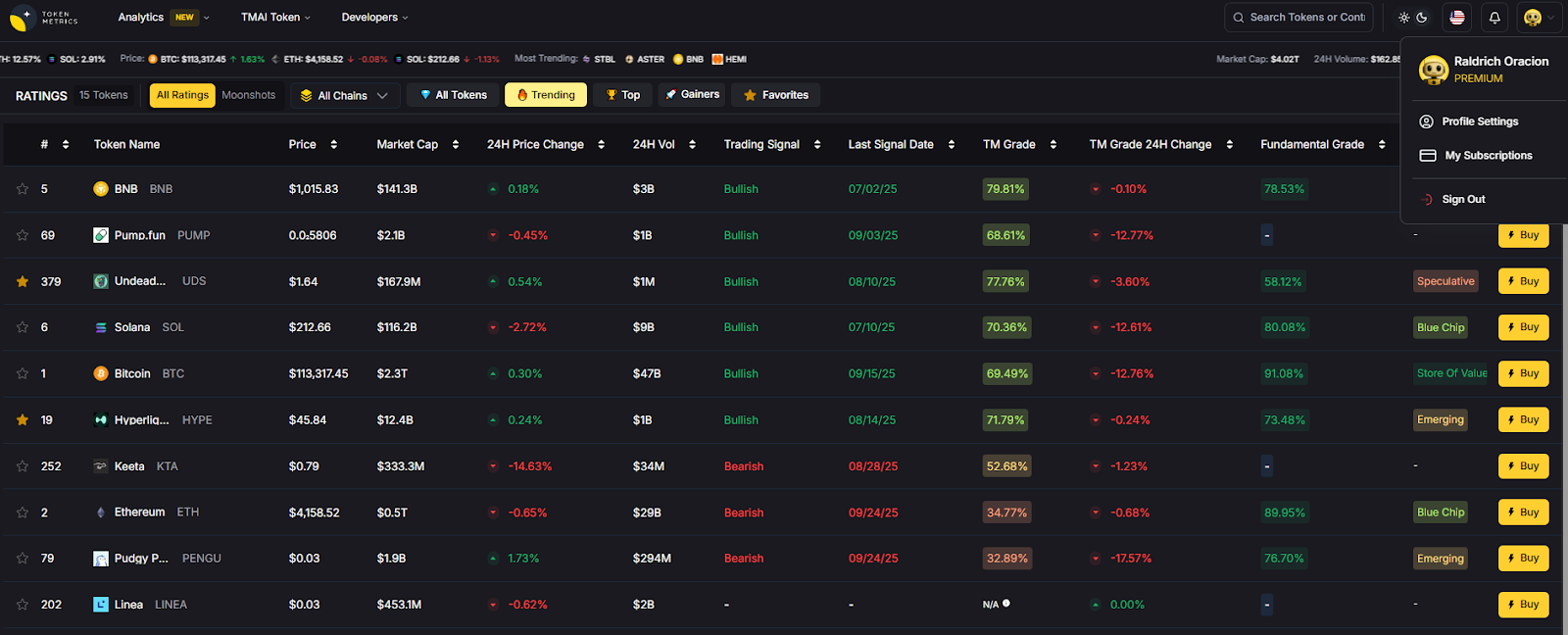
Top Crypto Trading Platforms in 2025




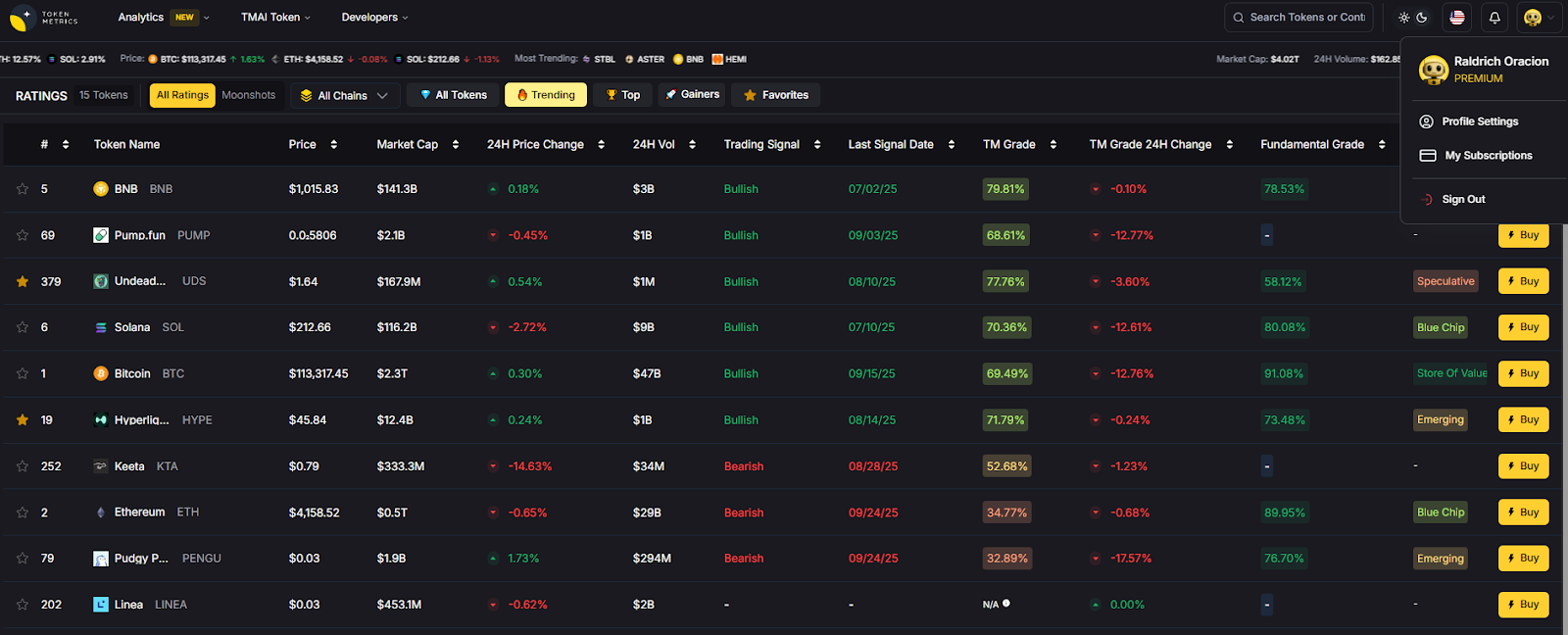
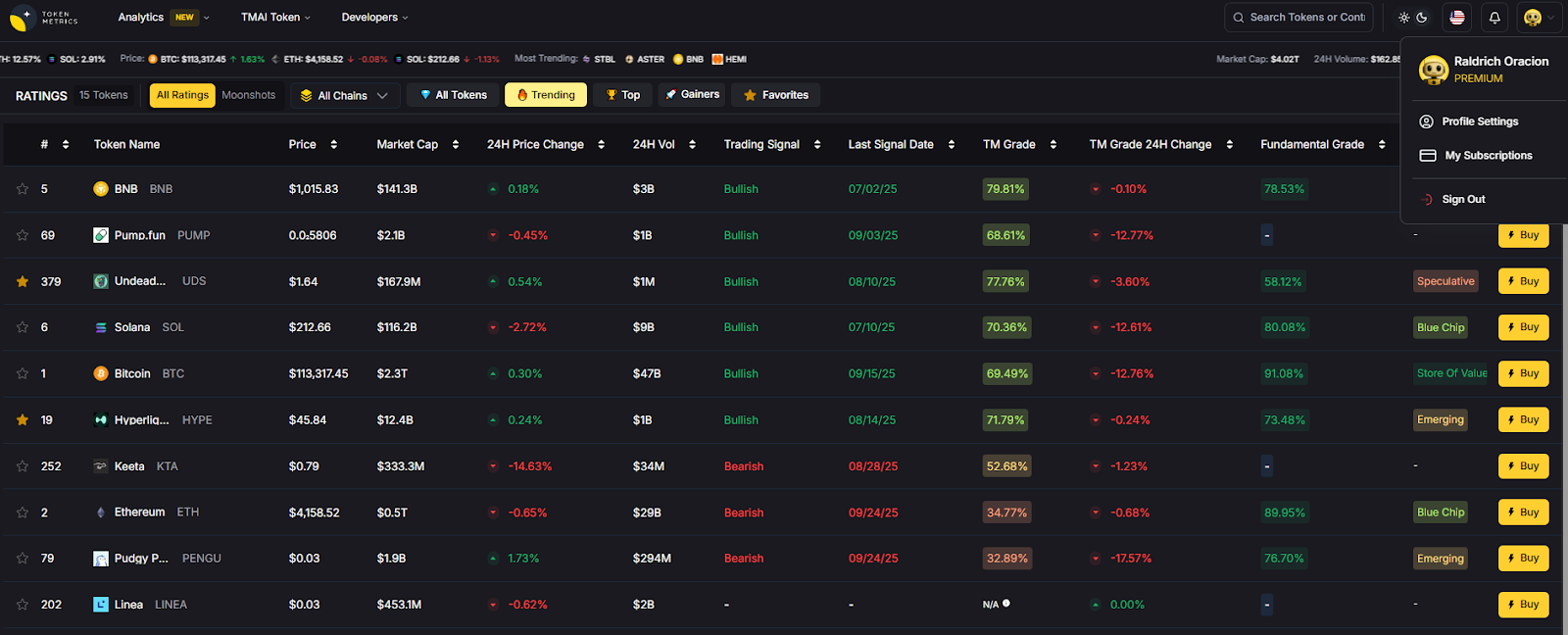
Big news: We’re cranking up the heat on AI-driven crypto analytics with the launch of the Token Metrics API and our official SDK (Software Development Kit). This isn’t just an upgrade – it's a quantum leap, giving traders, hedge funds, developers, and institutions direct access to cutting-edge market intelligence, trading signals, and predictive analytics.
Crypto markets move fast, and having real-time, AI-powered insights can be the difference between catching the next big trend or getting left behind. Until now, traders and quants have been wrestling with scattered data, delayed reporting, and a lack of truly predictive analytics. Not anymore.
The Token Metrics API delivers 32+ high-performance endpoints packed with powerful AI-driven insights right into your lap, including:
Getting started with the Token Metrics API is simple:
At Token Metrics, we believe data should be decentralized, predictive, and actionable.
The Token Metrics API & SDK bring next-gen AI-powered crypto intelligence to anyone looking to trade smarter, build better, and stay ahead of the curve. With our official SDK, developers can plug these insights into their own trading bots, dashboards, and research tools – no need to reinvent the wheel.
Retail-friendly mobile and web wallets make crypto usable—on your phone and in your browser—without relying on a centralized custodian. This guide ranks the best retail crypto wallets for 2025 so you can safely store, send, swap, and explore Web3. A crypto wallet is software that holds your keys and lets you sign transactions; self-custody means you control those keys.
We focus on practical needs: everyday buys, swaps, NFT viewing, multi-chain coverage, and clear fees. Expect mainstream names alongside rising multichain players. Secondary considerations include mobile crypto wallet UX, web3 wallet dapp access, and self-custody wallet security. If you’re new, start with a wallet that offers simple onboarding and robust recovery. If you’re advanced, look for pre-transaction risk checks, multichain swaps, and hardware support.
Why Use It: The most ubiquitous Web3 wallet, MetaMask balances power and familiarity. It’s everywhere dapps are, with mobile + browser extension, good network support, and strong swap/bridge routing in-app. Smart Transactions and built-in security alerts improve reliability for everyday users. MetaMask
Best For: EVM users, NFT collectors, L2 explorers, DeFi regulars.
Notable Features: Smart Transactions; Swaps/Bridge aggregator; MetaMask Learn; mobile + major browsers. MetaMask+1
Consider If: You want explicit fee transparency—MetaMask Swaps includes a 0.875% service fee (plus network gas). MetaMask Help Center
Alternatives: Trust Wallet, OKX Wallet.
Regions: Global.
Fees Notes: Network fees; MetaMask Swaps service fee 0.875%. MetaMask Help Center
Why Use It: Trust Wallet offers a simple, one-stop experience: buy, send, swap, stake, and manage NFTs across many chains. Its mobile app is fast, and the extension integrates with popular EVM and non-EVM chains. Trust Wallet+1
Best For: Beginners who want breadth; multichain NFT holders; mobile-first users.
Notable Features: Built-in DApp browser; simplified swaps with gas optimization; staking flows. Trust Wallet
Consider If: You want no added swap fee—Trust says it doesn’t charge extra on swaps (you still pay network/third-party fees). Trust Wallet
Alternatives: MetaMask, Crypto.com Onchain.
Regions: Global.
Fees Notes: Network/partner fees apply; Trust states no added in-app swap fee. Trust Wallet
Why Use It: Rebranded as the Base app, the former Coinbase Wallet keeps familiar self-custody features while embracing Base/L2 culture and onchain social/activity. If you already use Coinbase products, onboarding is straightforward while staying self-custodial. Coinbase
Best For: Coinbase users going self-custody; Base/L2 explorers; web3 social/NFT dabblers.
Notable Features: Self-custody; trading, posting, playing; continuity for Coinbase Wallet users. Coinbase
Consider If: You prefer chain-agnostic advanced tooling—others may offer deeper multichain utilities today.
Alternatives: MetaMask, Rainbow.
Regions: Global.
Fees Notes: Network fees; third-party swap/partner fees where used. Coinbase
Why Use It: Phantom started Solana-first and has grown into a polished multichain wallet (Solana, Ethereum, and more). The interface is clean, with strong NFT views and transaction clarity—great for newcomers to Solana and cross-chain dabblers. Phantom+1
Best For: Solana users, NFT traders, multichain retail.
Notable Features: In-wallet swaps and bridging; gasless swaps on Solana (select cases); robust notifications/history. Phantom Support+1
Consider If: You want the lowest possible swap fees—Phantom lists 0.85% on select pairs, with separate gas/bridge fees. Phantom Support
Alternatives: OKX Wallet, Trust Wallet.
Regions: Global.
Fees Notes: Network fees; Phantom fee 0.85% on select swaps; gasless-swap fee rules apply on Solana. Phantom Support+1
Why Use It: OKX Wallet (extension + mobile) plugs you into OKX’s DEX aggregator, NFT marketplace, and DeFi. It offers multiple swap modes and solid routing—useful when chasing best execution across chains. OKX Wallet+1
Best For: DeFi users seeking liquidity routing; cross-chain swappers; NFT traders.
Notable Features: Multi-mode swaps; DEX aggregator; marketplace; Earn/Discover sections. OKX Wallet
Consider If: You need crystal-clear fee schedules—OKX lists DEX interface fee tiers up to 0.85% depending on pair groups. OKX Wallet
Alternatives: MetaMask, Bitget Wallet.
Regions: Global (wallet).
Fees Notes: Network fees; OKX DEX interface fee 0–0.85% by pair category. OKX Wallet
Why Use It: Exodus is a long-standing, self-custodial wallet with a beautifully designed UI across desktop and mobile. Portfolio tracking and NFT galleries are polished, and its Web3 Wallet extends multichain support. Exodus
Best For: Newcomers who want clarity; portfolio-first users; multi-device use.
Notable Features: Multichain Web3 Wallet; thousands of swap pairs; simple buy/sell integrations. Exodus
Consider If: You want explicit fee details—Exodus doesn’t charge send/receive wallet fees, but network and partner fees still apply. Exodus Knowledge Base
Alternatives: Crypto.com Onchain, ZenGo.
Regions: Global.
Fees Notes: No Exodus send/receive fees; network fees + third-party swap/fiat fees may apply. Exodus Knowledge Base
Why Use It: Formerly known as the DeFi Wallet experience, Crypto.com Onchain is a self-custodial app with multichain support, in-wallet trading, and dapp access. It’s friendly for users who like Crypto.com’s ecosystem but want self-custody keys. Crypto.com
Best For: Mobile-first users; staking/earn explorers; Crypto.com ecosystem fans.
Notable Features: Local key encryption; import via 12/18/24-word phrases; multichain trading & dapp browser. Crypto.com
Consider If: You prefer a purely chain-agnostic wallet without exchange brand ties—others may feel “lighter.”
Alternatives: Trust Wallet, Exodus.
Regions: Global (feature availability can vary).
Fees Notes: Network/partner fees; self-custody (no custodial withdrawal fees). Crypto.com
Why Use It: ZenGo uses MPC to remove single-point seed phrase risks while keeping you in self-custody. That makes setup and recovery less nerve-wracking for new users, without buying hardware. Zengo+1
Best For: Beginners prioritizing recovery; mobile-only users; security-conscious travelers.
Notable Features: Seed-phrase-free MPC; in-app buy/swap; staking for select assets. Zengo+1
Consider If: You want classic seed control or advanced on-chain tooling—some power features are simpler by design.
Alternatives: Ledger Live (with hardware), Trust Wallet.
Regions: Global.
Fees Notes: Network fees; partner fees for buy/swap as quoted in-app. Zengo
Why Use It: Formerly BitKeep, Bitget Wallet has grown into a large multichain wallet with DEX aggregation, dapp discovery, and memecoin-friendly flows. It’s geared for on-chain traders who want routing and token coverage across 65+ chains. Bitget Wallet+1
Best For: Power users in DeFi; memecoin and airdrop participants; cross-chain swaps.
Notable Features: Multichain DEX aggregator; dapp hub; iOS/Android + Chrome extension. Bitget Wallet
Consider If: You prefer a simpler, beginner-first interface—others above are more hand-holding.
Alternatives: OKX Wallet, MetaMask.
Regions: Global.
Fees Notes: Network fees; interface/partner fees vary by route/pair. Bitget Wallet
Why Use It: Ledger Live is the companion app to Ledger hardware wallets; it brings buy, swap, stake, and portfolio monitoring into a single interface while private keys stay in the hardware device. Great for retail users who want a mobile/desktop app but insist on offline signing. Ledger
Best For: Long-term holders; high-value accounts; users planning to add hardware.
Notable Features: Buy/sell/swap/stake modules; multi-asset support; iOS/Android + desktop. Google Play+1
Consider If: You don’t own hardware—full security benefits require a Ledger device.
Alternatives: ZenGo (MPC), Trezor Suite (with hardware).
Regions: Global.
Fees Notes: Network fees; partner fees for buy/swap as quoted in-app. Ledger

Primary CTA: Start free trial

This article is for research/education, not financial advice.
What is a retail crypto wallet (mobile/web)?
A mobile/web retail wallet is software that stores your private keys and lets you sign transactions from your phone or browser. Most are self-custodial, meaning you—not an exchange—control your keys.
Is a self-custody wallet safer than keeping coins on an exchange?
Self-custody removes exchange counterparty risk. However, you must protect recovery methods (seed phrase, MPC recovery) and your device. Hardware or MPC-based options can add protection.
Which wallet is best for beginners?
For simplicity: Trust Wallet, Exodus, or ZenGo. They have straightforward onboarding, clear portfolio views, and solid docs. Advanced users might prefer MetaMask, Phantom, or OKX Wallet for deeper on-chain tooling. OKX Wallet+5Trust Wallet+5Exodus+5
What fees should I expect?
You’ll always pay network gas. Some wallets add interface/service fees on swaps/bridges (e.g., MetaMask 0.875%; Phantom 0.85% on select pairs; OKX DEX 0–0.85% depending on token groups). MetaMask Help Center+2Phantom Support+2
Do I need hardware for mobile/web wallets?
No. Many work fine without hardware. For higher balances, pairing a mobile/web app with a hardware wallet (e.g., via Ledger Live) can reduce signing risk. Ledger
Can I use one wallet across multiple chains?
Yes—most featured wallets are multichain. Check chain lists and NFT support before migrating. OKX Wallet+2Bitget Wallet+2
If you want maximum dapp coverage, go MetaMask; Solana-centric with great UX, pick Phantom; for exchange-adjacent simplicity, choose Base app or Crypto.com Onchain; for hardware-backed security, Ledger Live. Power users chasing routing and airdrops may prefer OKX Wallet or Bitget Wallet, while newcomers should consider Trust Wallet, Exodus, or ZenGo.
Related Reads:
If you trade crypto futures and options, picking the right derivatives platforms can make or break your results. In this guide, we sort the top exchanges and on-chain venues by liquidity, security, costs, and product depth so you can match your strategy to the right venue—fast. You’ll find quick answers near the top, deeper context below, and links to official resources. We cover crypto futures, crypto options, and perpetual swaps for both centralized and decentralized platforms.
Quick answer: The best platform for you depends on region/eligibility, contract types (perps, dated futures, options), fee structure, margin system, and support quality. Below we score each provider and map them to common use cases.
We scored each provider using the weights below (0–100 total):
Sources: Official platform pages, help centers, and product docs; public disclosures and product catalogs; our hands-on review and long-term coverage of derivatives venues. Last updated September 2025.
Each summary includes why it stands out, who it’s best for, and what to consider. Always check regional eligibility.
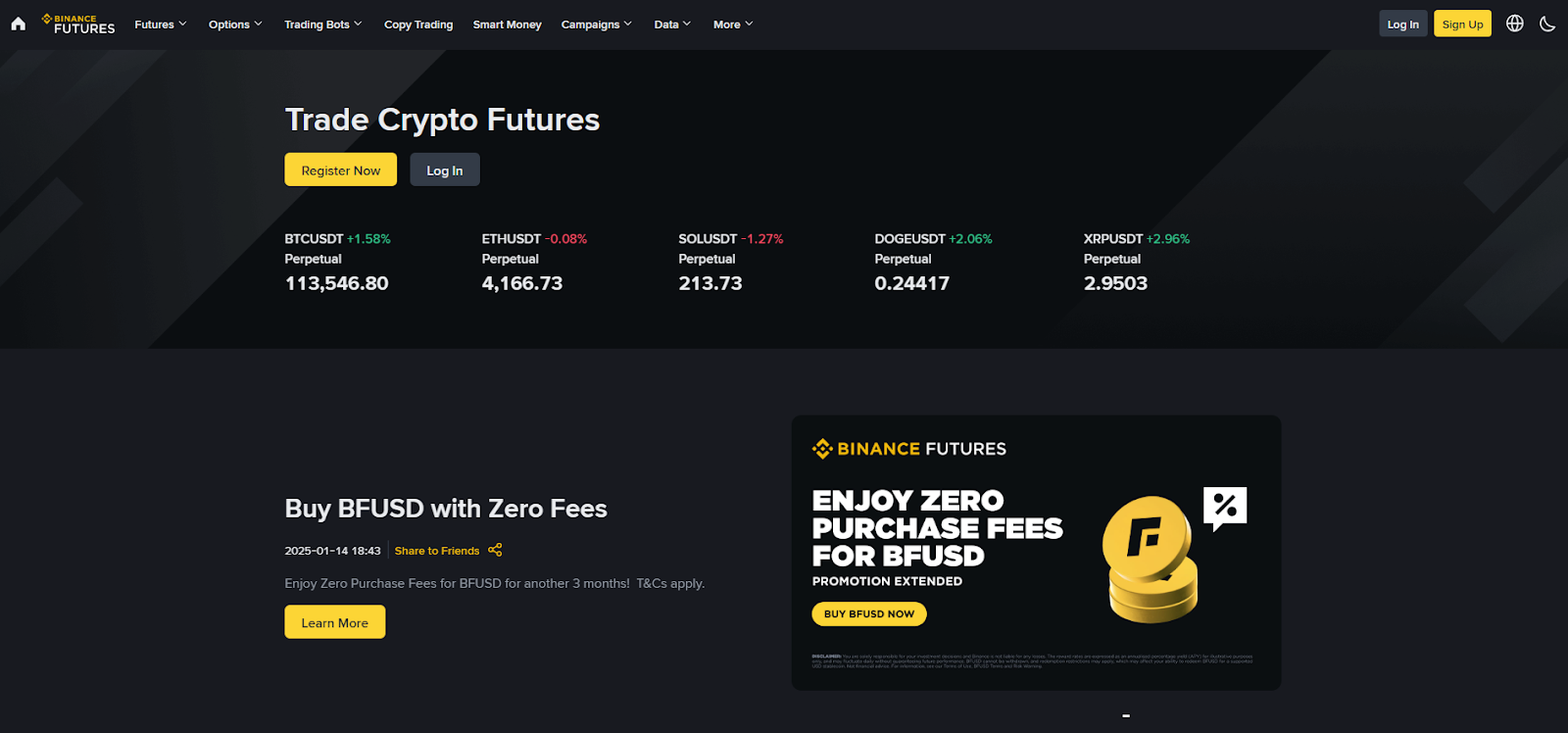
Why Use It: Binance Futures offers some of the deepest books and widest perp listings, with robust APIs and portfolio margin. It’s a go-to for active traders who need speed and breadth.
Best For: High-frequency/active traders; systematic/API users; altcoin perp explorers.
Notable Features: Perpetuals and dated futures, options module, copy trading, portfolio margin.
Consider If: You need U.S.-regulated access—availability may vary by region.
Alternatives: OKX, Bybit.
Why Use It: Strong product coverage (perps, dated futures, options) with solid liquidity and a polished interface. Good balance of features for discretionary and API traders.
Best For: Multi-instrument traders; users wanting options + perps under one roof.
Notable Features: Unified account, options chain, pre-market perps, apps and API.
Consider If: Region/eligibility and KYC rules may limit access.
Alternatives: Binance Futures, Bybit.
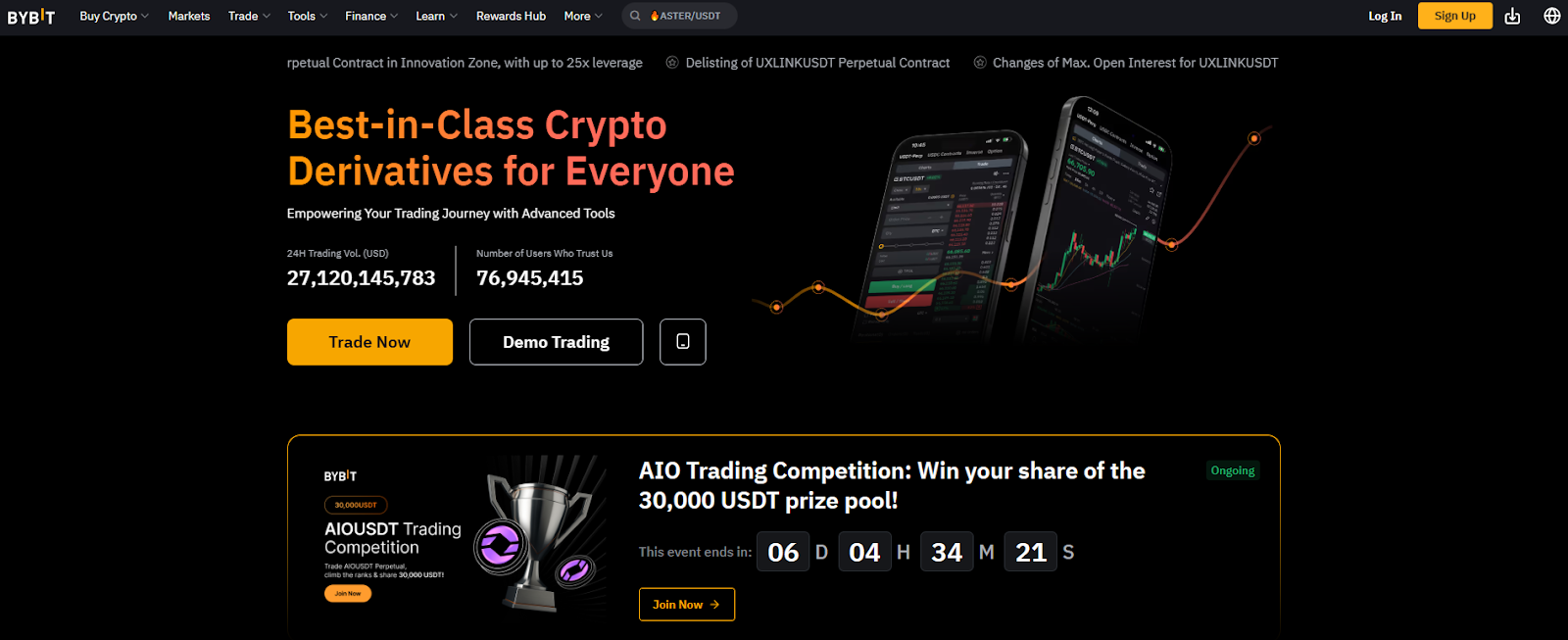
Why Use It: Competitive fees, broad perp markets, solid tooling, and a large user base make Bybit attractive for day traders and swing traders alike.
Best For: Perps power users; copy-trading and mobile-first traders.
Notable Features: USDT/USDC coin-margined perps, options, demo trading, OpenAPI.
Consider If: Check your local rules—service availability varies by region.
Alternatives: Binance Futures, Bitget.
Why Use It: Deribit is the reference venue for crypto options on BTC and ETH, with deep liquidity across maturities and strikes; it also offers futures.
Best For: Options traders (directional, spreads, volatility) and institutions.
Notable Features: Options analytics, block trading tools, test environment, 24/7 support.
Consider If: Regional access may be limited; primarily majors vs. broad alt coverage.
Alternatives: Aevo (on-chain), CME (regulated futures/options).
Why Use It: For institutions needing CFTC-regulated access, margin efficiency, and robust market infrastructure, CME is the standard for BTC/ETH futures and options.
Best For: Funds, corporates, and professionals with FCM relationships.
Notable Features: Standard and micro contracts, options, benchmarks, data tools.
Consider If: Requires brokerage/FCM onboarding; no altcoin perps.
Alternatives: Coinbase Derivatives (U.S.), Kraken Futures (institutions).
Why Use It: dYdX v4 runs on its own chain with on-chain settlement and pro tooling. Traders who want non-custodial perps and transparent mechanics gravitate here.
Best For: DeFi-native traders; users prioritizing self-custody and transparency.
Notable Features: On-chain orderbook, staking & trading rewards, API, incentives.
Consider If: Wallet/key management and gas/network dynamics add complexity.
Alternatives: Aevo (options + perps), GMX (alt DEX perps).
Why Use It: Kraken offers crypto futures for eligible regions, with a growing U.S. footprint via Kraken Derivatives US and established institutional services.
Best For: Traders who value brand trust, support, and clear documentation.
Notable Features: Pro interface, institutional onboarding, status and support resources.
Consider If: Product scope and leverage limits can differ by jurisdiction.
Alternatives: Coinbase Derivatives, CME.
Why Use It: NFA-supervised futures for eligible U.S. customers and resources that explain contract types. Outside the U.S., Coinbase also offers derivatives via separate entities.
Best For: U.S. traders needing regulated access; Coinbase ecosystem users.
Notable Features: Nano BTC/ETH contracts, 24/7 trading, learn content, FCM/FCM-like flows.
Consider If: Contract lineup is narrower than global offshore venues.
Alternatives: CME (institutional), Kraken Futures.
Why Use It: Bitget emphasizes a wide perp catalog, social/copy features, and frequent product updates—useful for traders rotating across narratives.
Best For: Altcoin perp explorers; copy-trading users; mobile-first traders.
Notable Features: USDT/USDC-margined perps, copy trading, frequent listings, guides.
Consider If: Check eligibility and risk—breadth can mean uneven depth in tail assets.
Alternatives: Bybit, OKX.
Why Use It: Aevo runs a custom L2 (OP-stack based) and offers options, perps, and pre-launch futures with unified margin—bridging CEX-like speed with on-chain settlement.
Best For: Options/perps traders who want DeFi custody with pro tools.
Notable Features: Unified margin, off-chain matching + on-chain settlement, pre-launch markets, detailed docs and fee specs.
Consider If: On-chain workflows (bridging, gas) and product scope differ from CEXs.
Alternatives: Deribit (options liquidity), dYdX (perps DEX).

Workflow (1–4): Research with Token Metrics → Pick venue(s) above → Execute perps/options → Monitor with alerts and refine.
Primary CTA: Start free trial

This article is for research/education, not financial advice.
What’s the difference between perps and traditional futures?
Perpetual swaps have no expiry, so you don’t roll contracts; instead, a funding rate nudges perp prices toward spot. Dated futures expire and may require roll management. Binance+1
Where can U.S. traders access regulated crypto futures?
Through CFTC/NFA-supervised venues like CME (via FCMs) and Coinbase Derivatives for eligible customers; availability and contract lists vary by account type. CME Group+2Coinbase+2
What’s the leading venue for BTC/ETH options liquidity?
Deribit has long been the primary market for BTC/ETH options liquidity used by pros and market makers. deribit.com
Which DEXs offer serious perps trading?
dYdX is purpose-built for on-chain perps with a pro workflow; Aevo blends options + perps with unified margin on a custom L2. dYdX Chain+1
How do I keep fees under control?
Use maker orders where possible, seek fee tier discounts/rebates, and compare funding rates over your expected holding time. Each venue publishes fee schedules and specs.
If you want deep global perps, start with Binance, OKX, or Bybit. For BTC/ETH options, Deribit remains the benchmark. If you need U.S.-regulated access, look at CME via an FCM or Coinbase Derivatives; Kraken is expanding its futures footprint. Prefer self-custody? dYdX and Aevo are solid on-chain choices. Match the venue to your region, contracts, and risk process—then let Token Metrics surface signals and manage the watchlist.
Related Reads
When you need to move size without moving the market, you use over-the-counter (OTC) trading. The best OTC desks for large block trades aggregate deep, private liquidity, offer quote certainty (via RFQ), and settle securely—often with high-touch coverage. In one sentence: an OTC crypto desk privately matches large buyers and sellers off-exchange to reduce slippage and information leakage. This guide is for funds, treasuries, family offices, market makers, and whales who want discretion, fast settlement, and reliable pricing in 2025. We compared global OTC providers on liquidity depth, security posture, coverage, costs, UX, and support, and selected 10 standouts. Expect clear use-case picks, region notes, and a simple checklist so you can choose faster. OKX
Data sources: official product/docs and institutional pages; security/transparency pages; and widely cited market datasets only for cross-checks (we do not link third-party sources in body). Last updated September 2025. OKX+3Coinbase+3Kraken+3


Primary CTA: Start free trial.

This article is for research/education, not financial advice.
What is an OTC crypto desk?
An OTC desk privately matches large buyers and sellers off public order books to minimize slippage and information leakage. Trades are negotiated via RFQ and settled bilaterally or through an exchange affiliate. OKX
How big is a “block trade” in crypto?
It varies by desk and asset. Many desks treat six-figure USD notional as a starting point; some exchange-affiliated desks list thresholds or minimum asset requirements in portals. OKX
Do U.S. clients have fewer options?
U.S. institutions often prefer regulated venues and agency models (e.g., Coinbase Institutional, Kraken). Some global platforms are limited for U.S. persons; check eligibility before onboarding. Coinbase+2Kraken+2
What fees should I expect?
Most OTC pricing is embedded in the spread. Some venues disclose desk or user-to-user OTC fees (e.g., Bitfinex lists 0.1% for certain OTC flows); always request example RFQs. support.bitfinex.com
Is OTC safer than exchanging on-book?
Neither is inherently “safer.” OTC can reduce market impact and information leakage, but you still need strong KYC/custody, verified comms, and clear settlement procedures. OKX
If you’re a U.S.-regulated fund that values agency execution, start with Coinbase Institutional or Kraken. If you need global, principal liquidity and breadth, look at Binance OTC, OKX, Cumberland, B2C2, Wintermute, FalconX, or Galaxy. Match the desk to your region, execution style (agency vs. principal), and settlement needs, then run trial quotes before you scale.
Related Reads:
