Top Crypto Trading Platforms in 2025







%201.svg)
%201.svg)
Big news: We’re cranking up the heat on AI-driven crypto analytics with the launch of the Token Metrics API and our official SDK (Software Development Kit). This isn’t just an upgrade – it's a quantum leap, giving traders, hedge funds, developers, and institutions direct access to cutting-edge market intelligence, trading signals, and predictive analytics.
Crypto markets move fast, and having real-time, AI-powered insights can be the difference between catching the next big trend or getting left behind. Until now, traders and quants have been wrestling with scattered data, delayed reporting, and a lack of truly predictive analytics. Not anymore.
The Token Metrics API delivers 32+ high-performance endpoints packed with powerful AI-driven insights right into your lap, including:
Getting started with the Token Metrics API is simple:
At Token Metrics, we believe data should be decentralized, predictive, and actionable.
The Token Metrics API & SDK bring next-gen AI-powered crypto intelligence to anyone looking to trade smarter, build better, and stay ahead of the curve. With our official SDK, developers can plug these insights into their own trading bots, dashboards, and research tools – no need to reinvent the wheel.
%201.svg)
%201.svg)
Layer 1 tokens like Hedera represent bets on specific blockchain architectures winning developer and user mindshare. HBAR carries both systematic crypto risk and unsystematic risk from Hedera's technical roadmap execution and ecosystem growth. Multi-chain thesis suggests diversifying across several L1s rather than concentrating in one, since predicting which chains will dominate remains difficult.
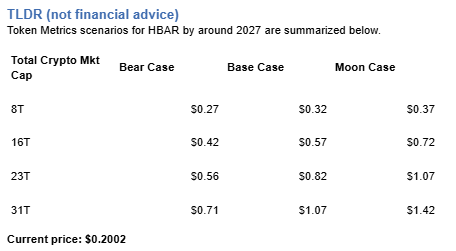
The projections below show how HBAR might perform under different market cap scenarios. While Hedera may have strong fundamentals, prudent portfolio construction balances L1 exposure across Ethereum, competing smart contract platforms, and Bitcoin to capture the sector without overexposure to any single chain's fate.
Disclosure
Educational purposes only, not financial advice. Crypto is volatile, do your own research and manage risk.
How to read it: Each band blends cycle analogues and market-cap share math with TA guardrails. Base assumes steady adoption and neutral or positive macro. Moon layers in a liquidity boom. Bear assumes muted flows and tighter liquidity.
TM Agent baseline:
Token Metrics lead metric for Hedera, cashtag $HBAR, is a TM Grade of 61.8%, which maps to Hold, and the trading signal is bearish, indicating short-term downward momentum. This means Token Metrics views $HBAR as having reasonably solid fundamentals but limited conviction for strong outperformance in the near term.
A concise long-term numeric view for a 12-month horizon: Token Metrics scenarios center around a range of about $0.06 to $0.18, with a base case near $0.10, reflecting steady ecosystem growth, moderate adoption of Hedera services, and continued enterprise partnerships. Implication: if Bitcoin and broader crypto risk appetite improve, $HBAR could revisit the higher end, while a risk-off market or slower-than-expected developer traction would keep it toward the lower bound.
Token Metrics scenarios span four market cap tiers, each representing different levels of crypto market maturity and liquidity:




These ranges illustrate potential outcomes for concentrated HBAR positions, but investors should weigh whether single-asset exposure matches their risk tolerance or whether diversified strategies better suit their objectives.
Professional investors across asset classes prefer diversified exposure over concentrated bets for good reason. Hedera faces numerous risks - technical vulnerabilities, competitive pressure, regulatory targeting, team execution failure - any of which could derail HBAR performance independent of broader market conditions. Token Metrics Indices spread this risk across one hundred tokens, ensuring no single failure destroys your crypto portfolio.
Diversification becomes especially critical in crypto given the sector's nascency and rapid evolution. Technologies and narratives that dominate today may be obsolete within years as the space matures. By holding HBAR exclusively, you're betting not only on crypto succeeding but on Hedera specifically remaining relevant. Index approaches hedge against picking the wrong horse while maintaining full crypto exposure.
Tax efficiency and rebalancing challenges also favor indices over managing concentrated positions. Token Metrics Indices handle portfolio construction, rebalancing, and position sizing systematically, eliminating the emotional and logistical burden of doing this manually with multiple tokens.
Early access to Token Metrics Indices
Hedera is a high-performance public ledger that emphasizes speed, low fees, and energy efficiency, positioning itself for enterprise and decentralized applications. It uses a unique Hashgraph consensus that enables fast finality and high throughput, paired with a council-governed model that targets real-world use cases like payments, tokenization, and decentralized identity.
HBAR is the native token used for fees, staking, and network security, and it supports smart contracts and decentralized file storage. Adoption draws from partnerships and integrations, though decentralization levels and reliance on institutional demand are often discussed in the community.
Token Metrics AI provides comprehensive context on Hedera's positioning and challenges.
Fundamental Grade: 81.08% (Community 74%, Tokenomics 100%, Exchange 100%, VC 59%, DeFi Scanner 85%).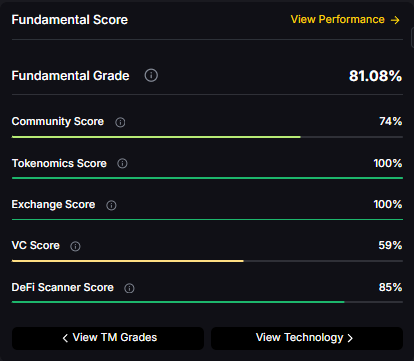
Technology Grade: 62.39% (Activity 58%, Repository 68%, Collaboration 74%, Security 56%, DeFi Scanner 85%).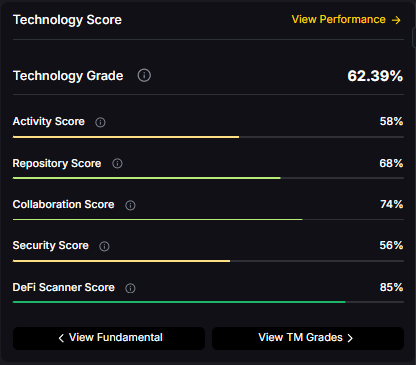
Can HBAR reach $1.00?
Yes. Based on the scenarios, HBAR could reach $1.00 or above in the higher tiers. The 23T tier projects $1.07 in the moon case and the 31T tier projects $1.42 in the moon case. Achieving this requires broad market cap expansion and Hedera maintaining competitive position. Not financial advice.
What price could HBAR reach in the moon case?
Moon case projections range from $0.37 at 8T to $1.42 at 31T. These scenarios assume maximum liquidity expansion and strong Hedera adoption. Diversified strategies aim to capture upside across multiple tokens rather than betting exclusively on any single moon scenario. Not financial advice.
What's the risk/reward profile for HBAR?
Risk and reward span from $0.27 in the lowest bear case to $1.42 in the highest moon case. Downside risks include regulatory or infrastructure setbacks and competitive pressure, while upside drivers include improved liquidity and enterprise adoption. Concentrated positions amplify both tails, while diversified strategies smooth outcomes.
Disclosure
Educational purposes only, not financial advice. Crypto is volatile, concentration amplifies risk, and diversification is a fundamental principle of prudent portfolio construction. Do your own research and manage risk appropriately.
%201.svg)
%201.svg)
Exchange tokens desrive value from trading volume and platform revenue, creating linkage between crypto market activity and LEO price action. LEO Token delivers utility through reduced trading fees and enhanced platform services on Bitfinex and iFinex across Ethereum and EOS. Token Metrics scenarios below model LEO outcomes across different total crypto market cap environments.
Disclosure
Educational purposes only, not financial advice. Crypto is volatile, do your own research and manage risk.
How to read it: Each band blends cycle analogues and market-cap share math with TA guardrails. Base assumes steady adoption and neutral or positive macro. Moon layers in a liquidity boom. Bear assumes muted flows and tighter liquidity.
TM Agent baseline: Token Metrics probabilities favor a modest range between about $5 and $15, with a base case around current levels near $9, conditional on exchange token utility remaining steady, and downside risk if centralized exchange macro pressure increases.
Token Metrics scenarios span four market cap tiers reflecting different crypto market maturity levels:




LEO Token is the native utility token of the Bitfinex and iFinex ecosystem, designed to provide benefits like reduced trading fees, enhanced lending and borrowing terms, and access to exclusive features on the platform. It operates on both Ethereum (ERC-20) and EOS blockchains, offering flexibility for users.
The primary role of LEO is to serve as a utility token within the exchange ecosystem, enabling fee discounts, participation in token sales, and other platform-specific advantages. Common usage patterns include holding LEO to reduce trading costs and utilizing it for enhanced platform services, positioning it primarily within the exchange token sector.
What gives LEO value?
LEO accrues value through reduced trading fees and enhanced platform services within the Bitfinex and iFinex ecosystem. Demand drivers include exchange usage and access to platform features, while supply dynamics follow the token’s exchange utility design. Value realization depends on platform activity and user adoption.
What price could LEO reach in the moon case?
Moon case projections range from $14.48 at 8T to $43.63 at 31T. These scenarios require maximum market cap expansion and strong exchange activity. Not financial advice.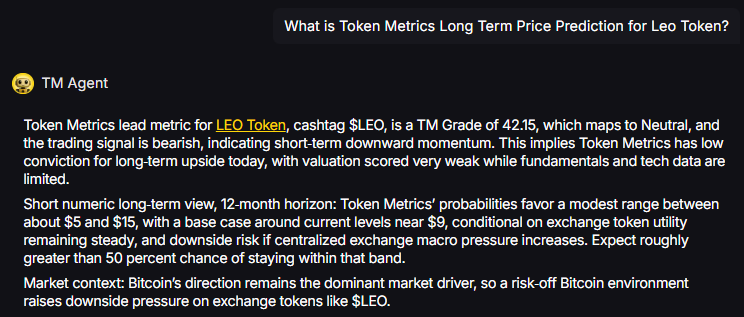
Curious how these forecasts are made? Token Metrics delivers LEO on-chain grades, forecasts, and deep research on 6,000+ tokens. Instantly compare fundamentals, on-chain scores, and AI-powered predictions.
Disclosure
Educational purposes only, not financial advice. Crypto is volatile, do your own research and manage risk.
%201.svg)
%201.svg)
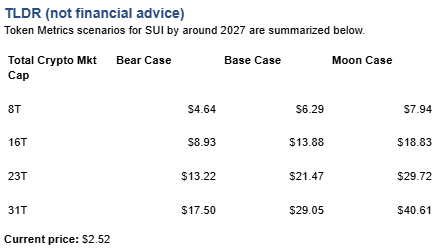
Layer 1 tokens like Sui represent bets on specific blockchain architectures winning developer and user mindshare. SUI carries both systematic crypto risk and unsystematic risk from Sui's technical roadmap execution and ecosystem growth. Multi-chain thesis suggests diversifying across several L1s rather than concentrating in one, since predicting which chains will dominate remains difficult.
The projections below show how SUI might perform under different market cap scenarios. While Sui may have strong fundamentals, prudent portfolio construction balances L1 exposure across Ethereum, competing smart contract platforms, and Bitcoin to capture the sector without overexposure to any single chain's fate.
Disclosure
Educational purposes only, not financial advice. Crypto is volatile, do your own research and manage risk.
Each band blends cycle analogues and market-cap share math with TA guardrails. Base assumes steady adoption and neutral or positive macro. Moon layers in a liquidity boom. Bear assumes muted flows and tighter liquidity.
TM Agent baseline: Token Metrics lead metric for Sui, cashtag $SUI, is a TM Grade of 67.4%, which maps to a Hold, and the trading signal is bearish, indicating short-term downward momentum. This suggests Token Metrics sees $SUI as having reasonable fundamentals but not yet strong conviction for substantial outperformance, while near-term momentum is negative and could limit rallies. Market context, brief: Bitcoin’s price direction is currently the primary market driver, and a risk-off Bitcoin environment increases downside pressure on layer-1 tokens like $SUI.
Professional investors across asset classes prefer diversified exposure over concentrated bets for good reason. Sui faces numerous risks - technical vulnerabilities, competitive pressure, regulatory targeting, team execution failure - any of which could derail SUI performance independent of broader market conditions. Token Metrics Indices spread this risk across one hundred tokens, ensuring no single failure destroys your crypto portfolio.
Diversification becomes especially critical in crypto given the sector's nascency and rapid evolution. Technologies and narratives that dominate today may be obsolete within years as the space matures. By holding SUI exclusively, you're betting not only on crypto succeeding but on Sui specifically remaining relevant. Index approaches hedge against picking the wrong horse while maintaining full crypto exposure.
Early access to Token Metrics Indices
Token Metrics scenarios span four market cap tiers, each representing different levels of crypto market maturity and liquidity:



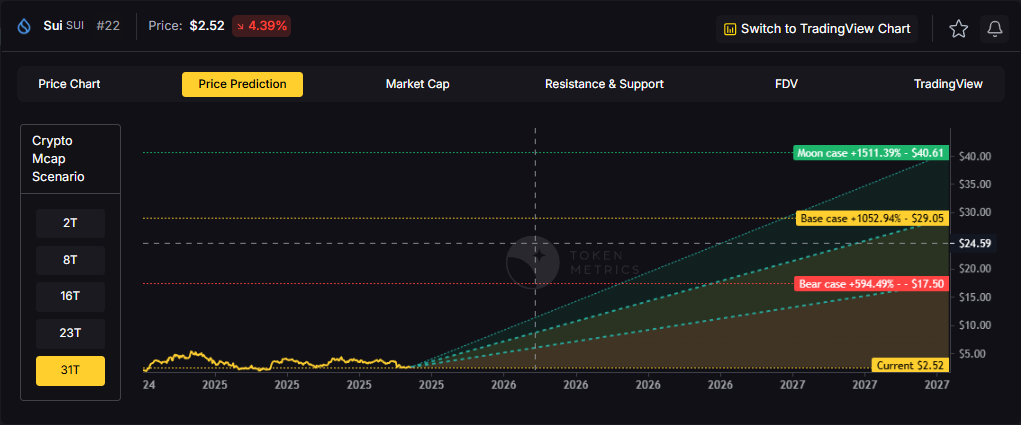
These ranges illustrate potential outcomes for concentrated SUI positions, but investors should weigh whether single-asset exposure matches their risk tolerance or whether diversified strategies better suit their objectives.
Sui is a layer-1 blockchain network designed for general-purpose smart contracts and scalable user experiences. It targets high throughput and fast settlement, aiming to support applications that need low-latency interactions and horizontal scaling.
SUI is the native token used for transaction fees and staking, aligning validator incentives and securing the network. It underpins activity across common crypto sectors such as NFTs and DeFi while the ecosystem builds developer tooling and integrations.
Vision: Sui aims to create a highly scalable and low-latency blockchain platform that enables seamless user experiences for decentralized applications. Its vision centers on making blockchain technology accessible and efficient for mainstream applications by removing traditional bottlenecks in transaction speed and cost.
Problem: Many existing blockchains face trade-offs between scalability, security, and decentralization, often resulting in high fees and slow transaction finality during peak usage. This limits their effectiveness for applications requiring instant settlement, frequent interactions, or large user bases, such as games or social platforms. Sui addresses the need for a network that can scale horizontally without sacrificing speed or cost-efficiency.
Solution: Sui uses a unique object-centric blockchain model and the Move programming language to enable parallel transaction processing, allowing high throughput and instant finality for many operations. Its consensus mechanism, Narwhal and Tusk, is optimized for speed and scalability by decoupling transaction dissemination from ordering. The network supports smart contracts, NFTs, and decentralized applications, with an emphasis on developer ease and user experience. Staking is available for network security, aligning with common proof-of-stake utility patterns.
Market Analysis: Sui competes in the layer-1 blockchain space with platforms like Solana, Avalanche, and Aptos, all targeting high-performance decentralized applications. It differentiates itself through its object-based data model and parallel execution, aiming for superior scalability in specific workloads. Adoption drivers include developer tooling, ecosystem incentives, and integration with wallets and decentralized exchanges. The broader market for high-throughput blockchains is driven by demand for scalable Web3 applications, though it faces risks from technical complexity, regulatory uncertainty, and intense competition.
Fundamental Grade: 77.60% (Community 80%, Tokenomics 60%, Exchange 100%, VC 76%, DeFi Scanner 75%).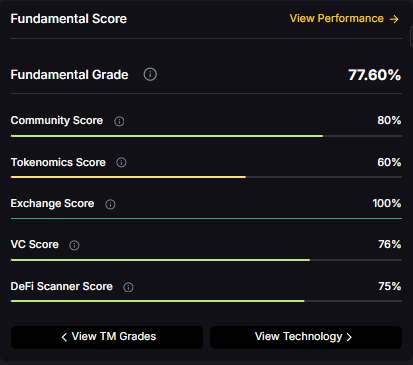
Technology Grade: 79.06% (Activity 77%, Repository 72%, Collaboration 89%, Security N/A, DeFi Scanner 75%).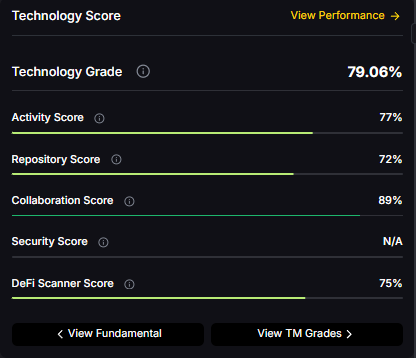
Token Metrics empowers you to analyze Sui and hundreds of digital assets with AI-driven ratings, on-chain and fundamental data, and index solutions to manage portfolio risk smartly in a rapidly evolving crypto market.
What price could SUI reach in the moon case?
Moon case projections range from $7.94 at 8T to $40.61 at 31T. These scenarios assume maximum liquidity expansion and strong Sui adoption. Diversified strategies aim to capture upside across multiple tokens rather than betting exclusively on any single moon scenario. Not financial advice.
What's the risk/reward profile for SUI?
Risk/reward spans from $4.64 to $40.61. Downside risks include regulatory pressure and competitive displacement, while upside drivers include ecosystem growth and favorable liquidity. Concentrated positions amplify both tails, while diversified strategies smooth outcomes.
What are the biggest risks to SUI?
Key risks include regulatory actions, technical issues, competitive pressure from other L1s, and adverse market liquidity. Concentrated SUI positions magnify exposure to these risks. Diversified strategies spread risk across tokens with different profiles, reducing portfolio vulnerability to any single failure point.
Disclosure
Educational purposes only, not financial advice. Crypto is volatile, concentration amplifies risk, and diversification is a fundamental principle of prudent portfolio construction. Do your own research and manage risk appropriately.
%201.svg)
%201.svg)
Location data powers modern products: discovery, logistics, analytics, and personalized experiences all lean on accurate mapping services. The Google Maps API suite is one of the most feature-rich options for embedding maps, geocoding addresses, routing vehicles, and enriching UX with Places and Street View. This guide breaks the platform down into practical sections—what each API does, how to get started securely, design patterns to control costs and latency, and where AI can add value.
The Maps Platform is modular: you enable only the APIs and SDKs your project requires. Key components include:
Each API exposes different latency, quota, and billing characteristics. Plan around the functional needs (display vs. heavy batch geocoding vs. real-time routing).
Begin in the Google Cloud Console: create or select a project, enable the specific Maps Platform APIs your app requires, and generate an API key. Key operational steps:
Authentication and identity management are foundational—wider access means higher risk of unexpected charges and data leakage.
Successful integrations optimize performance, cost, and reliability. Consider these patterns:
The Maps Platform uses a pay-as-you-go model with billing tied to API calls, SDK sessions, or map loads depending on the product. To control costs:
Budgeting requires monitoring real usage patterns and aligning product behavior (e.g., map refresh frequency) with cost objectives.
Combining location APIs with machine learning unlocks advanced features: predictive ETA models, demand heatmaps, intelligent geofencing, and dynamic routing that accounts for historic traffic patterns. AI models can also enrich POI categorization from Places API results or prioritize search results based on user intent.
For teams focused on research and signals, AI-driven analytical tools can help surface patterns from large location datasets, cluster user behavior, and integrate external data feeds for richer context. Tools built for crypto and on-chain analytics illustrate how API-driven datasets can be paired with models to create actionable insights in other domains—similarly, map and location data benefit from model-driven enrichment that remains explainable and auditable.
Build Smarter Crypto Apps & AI Agents with Token Metrics
Token Metrics provides real-time prices, trading signals, and on-chain insights all from one powerful API. Grab a Free API Key
Google offers a free usage tier and a recurring monthly credit for Maps Platform customers. Beyond the free allocation, usage is billed based on API calls, map loads, or SDK sessions. Monitor your project billing and set alerts to avoid unexpected charges.
The Places API provides address and place autocomplete features tailored for UX-focused address entry. For server-side address validation or bulk geocoding, pair it with Geocoding APIs and implement server-side caching.
Apply application restrictions (HTTP referrers for web, package name & SHA-1 for Android, bundle ID for iOS) and limit the key to only the required APIs. Rotate keys periodically and keep production keys out of client-side source control when possible.
Yes—the Directions and Distance Matrix APIs support routing and travel-time estimates. For large-scale fleet optimization, consider server-side batching, rate-limit handling, and hybrid solutions that combine routing APIs with custom optimization logic to manage complexity and cost.
Common issues include unbounded API keys, lack of caching for geocoding, excessive map refreshes that drive costs, and neglecting offline/mobile behavior. Planning for quotas, testing under realistic loads, and instrumenting telemetry mitigates these pitfalls.
This article is for educational and technical information only. It does not constitute financial, legal, or professional advice. Evaluate features, quotas, and pricing on official Google documentation and consult appropriate professionals for specific decisions.
%201.svg)
%201.svg)
Discord's API is the backbone of modern community automation, moderation, and integrations. Whether you're building a utility bot, connecting an AI assistant, or streaming notifications from external systems, understanding the Discord API's architecture, constraints, and best practices helps you design reliable, secure integrations that scale.
The Discord API exposes two main interfaces: the Gateway (a persistent WebSocket) for real-time events and the REST API for one-off requests such as creating messages, managing channels, and configuring permissions. Together they let developers build bots and services that respond to user actions, post updates, and manage server state.
Key concepts to keep in mind:
Authentication is based on tokens. Bots use a bot token (issued in the Discord Developer Portal) to authenticate both the Gateway and REST calls. When building or auditing a bot, treat tokens like secrets: rotate them when exposed and store them securely in environment variables or a secrets manager.
Intents let you opt-in to categories of events. For example, message content intent is required to read message text in many cases. Use the principle of least privilege: request only the intents you need to reduce data exposure and improve performance.
Practical steps:
Rate limits are enforced per route and per global bucket. Familiarize yourself with the headers returned by the REST API (X-RateLimit-Limit, X-RateLimit-Remaining, X-RateLimit-Reset) and adopt respectful retry strategies. For Gateway connections, avoid rapid reconnects; follow exponential backoff and obey the recommended identify rate limits.
Design patterns to improve resilience:
Webhooks are lightweight for sending messages into channels without a bot token and are excellent for notifications from external systems. Interactions and slash commands provide structured, discoverable commands that integrate naturally into the Discord UI.
Best practices when using webhooks and interactions:
Security goes beyond token handling. Consider these areas:
Combining Discord bots with AI or external data APIs can produce helpful automation, moderation aids, or analytics dashboards. When integrating, separate concerns: keep the Discord-facing layer thin and stateless where possible, and offload heavy processing to dedicated services.
For crypto- and market-focused integrations, external APIs can supply price feeds, on-chain indicators, and signals which your bot can surface to users. AI-driven research platforms such as Token Metrics can augment analysis by providing structured ratings and on-chain insights that your integration can query programmatically.
Build Smarter Crypto Apps & AI Agents with Token Metrics
Token Metrics provides real-time prices, trading signals, and on-chain insights all from one powerful API. Grab a Free API Key
Begin by creating an application in the Discord Developer Portal, add a bot user, and generate a bot token. Choose a client library (for example discord.js, discord.py alternatives) to handle Gateway and REST interactions. Test in a private server before inviting to production servers.
Intents are event categories that determine which events the Gateway will send to your bot. Enable only the intents your features require. Some intents, like message content, are privileged and require justification for larger bots or those in many servers.
Respect rate-limit headers, use client libraries that implement request queues, batch operations when possible, and shard your bot appropriately. Implement exponential backoff for retries and monitor request patterns to identify hotspots.
Webhooks are simpler for sending messages from external systems because they don't require a bot token and have a low setup cost. Bots are required for interactive features, slash commands, moderation, and actions that require user-like behavior.
Validate interaction signatures using Discord's public key. Verify timestamps to prevent replay attacks and ensure your endpoint only accepts expected request types. Keep validation code in middleware for consistency.
This article is educational and technical in nature. It does not provide investment, legal, or financial advice. Implementations described here focus on software architecture, integration patterns, and security practices; adapt them to your own requirements and compliance obligations.
%201.svg)
%201.svg)
APIs power much of the software and services we use every day, but the acronym itself can seem abstract to newcomers. This guide answers the simple question "what does API stand for," explains the main types and patterns, and shows how developers, analysts, and researchers use APIs—especially in data-rich fields like crypto and AI—to access information and automate workflows.
API stands for Application Programming Interface. In practice, an API is a set of rules and protocols that lets one software component request services or data from another. It defines how requests should be formatted, what endpoints are available, what data types are returned, and which authentication methods are required.
Think of an API as a contract between systems: the provider exposes functionality or data, and the consumer calls that functionality using an agreed syntax. This contract enables interoperability across languages, platforms, and teams without sharing internal implementation details.
APIs come in several flavors depending on purpose and architecture. Understanding these helps you choose the right integration approach:
In domains like crypto, API types often include REST endpoints for historical data, WebSocket endpoints for live market updates, and specialized endpoints for on-chain data and analytics.
APIs unlock automation and integration across many workflows. Typical examples include:
For researchers and developers in crypto and AI, APIs enable programmatic access to prices, on-chain metrics, and model outputs. Tools that combine multiple data sources through APIs can accelerate analysis while maintaining reproducibility.
APIs must be designed with security and reliability in mind. Key considerations include:
Designing or choosing APIs with clear documentation, sandbox environments, and predictable SLAs reduces integration friction and downstream maintenance effort.
Build Smarter Crypto Apps & AI Agents with Token Metrics
Token Metrics provides real-time prices, trading signals, and on-chain insights all from one powerful API. Grab a Free API Key
API stands for Application Programming Interface. It is a defined set of rules that enables software to communicate and exchange data or functionality with other software components.
An API is a specification for interaction; a library or SDK is an implementation that exposes an API in a specific programming language. Libraries call APIs internally or provide convenience wrappers for API calls.
Use REST for simple, resource-oriented endpoints and predictable cacheable interactions. Use GraphQL when clients require flexible, tailored queries and want to minimize round trips for composite data needs.
Rate limits cap how many requests a client can make in a given period. Respecting limits with caching and backoff logic prevents service disruption and helps maintain reliable access.
Yes. Streaming and WebSocket APIs can deliver low-latency data feeds that serve as inputs to real-time models, while REST endpoints supply bulk or historical datasets used for training and backtesting.
Integration platforms, API gateways, and orchestration tools manage authentication, rate limiting, retries, and transformations. For crypto and AI workflows, data aggregation services and programmatic APIs speed analysis.
Evaluate documentation, uptime reports, data coverage, authentication methods, and community usage. Platforms that combine market, on-chain, and research signals are especially useful for analytical workflows.
Official style guides, API design books, and public documentation from major providers (Google, GitHub, Stripe) offer practical patterns for versioning, security, and documentation.
Disclaimer: This article is educational and informational only. It does not constitute financial, legal, or investment advice. Readers should perform independent research and consult appropriate professionals for their specific needs.

%201.svg)
%201.svg)
ChatGPT API has become a foundational tool for building conversational agents, content generation pipelines, and AI-powered features across web and mobile apps. This guide walks through how the API works, common integration patterns, cost and performance considerations, prompt engineering strategies, and security and compliance checkpoints — all framed to help developers design reliable, production-ready systems.
The ChatGPT API exposes a conversational, instruction-following model through RESTful endpoints. It accepts structured inputs (messages, system instructions, temperature, max tokens) and returns generated messages and usage metrics. Key capabilities include multi-turn context handling, role-based prompts (system, user, assistant), and streaming responses for lower perceived latency.
When evaluating the API for a project, consider three high-level dimensions: functional fit (can it produce the outputs you need?), operational constraints (latency, throughput, rate limits), and cost model (token usage and pricing). Structuring experiments around these dimensions produces clearer decisions than ad-hoc prototyping.
At a technical level, the API exchanges conversational messages composed of roles and content. The model's input size is measured in tokens, not characters; both prompts and generated outputs consume tokens. Developers must account for:
Token-awareness is essential for cost control and designing concise prompts. Tools exist to estimate token counts for given strings; include these estimates in batching and truncation logic to prevent failed requests due to exceeding the context window.
Common patterns for integrating the ChatGPT API map to different functional requirements:
Select a pattern based on latency tolerance, concurrency requirements, and the need to control outputs with additional logic or verifiable sources.
Pricing for ChatGPT-style APIs typically ties to token usage and model selection. For production systems, optimize costs and performance by:
Measure end-to-end latency including network, model inference, and application processing. Use streaming when user-perceived latency matters; otherwise, batch requests for throughput efficiency.
Robust ChatGPT API usage blends engineering discipline with iterative evaluation:
Adopt iterative prompt tuning: A/B different system instructions, sampling temperatures, and max tokens while measuring relevance, correctness, and safety against representative datasets.
Build Smarter Crypto Apps & AI Agents with Token Metrics
Token Metrics provides real-time prices, trading signals, and on-chain insights all from one powerful API. Grab a Free API Key
The ChatGPT API is a conversational model endpoint for generating text based on messages and instructions. Use it when you need flexible, context-aware text generation such as chatbots, summarization, or creative writing assistants.
Tokens measure both input and output size. Longer prompts and longer responses increase token counts, which raises cost and can hit the model's context window limit. Optimize prompts and truncate history when necessary.
Implement client-side throttling, request queuing, exponential backoff on 429 responses, and prioritize critical requests. Monitor usage patterns and adjust concurrency to avoid hitting provider limits.
Start with a clear system instruction to set tone and constraints, use examples for format guidance, keep user prompts concise, and test iteratively. Templates and guardrails reduce variability in outputs.
Secure API keys (do not embed in client code), encrypt data in transit and at rest, anonymize sensitive user data when possible, and review provider data usage policies. Apply access controls and rotate keys periodically.
Use streaming to improve perceived responsiveness for chat-like experiences or long outputs. Streaming reduces time-to-first-token and allows progressive rendering in UIs.
This article is for informational and technical guidance only. It does not constitute legal, compliance, or investment advice. Evaluate provider terms and conduct your own testing before deploying models in production.

%201.svg)
%201.svg)
The OpenAI API has become a foundation for building modern AI applications, from chat assistants to semantic search and generative agents. This post breaks down how the API works, core endpoints, implementation patterns, operational considerations, and practical tips to get reliable results while managing cost and risk.
The OpenAI API exposes pre-trained and fine-tunable models through RESTful endpoints. At a high level, you send text or binary payloads and receive structured responses — completions, chat messages, embeddings, or file-based fine-tune artifacts. Communication is typically via HTTPS with JSON payloads. Authentication uses API keys scoped to your account, and responses include usage metadata to help with monitoring.
Understanding the data flow is useful: client app → API request (model, prompt, params) → model inference → API response (text, tokens, embeddings). Latency depends on model size, input length, and concurrency. Many production systems put the API behind a middleware layer to handle retries, caching, and prompt templating.
The API surface typically includes several core capabilities you should know when planning architecture:
Choosing the right endpoint depends on the use case: embeddings for search/indexing, chat for conversational interfaces, and fine-tuning for repetitive, domain-specific prompts where consistency matters.
Design patterns and practical tweaks reduce friction in real-world systems. Here are tested approaches:
For development workflows, maintain separate API keys and quotas for staging and production, and log both prompts and model responses (with privacy controls) to enable debugging and iterative improvement.
Operational concerns are often the difference between a prototype and a resilient product. Key considerations include:
Instrumenting observability — latency, error rates, token counts per request — lets you correlate model choices with operational cost and end-user experience.
Build Smarter Crypto Apps & AI Agents with Token Metrics
Token Metrics provides real-time prices, trading signals, and on-chain insights all from one powerful API. Grab a Free API Key
Common issues include prompt ambiguity, hallucinations, token truncation, and rate-limit throttling. Mitigation strategies:
Run adversarial tests to discover brittle prompts and incorporate guardrails in your application logic.
For scale, separate concerns into layers: ingestion, retrieval/indexing, inference orchestration, and post-processing. Use a vector database for embeddings, a message queue for burst handling, and server-side orchestration for prompt composition and retries. Edge caching for static outputs reduces repeated calls for common queries.
Consider hybrid strategies where smaller models run locally for simple tasks and the API is used selectively for high-value or complex inferences to balance cost and latency.
Most implementations use API keys sent in an Authorization header. Keys must be protected server-side. Rotate keys periodically and restrict scopes where supported.
Embedding-optimized models produce dense vectors for semantic tasks. Chat or completion models prioritize dialogue coherence and instruction-following. Select based on task: search and retrieval use embeddings; conversational agents use chat endpoints.
Use caching, smaller models for simple tasks, pre-compute embeddings for common queries, and implement warm-up strategies. Also evaluate regional endpoints and keep payload sizes minimal to reduce round-trip time.
Curate high-quality, representative datasets. Keep prompts consistent between fine-tuning and inference. Monitor for overfitting and validate on held-out examples to ensure generalization.
Track token usage by endpoint and user journey, set per-key quotas, and sample outputs rather than logging everything. Use batching and caching to reduce repeated calls, and enforce strict guards on long or recursive prompts.
Yes, with careful design. Add retries, fallbacks, safety checks, and human-in-the-loop reviews for high-stakes outcomes. Maintain SLAs that reflect model performance variability and instrument monitoring for regressions.
This article is for educational purposes only. It explains technical concepts, implementation patterns, and operational considerations related to the OpenAI API. It does not provide investment, legal, or regulatory advice. Always review provider documentation and applicable policies before deploying systems.
%201.svg)
%201.svg)
DeepSeek API has emerged as a specialized toolkit for developers and researchers who need granular, semantically rich access to crypto-related documents, on-chain data, and developer content. This article breaks down how the DeepSeek API works, common integration patterns, practical research workflows, and how AI-driven platforms can complement its capabilities without making investment recommendations.
The DeepSeek API is designed to index and retrieve contextual information across heterogeneous sources: whitepapers, GitHub repos, forum threads, on-chain events, and more. Unlike keyword-only search, DeepSeek focuses on semantic matching—returning results that align with the intent of a query rather than only literal token matches.
Key capabilities typically include:
Integrating the DeepSeek API into a product follows common design patterns depending on latency and scale requirements:
When building integrations, consider privacy, data retention, and whether you need to host a private index versus relying on a hosted DeepSeek endpoint.
Researchers using the DeepSeek API can follow a repeatable workflow to ensure comprehensive coverage and defensible results:
For reproducible experiments, version your query templates and save query-result sets alongside analysis notes.
Understanding the constraints of a semantic retrieval API is essential for reliable outputs:
Build Smarter Crypto Apps & AI Agents with Token Metrics
Token Metrics provides real-time prices, trading signals, and on-chain insights all from one powerful API. Grab a Free API Key
DeepSeek typically indexes a mix of developer-centric and community data: GitHub, whitepapers, documentation sites, forums, and on-chain events. Exact coverage depends on the provider's ingestion pipeline and configuration options you choose when provisioning indexes.
Embeddings map text into vector space where semantic similarity becomes measurable as geometric closeness. This allows queries to match documents by meaning rather than shared keywords, improving recall for paraphrased or conceptually related content.
While DeepSeek is optimized for textual retrieval, many deployments support linking to structured on-chain records. A common pattern is to return document results with associated on-chain references (contract addresses, event IDs) so downstream systems can fetch transaction-level details from block explorers or node APIs.
Use a combination of automated metrics (precision@k, recall sampling) and human review. For technical subjects, validate excerpts against source code, transaction logs, and authoritative docs to avoid false positives driven by surface-level similarity.
Keep retrieved context concise and relevant: prioritize high-salience chunks, include provenance for factual checks, and use retrieval augmentation to ground model outputs. Also, monitor token usage and prefer compressed summaries for long sources.
DeepSeek is focused on semantic retrieval and contextual search, while other crypto APIs may prioritize raw market data, on-chain metrics, or analytics dashboards. Combining DeepSeek-style search with specialized APIs (for price, on-chain metrics, or signals) yields richer tooling for research workflows.
Explore provider docs and example use cases. For integrated AI research and ratings, see Token Metrics which demonstrates how semantic retrieval can be paired with model-driven analysis for structured insights.
This article is for informational and technical education only. It does not constitute investment advice, endorsements, or recommendations. Evaluate tools and data sources critically and consider legal and compliance requirements before deployment.

%201.svg)
%201.svg)
Fabric API is a cornerstone for developers building permissioned blockchain solutions with Hyperledger Fabric. This article explains what Fabric APIs are, how they fit into Fabric's architecture, practical integration patterns, and how to evaluate tooling when you need reliable programmatic access to Fabric networks.
The term "Fabric API" broadly refers to the programmatic interfaces and SDKs that allow applications to interact with a Hyperledger Fabric network. These interfaces expose capabilities such as submitting transactions, querying ledger state, managing identities via Fabric CA, and deploying or invoking chaincode (smart contracts). For enterprise use cases—supply chain auditing, tokenized assets, or confidential data flows—the Fabric API is the gateway between business logic and the distributed ledger.
Key characteristics of Fabric APIs include:
Interacting with Fabric typically involves several layers. Understanding these helps you choose the right API surface for your application:
Choosing how to surface Fabric functionality depends on risk, latency, and operational model. Common patterns include:
Cross-cutting concerns to design for:
Follow a structured approach when integrating with Fabric networks:
Testing tips: use channel-level mock data, replay recorded endorsement responses for deterministic unit tests, and simulate peer failures to validate client retry logic.
Build Smarter Crypto Apps & AI Agents with Token Metrics
Token Metrics provides real-time prices, trading signals, and on-chain insights all from one powerful API. Grab a Free API Key
The Fabric API comprises SDKs, the Gateway API, chaincode interfaces, and CA endpoints that let applications manage identities, submit transactions, and query ledger state on Hyperledger Fabric networks.
Use the Gateway API for simpler, high-level transaction workflows and reduced configuration. Choose direct SDKs when you need low-level control over discovery, endorsement policies, or custom peer selection logic.
Yes. Implement a secure REST proxy or API gateway to translate HTTP calls to Fabric SDK operations. This adds flexibility for web/mobile clients but requires careful identity and input validation.
Use Fabric CA for certificate issuance, adopt hardware-backed key stores where possible, separate admin and app roles, and rotate/revoke certificates according to policy. Avoid embedding private keys in client-side code.
Instrument SDK calls, capture latency and endorsement statistics, log chaincode events, and integrate with observability stacks (Prometheus/Grafana). Monitor peer health and orderer topology to correlate API issues with network state.
Common issues include endorsement mismatches due to non-deterministic chaincode, exposing credentials to clients, insufficient testing of policy changes, and lacking observability for transaction failures.
Disclaimer: This article is educational and technical in nature. It does not provide financial, legal, or regulatory advice. Implementations should be validated against your organization's compliance and security requirements.
%201.svg)
%201.svg)
REST APIs are the connective tissue of modern web and mobile applications. Whether you're integrating services, building microservices, or exposing data for AI agents, a clear grasp of REST API principles helps you design interfaces that are maintainable, performant, and secure. This guide walks through the core concepts, practical design patterns, authentication and security considerations, and tooling that make REST APIs reliable in production.
REST (Representational State Transfer) is an architectural style that uses standard HTTP verbs and status codes to manipulate resources. Key tenets include:
Understanding these principles helps when choosing between REST, GraphQL, or RPC for a given use case. REST is well-suited for CRUD-style operations, caching, and wide compatibility with HTTP tooling.
Good API design starts with modeling resources and their relationships. Practical patterns include:
Design with backward compatibility in mind: deprecate endpoints with clear timelines, and prefer additive changes over breaking ones.
Security is non-negotiable. Common, interoperable mechanisms include:
Also consider CORS policies, input validation, and strict output encoding to reduce injection risks. Implement principle of least privilege for every endpoint and role.
Operational maturity requires monitoring and testing across the lifecycle. Focus on these areas:
Tooling choices—Postman, Insomnia, Swagger UI, or automated CI checks—help maintain quality as the API evolves. For AI-driven integrations, exposing well-documented JSON schemas and stable endpoints is critical.
Build Smarter Crypto Apps & AI Agents with Token Metrics
Token Metrics provides real-time prices, trading signals, and on-chain insights all from one powerful API. Grab a Free API Key
REST is ideal for resource-oriented services where standard HTTP semantics are beneficial. Choose REST when caching, simplicity, wide client compatibility, and predictable CRUD semantics are priorities. For highly dynamic queries, consider GraphQL as a complement rather than a replacement.
Version endpoints, use feature flags, and publish changelogs with migration guides. Prefer additive changes (new fields, new endpoints) and give clients time to migrate before removing legacy behavior.
Match the method to the use case: API keys for server-to-server integrations, OAuth 2.0 for delegated user access, and JWTs for stateless session claims. Always layer these with TLS and short token lifetimes.
Enforce per-key and per-IP limits, surface quota headers, and provide graceful 429 responses with a Retry-After header. Use adaptive throttling to protect critical downstream systems.
Adopt OpenAPI for specs, use Postman or Swagger UI for exploratory testing, integrate contract tests into CI, and deploy observability stacks (Prometheus, Grafana, OpenTelemetry) to monitor behavior in production.
This article is for educational and technical guidance only. It does not constitute legal, security, or operational advice. Evaluate risks and compliance requirements against your own environment before implementing changes.

%201.svg)
%201.svg)
APIs (application programming interfaces) are the connective tissue of modern software. Whether you use mobile apps, web services, or AI agents, APIs let systems exchange data and trigger actions without sharing inner code. This guide explains what an API is, how APIs work, why they matter in crypto and AI, and practical steps to evaluate and integrate them.
An API is a set of rules and definitions that allow one software program to interact with another. At its core, an API defines endpoints (URLs or RPC methods), expected inputs, responses, and error formats. APIs abstract complexity: a developer can request a price, submit a transaction, or call a machine-learning model without needing the provider’s internal implementation details.
Common API types include:
APIs expose functionality through well-documented endpoints. Each endpoint accepts parameters and returns structured responses, typically JSON or protocol buffers. Key concepts include authentication, rate limiting, and versioning:
Security best practices involve TLS/HTTPS, least-privilege API keys, signing of critical requests, input validation to avoid injection attacks, and monitoring logs for unusual patterns. For sensitive operations (transactions, private data), prefer APIs that support granular permissions and replay protection.
APIs power many crypto and AI workflows. In crypto, APIs provide price feeds, historical market data, exchange order placement, blockchain node interactions, and on-chain analytics. For AI, APIs expose model inference, embeddings, and data pipelines that let applications integrate intelligent features without hosting models locally.
Use-case examples:
AI-driven research platforms and analytics providers can speed hypothesis testing by combining disparate APIs into unified datasets. For example, Token Metrics and similar services merge price, on-chain, and sentiment signals into actionable datasets for research workflows.
Selecting and integrating an API involves technical and operational checks. Use this checklist to assess suitability:
Integration tips:
Build Smarter Crypto Apps & AI Agents with Token Metrics
Token Metrics provides real-time prices, trading signals, and on-chain insights all from one powerful API. Grab a Free API Key
Several integration patterns appear repeatedly in production systems:
Choosing a pattern depends on timeliness, cost, and complexity. For exploratory work, start with REST endpoints and move to streaming once latency demands increase.
A web service is a specific type of API that uses network protocols (often HTTP) to provide interoperable machine-to-machine interaction. All web services are APIs, but not all APIs are web services (some are in-process libraries or platform-specific interfaces).
An endpoint is a specific URL or method that accepts requests and returns data or performs actions. Endpoints are typically documented with required parameters, response formats, and error codes.
Common methods include API keys, OAuth 2.0 flows for delegated access, and JSON Web Tokens (JWTs). Choose mechanisms that match your security needs and rotate credentials regularly.
Use REST for request/response interactions and batch queries. Use WebSockets (or similar streaming protocols) when you need continuous, low-latency updates such as live market data or notifications.
Use provider sandbox environments or testnet endpoints for blockchain calls. Mock external APIs during unit testing and run integration tests against staging keys to validate behavior without impacting production systems.
Yes. RESTful conventions, OpenAPI/Swagger documentation, and GraphQL schemas are common standards that improve discoverability and ease client generation. Following consistent naming, pagination, and error practices reduces onboarding friction.
Disclaimer: This article is for educational and informational purposes only. It explains technical concepts, implementation patterns, and evaluation criteria for APIs. It is not investment, legal, or security advice. Conduct your own due diligence before integrating third-party services.

 Create Your Free Account
Create Your Free Account9450 SW Gemini Dr
PMB 59348
Beaverton, Oregon 97008-7105 US
.svg)




.png)
Token Metrics Media LLC is a regular publication of information, analysis, and commentary focused especially on blockchain technology and business, cryptocurrency, blockchain-based tokens, market trends, and trading strategies.
Token Metrics Media LLC does not provide individually tailored investment advice and does not take a subscriber’s or anyone’s personal circumstances into consideration when discussing investments; nor is Token Metrics Advisers LLC registered as an investment adviser or broker-dealer in any jurisdiction.
Information contained herein is not an offer or solicitation to buy, hold, or sell any security. The Token Metrics team has advised and invested in many blockchain companies. A complete list of their advisory roles and current holdings can be viewed here: https://tokenmetrics.com/disclosures.html/
Token Metrics Media LLC relies on information from various sources believed to be reliable, including clients and third parties, but cannot guarantee the accuracy and completeness of that information. Additionally, Token Metrics Media LLC does not provide tax advice, and investors are encouraged to consult with their personal tax advisors.
All investing involves risk, including the possible loss of money you invest, and past performance does not guarantee future performance. Ratings and price predictions are provided for informational and illustrative purposes, and may not reflect actual future performance.



