeepSeek focuses on semantic matching—returning results that align with the intent of a query rather than only literal token matches.
Key capabilities typically include:
Integrating the DeepSeek API into a product follows common design patterns depending on latency and scale requirements:
When building integrations, consider privacy, data retention, and whether you need to host a private index versus relying on a hosted DeepSeek endpoint.
Researchers using the DeepSeek API can follow a repeatable workflow to ensure comprehensive coverage and defensible results:
For reproducible experiments, version your query templates and save query-result sets alongside analysis notes.
Understanding the constraints of a semantic retrieval API is essential for reliable outputs:
Build Smarter Crypto Apps & AI Agents with Token Metrics
Token Metrics provides real-time prices, trading signals, and on-chain insights all from one powerful API. Grab a Free API Key
DeepSeek typically indexes a mix of developer-centric and community data: GitHub, whitepapers, documentation sites, forums, and on-chain events. Exact coverage depends on the provider's ingestion pipeline and configuration options you choose when provisioning indexes.
Embeddings map text into vector space where semantic similarity becomes measurable as geometric closeness. This allows queries to match documents by meaning rather than shared keywords, improving recall for paraphrased or conceptually related content.
While DeepSeek is optimized for textual retrieval, many deployments support linking to structured on-chain records. A common pattern is to return document results with associated on-chain references (contract addresses, event IDs) so downstream systems can fetch transaction-level details from block explorers or node APIs.
Use a combination of automated metrics (precision@k, recall sampling) and human review. For technical subjects, validate excerpts against source code, transaction logs, and authoritative docs to avoid false positives driven by surface-level similarity.
Keep retrieved context concise and relevant: prioritize high-salience chunks, include provenance for factual checks, and use retrieval augmentation to ground model outputs. Also, monitor token usage and prefer compressed summaries for long sources.
DeepSeek is focused on semantic retrieval and contextual search, while other crypto APIs may prioritize raw market data, on-chain metrics, or analytics dashboards. Combining DeepSeek-style search with specialized APIs (for price, on-chain metrics, or signals) yields richer tooling for research workflows.
Explore provider docs and example use cases. For integrated AI research and ratings, see Token Metrics which demonstrates how semantic retrieval can be paired with model-driven analysis for structured insights.
This article is for informational and technical education only. It does not constitute investment advice, endorsements, or recommendations. Evaluate tools and data sources critically and consider legal and compliance requirements before deployment.
%201.svg)
%201.svg)
Fabric API is a cornerstone for developers building permissioned blockchain solutions with Hyperledger Fabric. This article explains what Fabric APIs are, how they fit into Fabric's architecture, practical integration patterns, and how to evaluate tooling when you need reliable programmatic access to Fabric networks.
The term "Fabric API" broadly refers to the programmatic interfaces and SDKs that allow applications to interact with a Hyperledger Fabric network. These interfaces expose capabilities such as submitting transactions, querying ledger state, managing identities via Fabric CA, and deploying or invoking chaincode (smart contracts). For enterprise use cases—supply chain auditing, tokenized assets, or confidential data flows—the Fabric API is the gateway between business logic and the distributed ledger.
Key characteristics of Fabric APIs include:
Interacting with Fabric typically involves several layers. Understanding these helps you choose the right API surface for your application:
Choosing how to surface Fabric functionality depends on risk, latency, and operational model. Common patterns include:
Cross-cutting concerns to design for:
Follow a structured approach when integrating with Fabric networks:
Testing tips: use channel-level mock data, replay recorded endorsement responses for deterministic unit tests, and simulate peer failures to validate client retry logic.
Build Smarter Crypto Apps & AI Agents with Token Metrics
Token Metrics provides real-time prices, trading signals, and on-chain insights all from one powerful API. Grab a Free API Key
The Fabric API comprises SDKs, the Gateway API, chaincode interfaces, and CA endpoints that let applications manage identities, submit transactions, and query ledger state on Hyperledger Fabric networks.
Use the Gateway API for simpler, high-level transaction workflows and reduced configuration. Choose direct SDKs when you need low-level control over discovery, endorsement policies, or custom peer selection logic.
Yes. Implement a secure REST proxy or API gateway to translate HTTP calls to Fabric SDK operations. This adds flexibility for web/mobile clients but requires careful identity and input validation.
Use Fabric CA for certificate issuance, adopt hardware-backed key stores where possible, separate admin and app roles, and rotate/revoke certificates according to policy. Avoid embedding private keys in client-side code.
Instrument SDK calls, capture latency and endorsement statistics, log chaincode events, and integrate with observability stacks (Prometheus/Grafana). Monitor peer health and orderer topology to correlate API issues with network state.
Common issues include endorsement mismatches due to non-deterministic chaincode, exposing credentials to clients, insufficient testing of policy changes, and lacking observability for transaction failures.
Disclaimer: This article is educational and technical in nature. It does not provide financial, legal, or regulatory advice. Implementations should be validated against your organization's compliance and security requirements.
%201.svg)
%201.svg)
REST APIs are the connective tissue of modern web and mobile applications. Whether you're integrating services, building microservices, or exposing data for AI agents, a clear grasp of REST API principles helps you design interfaces that are maintainable, performant, and secure. This guide walks through the core concepts, practical design patterns, authentication and security considerations, and tooling that make REST APIs reliable in production.
REST (Representational State Transfer) is an architectural style that uses standard HTTP verbs and status codes to manipulate resources. Key tenets include:
Understanding these principles helps when choosing between REST, GraphQL, or RPC for a given use case. REST is well-suited for CRUD-style operations, caching, and wide compatibility with HTTP tooling.
Good API design starts with modeling resources and their relationships. Practical patterns include:
Design with backward compatibility in mind: deprecate endpoints with clear timelines, and prefer additive changes over breaking ones.
Security is non-negotiable. Common, interoperable mechanisms include:
Also consider CORS policies, input validation, and strict output encoding to reduce injection risks. Implement principle of least privilege for every endpoint and role.
Operational maturity requires monitoring and testing across the lifecycle. Focus on these areas:
Tooling choices—Postman, Insomnia, Swagger UI, or automated CI checks—help maintain quality as the API evolves. For AI-driven integrations, exposing well-documented JSON schemas and stable endpoints is critical.
Build Smarter Crypto Apps & AI Agents with Token Metrics
Token Metrics provides real-time prices, trading signals, and on-chain insights all from one powerful API. Grab a Free API Key
REST is ideal for resource-oriented services where standard HTTP semantics are beneficial. Choose REST when caching, simplicity, wide client compatibility, and predictable CRUD semantics are priorities. For highly dynamic queries, consider GraphQL as a complement rather than a replacement.
Version endpoints, use feature flags, and publish changelogs with migration guides. Prefer additive changes (new fields, new endpoints) and give clients time to migrate before removing legacy behavior.
Match the method to the use case: API keys for server-to-server integrations, OAuth 2.0 for delegated user access, and JWTs for stateless session claims. Always layer these with TLS and short token lifetimes.
Enforce per-key and per-IP limits, surface quota headers, and provide graceful 429 responses with a Retry-After header. Use adaptive throttling to protect critical downstream systems.
Adopt OpenAPI for specs, use Postman or Swagger UI for exploratory testing, integrate contract tests into CI, and deploy observability stacks (Prometheus, Grafana, OpenTelemetry) to monitor behavior in production.
This article is for educational and technical guidance only. It does not constitute legal, security, or operational advice. Evaluate risks and compliance requirements against your own environment before implementing changes.

%201.svg)
%201.svg)
The cryptocurrency landscape is as diverse as it is vast. As an investor, your primary concern is likely the security of your assets. To that end, hardware wallets, like the Trezor, have garnered substantial attention.
In this detailed review, we will delve into the Trezor wallet product, discussing its features, fees, and suggesting some worthy alternatives. By the end, you should have a clearer sense of whether Trezor is the right fit for your crypto storage needs.
Trezor, a pioneer in the hardware wallet industry, offers a cold storage solution that keeps your cryptocurrencies offline and away from potential online threats.
Hailing from SatoshiLabs, Trezor has a reputation for providing top-tier security, ensuring your crypto assets remain safe and accessible.
Superior Security
Intuitive Interface - Trezor Suite, the accompanying software, offers a clean, user-friendly interface, perfect for both beginners and experienced users.
Multi-Currency Support - Trezor supports over 1,000 coins, including prominent ones like BTC, ETH, and LTC.
Open Source - With its open-source nature, the tech community can constantly inspect Trezor's software, ensuring transparency and trustworthiness.
Navigating the world of cryptocurrency with Trezor Wallet involves a series of steps that prioritize security and ease-of-use. Here's a step-by-step guide on its operation:
1. Initialization - Start by connecting your Trezor device to a computer or mobile device using the provided USB cable. For first-time users, the device will prompt you to initialize it, creating a new wallet or recovering an existing one.
2. Set up a PIN - Once initialized, you'll be prompted to create a secure PIN. This PIN acts as the first line of defense, preventing unauthorized access to your wallet.
3. Backup Your Wallet - During the setup process, Trezor will generate a unique 12-24 word recovery seed for you. It's imperative to write this down and store it securely. This seed is your safety net; if you ever lose or damage your Trezor, this seed will help you recover your assets on a new device.
4. Installing Firmware - Ensure that your Trezor's firmware is up to date. The device will often prompt you to install or update the firmware upon connection. This step ensures that you're protected with the latest security patches and supports the newest coin integrations.
5. Transaction Management - Once set up, you can start sending and receiving cryptocurrencies. Using the Trezor Suite or compatible wallet software, you can initiate transactions. For added security, every transaction made requires manual confirmation on the Trezor device itself.
6. Safe Storage - When not in use, it's advisable to disconnect and store your Trezor in a safe location. Since it's a cold storage solution, your assets remain safe offline, away from potential online breaches.
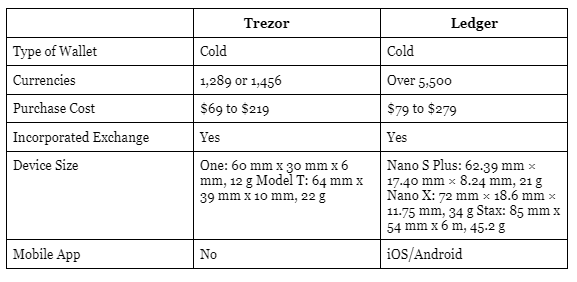
The Trezor Model T is priced around $219, in contrast to Ledger's similar model, which is available for $149 and has the capacity to hold up to 5,500 distinct cryptocurrencies. Meanwhile, Trezor's Model One is around $69, aligning closely with the cost of Ledger's most equivalent offering.
While Trezor itself doesn’t charge a fee for transactions, it’s crucial to understand that transferring cryptocurrencies always incurs network fees.
These vary based on the respective blockchain's congestion. Trezor’s software provides an adjustable fee setting, allowing you to decide how much you’re willing to pay for a transaction and how fast you want it processed.
Check more details here.
Trezor places a high emphasis on delivering comprehensive customer support to its users. On their official website, a detailed support section awaits users, packed with an extensive array of tutorials, FAQs, and insightful articles.
These resources are complemented by valuable input from the community, offering real-world experiences and solutions. Additionally, Trezor's dedicated blog serves as a hub of up-to-date information and industry insights.
For those active on social platforms, Trezor maintains a dynamic presence, ensuring users stay informed and engaged. If personal assistance is required, users can directly reach out to the Trezor support team through email or their efficient ticketing system.
When navigating the crypto-sphere, understanding the strengths and limitations of the tools you employ is crucial. The Trezor Wallet, celebrated for its robust security mechanisms, is no exception. Here's a closer look at its pros and cons.
Pros
1. Robust Security - Being a hardware wallet, Trezor operates offline, vastly reducing the risks associated with online hacks and breaches.
2. Multi-Currency Support - Trezor Model One supports 1289
Coins & Tokens including all ERC-20 and Trezor Model T support 1456 Coins & Tokens (Bitcoin, Litecoin, Ethereum (+all ERC-20) and more.
3. Transparent Operations - Trezor’s open-source software means its operations are transparent, allowing for rigorous community scrutiny.
4. User-Friendly Interface - The Trezor Suite, designed for intuitive use, ensures that both crypto-novices and veterans can navigate with ease.
5. Recovery Features - The wallet's recovery seed feature is a safeguard against potential device loss, ensuring users can always retrieve their assets.
Cons
1. Price - Hardware wallets like Trezor can be more expensive than some software or online wallet options.
2. Physical Vulnerability - While digital threats are reduced, the physical device can be lost, damaged, or stolen (though the recovery seed mitigates this risk to an extent).
3. Limited Mobile Interface - Unlike some competitors, Trezor might not be as seamless in mobile integration, potentially limiting on-the-go operations.
4. Learning Curve - For absolute beginners, there might be a slight learning curve in understanding the functionalities of a hardware wallet compared to simpler online wallets.
Also Read - Trezor vs Ledger - Which Crypto Wallet is Better?
While Trezor is undeniably an industry leader, it’s always helpful to know your options. Here are three top alternatives to consider:
Security: Ledger is another heavyweight in the hardware wallet sphere, offering top-tier security.
Bluetooth Feature: Unlike Trezor, the Nano X offers Bluetooth capabilities, allowing wireless connections.
Support: Ledger supports over 1,200 cryptocurrencies.
Check more details here.
Design: A more luxurious and robust design compared to Trezor.
Security: KeepKey provides similar cold storage solutions, ensuring your assets remain safe offline.
Integration: Seamless integration with both the Shapeshift platform and the Ledger Live software.
Q1. Is Trezor Wallet immune to computer viruses?
While the Trezor device itself is designed to be secure and can operate safely even on compromised computers, it's always recommended to ensure your computer is virus-free to maintain overall digital hygiene.
Q2. Can I use my Trezor Wallet on multiple computers?
Yes, the Trezor Wallet is portable and can be used on multiple computers. Just ensure you have the necessary software or browser extensions installed on each computer.
Q3. What happens if SatoshiLabs, the company behind Trezor, goes out of business?
Your funds remain safe. Trezor is an open-source device, which means its software isn't reliant on SatoshiLabs. Even if the company discontinues its services, you can still access and manage your funds.
Q4. Are there any ongoing fees associated with using a Trezor Wallet?
No, once you purchase the Trezor Wallet, there are no mandatory ongoing fees for using it. However, standard transaction fees on respective blockchains will still apply.
Q5. Can I use Trezor Wallet for staking or earning rewards on my crypto?
Trezor, by default, is a hardware wallet focused on storage. However, using third-party interfaces, certain cryptocurrencies might be staked. Always refer to official guides before attempting staking with your device.
Q6. How does Trezor compare in terms of durability? Is it waterproof or heat-resistant?
While Trezor is built to be robust, it's not waterproof or explicitly heat-resistant. It's advised to keep the device in a safe, dry environment away from extreme temperatures.
Q7. Can I manage my DeFi assets and tokens using Trezor?
Yes, with integration to platforms like MetaMask or MyEtherWallet, you can manage your Ethereum-based DeFi tokens securely through Trezor.
Q8. What if I forget my PIN or lose my recovery seed for Trezor?
The PIN ensures the security of your device, and the recovery seed is crucial for restoring your funds if the device is lost. If both are misplaced, it becomes extremely challenging to access your assets. Always store your recovery seed securely and avoid forgetting your PIN.
The world of cryptocurrencies demands robust security, and Trezor certainly meets this criterion. Its intuitive interface, broad coin support, and reputation make it a solid choice for many. However, your unique needs might lead you to consider alternatives like Ledger or KeepKey.
If you prioritize having a plethora of coins, Trezor or Ledger might be more your speed. If a premium design appeals to you, KeepKey might catch your eye.
Remember, the goal is always to ensure your assets remain safe, accessible, and under your control. Take a moment to assess your priorities, research further, and choose the wallet that aligns best with your crypto journey.
The information provided on this website does not constitute investment advice, financial advice, trading advice, or any other sort of advice and you should not treat any of the website's content as such.
Token Metrics does not recommend that any cryptocurrency should be bought, sold, or held by you. Do conduct your own due diligence and consult your financial advisor before making any investment decisions.

%201.svg)
%201.svg)
In the ever-evolving world of cryptocurrency, staying updated with the latest standards and technologies is imperative. One such development that has gained traction is the adoption of the ISO 20022 messaging standard.
In this comprehensive guide, we'll dive deep into what ISO 20022 coins are, their significance, and how they're revolutionizing crypto space.
Definition - ISO 20022 is a global messaging standard adopted by the financial world. It's not just limited to crypto but extends to other financial transactions, including payments, securities, trade services, cards, and foreign exchange. Its goal is to create a universal standard for exchanging financial messages.
Importance in the Financial Ecosystem - By promoting a singular messaging standard, ISO 20022 simplifies global business communication. It reduces errors, lowers operational costs, and promotes seamless integration among different financial systems worldwide.
Bridging the Traditional and Digital Worlds - ISO 20022 acts as a bridge between traditional banking and the digital currency world. By integrating this standard, cryptocurrencies can be more widely recognized and accepted by mainstream financial institutions, fostering mutual growth.
Ensuring Data Richness - The messaging standard carries detailed information about transactions, ensuring more transparency and facilitating better compliance with regulations. This is especially critical in the crypto space, often viewed as a 'wild west' of finance.
The intricate world of ISO 20022 coins stems from their integration of the ISO 20022 messaging standard, a globally accepted protocol for transmitting financial information.
But how does this integration manifest itself in the operation of these coins? At its core, ISO 20022 is a comprehensive and versatile framework that uses structured and descriptive messages.
When cryptocurrencies incorporate this standard, they essentially remodel their transactional messaging to be in sync with this universally recognized protocol.
This means that every transaction carried out with an ISO 20022 compliant coin is embedded with rich data, encompassing not just the fundamental details like sender, receiver, and amount, but also metadata about the transaction itself.
The structured nature of these messages significantly minimizes ambiguities and errors. In practical terms, when you're transacting with an ISO 20022 coin, whether you're sending, receiving, or just verifying a transaction, the underlying technology ensures a clearer, more standardized, and detail-rich information flow.
This doesn't just make the transaction more transparent; it also facilitates easier integration and communication with traditional financial systems that already employ the ISO 20022 standard.
Hence, these coins act as a bridge, melding the innovative realm of cryptocurrencies with the established world of mainstream finance, making cross-border transactions, trade finance, and global payments more seamless and efficient than ever before.
As of 2023, several cryptocurrencies have notably aligned themselves with the ISO 20022 standard, marking a significant step towards bridging traditional financial operations with the revolutionary world of digital assets:
XRP (XRP): Spearheading the ISO 20022 adoption, XRP, backed by the Ripple company, offers a digital payment protocol more than just a cryptocurrency.
It specializes in faster, cost-effective cross-border transactions, with its infrastructure designed to facilitate direct transfers between two parties in any form of currency, including other cryptos.
Quant (QNT): Quant's Overledger is renowned for its capability to interlink various blockchains, enabling them to operate harmoniously. By embracing ISO 20022, Quant further amplifies its commitment to connect diverse financial systems seamlessly and efficiently.
Algorand (ALGO): A public blockchain and cryptocurrency project, Algorand focuses on ensuring decentralized agreements and constructing new financial tools. Its adoption of ISO 20022 underscores its mission to maintain a transparent, secure, and speedy transaction system.
Stellar (XLM): Stellar's mission to connect banks, payment systems, and consumers seamlessly finds further strength with its ISO 20022 integration. It's optimized for quick transactions, making cross-border transfers affordable and straightforward.
Hedera HashGraph (HBAR): Distinct from a traditional blockchain, Hedera Hashgraph offers a distributed ledger technology, boasting high-grade security and speed. Their commitment to the ISO 20022 standard highlights their aim for broader financial collaboration and streamlined transactions.
IOTA (MIOTA): Rather than a blockchain, IOTA employs a directed acyclic graph called Tangle to manage its transactions. The ISO 20022 compliance attests to IOTA's dedication to evolve and sync with the globally accepted financial standards, amplifying its suitability for microtransactions and IoT implementations.
XDC Network (XDC): This enterprise-ready hybrid blockchain solution, specifically designed for Trade and Finance, optimally aligns with the ISO 20022 standard. XDC stands out in terms of interoperability, efficiency, and ease of integration into legacy systems, making it a prime choice for global finance operations.
Navigating the vast cryptocurrency market for sound investments often hinges on spotting trends anchored in real-world utility. ISO 20022 compliant coins, given their alignment with a global financial messaging standard, inherently possess a competitive edge.
Their integration with this standard signifies a commitment to transparency, interoperability, and regulatory compliance. For investors, this can translate to a higher degree of trust and potential for mainstream adoption.
While all investments come with risks, the strategic position of ISO 20022 coins in bridging traditional finance with digital assets makes them a compelling consideration for a diversified crypto portfolio.
As we move further into the digital age, the adoption of universal standards like ISO 20022 becomes increasingly important. This trend suggests a brighter future for compliant coins, with the potential for wider mainstream acceptance and more robust investment opportunities.
Already, we're seeing financial institutions, payment providers, and regulatory bodies taking interest in these coins, signaling their growing relevance.
As more sectors of the financial world adopt the ISO 20022 standard, these cryptocurrencies could become the go-to options for transactions that require speed, transparency, and a high degree of compatibility with existing financial systems.
Enhanced Interoperability - These coins can communicate effortlessly with banks and other financial entities using the same standard, eliminating potential barriers.
Advanced Compliance - With detailed transaction information, it becomes easier for these coins to adhere to regulatory standards, instilling more trust among investors and institutions.
Cost-Efficiency - A universal standard cuts down on transaction discrepancies, reducing the cost of resolving such issues and ensuring smooth operations.
Integration Overhead - Adapting to ISO 20022 can be cumbersome for some projects, given the need to overhaul existing systems.
Rapidly Evolving Crypto Landscape - While ISO 20022 is a robust standard, the world of crypto is ever-changing. Coins must ensure that this adoption doesn't stifle innovation or flexibility.
Q1. What triggered the need for a standard like ISO 20022 in cryptocurrencies?
While cryptocurrencies are revolutionary, their acceptance and integration into the broader financial system require standardized communication. ISO 20022 provides this standard, ensuring smooth, error-free transactions with traditional financial entities.
Q2. How does ISO 20022 impact cross-border transactions?
ISO 20022 streamlines and simplifies cross-border transactions, ensuring they're faster, more transparent, and compatible with varying regional financial systems.
Q3. Does ISO 20022 compliance mean a cryptocurrency is more secure?
While ISO 20022 enhances transaction clarity and standardization, it doesn't necessarily correlate with heightened security. Each cryptocurrency's security is based on its underlying technology and protocol.
Q4. How does ISO 20022 influence transaction fees?
By standardizing transaction messaging, ISO 20022 can potentially reduce errors and discrepancies, which might lead to reduced costs. However, transaction fees are also influenced by other factors, such as network congestion.
Q5. Will more cryptocurrencies adopt ISO 20022 in the future?
Given the standard's growing importance in the financial world, it's likely that more cryptocurrencies will consider ISO 20022 adoption to increase interoperability and acceptance among traditional financial institutions.
Q6. How can I check if a cryptocurrency is ISO 20022 compliant?
Usually, cryptocurrency projects that adopt ISO 20022 will announce it through their official channels. Investors can check the project's whitepaper, official website, or community forums for such information.
Q7. Are there any drawbacks for cryptocurrencies adopting ISO 20022?
While the standard brings many benefits, adoption might mean a significant overhaul of existing systems for some cryptocurrencies. This can be resource-intensive and may temporarily divert focus from other developmental priorities.
Q8. Can ISO 20022 adoption influence a cryptocurrency's price?
Market sentiment is influenced by various factors, including adoption of global standards. While ISO 20022 compliance might be seen as a positive development, it's just one of many factors that can impact a coin's price.
In an ecosystem as dynamic as cryptocurrency, the adoption of ISO 20022 presents a seismic shift, setting a new benchmark for financial messaging standards.
By integrating this globally recognized standard, these coins are not just pioneering a new frontier of transparency and efficiency but are also forging a stronger alliance with the mainstream financial world.
Whether you're an investor or simply interested in the future of digital assets, ISO 20022 compliant coins warrant your attention.
Also remember, Cryptocurrencies exhibit significant volatility. Before committing to any investment decisions, it's crucial to conduct thorough research or seek guidance from a financial advisor.
The information provided on this website does not constitute investment advice, financial advice, trading advice, or any other sort of advice and you should not treat any of the website's content as such.
Token Metrics does not recommend that any cryptocurrency should be bought, sold, or held by you. Do conduct your own due diligence and consult your financial advisor before making any investment decisions.

%201.svg)
%201.svg)
In our recent exploration into the intricate world of cryptocurrencies, we had the privilege to engage with Ian Balina, the esteemed founder and CEO of Token Metrics. Ian's journey in the crypto space is both fascinating and insightful. It's not every day you come across someone who turned a modest $20,000 into a staggering $5 million in under a year.
Drawing from his rich tapestry of experiences, we delved into the promising prospects of the upcoming crypto bull run—and how investors can position themselves to capture altcoin moonshots before they take off.
The overarching sentiment from Ian is optimistic. Weighing historical patterns against the current market trends, he predicts Bitcoin could reach $150,000 by April 2024. This projection follows the well-known halving cycle. Historically, a bull market begins to unfold 15 to 16 months after a Bitcoin halving event—2024 may be no different.
However, while Bitcoin remains the bellwether of crypto, the real asymmetric opportunities lie elsewhere.
Ian emphasized a vital concept that Token Metrics has championed for years: moonshot investing.
A moonshot in crypto refers to a low-cap altcoin with explosive upside potential—projects that can deliver 10x, 50x, or even 100x returns if timed correctly. These tokens often go under the radar until it's too late. According to Ian, the real wealth in bull runs is made not by chasing Bitcoin late—but by identifying the next wave of moonshots early.
Token Metrics offers a powerful, AI-driven solution to do just that.
Token Metrics has built a dedicated Moonshots Ratings Page that uses over 80 data points and AI algorithms to surface promising low-cap tokens with strong fundamentals and favorable technical indicators.
Here's how to use the platform to find your next moonshot:
From the main dashboard of Token Metrics, navigate to the Ratings tab.
Inside the Ratings section, select the Moonshots filter at the top. This view isolates only the high-potential, low-cap tokens that are actively monitored by the AI.
Each moonshot token listing includes:
You can even view Past Moonshots to track how historical picks performed over 7–14 days.
Click on any token to explore its fundamentals, real-time chart, top holders, and AI insights. This helps you build conviction before taking a position.
You can even buy directly from the Moonshots tab using the integrated Swap Widget—fast, secure, and simple.
Ian drew a powerful analogy: crypto today is where the internet was in the 1990s—misunderstood, volatile, but bursting with promise. Timing, he says, is everything. Using indicators and chart patterns, Token Metrics helps investors avoid emotional decisions and act on data-driven moonshot opportunities.
Our discussion touched on inflation, monetary tightening, and recession fears. Ian highlighted how macroeconomic forces will shape crypto flows, especially toward hedge assets like Bitcoin. However, he stressed that moonshot altcoins often perform best during uncertainty, as investors seek outsized returns in overlooked areas.
A surprising insight from Ian was to follow developer activity as a leading signal. For example, chains like StarkNet, Solana, and Cosmos are seeing surges in dev adoption. This often foreshadows new project launches—and potential moonshots.
Notably, the Helium–Solana partnership, and Polygon's quiet accumulation phase, represent these narratives in action. Ian advises keeping tabs on platforms attracting both developers and users.
One of the most exciting innovations is Token Metrics GPT—a ChatGPT-style AI assistant trained on the platform's vast crypto database. You can ask it questions like “Which moonshots have gained the most since listing?” or “What are the top tokens under $50M market cap with bullish momentum?”
This isn’t just AI for fun—it’s AI for financial action.
As we navigate this promising era of digital assets, one thing is clear: tools like Token Metrics are no longer optional—they’re essential.
Whether you're a seasoned investor or a curious newcomer, moonshots represent one of the highest ROI opportunities in the crypto world. But timing and research are everything.
With insights from leaders like Ian Balina, AI-powered dashboards, and a clear moonshot strategy, you're better equipped than ever to capture the next 10x or even 100x move before the crowd catches on.
Disclaimer
The information provided on this website does not constitute investment advice, financial advice, trading advice, or any other sort of advice and you should not treat any of the website's content as such. Token Metrics does not recommend that any cryptocurrency should be bought, sold, or held by you. Do conduct your own due diligence and consult your financial advisor before making any investment decisions.
Would you like a downloadable PDF version of this article, or a landing page design based on it?

%201.svg)
%201.svg)
In the evolving world of cryptocurrency, investors and traders constantly seek out strategies to maximize their profits and minimize risks.
One tool that has risen in popularity to aid in this quest is the "crypto signal". But what exactly are these signals, and how can one effectively identify and utilize them? Dive in with us as we demystify crypto signals and provide you with actionable steps.
Definition - Crypto signals are trading suggestions or tips that advise either buying or selling a particular cryptocurrency at a specific price and time. These signals can come from manual research by seasoned experts, or they can be generated by automated algorithms and software based on certain indicators.
Purpose - Crypto signals serve to guide users in their trading decisions. They help traders identify potential buying or selling opportunities based on various factors such as market trends, data analysis, and historical information.
Expert Analysis - Some crypto signals are derived from the expertise of professional traders and analysts who spend significant time studying the market. They utilize both fundamental and technical analysis to predict potential market movements.
Automated Tools - With advancements in technology, several tools and software solutions have emerged that can generate crypto signals based on preset criteria, algorithms, or patterns. These tools often use a combination of indicators to produce these suggestions.
Recognizing a trustworthy crypto signal is crucial. Here's what to look out for -
Source Reputation - Always consider the reputation of the source providing the signal. Platforms or analysts with a proven track record tend to offer more reliable advice.
Transparency - Reputable signal providers often offer a rationale behind their suggestions, helping you understand their decision-making process.
Consistency - An effective crypto signal provider maintains consistency in their signal accuracy over time.
Feedback and Reviews - Checking out reviews and feedback from other users can give insights into the signal's reliability.
Avoiding 'Pump and Dump' Schemes’ - Be cautious of signals that promise unrealistically high returns. Such schemes artificially inflate the price of a cryptocurrency for personal benefit.
Must Read - Pump and Dump Schemes
In the vast digital ocean of cryptocurrency, pinpointing trustworthy crypto signals can be challenging. However, sources like Token Metrics have transformed the quest.
Token Metrics, leveraging advanced AI technology, offers Price Prediction and trend signals that stand out for their accuracy and foresight. Instead of wading through countless uncertain sources, investors can rely on Token Metrics' sophisticated AI-driven insights.
These predictions and signals are not only based on vast amounts of historical data but are continually refined to reflect the ever-changing market dynamics.
With such a robust tool, investors gain a competitive edge, making well-informed decisions in a tumultuous crypto landscape.
Do Your Research - While signals can provide a great starting point, always conduct your own research before making a trading decision.
Diversify - Avoid putting all your funds into a single signal. Diversifying your trades can help manage risks.
Stay Updated - The cryptocurrency market is highly dynamic. Make sure to stay updated with the latest news and trends that might influence your trading decisions.
Employ Stop Losses - To ensure you do not incur significant losses, always set a stop loss when following a crypto signal.
Their primary advantage is they offer timely insights, enabling traders to capitalize on potential market opportunities without incessant monitoring.
For beginners, signals demystify complex market patterns, providing a clearer roadmap for entry and exit points.
Advanced traders benefit from signals as supplemental data to their strategies, refining their decision-making process.
Automated signals, in particular, process vast datasets rapidly, delivering insights that manual analysis might overlook.
Furthermore, the inclusion of stop loss and take profit points in signals equips traders with a structured approach, helping manage risks and optimize potential returns, all while saving precious time and effort.
While crypto signals provide valuable guidance, they're not without risks. Firstly, no signal, regardless of its source, can guarantee 100% accuracy due to the volatile nature of the crypto market.
Relying solely on signals without personal research can lead to uninformed decisions. Additionally, some unscrupulous sources may propagate misleading signals to manipulate asset prices, commonly termed as 'pump and dump' schemes.
Furthermore, automated signals, despite their algorithmic precision, might miss out on real-world events that can impact the market.
Thus, while signals are beneficial tools, they should be combined with personal diligence, market awareness, and a clear understanding of one's risk tolerance for optimal trading outcomes.
Q1. What's the difference between manual and automated crypto signals?
Manual signals are derived from human analysis, considering both fundamental and technical factors. Automated signals, on the other hand, are generated by algorithms based on pre-defined criteria or patterns without human intervention.
Q2. Can I use crypto signals for long-term investments or just short-term trading?
While many crypto signals cater to short-term trading opportunities, some providers offer signals tailored for longer-term investments, highlighting broader market trends and potential long-term asset growth.
Q3. How often are crypto signals updated?
The frequency varies by provider. Some signals, especially automated ones, may update multiple times a day, while others, particularly manual analyses, might be less frequent.
Q4. Are there free crypto signal providers?
Yes, some platforms or individuals offer free signals. However, it's vital to assess their reliability, as quality might differ from paid services. Investors can also try Token Metrics free trial to use the platform.
Q5. How do I differentiate between legitimate and scam signal providers?
Always check the track record, user reviews, and transparency level of a provider. Avoid those promising unrealistically high returns or those without a clear rationale behind their signals.
Q6. Can crypto signals predict exact market movements?
No tool or expert can predict market movements with absolute certainty. Crypto signals provide informed suggestions based on analysis, but markets can be influenced by unforeseen events or news.
Q7. How can I integrate crypto signals into my existing trading strategy?
Crypto signals can serve as supplementary information. Cross-referencing signal data with your strategy can highlight alignment or discrepancies, allowing for refined decision-making.
Q8. Does market news impact the accuracy of crypto signals?
Absolutely. Major news or events can drastically shift market sentiment, potentially impacting the relevance of a signal. It's always advisable to stay updated with market news alongside using signals.
Crypto signals can be immensely beneficial tools in the toolkit of a cryptocurrency trader or investor. However, like all tools, their efficacy depends largely on their usage.
By understanding what these signals are, where they come from, and how to identify the reliable ones, you place yourself in a favorable position to make informed and strategic trading decisions.
The information provided on this website does not constitute investment advice, financial advice, trading advice, or any other sort of advice and you should not treat any of the website's content as such.
Token Metrics does not recommend that any cryptocurrency should be bought, sold, or held by you. Do conduct your own due diligence and consult your financial advisor before making any investment decisions.

%201.svg)
%201.svg)
The world of finance has always been a playground for innovation. From the gold standard to cryptocurrencies, each era has ushered in a transformative way of looking at money and transactions.
Now, in the digital age, there's a buzz about the Quantum Financial System (QFS). Let's dive into this fascinating topic and decipher how it works.
The Quantum Financial System, or QFS, is a proposed new-age financial system that leverages the unique capabilities of quantum computing.
Quantum computers use the principles of quantum mechanics, a branch of physics that describes the tiniest particles in our universe, to process massive amounts of data at speeds previously deemed impossible.
In simple words, the QFS represents a paradigm shift in the world of finance, aiming to integrate the groundbreaking capabilities of quantum computing into our monetary systems.
At its core, the QFS utilizes principles from quantum mechanics, particularly quantum entanglement and quantum cryptography, to create a financial system that offers unparalleled security and real-time transaction speeds.
Unlike traditional systems where data breaches and hacks are concerns, any interference in the QFS alters the quantum state of data, instantly signaling a security threat. Moreover, its decentralized nature mirrors that of blockchain, reducing the control any single entity might have.
As the QFS promises a transparent, speedy, and ultra-secure financial landscape, it's capturing the keen interest of industry insiders and stakeholders.
Security: One of the biggest selling points of the QFS is its unparalleled security. Thanks to quantum cryptography, it becomes near impossible for hackers to infiltrate the system.
Speed: With quantum computers, transactions are processed in real-time, eliminating the need for intermediaries and reducing transaction times.
Transparency: The system is believed to be fully transparent, ensuring all financial activities are visible, thus reducing corruption and fraudulent activities.
Decentralization: Just like blockchain technology, the QFS aims to operate in a decentralized manner, preventing any single entity from gaining full control over the system.
The QFS working process is relatively straightforward -
Quantum Entanglement: At the heart of QFS is the phenomenon called quantum entanglement. This allows particles to become interconnected and the state of one (like spin direction) can instantly influence the state of another, no matter the distance separating them. This plays a role in creating a secure and instant communication system in QFS.
Quantum Cryptography: Security in the QFS is reinforced by quantum cryptography. Any attempt to eavesdrop or intercept information changes the quantum state of the information, immediately alerting the system.
Integration with Existing Systems: It's expected that QFS would not operate in isolation. Instead, it will likely be integrated with current financial systems and blockchain technologies to ensure a seamless transition and interoperability.
With the rise of cryptocurrencies like Bitcoin and Ethereum, many speculate how they would fit into the QFS. Given the decentralized nature of both blockchain and QFS, there's potential for significant synergy.
Cryptocurrencies might benefit from the enhanced security features of the QFS, ensuring more robust protection against hacks and unauthorized transactions. The immense speed of quantum computing could also address some scalability issues faced by current blockchain networks.
Unparalleled Security - At the heart of the QFS is quantum cryptography. Unlike traditional systems, where breaches can go undetected, any unauthorized attempt to access QFS data immediately changes its quantum state, alerting the system. This intrinsic property makes infiltrations almost impossible.
Near-Instantaneous Transactions - Quantum entanglement, a phenomenon where particles become interconnected regardless of distance, is a foundation of the QFS. It ensures transactions occur in real-time, obliterating typical global financial delays.
Decentralized Framework - Drawing inspiration from blockchain, the QFS operates without a central authority. This decentralization ensures transparency and reduces the potential for undue influence or manipulation by any single entity.
Enhanced Transparency - Owing to its decentralized nature, all transactions within the QFS are visible, creating an open system that reduces the chances of fraudulent activities and fosters trust among its users.
Technological Maturity: Quantum computers are still in their infancy. While there's rapid progress, widespread application in sectors like finance might still be years away.
Implementation: The shift from traditional financial systems to a new, untested one will be massive. Regulatory, technological, and practical challenges will need to be addressed.
Public Trust: Just as with cryptocurrencies, gaining the public's trust to move away from traditional banks and systems they're familiar with will be an uphill battle.
The initiation of the Quantum Financial System (QFS) is a topic of intense speculation within the financial community. As of now, while quantum computing has made significant strides, it's still in developmental stages, and a full-fledged QFS remains on the horizon.
The transition from our current systems to QFS will require robust technological maturity, regulatory adjustments, and widespread trust.
Though exact timelines are uncertain, continuous advancements suggest that the next decade might witness substantial progress towards its implementation.
Investing in the Quantum Financial System (QFS) demands an informed and strategic approach due to its emerging nature. A key perspective to consider is the rising belief among investors that ISO 20022-compliant cryptocurrencies will be instrumental in the QFS framework.
As such, diversifying your portfolio to include these specific cryptocurrencies could provide potential market exposure to the QFS. Alongside this, it's beneficial to research and invest in companies leading in quantum computing and blockchain innovations.
Subscribing to credible financial news sources will highlight timely opportunities. Before making any commitments, engaging with financial advisors is essential to ensure your investments match your risk appetite and financial objectives in this evolving landscape.
The Quantum Financial System (QFS) is positioned at the crossroads of innovation and potential disruption in the financial sector.
With its promise of unmatched security through quantum cryptography and blazing transaction speeds owing to quantum mechanics, many view it as the inevitable future of finance.
Coupled with the integration of ISO 20022-compliant cryptocurrencies, the system embodies a blend of transparency and efficiency.
However, the full realization of QFS depends on technological advancements, regulatory adaptations, and public trust. The coming decade is poised to be transformative, with QFS potentially redefining the global financial landscape.
Also Read - Future of Crypto in the Next 5 Years
Q1. What differentiates the Quantum Financial System from traditional banking systems?
The QFS employs quantum computing principles for heightened security and real-time transactions, distinguishing it from conventional systems that rely on classical computing techniques.
Q2. Is the Quantum Financial System hack-proof?
While no system can claim absolute invulnerability, QFS's use of quantum cryptography makes unauthorized data breaches extremely challenging, as any interference immediately alters the system's quantum state.
Q3. How will the QFS impact everyday banking for consumers?
Once implemented, consumers can expect faster transaction speeds, increased security, and potentially lower fees due to the reduced need for intermediaries.
Q4. Are there any potential risks or downsides to the QFS?
Like any emerging technology, QFS will face teething issues, including potential technological limitations, the need for new regulations, and initial public skepticism.
Q5. Will QFS replace blockchain technology or work in tandem with it?
The QFS is inspired by blockchain's decentralization principles. While it can function independently, it's believed that both technologies can coexist and complement each other, especially in creating transparent financial systems.
Q6. How will international trade and cross-border transactions benefit from QFS?
QFS promises real-time global transactions without typical delays, making international trade more efficient and potentially reducing transaction costs.
Q7. What is ISO 20022, and why is it significant in the context of QFS?
ISO 20022 is a standardized messaging protocol for electronic data interchange between financial institutions. Its compliance in cryptocurrencies indicates a move towards creating a unified and efficient global financial communication system, aligning with the principles of QFS.
Q8. How can one prepare for the transition to the QFS?
Staying informed about advancements in quantum computing and blockchain, understanding ISO 20022-compliant cryptocurrencies, and seeking advice from financial experts can help individuals and businesses smoothly navigate the shift to QFS.
The Quantum Financial System is indeed a revolutionary concept, promising heightened security, swift transactions, and a level of transparency previously unimagined.
But, as with all innovations, it's essential to approach it with a critical mindset. Understanding its workings, potential, and challenges can help stakeholders make informed decisions.
As the financial world braces for yet another transformation, only time will tell if the QFS will redefine our economic landscape or remain an aspirational concept. For now, let's keep our ears to the ground, stay informed, and be ready to adapt to the ever-evolving world of finance.
The information provided on this website does not constitute investment advice, financial advice, trading advice, or any other sort of advice and you should not treat any of the website's content as such.
Token Metrics does not recommend that any cryptocurrency should be bought, sold, or held by you. Do conduct your own due diligence and consult your financial advisor before making any investment decisions.

%201.svg)
%201.svg)
The world of cryptocurrencies never ceases to surprise. Among its many players, Dogecoin, once considered a meme coin, has grown in stature, with its potential continuously debated by experts and enthusiasts alike.
As we traverse 2023, a burning question remains: Can Dogecoin hit the $1 mark? Let's dive deep and understand the current scenarios and future potential of Dogecoin to make an informed decision.
Dogecoin's Humble Beginnings - Created in December 2013 by Billy Markus and Jackson Palmer, Dogecoin started as a light-hearted joke, a riff on the popular "Doge" meme.
Its initial lack of seriousness ironically gave it attention, leading to rapid adoption within communities, especially for microtransactions and tipping online.
Price Movements - Over the last couple of years, Dogecoin (DOGE) has experienced massive surges. These were largely propelled by celebrity endorsements, community hype, and the broader acceptance of cryptos.
By 2021, its year-to-date gains had stunned the crypto community, hitting record highs. However, the trajectory has been volatile, with peaks followed by corrections.
Dogecoin Current Stats -
Current Price (As of Writing) - $0.0625
Market cap - $8.8B
Supply - 140.78B DOGE

Macro-economic Landscape - Given the global economic backdrop, characterized by inflation fears and increased institutional acceptance of cryptocurrencies, altcoins like Dogecoin have become attractive hedges and investment options.
Celebrity Endorsements - Notable figures, like Elon Musk, have played pivotal roles in driving Dogecoin's price. Their tweets, comments, or mere mentions can lead to significant market movements.
Community and Developer Activity - One of Dogecoin's most significant assets is its robust community. In 2023, a dedicated team began working on the coin's scalability and transaction efficiency, further embedding its utility in real-world applications.
Rumors on Dogecoin - Devotees of Dogecoin are eagerly anticipating the tech magnate's move to incorporate Dogecoin transactions into the prominent social media platform.
The prevailing theory among industry experts and enthusiasts is that such integration could significantly enhance Dogecoin's real-world applications.
By broadening its use cases in this way, it's expected to bolster demand, potentially leading to an upward momentum in its market price. Nevertheless, as of now, this anticipated development remains unrealized.
The prospect of Dogecoin hitting $1 is intriguing, especially when considering its vast circulating supply of 140 billion tokens. Reaching this price would catapult Dogecoin to a staggering market capitalization of $140 billion, surpassing the valuation of numerous well-established corporations.
Though Dogecoin witnessed a meteoric rise in early 2021, primarily fueled by speculation, achieving the $1 mark based solely on core fundamentals presents challenges.
However, if Dogecoin can carve out tangible, real-world applications and continue to garner strong community and institutional support, the potential exists for it to approach, if not achieve, this ambitious price point.
Lack of Definitive Use Case - Despite its popularity, Dogecoin struggles to establish a definitive use case. While it's lauded for microtransactions, it needs to cement its place in broader ecosystems to sustainably drive its price upwards.
Market Volatility - Like all cryptocurrencies, Dogecoin is subject to market whims. External factors, regulatory pressures, or macroeconomic developments can induce price swings.
Competition from Other Altcoins - As the altcoin space grows increasingly crowded, Dogecoin competes with newer, technologically advanced coins promising better scalability, security, and utility.
Also Read - Is Dogecoin Dead?
Many industry pundits have mixed opinions. Some believe in Dogecoin's potential, banking on its strong community and increasing acceptability. Others remain skeptical, citing its origin as a joke and lack of solid technological backing.
The future trajectory of Dogecoin remains a topic of fervent discussion in the crypto realm. Originally conceived as a meme, its evolution has defied expectations, underpinned by a zealous community and sporadic celebrity endorsements.
As we look ahead, Dogecoin's potential hinges on several key factors. Its integration into mainstream platforms, potential technological upgrades, and broadening utility in real-world transactions will be pivotal. Furthermore, as regulatory frameworks around cryptocurrencies crystallize, Dogecoin's adaptability will be tested.
While challenges loom, the coin's dedicated community and increasing merchant acceptability offer a glimmer of optimism. Ultimately, Dogecoin's long-term viability will be determined by its ability to transform its internet fame into tangible, sustainable utility.
For Investors - If you're considering investing in Dogecoin, it's crucial to diversify your portfolio. Like all cryptos, Dogecoin should form part of a well-balanced portfolio. Regularly stay updated, as the crypto world evolves rapidly.
For Day Traders - Volatility can be both a boon and a bane. Set clear stop-losses and don't be swayed purely by market sentiment or celebrity tweets.
For The Community - For those who believe in Dogecoin's potential, community efforts to increase its utility, adoption, and technological advancements will be crucial in driving it towards the $1 mark.
Q1. What sets Dogecoin apart from other cryptocurrencies?
Dogecoin, originally created as a meme coin, has a strong community backing and is often used for online tipping and charitable donations. Its lighter-hearted approach differentiates it from more "serious" cryptos.
Q2. How secure is Dogecoin?
Like other cryptocurrencies, Dogecoin employs cryptographic techniques to secure transactions. However, it's always essential to use reputable wallets and be wary of phishing attacks.
Q3. Where can I buy and store Dogecoin?
Dogecoin is available on multiple cryptocurrency exchanges. For storage, it's recommended to use hardware wallets or secure software wallets with a strong reputation.
Q4. How is Dogecoin being adopted in the mainstream market?
Several online merchants and platforms are beginning to accept Dogecoin as a form of payment. Its community-driven initiatives also drive its adoption for various charitable causes.
Q5. What are the transaction fees for Dogecoin?
Dogecoin is known for its relatively low transaction fees compared to other cryptos, making it popular for micropayments. However, exact fees can vary based on network congestion.
Q6. Does Dogecoin have a maximum supply like Bitcoin?
No, Dogecoin does not have a maximum supply cap. This is in contrast to Bitcoin, which is capped at 21 million coins. This aspect influences Dogecoin's inflationary nature.
Q7. How does the Dogecoin community influence its trajectory?
The Dogecoin community is known for its vibrant and collaborative nature. They've spearheaded fundraising campaigns, charity events, and even sponsored a NASCAR driver. Their active involvement often sways public perception and adoption rates.
Q8. What are the potential risks of investing in Dogecoin?
Like all cryptocurrencies, Dogecoin investments come with risks. Market volatility, regulatory changes, and technological vulnerabilities can all impact its value. It's crucial to do thorough research and perhaps seek financial advice before investing.
Can Dogecoin reach $1 in 2023? The answer remains shrouded in layers of market dynamics, community efforts, global events, and pure unpredictability inherent to the crypto space.
However, one thing is clear: Dogecoin has come a long way from its meme origins, and its journey, whether it reaches $1 or not, remains a testament to the unpredictable and ever-evolving nature of the cryptocurrency world.
The information provided on this website does not constitute investment advice, financial advice, trading advice, or any other sort of advice and you should not treat any of the website's content as such.
Token Metrics does not recommend that any cryptocurrency should be bought, sold, or held by you. Do conduct your own due diligence and consult your financial advisor before making any investment decisions.

%201.svg)
%201.svg)
We're thrilled to announce a unique opportunity for your brand. Token Metrics has launched a compelling suite of podcasts, and we're inviting you to become an exclusive sponsor.
Take advantage of this tailor-made opportunity to boost your brand. To explore this collaboration further, please fill out our sponsor interest form.

%201.svg)
%201.svg)
In the world of cryptocurrency, the question of security is paramount. No matter how well you understand the market, or how diversified your portfolio is, if you don’t safeguard your assets, all can be lost in the blink of an eye.
Two names stand out in the hardware wallet industry: Trezor and Ledger. Both promise top-notch security, but which one should you entrust with your digital gold? Let's dive deep and make an informed decision.
Before we start, it's essential to grasp what a hardware wallet is. Simply put, it's a physical device, often resembling a USB stick, that stores your cryptocurrency private keys offline.
By keeping the keys offline, it offers protection against online hacking attempts, a significant advantage over online wallets.
Trezor Wallet is a pioneering hardware wallet developed by SatoshiLabs, a Czech-based company. Introduced in 2013, Trezor set the gold standard for cold storage of cryptocurrencies.
Unlike traditional online wallets, which are vulnerable to hacks, Trezor keeps your private keys offline, ensuring top-tier security against cyber threats. It's a compact device, somewhat resembling a USB flash drive, which connects to your computer or smartphone.
The wallet supports over a thousand different cryptocurrencies, providing both accessibility and security. Its intuitive interface, combined with features like pin protection, physical transaction confirmation, and a recovery seed system, ensures that even beginners can handle their crypto holdings with confidence and peace of mind.
Origin: Czech Republic
Founded: 2013 by SatoshiLabs
Popular Models: Trezor One, Trezor Model T
Ledger Wallet stands as one of the crypto community's most trusted hardware wallet solutions. Founded in France in 2014, Ledger offers users the security of cold storage combined with the flexibility of more than 1,800 supported cryptocurrencies.
Distinctively, Ledger incorporates a Secure Element (SE) chip, an advanced layer of protection against potential breaches. Resembling a sleek USB device, the Ledger can be connected to both computers and mobile devices.
Through its proprietary Ledger Live software, users can seamlessly manage transactions, check balances, and perform firmware updates.
With mandatory pin protection, physical verification of transactions, and a 24-word recovery seed mechanism, Ledger maintains a balance of user-friendliness and robust security for crypto enthusiasts.
Origin: France
Founded: 2014
Popular Models: Ledger Nano S, Ledger Nano X
Both devices prioritize security. After all, that's their primary function. Let's look at how each performs in this domain.
Trezor:
Ledger:
One of the primary considerations for crypto enthusiasts when selecting a hardware wallet is the range of supported cryptocurrencies. Ledger and Trezor, the industry titans, both offer extensive compatibility, albeit with some differences.
Ledger, with its Ledger Live software, proudly supports over 1,800 coins and tokens, ensuring that users can securely manage a broad spectrum of assets from major currencies like Bitcoin and Ethereum to numerous ERC-20 tokens.
On the other hand, Trezor isn't far behind, boasting support for more than 1,000 coins and tokens. While it provides native support for heavyweights like Bitcoin and Ethereum, certain lesser-known coins might require third-party interfaces.
Ultimately, while both wallets cater to the majority of crypto users' needs, those with diverse portfolios might lean towards Ledger for its wider array, whereas Trezor users appreciate its straightforward, web-based interface.
Usability plays a pivotal role in ensuring that users can securely and efficiently manage their assets.
Trezor:
1. Trezor offers straightforward interface with clear instructions.
2. Web-based interface that can be accessed easily from any computer.
3. The Model T features a touch screen for improved user experience.
Ledger:
1. Ledger Live software offers a comprehensive dashboard to manage assets.
2. The Nano X can connect via Bluetooth, making it compatible with mobile devices.
3. User-friendly design and intuitive features.
Q1. How often do Trezor and Ledger release firmware updates?
Both Trezor and Ledger are committed to maintaining high security and functionality standards. As such, firmware updates are released periodically, addressing potential vulnerabilities and improving user experience.
Q2. Can I use both Trezor and Ledger simultaneously for different assets?
Absolutely! Many crypto investors use multiple wallets to diversify their security approach. You can manage different assets or even the same asset across both wallets.
Q3. What happens if my hardware wallet gets stolen or damaged?
Both Trezor and Ledger provide recovery seeds (a series of words) during initial setup. With this seed, you can restore your assets on a new device.
Q4. Is it possible to add custom tokens or coins that aren't natively supported?
Ledger and Trezor both support numerous ERC-20 tokens and other assets. If a token isn't natively supported, it may be possible through third-party integrations or software.
Q5. Do I need an internet connection to use these hardware wallets?
While the wallets themselves store keys offline, an internet connection is required for transactions or updates. Always ensure a secure connection when using your wallet.
Q6. How do I know if the firmware update is official and not from a malicious source?
Always update firmware from the official Trezor or Ledger websites. Be wary of emails or pop-ups directing you to other sites or urging immediate updates.
Q7. Is it safe to use hardware wallets on public computers or networks?
While hardware wallets provide a layer of protection, using them on potentially compromised computers or open networks might expose you to risks. Always prioritize using trusted devices and networks.
Q8. Can I use my Trezor or Ledger wallet with mobile devices?
Yes, both wallets have mobile compatibility. Ledger's Nano X even offers Bluetooth connectivity for added convenience with mobile devices.
The decision between Trezor and Ledger boils down to personal preferences and specific needs.
Research & Stay Updated: Always look for the most recent reviews and updates on hardware wallets. The crypto world evolves rapidly, and staying informed is crucial.
Prioritize Security: No matter which wallet you choose, never share your pin or recovery seed with anyone.
Purchase from Official Channels: To avoid counterfeit devices, always buy directly from the official Trezor or Ledger websites or authorized sellers.
Backup: Always keep multiple copies of your recovery seed in safe places.
In conclusion, both Trezor and Ledger have proven their mettle in the crypto community, earning trust and loyalty from users. Your decision should align with your specific needs and preferences, but rest assured, both devices strive to offer the best protection for your digital assets.
The information provided on this website does not constitute investment advice, financial advice, trading advice, or any other sort of advice and you should not treat any of the website's content as such.
Token Metrics does not recommend that any cryptocurrency should be bought, sold, or held by you. Do conduct your own due diligence and consult your financial advisor before making any investment decisions.

%201.svg)
%201.svg)
The world of cryptocurrencies and blockchain technology can be both exciting and daunting. One tool that many crypto enthusiasts have likely come across is MetaMask.
But as with anything in the digital realm, safety is paramount. So, is MetaMask safe to use? Let's dive deep and uncover the facts.
MetaMask is a digital bridge that connects users to the Ethereum blockchain, primarily serving as both an Ethereum wallet and a browser extension.
Pioneering a more accessible approach to blockchain interactions, MetaMask allows users to run Ethereum dApps directly in their browsers without operating a full Ethereum node.
Designed with user-friendliness in mind, it offers a sleek interface where individuals can manage, store, and transfer Ethereum (ETH) and other ERC-20 tokens.
Beyond its basic wallet functions, MetaMask acts as a gateway, providing its users with the means to interact with various decentralized platforms, from DeFi (Decentralized Finance) projects to NFT (Non-Fungible Token) marketplaces, all while ensuring the security and privacy of its users' data and assets.
In essence, MetaMask combines the capabilities of a traditional crypto wallet with the added benefits of seamless browser integration, positioning itself as an essential tool for both novice and seasoned Ethereum enthusiasts.
MetaMask functions as a bridge between your browser and the Ethereum blockchain, embedding a cryptographic wallet directly in your browser.
Upon installation, it prompts users to create a wallet, generating a unique public (address) and private key pair. The public key allows receipt of Ethereum and ERC-20 tokens, while the private key, stored locally, authorizes transactions.
As you navigate supported websites, MetaMask detects and manages blockchain interactions, requesting your confirmation for each action. Transactions are signed using your private key, ensuring it remains confidential.
With its hierarchical deterministic design, multiple Ethereum addresses can be derived from a single seed phrase, streamlining user interactions with the decentralized web.
Yes, MetaMask stands as one of the most recognized tools in the Ethereum ecosystem, and its reputation is anchored in its commitment to user security.
The platform is designed to ensure that users' private keys, which are essential for accessing funds and authorizing transactions, are stored locally on their device, never on centralized servers.
This means the keys remain exclusively in the user's control, significantly reducing the risk of external breaches. Additionally, MetaMask employs end-to-end encryption and provides a unique seed phrase during setup—a set of words that act as a recovery tool, ensuring users can always regain access to their assets.
However, like all digital tools, MetaMask's safety hinges on vigilant user practices, like avoiding phishing sites and routinely backing up their seed phrase.
In essence, while MetaMask offers robust security features, users' behaviors play a pivotal role in ensuring optimal safety.
MetaMask hasn't gained its widespread reputation without good reason. It boasts several features designed to keep your assets safe:
Local Storage of Private Keys - MetaMask stores users' private keys directly on their device, rather than on centralized servers. By doing so, it significantly reduces the risks associated with hacks or unauthorized breaches, ensuring that users maintain total control over their keys and, by extension, their assets.
Seed Phrase System - Upon wallet creation, users are given a unique set of words known as a seed phrase. This seed phrase is paramount for backup and recovery. Should a user lose access to their MetaMask account or face device issues, the seed phrase serves as the only way to restore access to their assets.
User Confirmation for Transactions - For every action, whether it's a transaction or an interaction with a decentralized application (dApp), MetaMask prompts users for explicit confirmation. This added layer of confirmation acts as a safeguard, preventing any unintentional or malicious transactions from processing without the user's express consent.
End-to-End Encryption - MetaMask employs rigorous encryption standards to ensure that all data and communication within the platform remain private and protected.
This ensures that sensitive information, such as transaction details, remains confidential, safeguarding against potential eavesdropping or interception by malicious actors.
Regular Updates - MetaMask's development team continually rolls out updates to address potential vulnerabilities and improve overall security.
By keeping the platform up-to-date, users are better protected against evolving digital threats and can benefit from enhanced features and improved security protocols.
MetaMask has emerged as an indispensable tool in the Ethereum and broader blockchain landscape, offering users a myriad of advantages. Here's a look at some of the key benefits:
User-Friendly Interface - MetaMask boasts an intuitive design, making it easy for both beginners and seasoned crypto enthusiasts to navigate and manage their assets.
Direct Browser Integration - As a browser extension, MetaMask offers seamless interaction with decentralized applications (dApps) without needing to leave your browser or run a full Ethereum node.
Compatibility - MetaMask was initially designed for the Ethereum network, yet it also offers connectivity to chains compatible with Ethereum, commonly known as EVM (Ethereum Virtual Machine) chains. This functionality allows users to link to various networks, including Binance Smart Chain, Polygon (formerly Matic), xDai, among others.
Support for Multiple Tokens - Beyond Ethereum (ETH), MetaMask can store and manage a variety of ERC-20 and ERC-721 tokens, offering flexibility and a comprehensive asset management system.
Secure Environment - With local storage of private keys, end-to-end encryption, and a unique seed phrase recovery system, MetaMask emphasizes robust security measures to protect users' assets.
Decentralized Access - MetaMask facilitates a decentralized web experience, granting users access to a vast array of dApps, from games to decentralized finance platforms.
Customizable Gas Fees - Users have the flexibility to adjust gas fees based on their transaction urgency, allowing for cost-effective transfers during less congested network times.
Regularly Updated - MetaMask's team continually rolls out updates, ensuring the platform remains current, secure, and packed with the latest features.
While MetaMask has several commendable safety features, it's crucial to be aware of potential risks:
Phishing Scams: Cybercriminals create fake MetaMask websites or applications. If you input your details here, they could gain access to your funds.
Browser Vulnerabilities: Being a browser extension, MetaMask could be susceptible to browser-related security flaws or vulnerabilities.
Human Error: Losing your seed phrase or mistakenly sending assets to the wrong address can result in irreversible losses. Remember, blockchain transactions are final.
Also Read - Is Ethereum Dead? - Complete Analysis
Enhancing MetaMask security involves several steps:
Backup - Always backup your seed phrase offline in multiple secure locations.
Software - Keep your browser, MetaMask extension, and system software up-to-date.
Phishing - Be cautious of phishing attempts. Always double-check URLs and never provide your seed phrase online.
Additional Layers - Consider hardware wallets or using MetaMask in combination with tools like Ledger or Trezor for added security layers.
If you suspect your MetaMask has been compromised:
Immediate Action - Transfer funds to a new, secure Ethereum address if possible.
Recovery - Use your seed phrase to restore your wallet on a different, secure device.
Review - Analyze how the breach occurred—was it due to a phishing scam, malware, or some other reason?
Preventive Measures - Implement stronger security measures, like integrating a hardware wallet or regularly reviewing active authorized sites on MetaMask.
Report - Inform the MetaMask team about the incident to potentially get support and to help them be aware of any new vulnerabilities or attack strategies.
In line with Token Metrics' dedication to quality, accuracy, and actionable insights, here are steps you can take to ensure the utmost safety when using MetaMask -
Double-Check URLs - Before entering any information, ensure you're on the official MetaMask platform. Avoid clicking on suspicious links from emails or social media.
Backup Your Seed Phrase - Store your 12-word seed phrase in a secure and offline environment. This is your only recovery option.
Regularly Update - Ensure your MetaMask extension and browser are always up to date. This ensures you're protected with the latest security patches.
Use Hardware Wallets - For added security, especially if you're dealing with significant amounts, consider linking MetaMask with a hardware wallet like Ledger or Trezor.
Beware of Unsolicited Offers - Scammers might reach out with too-good-to-be-true offers or impersonate support. Always be skeptical and never share your seed phrase.
Q1. Can I use MetaMask on mobile devices?
Yes, MetaMask offers a mobile application available for both Android and iOS. This app not only serves as a wallet but also as a browser to interact with decentralized applications.
Q2. How do I backup my MetaMask wallet?
It's crucial to backup your seed phrase provided during the wallet's initial setup. Store this phrase securely, as it's the primary method to recover your account in case you lose access.
Q3. Can I import wallets from other services into MetaMask?
Absolutely. MetaMask allows users to import accounts using either their private key or a JSON file, making it easy to consolidate Ethereum-based assets.
Q4. Can I swap tokens directly within MetaMask?
Yes, MetaMask introduced a token swapping feature, allowing users to exchange one token for another directly within the extension, ensuring convenience and security.
Q5. What should I do if I suspect a phishing attack or scam related to MetaMask?
If you come across suspicious activity, immediately avoid providing any personal or wallet details. Report the incident to MetaMask's official channels, and always double-check URLs and sources before entering your credentials.
Q6. Are there alternatives to MetaMask in the market?
While MetaMask is popular, there are several other Ethereum wallet and browser extension options like Trust Wallet, MyEtherWallet, and Coinbase Wallet. Each offers its own features and security protocols, so it's recommended to research based on individual needs.
Q7. Is MetaMask safer than Coinbase?
Both MetaMask and Coinbase prioritize user security, but they function differently. With MetaMask, the user's security depends largely on their practices, like protecting their seed phrase.
In contrast, Coinbase users rely on the platform's security measures and insurances. Neither is inherently "safer"; it's more about where users feel more comfortable placing their trust and how they manage security on their end.
Q8. Is storing on MetaMask safe?
Yes, storing assets on MetaMask is considered safe due to its decentralized nature and local storage of private keys. However, its security is also contingent on the user's practices. It's vital to ensure that the seed phrase is stored securely offline, avoid phishing sites, and ensure the device on which MetaMask is installed remains secure.
MetaMask, in its essence, offers robust security features designed to protect its users. However, like many digital tools, its safety also largely depends on user practices. By staying informed and following recommended safety protocols, you can enjoy the functionalities of MetaMask with peace of mind.
Remember, the crypto world is still relatively young, and while tools like MetaMask bring immense convenience, they also come with responsibilities. Stay vigilant, stay informed, and always prioritize your digital safety.
The information provided on this website does not constitute investment advice, financial advice, trading advice, or any other sort of advice and you should not treat any of the website's content as such.
Token Metrics does not recommend that any cryptocurrency should be bought, sold, or held by you. Do conduct your own due diligence and consult your financial advisor before making any investment decisions.

 Create Your Free Account
Create Your Free Account9450 SW Gemini Dr
PMB 59348
Beaverton, Oregon 97008-7105 US
.svg)




.png)
Token Metrics Media LLC is a regular publication of information, analysis, and commentary focused especially on blockchain technology and business, cryptocurrency, blockchain-based tokens, market trends, and trading strategies.
Token Metrics Media LLC does not provide individually tailored investment advice and does not take a subscriber’s or anyone’s personal circumstances into consideration when discussing investments; nor is Token Metrics Advisers LLC registered as an investment adviser or broker-dealer in any jurisdiction.
Information contained herein is not an offer or solicitation to buy, hold, or sell any security. The Token Metrics team has advised and invested in many blockchain companies. A complete list of their advisory roles and current holdings can be viewed here: https://tokenmetrics.com/disclosures.html/
Token Metrics Media LLC relies on information from various sources believed to be reliable, including clients and third parties, but cannot guarantee the accuracy and completeness of that information. Additionally, Token Metrics Media LLC does not provide tax advice, and investors are encouraged to consult with their personal tax advisors.
All investing involves risk, including the possible loss of money you invest, and past performance does not guarantee future performance. Ratings and price predictions are provided for informational and illustrative purposes, and may not reflect actual future performance.