Top Crypto Trading Platforms in 2025







%201.svg)
%201.svg)
Big news: We’re cranking up the heat on AI-driven crypto analytics with the launch of the Token Metrics API and our official SDK (Software Development Kit). This isn’t just an upgrade – it's a quantum leap, giving traders, hedge funds, developers, and institutions direct access to cutting-edge market intelligence, trading signals, and predictive analytics.
Crypto markets move fast, and having real-time, AI-powered insights can be the difference between catching the next big trend or getting left behind. Until now, traders and quants have been wrestling with scattered data, delayed reporting, and a lack of truly predictive analytics. Not anymore.
The Token Metrics API delivers 32+ high-performance endpoints packed with powerful AI-driven insights right into your lap, including:
Getting started with the Token Metrics API is simple:
At Token Metrics, we believe data should be decentralized, predictive, and actionable.
The Token Metrics API & SDK bring next-gen AI-powered crypto intelligence to anyone looking to trade smarter, build better, and stay ahead of the curve. With our official SDK, developers can plug these insights into their own trading bots, dashboards, and research tools – no need to reinvent the wheel.
%201.svg)
%201.svg)
Why 2026 Looks Bullish, And What It Could Mean for TRX
The crypto market is shifting toward a broadly bullish regime into 2026 as liquidity improves and risk appetite normalizes.
Regulatory clarity across major regions is reshaping the classic four-year cycle, flows can arrive earlier and persist longer.
Institutional access keeps expanding through ETFs and qualified custody, while L2 scaling and real-world integrations broaden utility.
Infrastructure maturity lowers frictions for capital, which supports deeper order books and more persistent participation.
This backdrop frames our scenario work for TRX.
The bands below map potential outcomes to different total crypto market sizes.
Use the table as a quick benchmark, then layer in live grades and signals for timing.
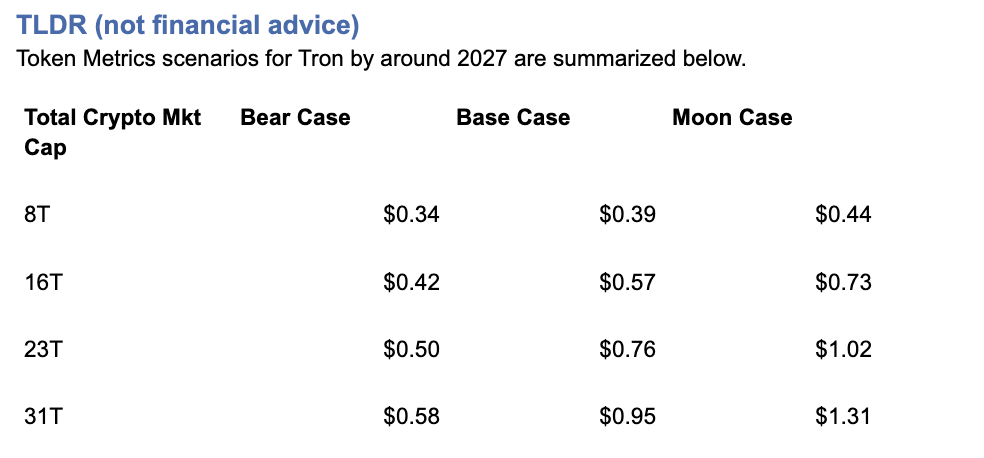
Current price: $0.2971.
How to read it: Each band blends cycle analogues and market-cap share math with TA guardrails. Base assumes steady adoption and neutral or positive macro. Moon layers in a liquidity boom. Bear assumes muted flows and tighter liquidity.
TM Agent baseline: Token Metrics TM Grade for $TRX is 19.06, which translates to a Strong Sell, and the trading signal is bearish, indicating short-term downward momentum.
Price context: $TRX is trading around $0.297, market cap rank #10, and is down about 11% over 30 days while up about 80% year-over-year, it has returned roughly 963% since the last trading signal flip.
Live details: Tron Token Details → https://app.tokenmetrics.com/en/tron
Buy TRX: https://www.mexc.com/acquisition/custom-sign-up?shareCode=mexc-2djd4
Scenario driven, outcomes hinge on total crypto market cap, higher liquidity and adoption lift the bands.
TM Agent gist: bearish near term, upside depends on a sustained risk-on regime and improvements in TM Grade and the trading signal.
Education only, not financial advice.
8T: 
16T: 
23T: 
Diversification matters.
Tron is compelling, yet concentrated bets can be volatile.
Token Metrics Indices hold TRX alongside the top one hundred tokens for broad exposure to leaders and emerging winners.
Our backtests indicate that owning the full market with diversified indices has historically outperformed both the total market and Bitcoin in many regimes due to diversification and rotation.
Get early access: https://docs.google.com/forms/d/1AnJr8hn51ita6654sRGiiW1K6sE10F1JX-plqTUssXk/preview
If your editor supports embeds, place a form embed here. Otherwise, include the link above as a button labeled Join Indices Early Access.
Tron is a smart-contract blockchain focused on low-cost, high-throughput transactions and cross-border settlement.
The network supports token issuance and a broad set of dApps, with an emphasis on stablecoin transfer volume and payments.
TRX is the native asset that powers fees and staking for validators and delegators within the network.
Developers and enterprises use the chain for predictable costs and fast finality, which supports consumer-facing use cases.
• Institutional and retail access expands with ETFs, listings, and integrations.
• Macro tailwinds from lower real rates and improving liquidity.
• Product or roadmap milestones such as upgrades, scaling, or partnerships.
• Macro risk-off from tightening or liquidity shocks.
• Regulatory actions or infrastructure outages.
• Concentration or validator economics and competitive displacement.
Unlock platform-wide intelligence on every major crypto asset. Use code ADVANCED20 at checkout for twenty percent off.
AI powered ratings on thousands of tokens for traders and investors.
Interactive TM AI Agent to ask any crypto question.
Indices explorer to surface promising tokens and diversified baskets.
Signal dashboards, backtests, and historical performance views.
Watchlists, alerts, and portfolio tools to track what matters.
Early feature access and enhanced research coverage.
Start with Advanced today → https://www.tokenmetrics.com/token-metrics-pricing
Can TRX reach $1?
Yes, the 23T moon case shows $1.02 and the 31T moon case shows $1.31, which imply a path to $1 in higher-liquidity regimes. Not financial advice.
Is TRX a good long-term investment
Outcome depends on adoption, liquidity regime, competition, and supply dynamics. Diversify and size positions responsibly.

Track live grades and signals: Token Details → https://app.tokenmetrics.com/en/tron
Join Indices Early Access: https://docs.google.com/forms/d/1AnJr8hn51ita6654sRGiiW1K6sE10F1JX-plqTUssXk/preview
Want exposure Buy TRX on MEXC → https://www.mexc.com/acquisition/custom-sign-up?shareCode=mexc-2djd4
Educational purposes only, not financial advice. Crypto is volatile, do your own research and manage risk.
Token Metrics delivers AI-powered crypto ratings, research, and portfolio tools for every level of investor and trader seeking an edge.
%201.svg)
%201.svg)
Bitcoin
TL;DR (not financial advice): Token Metrics scenarios put BTC between ~$177k–$219k in an $8T total crypto market, $301k–$427k at $16T, $425k–$635k at $24T, and $548k–$843k at $32T by ~2027.
Baseline long-term view from TM Agent: $100k–$250k if macro stays favorable; $20k–$40k downside in a prolonged risk-off regime.
→ Deep dive & live signals: Bitcoin Token Details
→ Want to buy BTC? Use our partner link: MEXC sign-up
Scenario-driven: BTC outcomes hinge on total crypto market cap. Higher aggregate liquidity/adoption = higher BTC bands.
Fundamentals strong: Fundamental Grade 89.53% (Tokenomics 100%, Exchange 100%, Community 84%).
Tech solid: Technology Grade 69.78% (Repo 79%, Collaboration 70%, Activity 63%).
TM Agent baseline: multi-year $100k–$250k with upside if institutions & macro cooperate; risk to $20k–$40k in a severe risk-off.
This article is education only; not financial advice.
Total Crypto Mkt Cap |
Bear Case |
Base Case |
Moon Case |
$8T |
$176,934 |
$197,959 |
$218,985 |
$16T |
$300,766 |
$363,842 |
$426,918 |
$24T |
$424,598 |
$529,725 |
$634,852 |
$32T |
$548,430 |
$695,608 |
$842,786 |
Current price when modeled: ~$115.6k.
How to read it: Each band blends cycle analogues + market-cap share math and applies TA guardrails.
The base path assumes steady ETF/treasury adoption and neutral-to-positive macro; moon adds a liquidity boom + accelerated institutional flows; bear assumes muted flows and tighter liquidity.
8T MCap Scenario

16T MCap Scenario

24T MCap Scenario

32T MCap Scenario

Spot ETF flows, corporate/treasury allocations, and global liquidity are the swing factors that push BTC between the $100k–$250k baseline and the higher scenario bands.
If real rates fall and risk appetite rises, the system can support $16T–$24T crypto, putting BTC’s base case in the $364k–$530k zone.
Programmatic issuance cuts keep the scarcity story intact; historically, post-halving windows have supported asymmetric upside as demand shocks meet slower new supply.
Fundamental Grade 89.53% with perfect Tokenomics and Exchange access supports liquidity and distribution.
Technology Grade 69.78% (Repo 79%, Collaboration 70%) signals a mature, continuously maintained codebase—even if raw dev “Activity” cycles with market phases.
With price recently around $115k, the $8T path implies a medium-term corridor of $177k–$219k if crypto caps stall near cycle mid.
Reclaims above prior weekly supply zones (mid-$100ks to high-$100ks) would bias toward the $16T track ($301k–$427k).
A macro/liquidity slump that undercuts weekly supports could revisit the TM Agent downside zone ($20k–$40k), though that would require a deep and sustained risk-off.
For live support/resistance levels and signals, open: Bitcoin Token Details.
Fundamental Grade: 89.53%
Community: 84%
Tokenomics: 100%
Exchange availability: 100%
DeFi Scanner: 77%
VC Score: N/A

Technology Grade: 69.78%
Activity: 63%
Repository: 79%
Collaboration: 70%
Security: N/A
DeFi Scanner: 77%

Interpretation: Liquidity/access + pristine token mechanics keep BTC the market’s base collateral; tech metrics reflect a conservative, security-first core with steady maintenance rather than hype-driven burst commits.
• ETF/retirement channel penetration broadens demand beyond crypto-native cohorts.
• Treasury adoption (corporates, macro funds) increases “digital collateral” utility.
• Macro easing / falling real yields can push total crypto mkt cap toward $16T–$24T.
• Global tightening (higher real rates, QT) compresses risk premiums.
• Regulatory shocks curtail flows or custody rails.
• Vol/liquidity pockets amplify drawdowns; deep retests remain possible.
Can BTC hit $200k–$250k?
Yes—those sit inside our $8T–$16T bands (base/mid), contingent on continued institutional adoption and constructive macro. Not guaranteed.
Could BTC reach $500k–$800k?
Those levels map to $24T–$32T total crypto scenarios (base → moon). They require a powerful liquidity cycle plus broader balance-sheet adoption.
What invalidates the bull case?
Sustained high real rates, policy tightening, or adverse regulation that throttles ETF/fiat rails—conditions aligned with the TM Agent $20k–$40k downside.
Track the live grade & signals: Bitcoin Token Details
Set alerts around key breakout/retest levels inside Token Metrics.
Want exposure? Consider our partner: Buy BTC on MEXC
Disclosure & disclaimer: This content is for educational purposes only and not financial advice. Cryptocurrency is volatile; do your own research and manage risk.
%201.svg)
%201.svg)
Cryptocurrency's digital nature creates unprecedented investment opportunities—24/7 global markets, instant transactions, and direct ownership without intermediaries.
But this same digital nature introduces unique security challenges absent from traditional investing.
You can't lose your stock certificates to hackers, but you absolutely can lose your cryptocurrency to theft, scams, or user error.
Industry estimates suggest billions of dollars in cryptocurrency are lost or stolen annually through hacks, phishing attacks, forgotten passwords, and fraudulent schemes.
For many prospective crypto investors, security concerns represent the primary barrier to entry.
"What if I get hacked?" "How do I keep my crypto safe?" "What happens if I lose my password?"
These aren't trivial concerns—they're legitimate questions demanding thoughtful answers before committing capital to digital assets.
Token Metrics AI Indices approach security holistically, addressing not just portfolio construction and performance but the entire ecosystem of risks facing crypto investors.
From selecting fundamentally secure cryptocurrencies to providing guidance on safe custody practices, Token Metrics prioritizes investor protection alongside return generation.
This comprehensive guide explores the complete landscape of crypto security risks, reveals best practices for protecting your investments, and demonstrates how Token Metrics' systematic approach enhances safety across multiple dimensions.
Exchange Hacks and Platform Vulnerabilities
Cryptocurrency exchanges—platforms where users buy, sell, and store digital assets—represent prime targets for hackers given the enormous value they custody.
History is littered with devastating exchange hacks including Mt. Gox (2014): 850,000 Bitcoin stolen, worth $450 million then, billions today; Coincheck (2018): $530 million in NEM tokens stolen; QuadrigaCX (2019): $190 million lost when founder died with only access to cold wallets; and FTX (2022): Collapse resulting in billions in customer losses.
These incidents highlight fundamental custody risks. When you hold cryptocurrency on exchanges, you don't truly control it—the exchange does.
The industry saying captures this reality: "Not your keys, not your coins." Exchange bankruptcy, hacking, or fraud can result in total loss of funds held on platforms.
Token Metrics addresses exchange risk by never directly holding user funds—the platform provides investment guidance and analysis, but users maintain custody of their assets through personal wallets or trusted custodians they select.
This architecture eliminates single-point-of-failure risks inherent in centralized exchange custody.
Private Key Loss and User Error
Unlike traditional bank accounts where forgotten passwords can be reset, cryptocurrency relies on cryptographic private keys providing sole access to funds.
Lose your private key, and your cryptocurrency becomes permanently inaccessible—no customer service department can recover it.
Studies suggest 20% of all Bitcoin (worth hundreds of billions of dollars) is lost forever due to forgotten passwords, discarded hard drives, or deceased holders without key succession plans.
This user-error risk proves particularly acute for non-technical investors unfamiliar with proper key management.
Token Metrics provides educational resources on proper key management, wallet selection, and security best practices.
The platform emphasizes that regardless of how well indices perform, poor personal security practices can negate all investment success.
Phishing, Social Engineering, and Scams
Crypto scams exploit human psychology rather than technical vulnerabilities.
Common schemes include phishing emails impersonating legitimate platforms, fake customer support targeting victims through social media, romance scams building relationships before requesting crypto, pump-and-dump schemes artificially inflating token prices, and fake investment opportunities promising unrealistic returns.
These scams succeed because they manipulate emotions—fear, greed, trust. Even sophisticated investors occasionally fall victim to well-crafted social engineering.
Token Metrics protects users by vetting all cryptocurrencies included in indices, filtering out known scams and suspicious projects.
The platform's AI analyzes on-chain data, code quality, team credentials, and community sentiment, identifying red flags invisible to casual investors. This comprehensive due diligence provides first-line defense against fraudulent projects.
Smart Contract Vulnerabilities
Many cryptocurrencies operate on smart contract platforms where code executes automatically.
Bugs in smart contract code can be exploited, resulting in fund loss. Notable incidents include the DAO hack (2016): $50 million stolen through smart contract vulnerability; Parity wallet bug (2017): $280 million frozen permanently; and numerous DeFi protocol exploits draining millions from liquidity pools.
Token Metrics' analysis evaluates code quality and security audits for projects included in indices.
The AI monitors for smart contract risks, deprioritizing projects with poor code quality or unaudited contracts. This systematic evaluation reduces but doesn't eliminate smart contract risk—inherent to DeFi investing.
Regulatory and Compliance Risks
Cryptocurrency's evolving regulatory landscape creates risks including sudden regulatory restrictions limiting trading or access, tax compliance issues from unclear reporting requirements, securities law violations for certain tokens, and jurisdictional complications from crypto's borderless nature.
Token Metrics monitors regulatory developments globally, adjusting index compositions when regulatory risks emerge.
If specific tokens face heightened regulatory scrutiny, the AI can reduce or eliminate exposure, protecting investors from compliance-related losses.
Understanding Wallet Types
Cryptocurrency storage options exist along a security-convenience spectrum. Hot wallets (software wallets connected to internet) offer convenience for frequent trading but increased hacking vulnerability.
Cold wallets (hardware wallets or paper wallets offline) provide maximum security but reduced convenience for active trading. Custodial wallets (exchanges holding keys) offer simplicity but require trusting third parties.
For Token Metrics investors, recommended approach depends on portfolio size and trading frequency.
Smaller portfolios with frequent rebalancing might warrant hot wallet convenience. Larger portfolios benefit from cold wallet security, moving only amounts needed for rebalancing to hot wallets temporarily.
Hardware Wallet Security
Hardware wallets—physical devices storing private keys offline—represent the gold standard for cryptocurrency security. Popular options include Ledger, Trezor, and others providing "cold storage" immunity to online hacking.
Best practices for hardware wallets include:
• Purchasing directly from manufacturers
• Never buying used
• Verifying device authenticity through manufacturer verification
• Storing recovery seeds securely (physical copies in safe locations)
• Using strong PINs and never sharing device access
For substantial Token Metrics allocations, hardware wallets prove essential.
The modest cost ($50-200) pales compared to security benefits for portfolios exceeding several thousand dollars.
Multi-Signature Security
Multi-signature (multisig) wallets require multiple private keys to authorize transactions—for example, requiring 2-of-3 keys. This protects against single-point-of-failure risks: if one key is compromised, funds remain secure; if one key is lost, remaining keys still enable access.
Advanced Token Metrics investors with substantial holdings should explore multisig solutions through platforms like Gnosis Safe or Casa.
While more complex to set up, multisig dramatically enhances security for large portfolios.
Institutional Custody Solutions
For investors with six-figure+ crypto allocations, institutional custody services provide professional-grade security including:
• Regulated custodians holding cryptocurrency with insurance
• Cold storage with enterprise security protocols
• Compliance with financial industry standards
Services like Coinbase Custody, Fidelity Digital Assets, and others offer insured custody for qualified investors.
While expensive (typically basis points on assets), institutional custody eliminates personal security burdens for substantial holdings.
Password Management and Two-Factor Authentication
Basic security hygiene proves critical for crypto safety.
Use unique, complex passwords for every exchange and platform—password managers like 1Password or Bitwarden facilitate this. Enable two-factor authentication (2FA) using authenticator apps (Google Authenticator, Authy) rather than SMS which can be intercepted.
Never reuse passwords across platforms. A data breach exposing credentials from one service could compromise all accounts using identical passwords. Token Metrics recommends comprehensive password management as foundational security practice.
Recognizing and Avoiding Phishing
Phishing attacks impersonate legitimate services to steal credentials. Red flags include emails requesting immediate action or login, suspicious sender addresses with subtle misspellings, links to domains not matching official websites, and unsolicited contact from "customer support."
Always navigate directly to platforms by typing URLs rather than clicking email links. Verify sender authenticity before responding to any crypto-related communications. Token Metrics will never request passwords, private keys, or urgent fund transfers—any such requests are fraudulent.
Device Security and Network Safety
Maintain device security by:
• Keeping operating systems and software updated
• Running antivirus/anti-malware software
• Avoiding public WiFi for crypto transactions
• Considering dedicated devices for high-value crypto management
The computer or phone accessing crypto accounts represents potential vulnerability.
Compromised devices enable keyloggers capturing credentials or malware stealing keys. For substantial portfolios, dedicated devices used only for crypto management enhance security.
Cold Storage for Long-Term Holdings
For cryptocurrency not needed for active trading—long-term holdings in Token Metrics indices not requiring frequent rebalancing—cold storage provides maximum security.
Generate addresses on air-gapped computers, transfer funds to cold storage addresses, and store private keys/recovery seeds in physical safes or bank safety deposit boxes.
This approach trades convenience for security—appropriate for the majority of holdings requiring only occasional access.
No Custody Model
Token Metrics' fundamental security advantage is never taking custody of user funds. Unlike exchanges that become honeypots for hackers by concentrating billions in crypto, Token Metrics operates as an information and analytics platform. Users implement index strategies through their own chosen custody solutions.
This architecture eliminates platform hacking risk to user funds. Even if Token Metrics platform experienced data breach (which comprehensive security measures prevent), user cryptocurrency remains safe in personal or custodial wallets.
Data Security and Privacy
Token Metrics implements enterprise-grade security for user data including:
• Encrypted data transmission and storage
• Regular security audits and penetration testing
• Access controls limiting employee data access
• Compliance with data protection regulations
While Token Metrics doesn't hold crypto, protecting user data—account information, portfolio holdings, personal details—remains paramount.
The platform's security infrastructure meets standards expected of professional financial services.
API Security and Access Control
For users implementing Token Metrics strategies through API connections to exchanges, the platform supports secure API practices including:
• Read-only API keys when possible (avoiding withdrawal permissions)
• IP whitelisting restricting API access to specific addresses
• Regularly rotating API keys as security best practice
Never grant withdrawal permissions through API keys unless absolutely necessary.
Token Metrics strategies can be implemented through read-only keys providing portfolio data without risking unauthorized fund movement.
Continuous Monitoring and Threat Detection
Token Metrics employs active security monitoring including:
• Unusual activity detection flagging suspicious account access
• Threat intelligence monitoring for emerging crypto security risks
• Rapid incident response protocols should breaches occur
This proactive approach identifies and addresses security threats before they impact users, maintaining platform integrity and protecting user interests.
Diversification as Risk Management
Security isn't just about preventing theft—it's also about preventing portfolio devastation through poor investment decisions. Token Metrics' diversification inherently provides risk management by:
• Preventing over-concentration in any single cryptocurrency
• Spreading exposure across projects with different risk profiles
• Combining assets with low correlations reducing portfolio volatility
This diversification protects against the "secure wallet, worthless holdings" scenario where cryptocurrency is safely stored but becomes valueless due to project failure or market collapse.
Liquidity Risk Management
Liquidity—ability to buy or sell without significantly impacting price—represents important risk dimension. Token Metrics indices prioritize liquid cryptocurrencies with substantial trading volumes, multiple exchange listings, and deep order books.
This liquidity focus ensures you can implement index strategies efficiently and exit positions when necessary without severe slippage.
Illiquid tokens might offer higher theoretical returns but expose investors to inability to realize those returns when selling.
Regulatory Compliance and Tax Security
Following applicable laws and regulations protects against government enforcement actions, penalties, or asset seizures. Token Metrics provides transaction histories supporting tax compliance but users must maintain detailed records of all crypto activities including purchases, sales, rebalancing transactions, and transfers between wallets.
Consider working with crypto-specialized tax professionals ensuring full compliance with reporting requirements. The cost of professional tax assistance proves trivial compared to risks from non-compliance.
Emergency Preparedness and Succession Planning
Comprehensive security includes planning for emergencies including:
• Documenting wallet access instructions for trusted individuals
• Maintaining secure backup of recovery seeds and passwords
• Creating crypto asset inventory for estate planning
• Considering legal documents addressing cryptocurrency inheritance
Without proper planning, your cryptocurrency could become inaccessible to heirs upon death. Many families have lost access to substantial crypto holdings due to lack of succession planning.
Assessing Your Security Needs
Security requirements scale with portfolio size and complexity.
For small portfolios under $5,000, reputable exchange custody with 2FA and strong passwords may suffice. For portfolios of $5,000-$50,000, hardware wallets become essential for majority of holdings.
For portfolios exceeding $50,000, multisig or institutional custody warrant serious consideration. For portfolios exceeding $500,000, professional security consultation and institutional custody become prudent.
Assess your specific situation honestly, implementing security measures appropriate for your holdings and technical capabilities.
Creating Security Checklists
Develop systematic security checklists covering:
• Regular security audits of wallet configurations
• Password rotation schedules
• 2FA verification across all platforms
• Recovery seed backup verification
• Device security updates
Regular checklist execution ensures security doesn't degrade over time as you become complacent. Set quarterly reminders for comprehensive security reviews.
Continuous Education
Crypto security threats evolve constantly. Stay informed through:
• Token Metrics educational resources and platform updates
• Cryptocurrency security news and advisories
• Community forums discussing emerging threats
• Periodic security webinars and training
Knowledge proves the most powerful security tool. Understanding threat landscape enables proactive defense rather than reactive damage control.
Cryptocurrency's revolutionary potential means nothing if your investment is lost to theft, hacks, or user error.
Security isn't an afterthought—it's the foundation enabling confident long-term investing. Without proper security measures, even the most sophisticated investment strategies become meaningless.
Token Metrics AI Indices provide comprehensive security through multiple dimensions—selecting fundamentally secure cryptocurrencies, providing educational resources on custody best practices, implementing platform-level security protecting user data, and maintaining no-custody architecture eliminating single-point-of-failure risks.
But ultimately, security requires your active participation. Token Metrics provides tools, knowledge, and guidance, but you must implement proper custody solutions, maintain operational security hygiene, and stay vigilant against evolving threats.
The investors who build lasting crypto wealth aren't just those who select winning tokens—they're those who protect their investments with appropriate security measures. In cryptocurrency's digital landscape where irreversible transactions and pseudonymous attackers create unique challenges, security determines who ultimately enjoys their gains and who watches helplessly as value evaporates.
Invest intelligently with Token Metrics' AI-powered indices. Protect that investment with comprehensive security practices. This combination—sophisticated strategy plus robust security—positions you for long-term success in cryptocurrency's high-opportunity, high-risk environment.
Your crypto investments deserve professional-grade portfolio management and professional-grade security. Token Metrics delivers both.
At Token Metrics, safeguarding your crypto assets is fundamentally built into our platform.
We never take custody of client funds; instead, our AI-driven indices provide guidance, education, and advanced risk screening so you retain full control over your assets at all times.
Our robust platform-level security—encompassing encrypted communications, role-based access, and continuous threat monitoring—offers enterprise-grade protection for your data and strategies.
Whether you want to analyze secure projects, develop stronger portfolio management, or combine expert research with your own secure storage, Token Metrics provides a comprehensive support system to help you invest confidently and safely.
Use unique, complex passwords for every platform, enable two-factor authentication using authenticator apps (not SMS), avoid custodial wallets on exchanges for long-term holdings, store large balances in hardware wallets, and never share your private keys with anyone.
Hardware wallets offer the highest level of security for most users. For substantial balances, using multi-signature wallets or institutional custodians (for qualified investors) adds protection. Always keep backup recovery phrases in secure physical locations.
AI indices, such as those from Token Metrics, systematically vet projects for smart contract vulnerabilities, regulatory issues, code security, liquidity, and signs of fraudulent activity, thus reducing exposure to compromised or risky assets.
Do not interact with the suspicious message. Instead, independently visit the platform’s website by typing the URL directly and contact official customer support if needed. Never provide passwords or private keys to unsolicited contacts.
Document wallet access information and recovery instructions for trusted family or legal representatives. Maintain secure, physical records of all backup phrases, and consider legal estate planning that addresses your digital assets.
This blog is for informational and educational purposes only and does not constitute investment advice, a recommendation, or an offer to buy or sell any cryptocurrency or digital asset. You should consult your own legal, tax, and financial professionals before making any investment or security decisions. While every effort was made to ensure accuracy, neither Token Metrics nor its contributors accept liability for losses or damages resulting from information in this blog.

%201.svg)
%201.svg)
The terms crypto and blockchain are often used interchangeably in conversations about digital money and technology, but they actually represent fundamentally different concepts. As we move through 2025, understanding what is the difference between crypto and blockchain has become increasingly important for investors, traders, technologists, and anyone interested in the future of finance and digital innovation. This comprehensive guide will clarify these distinctions, explain how both technologies work, and explore their evolving roles in shaping the global digital economy.
At its core, blockchain technology is a revolutionary form of a distributed ledger that records transactions across a network of multiple computers, or nodes, simultaneously. Blockchain is a type of distributed ledgers system. Unlike a traditional central database controlled by a single entity, a blockchain network operates without a central authority, distributing data across many participants to create a decentralized ledger. This infrastructure ensures that the blockchain records are immutable, meaning once a transaction is recorded, it cannot be altered without consensus from the network. Blockchain ensures transaction integrity, transparency, and trust by making records tamper-proof and verifiable by all participants.
The blockchain works by grouping transaction data into “blocks.” Each block contains a transaction record, a timestamp, and a reference to the previous block through a cryptographic hash. Blockchain uses cryptographic structures, such as Merkle trees, for storing data securely and immutably. This chaining of blocks forms an immutable digital ledger that ensures data integrity and security. Because every block links to its predecessor, tampering with any single block would require changing all subsequent blocks across the entire network, which is practically impossible.
Key characteristics of blockchain include:
Each block contains a transaction record that is unalterable; the transaction record includes all relevant details of each transaction. If corrections are needed, they are made with additional entries, ensuring a complete and transparent history.
Beyond cryptocurrency, blockchain refers to the underlying technology that supports a wide range of applications, from supply chain management to decentralized applications and smart contracts. Businesses can operate their own private blockchain networks or join consortium blockchain networks where preselected organizations maintain the ledger collectively. Blockchain software automates and streamlines the processes involved in how blockchain works.
At the heart of blockchain technology is a decentralized digital ledger that revolutionizes how we record transactions. Unlike traditional systems that rely on a central authority, a blockchain network operates across a distributed network of computers—known as nodes—where multiple parties can participate in validating and recording transactions. This peer-to-peer structure is the underlying technology that powers secure and transparent data sharing in various industries, from supply chain management to financial institutions and even voting systems.
When a transaction is initiated, it is broadcast to the entire blockchain network. Nodes independently verify the transaction using complex algorithms, ensuring its authenticity and accuracy. Once validated, the transaction is grouped with others into a block. Each block is then assigned a unique cryptographic hash, which links it to the previous block, forming a continuous and unbreakable chain. This blockchain protocol guarantees that every transaction is permanently recorded and cannot be altered without consensus from the network, making the system tamper-proof.
The result is a transparent and immutable record of all transactions, accessible to all network participants. This approach not only enhances trust among multiple parties but also streamlines processes in supply chain management, enables secure voting systems, and provides financial institutions with a robust alternative to traditional centralized databases. By eliminating the need for a central authority, blockchain technology empowers organizations to collaborate more efficiently and securely across a wide range of applications.
Blockchain networks come in several forms, each tailored to different needs and levels of access. Public blockchain networks, such as the bitcoin network, are open to anyone who wishes to participate. These networks allow anyone to record transactions and view the blockchain, making them ideal for applications that benefit from transparency and broad participation, such as cryptocurrencies and open voting systems.
In contrast, private blockchain networks restrict access to authorized participants only. These networks are often chosen by financial institutions and organizations that require greater control and confidentiality. For example, in supply chain management, a private blockchain allows multiple parties within a business network to securely record transactions and share data without exposing sensitive information to the public.
Consortium blockchain networks offer a hybrid approach, where a group of preselected organizations collectively manage the network. This model is particularly useful in industries where collaboration between multiple parties is essential, such as in the financial sector or complex supply chains. Consortium blockchain networks balance the need for shared control with enhanced security and efficiency.
By choosing the appropriate type of blockchain—public, private, or consortium—organizations can tailor their blockchain solutions to meet specific requirements for security, transparency, and collaboration.
Blockchain protocols are the foundational rules that dictate how data is recorded, validated, and shared within a blockchain network. These protocols are essential for ensuring that all transactions are secure, transparent, and tamper-proof, forming the backbone of decentralized systems.
Different blockchain protocols use various consensus mechanisms to validate transactions. For instance, the bitcoin protocol relies on proof-of-work, where nodes compete to solve complex mathematical puzzles to add new blocks to the chain. This process secures the network but can be resource-intensive. In contrast, protocols like Ethereum have adopted proof-of-stake, where validators “stake” their own cryptocurrency to gain the right to verify transactions, offering a more energy-efficient alternative.
Blockchain protocols also enable the creation and execution of smart contracts—self-executing agreements with terms directly written into code. These smart contracts power decentralized applications, automating processes such as asset transfers and ensuring that all parties adhere to agreed-upon terms without the need for intermediaries.
By establishing clear rules for how transactions are processed and how network participants interact, blockchain protocols are critical to the operation and trustworthiness of blockchain networks and the decentralized applications built on top of them.
Cryptocurrency is a type of digital asset and a form of digital or virtual currency that leverages blockchain technology to enable secure, peer-to-peer transfer of value without intermediaries like banks or governments. The most well-known example is Bitcoin, which launched in 2009 on the bitcoin network and introduced the concept of a decentralized ledger for cryptocurrency transactions.
Cryptocurrencies are essentially digital assets or digital money that exist purely in electronic form. Digital assets include cryptocurrencies and other blockchain-based representations of value, such as tokenized assets and digital collectibles. Unlike cash or coins, cryptocurrencies have no physical counterpart. They rely on cryptographic security to control the creation of new units and to verify transactions. This makes cryptocurrencies resistant to counterfeiting and censorship.
By 2025, the landscape of digital currencies has expanded dramatically. The total market capitalization of cryptocurrencies has surpassed $4 trillion, and institutional involvement has increased significantly. The launch of Bitcoin and Ethereum spot ETFs has broadened access to digital currency investments, while the rise of decentralized finance (DeFi) platforms has opened new avenues for users to access financial services without traditional intermediaries. Bitcoin was the first of many virtual currencies, and since its inception, numerous other virtual currencies have emerged, each with unique features and use cases.
Essential features of cryptocurrencies include:
While all cryptocurrencies rely on blockchain, not all blockchains are designed for cryptocurrencies. Some blockchain platforms focus on other use cases, such as supply chain transparency or voting systems. The difference between blockchain and cryptocurrencies is that blockchain is the foundational technology—a distributed ledger system—while cryptocurrencies are just one application of blockchain, serving as digital assets or virtual currencies built on top of it.
To clarify what is the difference between crypto and blockchain, it helps to think of blockchain as the underlying technology or infrastructure, while cryptocurrency is one of its most famous applications.
In summary, while blockchain lies at the heart of cryptocurrencies, it extends far beyond them, enabling decentralized ledgers and blockchain systems that transform how data is stored and shared securely.
As of 2025, both blockchain and cryptocurrency have matured and integrated more deeply into mainstream finance and business. Traditional financial institutions are issuing their own stablecoins, digital currencies pegged to fiat money, with the total market capitalization of these fiat-pegged stablecoins projected to reach $500 billion. Many of these stablecoins are built on a private blockchain network infrastructure, providing enhanced control and permissioned access for participating organizations. This marks a significant step toward institutional acceptance and integration of blockchain-based digital assets.
At the same time, governments worldwide are developing Central Bank Digital Currencies (CBDCs), which utilize blockchain technology to issue state-backed digital money while retaining centralized control. Governments may implement CBDCs using private blockchains or a consortium blockchain network model, allowing multiple authorized entities to participate in managing the digital currency. This hybrid approach demonstrates how blockchain can support both decentralized and centralized financial models.
Moreover, the rise of Blockchain-as-a-Service (BaaS) platforms allows businesses to leverage blockchain technology without building infrastructure from scratch. Businesses can choose to join a public blockchain network or deploy private blockchain networks and consortium blockchain networks depending on their specific requirements for access, control, and scalability. This trend is accelerating adoption in industries beyond finance, including healthcare, retail, and supply chain management.
These technological advancements highlight the growing importance of blockchain as the underlying infrastructure for a wide array of applications, while cryptocurrencies continue to evolve as digital assets within this ecosystem.
With the increasing complexity of the cryptocurrency market, professional tools are essential for making informed decisions. Platforms like Token Metrics exemplify the new generation of AI-powered crypto analytics tools that combine blockchain protocols with machine learning to provide actionable insights.
Token Metrics offers AI-driven ratings, market intelligence, and predictive analytics for various cryptocurrencies, helping traders navigate volatile markets. The platform’s integration of on-chain data analysis allows users to evaluate bitcoin transactions and other cryptocurrency transactions in real time, enhancing transparency and decision-making.
Innovations such as integrated trading capabilities and AI-powered agents provide seamless transitions from research to execution, streamlining the trading process. For investors seeking emerging opportunities, Token Metrics specializes in identifying promising altcoins or “moonshots” before they gain widespread attention.
Such tools are critical for managing risks and capitalizing on the rapid evolution of blockchain bitcoin and other digital assets, making professional-grade analytics accessible to both retail and institutional investors.
While cryptocurrency remains the most visible application of blockchain, the technology’s potential extends far beyond digital money. Industries across the board are leveraging blockchain to improve transparency, security, and efficiency.
In supply chain management, blockchain enables companies to track products from origin to consumer, ensuring authenticity and reducing counterfeiting. Luxury brands like Gucci and Balenciaga use blockchain platforms to provide provenance verification, enhancing consumer trust. In these enterprise blockchain applications, private transactions are essential for maintaining confidentiality and controlled access to sensitive business data.
Healthcare organizations are adopting blockchain for secure patient data management, drug traceability, and maintaining the integrity of clinical trial data. The immutable record capabilities of blockchain ensure accurate and tamper-proof medical histories. Private transactions also play a key role in healthcare, helping to protect patient privacy and comply with regulatory requirements.
Retailers are also embracing blockchain to combat fraud and enhance transparency, contributing to the growth of the global blockchain retail market, which is expected to expand rapidly in the coming decade.
Other notable applications include voting systems that use blockchain to create transparent and tamper-resistant election processes, and decentralized applications that run on blockchain networks to enable new business models. Some of these applications leverage public networks to ensure transparency and broad participation, especially in open, permissionless environments.
Despite its transformative potential, blockchain technology faces several significant challenges that can slow its adoption across various industries. One of the most pressing issues is scalability. Many blockchain networks struggle to process a high volume of transactions per second, leading to congestion, delays, and increased transaction fees. This limitation can make blockchain less competitive compared to traditional payment systems.
Regulatory uncertainty is another major hurdle. As governments and regulatory bodies grapple with how to oversee blockchain technology and cryptocurrency transactions, businesses often face unclear or evolving compliance requirements. This uncertainty can deter investment and slow the integration of blockchain solutions in sectors like finance and supply chain management.
Technical complexity also poses a barrier. Implementing and maintaining blockchain networks requires specialized expertise, which can be scarce and costly for organizations new to the technology. Additionally, the public nature of many blockchains raises concerns about data privacy and security, as sensitive information recorded on a public ledger may be accessible to unintended parties.
Finally, as a relatively new technology, blockchain’s long-term viability and the full scope of its applications remain uncertain. Questions about interoperability between different blockchain networks and the environmental impact of certain consensus mechanisms also persist.
Despite these challenges, the potential benefits of blockchain technology—such as enhanced transparency, security, and efficiency—continue to drive innovation and exploration across a wide range of industries. As solutions to these hurdles emerge, blockchain is poised to play an increasingly important role in the digital economy.
The future of blockchain and cryptocurrency is one of ongoing evolution and integration. Blockchain technology is expected to become increasingly invisible to end-users, embedded as the shared database infrastructure powering many digital services.
Cryptocurrencies may diversify into specialized tokens serving distinct functions within various ecosystems, from digital money to governance rights and beyond. Regulatory clarity will be pivotal, as recent developments indicate growing institutional acceptance and potential recognition of Bitcoin as a strategic reserve asset.
The convergence of AI with blockchain and cryptocurrency trading, as seen with platforms like Token Metrics, heralds a new frontier in market sophistication. These technological synergies will create fresh opportunities for both individual investors and institutions.
Understanding the nuanced differences and complementary roles of crypto and blockchain will be essential for success in this rapidly changing landscape.
In conclusion, what is the difference between crypto and blockchain is a fundamental question for anyone involved in the digital economy. Blockchain is the technology — a decentralized, secure, and transparent ledger system that supports a variety of applications across industries. Cryptocurrency is a prominent application of blockchain technology, representing digital or virtual currency designed to function as digital money outside of traditional financial systems.
As 2025 unfolds, blockchain continues to serve as critical infrastructure for numerous sectors, while cryptocurrencies mature as an asset class with growing institutional adoption. Leveraging advanced analytics tools like Token Metrics can provide significant advantages for those navigating the complex world of crypto trading and investment.
Ultimately, both blockchain and cryptocurrency will play distinct but interconnected roles in shaping the future of finance, business, and technology — making an understanding of their differences not just useful, but essential.

%201.svg)
%201.svg)
The cryptocurrency space continues to evolve at a rapid pace, with Bitcoin and Ethereum maintaining their status as the two most dominant digital assets in the crypto market. Both Bitcoin and Ethereum operate on blockchain technology, yet they differ fundamentally in their design, purpose, and investment profiles. This article presents a bitcoin vs ethereum comparison, exploring the key differences between these leading cryptocurrencies. Understanding the Bitcoin vs Ethereum debate and the key differences between Bitcoin and Ethereum is essential for investors and enthusiasts seeking to navigate the dynamic cryptocurrency market of 2025 effectively.
Bitcoin and Ethereum stand as the two most prominent digital assets in the cryptocurrency market, commanding a combined market capitalization that exceeds $1 trillion. Both bitcoin and ethereum leverage blockchain technology, which provides a decentralized and secure method for recording and verifying transactions. Despite this shared foundation, their purposes and functionalities diverge significantly.
Bitcoin is widely recognized as digital gold—a decentralized digital currency designed to serve as a store of value and a hedge against inflation. Its primary function is to enable peer-to-peer transactions without the need for a central authority, making it a pioneering force in the world of digital money. In contrast, Ethereum is a decentralized platform that goes beyond digital currency. It empowers developers to build and deploy smart contracts and decentralized applications (dApps), opening up a world of possibilities for programmable finance and innovation.
Understanding the underlying technology, value propositions, and investment potential of both bitcoin and ethereum is crucial for anyone looking to participate in the evolving landscape of digital assets. Whether you are interested in the stability and scarcity of bitcoin or the versatility and innovation of the ethereum network, both offer unique opportunities in the rapidly growing world of blockchain technology.
Bitcoin was introduced in 2009 as the first decentralized digital currency, often described as “digital gold.” Its primary goal is to serve as a peer-to-peer electronic cash system and a store of value that operates without a central authority or intermediaries, such as a central bank, highlighting its independence from traditional financial systems. Bitcoin focuses on simplicity and security, aiming to facilitate trustless, secure transactions while providing a hedge against inflation. Bitcoin aims to be a decentralized, universal form of money, prioritizing security, decentralization, and a stable long-term monetary policy. A key advantage is bitcoin's simplicity, which sets it apart from more complex blockchain platforms and supports its long-term stability and adoption. This finite supply of bitcoins, capped at 21 million, reinforces its role as digital money with scarcity akin to precious metals.
In contrast, Ethereum, launched in 2015, represents a major shift from a mere digital currency to a programmable blockchain platform. Often referred to as “the world computer,” Ethereum enables developers to create decentralized applications (dApps) and smart contracts—self-executing code that runs on the blockchain without downtime or interference. This capability allows the Ethereum ecosystem to support a vast array of decentralized finance (DeFi) protocols, tokenized assets, and automated agreements, making it a core infrastructure for innovation in the cryptocurrency space.
The ongoing development of Bitcoin and Ethereum is a testament to the strength and vision of their respective communities. Bitcoin was launched by the enigmatic Satoshi Nakamoto, whose identity remains unknown, and its evolution is now guided by a global network of bitcoin developers. These contributors work collaboratively on the open-source Bitcoin Core protocol, ensuring the security, reliability, and decentralization of the bitcoin network.
Ethereum, on the other hand, was conceived by Vitalik Buterin and is supported by the Ethereum Foundation, a non-profit organization dedicated to advancing the ethereum network. The foundation coordinates the efforts of ethereum developers, researchers, and entrepreneurs who drive innovation across the platform. A cornerstone of Ethereum’s technical architecture is the Ethereum Virtual Machine (EVM), which enables the execution of smart contracts and decentralized applications. This powerful feature allows the ethereum network to support a wide range of programmable use cases, from decentralized finance to tokenized assets.
Both bitcoin and ethereum benefit from active, passionate developer communities that continually enhance their networks. The collaborative nature of these projects ensures that both platforms remain at the forefront of blockchain technology and digital asset innovation.
As of 2025, bitcoin's dominant market share is reflected in its market capitalization of approximately $2.3 trillion, significantly larger than Ethereum’s $530 billion market cap. Despite this gap, Ethereum’s market cap is about three times that of the next-largest cryptocurrency, highlighting its dominant position beyond Bitcoin.
The price performance of these assets has also diverged this year. After Bitcoin’s halving event in April 2024, which reduced the rate at which new bitcoins are created, Bitcoin demonstrated resilience with a price increase of around 16% through March 2025. Ethereum, however, experienced a notable drop of nearly 50% during the same period, reflecting its higher volatility and sensitivity to broader market trends. Recently, Ethereum rebounded with a surge exceeding 50%, underscoring the distinct risk and reward profiles of these digital assets in the cryptocurrency market.
Bitcoin and Ethereum differ significantly in their underlying technology and consensus algorithms. Both Proof-of-Work (PoW) and Proof-of-Stake (PoS) are types of consensus algorithms that determine how transactions are validated and agreed upon across the network. Bitcoin operates on a Proof-of-Work (PoW) consensus mechanism, where miners compete to solve complex mathematical puzzles to validate transactions and add new blocks to bitcoin's blockchain, which serves as a decentralized ledger. A typical bitcoin transaction involves transferring digital currency units, which are then validated and recorded on bitcoin's blockchain through this process. Bitcoin transactions are fundamental to the Proof-of-Work process, as they are grouped into blocks and confirmed by miners using the consensus algorithm. This process, while highly secure and decentralized, requires substantial energy consumption. For example, creating a new bitcoin currently demands around 112 trillion calculations, reflecting Bitcoin’s commitment to security and decentralization. To address limitations in transaction speed and scalability, bitcoin's lightning network has been developed as a solution to enable faster and lower-cost payments.
Ethereum initially used a similar PoW system but transitioned to a Proof-of-Stake (PoS) consensus mechanism in 2022 through an upgrade known as “The Merge.” This shift allows validators to secure ethereum networks by staking their native cryptocurrency, ETH, rather than mining. The PoS system drastically reduces energy consumption, improves scalability, and maintains network security. This technical improvement positions Ethereum as a more environmentally sustainable and efficient platform compared to Bitcoin’s energy-intensive approach.
When it comes to transaction speed and scalability, Bitcoin and Ethereum offer different capabilities. The bitcoin network processes approximately 7 transactions per second, which is sufficient for a decentralized payment network but limits throughput. Ethereum’s main layer can handle about 15 transactions per second, nearly double Bitcoin’s capacity. However, Ethereum’s true scalability advantage lies in its Layer 2 solutions, such as Polygon, Arbitrum, and Optimism, which significantly increase transaction throughput and reduce transaction fees.
These advancements in the ethereum blockchain help support a growing number of decentralized applications and DeFi protocols that demand fast, low-cost transactions. Unlike Bitcoin's fixed supply, Ethereum features a dynamic supply, allowing its economic model to flexibly adjust issuance and burn fees, resulting in inflationary or deflationary tendencies as needed. The Ethereum network is also capable of processing executable code within transactions, enabling the creation and operation of smart contracts and decentralized applications. ETH serves as the native currency of the Ethereum network, and as the native token, it is used for a variety of functions across the platform. Users pay transaction fees with ETH, especially when executing smart contracts or deploying decentralized applications. Ethereum’s ecosystem continues to innovate with technical improvements that enhance scalability, making it a preferred platform for developers and users seeking dynamic and efficient decentralized finance solutions.
The communities and ecosystems surrounding Bitcoin and Ethereum are among the most dynamic in the cryptocurrency space. The bitcoin network boasts a mature and well-established ecosystem, with widespread adoption as a decentralized digital currency and a robust infrastructure supporting everything from payment solutions to secure storage.
In contrast, the ethereum ecosystem is renowned for its focus on decentralized finance (DeFi) and the proliferation of decentralized applications. The ethereum network has become a hub for innovation, hosting a vast array of dApps, tokens, stablecoins, and non-fungible tokens (NFTs). This vibrant environment attracts developers, investors, and users who are eager to explore new financial products and services built on blockchain technology.
Both bitcoin and ethereum owe much of their success to their engaged and diverse communities. These groups not only contribute to the development of the underlying technology but also drive adoption and create new use cases. For investors, understanding the strengths and focus areas of each ecosystem is key to evaluating the long-term potential and value proposition of these leading digital assets. Key takeaways bitcoin and ethereum offer include the importance of community-driven growth, ongoing innovation, and the expanding possibilities within the world of decentralized applications and finance.
Bitcoin’s primary use cases revolve around its role as digital gold and a decentralized digital currency. It is widely adopted for cross-border payments, remittances, and as an inflation hedge by institutions and corporations. Many companies now hold bitcoin as a treasury reserve asset, recognizing its value as a finite supply digital money that operates independently of central banks and traditional currencies. Unlike national currencies, which are issued and regulated by governments, Bitcoin was created as an alternative medium of exchange and store of value, offering users a decentralized option outside the control of any single nation.
Ethereum, on the other hand, offers a broader range of applications through its programmable blockchain. It powers decentralized finance protocols, enabling lending, borrowing, and trading without intermediaries. Ethereum also supports non-fungible tokens (NFTs), decentralized autonomous organizations (DAOs), and enterprise blockchain solutions. The ethereum network’s ability to execute smart contracts and host decentralized applications makes it a foundational platform for the future of tokenized assets and innovative financial products.
From an investment perspective, bitcoin and ethereum present distinct profiles. Bitcoin is often viewed as a stable store of value with strong institutional validation, appealing to conservative investors seeking security and macroeconomic hedging. Its simplicity and fixed supply contribute to its perception as a reliable digital silver or digital gold.
Ethereum represents a growth-oriented investment, offering exposure to the expanding decentralized finance ecosystem and technological innovation. However, this comes with higher volatility and risk. Ethereum’s future developments and upgrades promise to enhance its capabilities further, attracting investors interested in the evolving crypto adoption and the broader use of blockchain technology. Still, ethereum's future remains complex and uncertain, with ongoing challenges, competition, and the outcomes of recent upgrades all influencing its long-term prospects and value proposition.
Market analysts remain cautiously optimistic about both bitcoin and ethereum throughout 2025. Projections suggest that Ethereum could reach $5,400 by the end of the year and potentially approach $6,100 by 2029. However, Ethereum's price remains subject to significant fluctuations, potentially rising above $5,000 or falling below $2,000 depending on market conditions and regulatory developments.
Bitcoin's outlook is similarly influenced by factors such as institutional adoption, regulatory clarity, and macroeconomic trends. Its status as the first digital asset and a decentralized payment network underpins its resilience in global markets. Investors should consider these dynamics alongside their investment objectives and risk tolerance when evaluating these cryptocurrencies.
Navigating the complex cryptocurrency market requires sophisticated tools and data-driven insights. Platforms like Token Metrics have emerged as invaluable resources for investors aiming to make informed decisions. Token Metrics is an AI-powered crypto research and investment platform that consolidates market analysis, portfolio management, and real-time insights.
By leveraging artificial intelligence and machine learning, Token Metrics offers comprehensive research tools, back-tested bullish signals, and sector trend analysis. Its AI-driven X agent provides actionable insights that help investors identify opportunities and manage risks in the 24/7 crypto market. This advanced analytics platform is especially beneficial for those looking to optimize their investment strategy in both bitcoin and ethereum.
For investors considering both bitcoin and ethereum, a diversified portfolio approach is advisable. Bitcoin's stability and role as digital gold complement Ethereum's growth potential in decentralized finance and technology-driven applications. Depending on risk tolerance and investment goals, allocations might vary:
This balanced approach leverages the unique features of both cryptocurrencies while managing volatility and maximizing exposure to different segments of the cryptocurrency ecosystem.
Bitcoin and Ethereum offer distinct but complementary value propositions in the cryptocurrency space. Bitcoin remains the first digital asset, a decentralized payment network, and a trusted store of value often likened to digital gold. Ethereum, powered by its programmable blockchain and smart contracts, drives innovation in decentralized finance and applications, shaping the future of the crypto market.
Choosing between bitcoin and ethereum—or deciding on an allocation between both—depends on individual investment objectives, risk appetite, and confidence in blockchain technology’s future. Both assets have a place in a well-rounded portfolio, serving different roles in the evolving digital economy.
For investors serious about cryptocurrency investing in 2025, utilizing advanced analytics platforms like Token Metrics can provide a competitive edge. With AI-powered insights, comprehensive research tools, and real-time market analysis, Token Metrics stands out as a leading platform to navigate the complexities of the cryptocurrency market.
Whether your preference is bitcoin’s simplicity and stability or ethereum’s innovation and versatility, success in the cryptocurrency market increasingly depends on access to the right data, analysis, and tools to make informed decisions in this exciting and fast-changing landscape.
Disclaimer: Certain cryptocurrency investment products, such as ETFs or trusts, are not classified as investment companies or investment companies registered under the Investment Company Act of 1940. As a result, these products do not have the same regulatory requirements as traditional mutual funds. This article does not provide tax advice. For personalized tax advice or guidance regarding regulatory classifications, consult a qualified professional.

%201.svg)
%201.svg)
In today’s rapidly evolving digital landscape, blockchain technology stands out as one of the most transformative innovations reshaping industries worldwide. At its core, blockchain is a decentralized, distributed blockchain database that securely records and verifies transactions across a peer-to-peer network. Understanding what is blockchain and how does it work has become essential for anyone interested in the future of digital transactions, data security, and decentralized systems. As we navigate through 2025, blockchain continues to redefine how information is stored, shared, and secured across multiple sectors.
At its essence, blockchain is a revolutionary form of database technology that diverges from traditional centralized systems. A blockchain consists of interconnected blocks that store transaction data and are cryptographically linked, forming a secure and ordered chain. Unlike conventional databases controlled by a single authority, blockchain operates on a distributed network of computers known as nodes. These nodes collectively maintain a shared ledger—a decentralized ledger—that records and verifies transaction data transparently and securely.
Imagine blockchain as an immutable digital ledger simultaneously stored on thousands of computers around the globe. In fact, blockchain functions as a distributed database, with data stored across multiple nodes, making it highly resistant to tampering. Every time a transaction occurs—whether it involves digital currency or other types of digital assets—it must be validated by multiple nodes before being permanently added to the blockchain. This process ensures that the transaction records—or blockchain records—are immutable and auditable, enhancing transparency and facilitating audits. These records are accurate and cannot be altered or deleted, providing an unprecedented level of security and trust.
The core principles underpinning blockchain technology are decentralization, transparency, and immutability. Blockchain decentralization enhances security and data integrity by distributing data across multiple nodes, preventing tampering and ensuring redundancy. A decentralized blockchain is a system where control is distributed across multiple nodes, eliminating the need for a central authority. Unlike traditional business networks that rely on a centralized entity, blockchain eliminates the need for intermediaries by enabling peer-to-peer network interactions. This decentralized structure fosters a trustless environment where blockchain users can conduct transactions directly, reducing costs and increasing efficiency. In contrast to centralized systems, decentralized blockchains offer a distributed structure and greater resilience, setting them apart from single-entity control models.
The journey of blockchain technology began with early cryptographic innovations in the 1980s, but it was the introduction of Bitcoin in 2008 that truly brought blockchain into the spotlight. Bitcoin’s launch marked the first successful use of a decentralized digital currency, powered by a blockchain network that allowed users to record transactions securely without relying on a central authority. This breakthrough demonstrated the potential of blockchain as more than just a ledger for digital currency—it became a foundation for trustless, peer-to-peer value exchange.
As blockchain technology matured, its applications rapidly expanded beyond cryptocurrencies. The development of smart contracts enabled automated, self-executing agreements on blockchain platforms, paving the way for decentralized finance (DeFi) and a new era of programmable money. The rise of non-fungible tokens (NFTs) further showcased blockchain’s versatility in managing digital assets and intellectual property.
Over time, the blockchain ecosystem diversified with the emergence of various blockchain networks, including public, private, and consortium blockchains. Each type of network brought unique features and use cases, from open participation and transparency to controlled access and enterprise collaboration. Today, blockchain technologies underpin a wide range of applications, driving innovation across finance, supply chain, healthcare, and beyond.
The mechanics of blockchain revolve around linking blocks of data in a secure and verifiable chain. Each block contains a batch of transaction records, and crucially, each block references the previous block through a cryptographic hash. This linking forms a continuous chain, making it extraordinarily difficult to alter any individual block without affecting all subsequent blocks. Blockchain work involves recording, verifying, and chaining data or transactions across a decentralized network, ensuring transparency and security.
The transaction lifecycle begins when a user initiates a transaction on the blockchain network. This transaction is broadcast to the network participants, who then engage in a verification process to validate its authenticity. Nodes use blockchain protocols—the fundamental set of rules and algorithms that govern how data is recorded, shared, and secured within the network, such as proof-of-stake or Byzantine fault-tolerant protocols—to confirm that the transaction adheres to the network’s standards.
Once verified, the process of recording transactions immutably on the blockchain takes place. The transaction is grouped with other validated transactions into a new data block. This block is then appended to the existing blockchain, creating an immutable transaction record. A transaction record is an entry that cannot be altered or tampered with, and a transaction record includes all relevant details for auditability and transparency. The cryptographic hash linking ensures that any attempt to tamper with the transaction ledger would require recalculating the hashes of all subsequent blocks, a feat computationally infeasible in a well-secured blockchain system.
During the verification process, validating transactions through consensus mechanisms is crucial to ensure the integrity and trustworthiness of the ledger. Consensus mechanisms like proof of work (used in the bitcoin blockchain) or proof of stake help the network validate transactions and maintain trust without a central authority. Efficient consensus and network design can significantly increase the number of transactions processed by the blockchain. This process, often referred to as blockchain mining, secures the network and processes blockchain transactions efficiently.
Each node in the network maintains a copy of the entire blockchain, meaning all data stored on the blockchain is replicated across participants. As the blockchain grows, the amount of data stored increases, presenting challenges related to storage capacity and efficient data management.
Blockchain networks come in several forms, each tailored to specific needs and use cases. Public blockchain networks, such as the Bitcoin and Ethereum networks, are open to anyone who wishes to participate. These networks rely on decentralized consensus mechanisms like proof of work, allowing users worldwide to validate transactions and contribute to the network’s security and transparency.
In contrast, private blockchain networks restrict access to a select group of participants, making them ideal for organizations that require greater control over data and permissions. Private blockchains are commonly used in enterprise settings, where privacy, regulatory compliance, and efficiency are paramount.
Consortium blockchain networks offer a hybrid approach, bringing together multiple organizations to jointly manage the network. In a consortium blockchain, a group of trusted entities collaborates to validate transactions and maintain the distributed ledger, balancing decentralization with governance and operational efficiency. This model is particularly effective for industries where competitors or partners need to share data securely, such as banking, logistics, or healthcare.
The architecture of any blockchain network is built around nodes—computers that store and process data blocks. These nodes can be full nodes, which maintain a complete copy of the blockchain ledger, or light nodes, which store only essential information. Consensus mechanisms, such as proof of work or proof of stake, ensure that all network participants agree on the validity of transactions, maintaining the integrity and security of the blockchain system. Understanding these different types of blockchain networks and their architectures is essential for selecting the right platform for any blockchain implementation.
One of the defining strengths of blockchain technology is its robust approach to security and transparency. Every transaction recorded on a blockchain network is secured using cryptographic hash functions, which create a unique digital fingerprint for each data block. This ensures that once data is stored on the blockchain, it cannot be altered without detection, providing an immutable record of all activity.
The decentralized structure of blockchain networks further enhances security. By distributing data across multiple nodes, blockchain eliminates single points of failure and makes it extremely difficult for any one party to manipulate the transaction ledger. This distributed approach not only safeguards against tampering but also increases the resilience of the network against cyberattacks.
Transparency is another key benefit of blockchain technology. Public blockchain networks allow anyone to access data and verify transaction records, fostering trust among users. Even in private or consortium blockchains, authorized participants can track and audit transactions, ensuring accountability and compliance. However, maintaining high levels of security and transparency requires careful network design, regular code audits, and proactive identification of potential vulnerabilities. By prioritizing these elements, blockchain networks can deliver secure transactions and reliable data management for a wide range of applications.
By 2025, blockchain technology has transitioned from a niche innovation associated primarily with cryptocurrencies to a foundational infrastructure across multiple industries. The blockchain adoption curve is steepening as businesses and governments recognize the benefits of blockchain based distributed ledgers for enhancing security, transparency, and efficiency. The proliferation of blockchain systems across sectors such as finance, media, and supply chain is fostering innovation and enabling interoperability among different networks.
Industries such as finance, healthcare, supply chain, and entertainment are leading the charge in integrating blockchain solutions. Financial institutions increasingly utilize blockchain to streamline financial transactions, reduce settlement times, and improve regulatory compliance. Distributed ledger technologies and distributed ledger technology provide secure, immutable record-keeping, ensuring data integrity and transparency in these sectors. The rise of decentralized finance (DeFi) platforms built on blockchain platforms like the ethereum blockchain exemplifies how blockchain is reshaping traditional financial services.
Moreover, major corporations including IBM, Google, Visa, and Deloitte have invested heavily in blockchain projects, developing enterprise-grade solutions that leverage private blockchain networks and consortium blockchain networks. These networks provide the benefits of decentralization while maintaining controlled access and privacy for sensitive transaction data. Blockchain records are used to ensure transparency and auditability at scale, addressing storage requirements and potential costs as data grows.
As a result, users in 2025 enjoy faster transaction confirmations, lower transaction fees, and more intuitive interfaces that abstract the complexities of blockchain technology, making it accessible to a broader audience. Blockchain also enables the recording of other transactions beyond financial ones, such as data uploads or document exchanges, further expanding its utility.
In the context of consortium and private networks, blockchain facilitates secure data sharing within a business network, allowing multiple organizations to collaborate efficiently while maintaining trust and transparency.
The versatility of blockchain extends far beyond bitcoin transactions and digital currencies. Its ability to create a distributed ledger that is both secure and transparent has unlocked numerous practical applications across sectors.
In supply chain management, blockchain enhances data transparency by providing an immutable record of product provenance accessible to all network participants. Public blockchain networks allow open participation and transparency, enabling anyone to join and verify transactions, which helps reduce fraud, improve compliance, and streamline operations.
Healthcare providers use blockchain to secure patient records while enabling authorized data sharing, ensuring privacy and accuracy. Private blockchain networks are often used in enterprise and healthcare applications to restrict access and enhance privacy for sensitive information. Access to encrypted medical records is protected by a private key, which acts as a confidential password to ensure only authorized parties can view or modify data. The use of private transactions further restricts access to sensitive information, maintaining confidentiality within the blockchain.
The entertainment industry leverages blockchain for digital rights management, facilitating fair royalty distribution and protecting intellectual property. Here, private keys are essential for securing control over digital assets and ensuring only rightful owners can access or transfer rights.
Financial institutions harness blockchain for cross-border payments, reducing costs and settlement times dramatically. Real estate transactions benefit from blockchain’s tamper-proof property records, increasing trust and reducing paperwork. Even voting systems are being revolutionized by blockchain technology, offering transparent and verifiable election processes that enhance democratic integrity.
Smart contracts, which are self-executing programs on blockchain technology, automate and enforce agreements based on predefined conditions, eliminating the need for intermediaries and streamlining transaction processes.
Consortium blockchain networks represent a powerful model for partnership and collaboration in the digital age. Unlike public or private blockchains, a consortium blockchain network is governed by a group of organizations that collectively validate transactions and manage the distributed ledger. This collaborative approach enables businesses to share data and processes securely, without relying on a single central authority.
The benefits of consortium blockchains are especially evident in industries where multiple stakeholders need to coordinate and trust each other, such as finance, healthcare, and logistics. By working together on a shared blockchain network, organizations can streamline operations, reduce costs, and improve data transparency. For example, financial institutions can use consortium blockchains to process cross-border payments more efficiently, while supply chain partners can track goods in real time with greater accuracy.
Successful consortium blockchain networks depend on strong partnerships and clear governance structures. By pooling resources and expertise, participating organizations can validate transactions, maintain network integrity, and unlock the full benefits of blockchain technology. As more industries recognize the value of collaboration, consortium blockchains are poised to drive innovation and transform traditional business networks into agile, secure, and transparent ecosystems.
With the maturation of blockchain technology, the cryptocurrency market has become both complex and dynamic. For those seeking to invest or trade in this space, access to sophisticated analytical tools is crucial. This is where platforms like Token Metrics come into play.
Token Metrics is an AI-powered platform providing comprehensive crypto trading research, analytics, and indices. It offers data-driven crypto trading insights, including AI-powered ratings, trader and investor grades, and the discovery of promising altcoins or "crypto moonshots." Such tools help users navigate the volatile and sentiment-driven cryptocurrency markets with greater confidence.
In 2025, Token Metrics has evolved into a full trading ecosystem, integrating on-chain trading features that allow users to execute trades directly on the platform. By connecting their wallets, users can select tokens and complete transactions swiftly, often in under two minutes.
What differentiates Token Metrics is its AI-driven approach to market analysis, real-time signals, and alerts, alongside tools for both long-term investing and short-term trading. The platform also supports creating custom dashboards, AI bots, and automated trading strategies, empowering blockchain users to optimize their investment decisions.
Additionally, Token Metrics engages its community with AI-powered agents that deliver timely, data-backed market insights, helping users stay informed about trends, sector performance, and bullish signals derived from proprietary data.
Looking forward, blockchain technology promises to become the backbone of a more decentralized, efficient, and secure digital economy. Businesses that invest in blockchain development services today are positioning themselves for competitive advantage in tomorrow’s market.
Ongoing advancements focus on improving scalability, interoperability, and energy efficiency. Layer 2 solutions are mitigating transaction speed and cost challenges, while cross-chain protocols enable seamless communication between disparate blockchain networks, further expanding blockchain’s potential.
Governments are exploring central bank digital currencies (CBDCs), and enterprises are deploying blockchain for identity verification, carbon credit trading, and more. The increasing blockchain adoption across both public and private blockchains signals a future where blockchain based distributed ledgers become integral to everyday life and business operations.
For newcomers, understanding what is blockchain and how does it work might seem daunting, but the foundational concepts are approachable with the right resources. Begin by familiarizing yourself with key terms like nodes, consensus mechanisms, and smart contracts—self-executing contracts coded on blockchain platforms that automate agreements without intermediaries.
Explore different blockchain networks such as the bitcoin network, ethereum blockchain, and emerging blockchain platforms to appreciate their unique features and applications. For investors and traders, leveraging AI-driven analytics platforms like Token Metrics can provide valuable insights and enhance decision-making in the cryptocurrency market.
Blockchain technology has evolved from a novel concept into a transformative infrastructure reshaping industries worldwide. Its core attributes—decentralization, transparency, and security—drive innovation and foster trust in digital transactions and data management.
As 2025 progresses, mastering what is blockchain and how does it work becomes increasingly important for businesses, investors, and individuals alike. Whether exploring blockchain’s technological capabilities or engaging with the cryptocurrency markets, access to reliable information and advanced analytical tools is essential.
The blockchain revolution is not merely about technology; it represents a fundamental shift in how we store, transfer, and verify information in a connected world. As blockchain adoption accelerates and new blockchain applications emerge, those who embrace blockchain today will be best positioned to thrive in the decentralized future ahead.

%201.svg)
%201.svg)
In the rapidly evolving landscape of blockchain technology, zero knowledge proofs (ZKPs, or zero knowledge proof zkp) have emerged as one of the most transformative innovations, addressing two critical challenges that have long plagued the industry: privacy and scalability. At a high level, zero knowledge proofs are a type of cryptographic proof that enables one party to prove the validity of a statement to another party without revealing any additional information beyond the fact that the statement is true. This cryptographic proof provides privacy and security in blockchain applications, such as transaction validation and identity verification. Zero knowledge proofs represent a revolutionary advance in computational integrity and privacy technology, enabling the secure and private exchange of information without revealing underlying private data. As we navigate through 2025, understanding zero knowledge proof systems has become essential for anyone involved in cryptocurrency trading, DeFi protocols, or blockchain development. Emerging trends like zk-SNARKs and hardware acceleration are driving the blockchain world toward rapid scalability and secure interoperability.
Zero knowledge proofs are a powerful cryptographic method that allows one party to prove knowledge of specific data to another party without revealing the data itself. In other words, a prover can convince a verifier that a particular statement is true without disclosing any secret information or other data beyond the statement’s validity. This capability is crucial for preserving user privacy while enabling trustless verification.
The core of zero knowledge proofs lies in the three properties: completeness, soundness, and zero knowledge. Completeness ensures that if the statement is true, an honest verifier will be convinced by an honest prover. For example, if a prover claims to know a secret password, completeness guarantees that the verifier will accept the proof if the prover is truthful. Soundness guarantees that if the statement is false, no dishonest prover can convince the honest verifier otherwise, preventing fraud or deception. The zero-knowledge property ensures that the verifier learns nothing beyond the fact that the statement's truth has been established; no additional knowledge or secret information is revealed during the process.
To explain zero knowledge protocols, consider the classic 'Where's Wally?' scenario. Here, two parties are involved: the prover P, who claims to know Wally's location (the secret), and the verifier. The goal is proving knowledge of Wally's location without revealing it. The protocol works as follows: the verifier randomly chooses which path the prover P must take to reach Wally. The prover P then demonstrates their knowledge by successfully navigating the chosen path. This process is repeated multiple times, and each time, the verifier observes through a small hole—an analogy for seeing just enough to confirm the claim without revealing Wally's location or any other details. What is proved is that the prover P knows Wally's location, not the secret itself. The act of proving is done without revealing any information about Wally's location; the protocol reveals nothing about the secret. This example proves the prover's knowledge and captures the essence of zero knowledge protocols, where the verifier gains confidence in the statement's truth while the secret remains protected.
Zero knowledge proof systems come in several distinct forms, each designed to address different security and efficiency requirements in cryptographic protocols. At their core, these proof systems enable one party—the prover—to convince another party—the verifier—that a specific statement is true, all without revealing any secret information or additional data beyond the statement’s validity.
One of the foundational structures in zero knowledge is the interactive proof system. In this approach, the prover and verifier engage in multiple rounds of communication, with the verifier issuing challenges and the prover responding to demonstrate knowledge. This interactive process is essential for certain applications where dynamic verification is required, and it forms the basis for many early zero knowledge protocols.
Beyond interactive proof systems, there are statistical zero knowledge and computational zero knowledge proof systems. Statistical zero knowledge relies on probabilistic techniques to ensure that, even if the verifier is dishonest, they cannot extract meaningful information about the secret, except with negligible probability. Computational zero knowledge, on the other hand, leverages advanced mathematics and the assumed hardness of problems like the discrete logarithm problem to guarantee that, for any efficient adversary, the secret remains secure.
Modern developments have introduced succinct non-interactive arguments of knowledge (SNARKs), which allow users to generate a proof that can be verified quickly and without the need for back-and-forth communication. These non-interactive proof systems are particularly valuable for blockchain applications, where efficiency and scalability are paramount.
The security of these zero knowledge proof systems is rooted in their three essential properties: completeness (an honest prover can always convince an honest verifier), soundness (a dishonest prover cannot convince the verifier of a false statement, except with negligible probability), and zero knowledge (the verifier learns nothing beyond the truth of the statement). By combining these properties with robust mathematical foundations, zero knowledge protocols empower users to prove possession of knowledge or credentials without revealing the underlying secret information, making them a cornerstone of privacy-enhancing technologies in the digital age.
In 2025, zero knowledge proofs are revolutionizing online privacy and security by enabling proofs without revealing secrets or sensitive personal information. This transformation is particularly significant for regulated industries, where data breaches can lead to severe penalties and loss of user trust. Zero knowledge proof systems allow organizations to prove compliance or transaction validity while preserving user privacy and protecting sensitive data.
One of the key trends driving this revolution is hardware acceleration technology. Creating zero knowledge proofs often requires substantial computational power due to the complex mathematical operations involved. The process of generating a proof begins with a given input, which is the data or statement to be proved without revealing the underlying information. Some zero-knowledge proof systems require a trusted setup to securely generate cryptographic parameters before proofs can be created. Specialized hardware accelerators now assist developers in generating proofs more efficiently, making zero knowledge protocols practical and cost-effective for widespread adoption. This advancement is critical for scaling zero knowledge proof systems to support real-world applications with high throughput and low latency.
Among the most impactful applications of zero knowledge proofs in 2025 are ZK-rollups, which address blockchain scalability challenges by bundling hundreds or thousands of transactions off-chain into a single succinct cryptographic proof posted on-chain. This approach significantly reduces gas fees and network congestion while maintaining security and data integrity.
ZK-rollups operate as layer 2 scaling solutions that shift computation and state storage off the main Ethereum blockchain. They use zero knowledge proofs to validate the correctness of off-chain transactions, enabling a high transaction throughput without compromising security. After processing transactions off-chain, a succinct non-interactive cryptographic proof—often a zk-SNARK—is posted to the mainnet, allowing the network to efficiently verify the validity of the entire batch. The process of verifying these cryptographic proofs ensures the correctness and authenticity of all included transactions without revealing sensitive information.
The efficiency gains are remarkable. For example, in a privacy-preserving withdrawal scenario, a zero knowledge rollup requires only about 296 bytes per transaction, combining essential elements like the root index, nullifier, recipient data, and the zk-SNARK proof. This represents a 77-fold efficiency increase compared to processing transactions directly on layer 1, highlighting the scalability potential of zero knowledge proof systems.
The ZK-rollup ecosystem has experienced explosive growth in 2025, with several projects leading the charge to solve scalability challenges while maintaining security and decentralization. Ethereum-based ZK-rollups have become synonymous with enhanced scalability, improved transaction throughput, and reduced gas fees, all while preserving data privacy and integrity.
One prominent example is zkSync, which continues to evolve as a major player by enabling banks and enterprises to future-proof finance and expand into global digital assets with privacy and regulatory compliance. Projects like zkSync leverage advanced cryptographic protocols and are fundamentally built on top of a zero knowledge proof system to deliver scalable, secure, and privacy-preserving blockchain solutions. These ZK-rollup initiatives are not only improving blockchain infrastructure but also opening new investment opportunities in the decentralized finance space throughout 2025.
In the dynamic ZKP landscape of 2025, analytics platforms play a crucial role in identifying promising projects and market opportunities. Token Metrics has established itself as a premier AI-powered crypto trading and analytics platform, revolutionizing crypto investing with automated trading and real-time insights focused on zero knowledge proof technologies.
Token Metrics’ AI platform provides comprehensive analysis of ZK projects, including ZK-rollups, privacy coins, and infrastructure developments. By leveraging machine learning and data-driven methodologies, Token Metrics helps traders and investors navigate the complex zero knowledge proof ecosystem, identifying trends and evaluating tokenomics and technical progress. The platform also evaluates projects based on factors such as scalability, security, and knowledge complexity of their zero-knowledge proof systems.
The Token Metrics Moon Awards further highlight the most innovative and impactful ZK technologies, recognizing platforms and projects that significantly advance privacy-enhancing technologies and scalability solutions. Through these initiatives, Token Metrics continues to support the growth and maturation of zero knowledge proof systems in the blockchain industry.
Zero knowledge proofs have far-reaching applications beyond simple transaction privacy. By enabling cryptographic proofs that verify conditions without revealing secret information, zero knowledge protocols empower developers to create secure and privacy-preserving decentralized applications.
Key use cases include:
Zero-knowledge proofs can also be used to verify other properties of data, such as account balances or location, without revealing the actual information.
These examples showcase how zero knowledge proofs enable secure, private, and efficient verification across diverse industries, enhancing user privacy and transaction privacy simultaneously.
Despite their promise, zero knowledge proof systems face significant technical and security challenges. The advanced mathematics underlying zero knowledge protocols—such as discrete logarithm problems, quadratic residuosity, prime factorization, and one-way functions—require specialized expertise to implement securely and efficiently.
Ensuring the completeness, soundness, and perfect zero knowledge of proofs demands rigorous testing and formal verification. Circuit-layer vulnerabilities and the risk of dishonest provers attempting to cheat the system must be carefully mitigated. Additionally, the complexity of interactive proofs—protocols that require multiple rounds of communication between the prover and verifier—presents unique challenges. The concurrent execution of multiple zero-knowledge protocols further complicates the design, as maintaining security during concurrent interactions is difficult and often requires specialized protocols like witness-indistinguishability.
To address these issues, the development of user-friendly ZKP frameworks and hardware accelerators is underway, abstracting much of the cryptographic complexity and enabling more secure and scalable implementations. Research into scalable transparent argument systems and succinct non-interactive zero knowledge proofs (SNARKs) continues to advance the field, reducing reliance on trusted setups and enhancing proof validity.
As zero knowledge proofs become integral to blockchain, finance, and digital identity systems, the regulatory environment is rapidly adapting to address their unique capabilities and challenges. Regulatory bodies worldwide are recognizing the potential of zero knowledge proof systems to enhance privacy and security, while also raising important questions about compliance and oversight.
A central issue is how zero knowledge proofs can be used to prove identity, ownership, or compliance without revealing sensitive personal data. This ability to verify statements without revealing underlying information is both a strength and a challenge when it comes to meeting anti-money laundering (AML) and know-your-customer (KYC) requirements. Regulators are exploring how proof systems can be designed to satisfy legal obligations while still protecting user privacy.
In the United States, the Securities and Exchange Commission (SEC) has begun to issue guidance on the use of zero knowledge proofs in blockchain-based securities offerings, emphasizing the need for transparency and market integrity. Meanwhile, the European Union’s General Data Protection Regulation (GDPR) places a strong emphasis on user data protection and control. Zero knowledge protocols offer a promising solution by allowing organizations to prove compliance with data protection laws without revealing or storing unnecessary personal information.
Navigating this evolving regulatory landscape requires a deep understanding of both the technical aspects of zero knowledge proofs and the legal frameworks that govern their use. Collaboration between developers, industry stakeholders, and regulators is essential to ensure that zero knowledge proof systems are developed and deployed in a way that upholds compliance, protects user rights, and fosters innovation. As adoption grows, ongoing dialogue and adaptive regulation will be key to unlocking the full potential of zero knowledge technologies while maintaining trust and accountability in digital systems.
The market for zero knowledge proof technologies is booming in 2025, with growing interest in modular blockchain architectures that integrate ZK-rollups and other privacy-enhancing technologies. The 2nd IEEE International Workshop on Programmable Zero-Knowledge Proofs for Decentralized Applications (ZKDAPPS 2025) underscores the academic and industry focus on advancing ZKP research and practical applications.
Investors are increasingly drawn to infrastructure projects building ZKP tooling, privacy-focused DeFi protocols, and layer 2 scaling solutions. Token Metrics provides invaluable insights into these opportunities, assisting investors in identifying high-growth prospects within the zero knowledge proof ecosystem. As the technology matures, the market is expected to expand further, driven by demand for secure, private, and scalable blockchain solutions.
Zero knowledge blockchain projects are poised to become foundational for the next generation of decentralized applications, enabling developers to build scalable Web3 ecosystems that prioritize user privacy and security. The zero knowledge protocol, a fundamental cryptographic innovation, plays a crucial role in enabling privacy and security by allowing verification without revealing sensitive information. As regulatory pressures and user expectations converge, zero knowledge proofs will become standard infrastructure components for blockchain applications requiring both transparency and confidentiality.
The balance between transparency and privacy, scalability and security, positions zero knowledge proofs as critical tools for mainstream blockchain adoption. Organizations recognize that sustainable blockchain solutions must integrate powerful cryptographic tools like zero knowledge protocols to protect identity, data, and transaction privacy while ensuring system integrity.
Zero knowledge proofs represent a paradigm shift in how privacy and scalability are addressed in blockchain technology throughout 2025. From ZK-rollups transforming Ethereum’s scalability to privacy-preserving DeFi applications, zero knowledge proofs are reshaping the cryptocurrency landscape with hardware acceleration and advanced cryptographic innovations.
For investors and traders, understanding zero knowledge proof technology and its market implications is crucial for making informed decisions. Platforms like Token Metrics offer the analytical tools and insights needed to navigate this complex but promising sector. As we progress through 2025, zero knowledge proofs will continue to drive innovation and create new opportunities for those positioned to capitalize on this revolutionary technology.
The future of blockchain lies in solutions that provide both transparency and privacy, scalability and security. Zero knowledge proofs are the key to unlocking this future, making them essential knowledge for anyone serious about the direction of cryptocurrency and blockchain technology.

%201.svg)
%201.svg)
The Web3 revolution is fundamentally transforming how users interact with digital assets, and at the core of this transformation are Web3 wallets. Before the rise of Web3 wallets, the crypto wallet was the essential tool for securely managing and storing cryptocurrencies, with Web3 wallets representing an evolution of the traditional crypto wallet. These digital wallets serve as essential gateways, providing access to the decentralized web by enabling seamless interactions with blockchain networks, decentralized applications (dApps), and a wide array of crypto assets. As we advance into 2025, gaining a thorough understanding of Web3 wallets is crucial for anyone looking to actively participate in the evolving cryptocurrency ecosystem.
Web3 wallets go far beyond being mere storage solutions for cryptocurrencies. They function as comprehensive digital identity managers, allowing users to securely store, manage, and transfer valuable digital assets while retaining complete control over their private keys. Unlike traditional banking systems or custodial wallets, where institutions hold custody of your funds, Web3 wallets embody the principle of self-custody and true ownership, giving users complete control over their crypto assets. A non custodial wallet, such as Metamask, ensures that only the user has access to their assets and keys, aligning with the principles of decentralization and user sovereignty.
A key difference between Web3 wallets and conventional crypto wallets lies in their ability to interact directly with blockchain networks. While traditional wallets typically support only basic send-and-receive functions, Web3 wallets enable users to connect with smart contracts, decentralized exchanges, NFT marketplaces, and various decentralized finance (DeFi) protocols. These wallets use a public key, which acts as a shareable address derived from the private key, allowing others to send assets to you. The private key is essential for signing transactions and proving ownership, and it must be kept secure to protect your assets. This enhanced functionality makes Web3 wallets indispensable tools for accessing the full spectrum of decentralized finance opportunities and engaging with the decentralized web.
The security market for Web3 wallets is rapidly expanding, with projections estimating a compound annual growth rate (CAGR) of 23.7% from 2024 to 2033, reaching an impressive $68.8 billion by 2033. This growth underscores the critical importance of wallet security as users increasingly entrust these digital wallets with their valuable digital assets.
Recent studies reveal mixed security practices among users: approximately 34.65% of users opt to record and securely store their private keys on paper, 24.75% use encrypted digital storage methods, and only 13.86% rely on professional hardware wallets. These statistics highlight a significant gap in adoption of enhanced security measures, such as hardware wallets, which store private keys offline and provide maximum security.
The security landscape in 2024 has also been challenged by increasingly sophisticated phishing attacks and other cyber threats targeting both decentralized and centralized finance platforms. This evolving threat environment emphasizes the need for robust wallet security measures and comprehensive user education to protect assets effectively.
Web3 wallets come in two primary categories: hot wallets and cold wallets. Hot wallets remain connected to the internet, offering unmatched convenience for frequent transactions and interactions with decentralized applications. Examples include browser extensions like MetaMask, mobile apps such as Trust Wallet, and various web-based wallets. Many hot wallets also feature a built-in dapp browser, enabling users to access and interact with decentralized applications (dApps) directly from within the wallet. These wallets provide an easy-to-use interface and support multichain functionality, allowing users to manage assets across multiple blockchains. However, their constant online connectivity exposes them to higher security risks.
In contrast, cold wallets—often referred to as hardware wallets—store private keys offline, significantly reducing exposure to hacking attempts. Popular hardware wallets like Ledger and Trezor exemplify this category, providing enhanced security for long-term storage of crypto assets. While cold wallets may be less convenient for everyday trading, they offer the highest level of security and are widely regarded as the gold standard for safeguarding valuable digital assets.
Another important distinction is between custodial and non-custodial wallets. Custodial wallets manage private keys on behalf of users, providing familiar login experiences and recovery options similar to traditional online services. Wallets like Coinbase Wallet fall into this category, appealing to newcomers who prefer institutional custody and the convenience of account recovery options. However, custodial wallets require users to trust third-party services, which conflicts with the Web3 ethos of decentralization and self-sovereignty.
Non-custodial wallets, on the other hand, give users complete control over their private keys and funds. This approach aligns with the decentralized web’s core principles, ensuring users have true ownership and control over their digital assets. While non-custodial wallets demand greater personal responsibility—such as securely managing recovery phrases—they empower users with enhanced privacy and freedom. The recovery phrase is a human-readable backup that allows users to restore access to their wallet if needed.
Browser extensions and wallets have become a popular choice for users looking to manage digital assets and interact with decentralized applications (dApps) directly from their web browsers. These browser extensions, such as MetaMask, offer a streamlined and user-friendly interface, making it easy to store, send, and receive cryptocurrencies, as well as interact with smart contracts on various blockchain networks. The convenience of accessing your wallet and assets with just a few clicks has made browser extensions a go-to solution for many in the Web3 space.
However, this convenience comes with its own set of security considerations. Because browser extensions are connected to the internet, they can be susceptible to phishing attacks and other security threats targeting users’ private keys and digital assets. To keep your wallet secure, it’s crucial to choose reputable and well-reviewed browser extensions, regularly update your wallet software, and remain vigilant against suspicious links or pop-ups.
For users seeking enhanced security, pairing a browser extension with a hardware wallet is highly recommended. Hardware wallets store private keys offline, significantly reducing the risk of unauthorized access even if your browser extension is compromised. This combination allows users to interact with decentralized applications and sign transactions securely, ensuring that private keys never leave the safety of the hardware wallet. By following these best practices, users can enjoy the convenience of browser extensions while keeping their digital assets and private keys protected.
As Web3 wallets aim to reach mainstream adoption, delivering an exceptional user experience and intuitive interface is more important than ever. The next generation of users will expect wallets to be as easy to use as traditional financial apps, without needing to understand the complexities of blockchain technology. To meet these expectations, wallet developers are focusing on user-centric design, ensuring that every feature and interaction is clear, accessible, and straightforward.
Key features such as two-factor authentication, transaction verification, and clear asset management tools are becoming standard, providing users with both security and peace of mind. Wallet interfaces should present information in a concise and understandable way, guiding users through each step of managing their digital assets. Adaptability is also crucial—wallets must offer a seamless experience across mobile devices, desktops, and browser extensions, so users can access their assets wherever they are.
By prioritizing intuitive design and robust security features, Web3 wallets can lower the barrier to entry for new users and make managing digital assets a smooth, stress-free experience. This focus on user experience is essential for onboarding the next billion users into the decentralized web.
A seamless user journey and onboarding process are essential for making Web3 wallets accessible to everyone, regardless of their technical background. The best wallets guide users step-by-step through creating a wallet, securing their digital assets, and interacting with decentralized applications. Clear instructions, interactive tutorials, and responsive customer support help users feel confident as they navigate the world of Web3.
User education is a cornerstone of effective onboarding. Leading wallets provide comprehensive resources, including guides on security best practices, explanations of key concepts, and tips for safely managing assets. This educational approach empowers users to make informed decisions and reduces the risk of costly mistakes.
By simplifying the onboarding process and offering robust support, Web3 wallets can help users quickly get started, securely store their assets, and begin interacting with the decentralized ecosystem. Making Web3 technology approachable and understandable is key to driving widespread adoption and ensuring users can fully benefit from the opportunities it offers.
Web3 wallets are not just tools for storing and managing digital assets—they also open the door to a variety of rewards and incentives. Many wallets, including Trust Wallet and Coinbase Wallet, offer users the ability to earn rewards through staking, yield farming, and participation in decentralized finance (DeFi) protocols. These opportunities can provide a valuable source of passive income, making wallets even more attractive for users looking to grow their assets.
To maximize these benefits, users should conduct their own research and carefully review the terms and conditions of each reward program. Understanding the risks, requirements, and potential returns is essential for making informed decisions. Wallets that prioritize transparency make it easy for users to discover, compare, and participate in different earning opportunities.
By taking advantage of these reward programs, users can enhance their Web3 experience and unlock additional value from their digital assets. As wallets continue to innovate, expect even more ways to earn rewards and participate in the decentralized economy directly from your wallet interface.
The Web3 wallet industry is evolving rapidly, with 2025 poised to accelerate innovations that position wallets as essential infrastructure for digital life. Several key trends are shaping this future landscape:
Enhanced User Experience: Developers are striving to create wallet software that combines Web2-like simplicity with full Web3 functionality. This includes streamlined onboarding, intuitive interfaces, and seamless integration with everyday apps, making it easier for users to connect, verify, and manage their assets.
Multi-Chain Interoperability: Modern wallets increasingly support multiple blockchains, allowing users to store and manage tokens, NFTs, and other digital assets across various ecosystems from a single interface. This multichain support addresses the fragmented blockchain landscape and simplifies asset management.
Advanced Security Features: Security remains paramount, with wallets adopting biometric authentication, multi-signature capabilities, and AI-powered fraud detection to significantly reduce risks. These added security layers help users maintain wallet security and protect against phishing attacks and unauthorized transactions.
Social Recovery Options: New wallet architectures are incorporating social recovery mechanisms, enabling users to regain access to their wallets through trusted contacts instead of relying solely on recovery phrases. This innovation enhances account recovery without compromising security.
While Web3 wallets provide the essential infrastructure to store and manage crypto assets, many now allow users to buy, sell, and swap cryptocurrencies directly within the wallet interface, making asset management more efficient. Successful trading in the complex cryptocurrency market requires sophisticated analytics and market intelligence. Platforms like Token Metrics are becoming invaluable resources for traders and investors seeking data-driven insights.
Token Metrics leverages artificial intelligence and machine learning to offer comprehensive crypto research, token ratings, price predictions, and portfolio optimization tools. This next-generation platform consolidates trading signals, market trend analysis, and index data, empowering users to make informed decisions in a highly volatile and sentiment-driven market.
By combining traditional financial analysis with cutting-edge AI technology, Token Metrics helps users identify potential crypto moonshots, optimize their portfolios, and manage risk effectively. This integration of analytics with wallet functionality enables users to authorize transactions confidently and interact with decentralized applications more strategically.
Maintaining wallet security is critical for protecting your digital assets. Here are essential security practices every Web3 wallet user should follow:
Seed Phrase Management: Always store your recovery phrase securely in multiple physical locations, preferably using durable metal backup solutions. Avoid storing seed phrases digitally or sharing them with anyone to prevent unauthorized access.
Transaction Verification: Before authorizing any transaction, carefully verify recipient addresses, transaction details, and smart contract interactions. Vigilance helps defend against phishing attacks and fraudulent transactions. When swapping tokens within your Web3 wallet, always double-check all information to avoid errors or falling victim to scams.
Regular Updates: Keep your wallet software, including browser extensions and mobile apps, up to date. Enable automatic updates where possible to benefit from the latest security patches and enhanced features.
Network Awareness: Exercise caution when connecting to public Wi-Fi networks and consider using VPN services to add privacy layers, reducing exposure to potential network-based attacks.
The integration of exchanges and wallets is playing a pivotal role in bridging the gap between centralized finance (CeFi) and decentralized finance (DeFi). Modern Web3 wallets are increasingly offering seamless connectivity with both centralized exchanges and decentralized platforms, allowing users to manage, swap, and transfer assets across multiple ecosystems without leaving their wallet interface.
This integration enables users to enjoy the liquidity, speed, and familiar features of centralized exchanges while also accessing the transparency, control, and innovative services of DeFi protocols. Features such as in-wallet token swaps, fiat on-ramps, and direct access to decentralized applications are becoming standard, making it easier than ever to move assets between CeFi and DeFi environments.
By supporting multiple blockchains and exchange integrations, Web3 wallets empower users with true ownership and flexibility over their digital assets. This convergence is driving the next generation of financial services, where users can interact with both traditional and decentralized platforms from a single, secure wallet—unlocking new possibilities for trading, investing, and managing crypto assets in 2025 and beyond.
Web3 wallets are increasingly serving as gateways to the expanding decentralized finance ecosystem. They enable users to participate in yield farming, liquidity mining, decentralized exchanges, and lending protocols with ease. The integration between wallets and DeFi platforms is deepening, with features like gas optimization, transaction batching, and automated strategy execution becoming more common.
Looking ahead, wallets are expected to incorporate built-in DeFi functionalities, direct fiat on-ramps, and advanced portfolio management tools. This evolution will further blur the lines between traditional finance and decentralized alternatives, empowering users to earn rewards, swap tokens, collect NFTs, and manage assets across multiple chains—all from a single, secure digital wallet.
Web3 wallets form the foundational infrastructure that enables users to engage confidently with the decentralized economy. As the market evolves with enhanced security features, improved user experiences, and deeper DeFi integration, selecting the right wallet becomes increasingly important for both casual holders and active traders.
Understanding the differences between wallet types, adopting best security practices, and leveraging powerful analytics platforms like Token Metrics will empower users to manage their crypto assets securely and make smarter trading decisions. The future of Web3 wallets is bright, with ongoing innovation focused on making decentralized finance accessible, secure, and user-friendly.
As we progress through 2025, Web3 wallets will continue to play a pivotal role in our digital financial lives, offering users complete control, enhanced security, and seamless interaction with the decentralized web. Embracing these tools is essential for anyone seeking to thrive in the next generation of the internet.

%201.svg)
%201.svg)
As we navigate through 2025, the cryptocurrency landscape continues to evolve at a breakneck speed, with three giants dominating the conversation: Solana, Bitcoin, and Ethereum. These crypto coins represent distinct visions for the future of blockchain technology, each offering unique features and advantages that appeal to different segments of the market. Cryptocurrencies are increasingly viewed as an alternative to traditional currencies and assets, providing new options for storing and transferring value.
Understanding the key differences between Solana vs Bitcoin vs Ethereum is crucial for investors, developers, and crypto enthusiasts who want to stay ahead in this rapidly changing industry. Recent developments, such as the SEC approval of a Bitcoin ETF, have made Bitcoin more accessible to a broader audience, encouraging easier entry into cryptocurrency investing.
Cryptocurrencies are decentralized digital currencies that leverage cryptography to ensure secure and transparent transactions across a global network. Since the inception of Bitcoin, the crypto market has expanded rapidly, introducing a diverse range of crypto coins that serve various purposes. While many investors are drawn to trading crypto for its potential returns, others see cryptocurrencies as a way to participate in decentralized finance (DeFi) protocols or to buy Bitcoin as a long-term store of value.
Unlike Bitcoin, which primarily functions as a decentralized digital currency and a hedge against traditional financial systems, other blockchain platforms like Ethereum and Solana have evolved to power decentralized applications and smart contracts. The Solana blockchain, for example, is renowned for its high-speed, low-cost transactions, making it a popular choice among developers and investors seeking scalable solutions. As the crypto market matures, these platforms continue to drive innovation, offering new ways to store, transfer, and create value in a secure and decentralized manner.
The crypto market in 2025 has matured significantly, marked by increased institutional adoption and broader mainstream acceptance. As of September 15, 2025, Solana (SOL) is trading at an impressive price of $235.69, boasting a market capitalization of $138.75 billion. This represents remarkable growth from its previous lows and highlights Solana’s rise as a serious competitor in the blockchain space.
Meanwhile, Bitcoin (BTC) remains solidly above $118,000, reinforcing its status as digital gold and a reliable store of value. Ethereum (ETH), on the other hand, is on track for a consistent recovery, driven by ongoing upgrades and expanding use cases. This overall bullish sentiment reflects the growing confidence investors have in these leading blockchain platforms.
For traders and analysts seeking comprehensive insights into the crypto market, Token Metrics stands out as a premier crypto trading and analytics platform. It offers advanced AI-driven analysis, price predictions, and portfolio optimization tools that help thousands of investors navigate the volatile cryptocurrency market with confidence.
Bitcoin continues to reign as the undisputed king of cryptocurrencies, widely regarded as the original decentralized digital currency and a trusted store of value. Unlike traditional currencies, Bitcoin operates independently of any central bank, further emphasizing its decentralized nature. Its primary value proposition lies in its role as digital gold—a decentralized store of value that serves as a hedge against the traditional banking system and fiat currencies like the dollar.

Institutional adoption of Bitcoin has accelerated in 2025, with an increasing number of corporations adding BTC to their treasury reserves. This growing acceptance underscores Bitcoin’s reputation as a safe haven asset in times of economic uncertainty. The Bitcoin decentralized network enables secure, peer-to-peer transactions, which are fundamental to its accessibility and resilience.
Bitcoin’s strength is rooted in its simplicity and security. The Bitcoin network has operated without major issues for over 15 years, building unmatched trust among investors worldwide. In 2025, Bitcoin’s development continues with new commits for Taproot++ features, including experimentation with vault primitives, demonstrating ongoing commitment to improving security and functionality despite its mature status. As a store of value, Bitcoin is often compared to precious metals like gold, with both serving as safe haven assets and stores of wealth.
However, Bitcoin’s limitations are well-known. Its consensus mechanism, Proof of Work (PoW), demands significant energy consumption, raising environmental concerns. Additionally, Bitcoin processes roughly 7 transactions per second, resulting in slower transaction speeds compared to newer blockchain platforms. This makes Bitcoin less suitable for applications requiring high-frequency transactions but reinforces its role as a secure and decentralized store of value and as a form of digital money used for both storing value and as a medium of exchange.
Unlike some other cryptocurrencies that may be classified as securities, Bitcoin is generally considered a commodity, which subjects it to lighter regulatory oversight and has important implications for its adoption and ETF approval prospects.
Ethereum stands as the second largest cryptocurrency by market capitalization, trailing only Bitcoin. Unlike Bitcoin, Ethereum functions as a versatile blockchain platform designed to power decentralized applications (DApps) and decentralized finance (DeFi) protocols through its smart contract capabilities.

Ethereum’s ecosystem has expanded rapidly in 2025. Notably, Layer 2 scaling solutions like StarkNet and zkSync have attracted contributions from over 1,100 developers, enhancing Ethereum’s performance and addressing scalability challenges. These advancements enable Ethereum to support a wide range of Solana vs Bitcoin vs Ethereum: The Ultimate 2025 Cryptocurrency Showdown
As we navigate through 2025, the cryptocurrency landscape continues to evolve at a breakneck speed, with three giants dominating the conversation: Solana, Bitcoin, and Ethereum. These crypto coins represent distinct visions for the future of blockchain technology, each offering unique features and advantages that appeal to different segments of the market. Understanding the key differences between Solana vs Bitcoin vs Ethereum is crucial for investors, developers, and crypto enthusiasts who want to stay ahead in this rapidly changing industry.
The crypto market in 2025 has matured significantly, marked by increased institutional adoption and broader mainstream acceptance. As of September 15, 2025, Solana (SOL) is trading at an impressive price of $235.69, boasting a market capitalization of $138.75 billion. This represents remarkable growth from its previous lows and highlights Solana’s rise as a serious competitor in the blockchain space.
Meanwhile, Bitcoin (BTC) remains solidly above $118,000, reinforcing its status as digital gold and a reliable store of value. Ethereum (ETH), on the other hand, is on track for a consistent recovery, driven by ongoing upgrades and expanding use cases. This overall bullish sentiment reflects the growing confidence investors have in these leading blockchain platforms.
For traders and analysts seeking comprehensive insights into the crypto market, Token Metrics stands out as a premier crypto trading and analytics platform. It offers advanced AI-driven analysis, price predictions, and portfolio optimization tools that help thousands of investors navigate the volatile cryptocurrency market with confidence.
Bitcoin continues to reign as the undisputed king of cryptocurrencies, widely regarded as the original decentralized digital currency and a trusted store of value. Its primary value proposition lies in its role as digital gold—a decentralized store of value that serves as a hedge against the traditional banking system and fiat currencies like the dollar.
Institutional adoption of Bitcoin has accelerated in 2025, with an increasing number of corporations adding BTC to their treasury reserves. This growing acceptance underscores Bitcoin’s reputation as a safe haven asset in times of economic uncertainty.
Bitcoin's strength is rooted in its simplicity and security. The Bitcoin network has operated without major issues for over 15 years, building unmatched trust among investors worldwide. In 2025, Bitcoin's development continues with new commits for Taproot++ features, including experimentation with vault primitives, demonstrating ongoing commitment to improving security and functionality despite its mature status.
However, Bitcoin’s limitations are well-known. Its consensus mechanism, Proof of Work (PoW), demands significant energy consumption, raising environmental concerns. Additionally, Bitcoin processes roughly 7 transactions per second, resulting in slower transaction speeds compared to newer blockchain platforms. This makes Bitcoin less suitable for applications requiring high-frequency transactions but reinforces its role as a secure and decentralized store of value.
Ethereum stands as the second largest cryptocurrency by market capitalization, trailing only Bitcoin. Unlike Bitcoin, Ethereum functions as a versatile blockchain platform designed to power decentralized applications (DApps) and decentralized finance (DeFi) protocols through its smart contract capabilities.
Ethereum’s ecosystem has expanded rapidly in 2025. Notably, Layer 2 scaling solutions like StarkNet and zkSync have attracted contributions from over 1,100 developers, enhancing Ethereum’s performance and addressing scalability challenges. These advancements enable Ethereum to support a wide range of decentralized services while maintaining security and decentralization.
Ethereum’s versatility is its greatest strength. It hosts the majority of blockchain innovation, from DeFi protocols and NFT marketplaces to enterprise blockchain solutions and tokenization platforms. However, Ethereum remains volatile, with its price potentially rising above $5,000 or falling below $2,000 depending on market trends, regulatory developments, and technological upgrades such as Ethereum ETFs and institutional investments.
Token Metrics’ advanced analytics platform offers real-time tracking of Ethereum’s extensive DeFi ecosystem, helping investors and developers identify emerging opportunities and assess risks across hundreds of Ethereum-based protocols.
Solana has emerged as the most formidable challenger to Ethereum’s smart contract dominance. In 2024 and continuing into 2025, Solana experienced a significant rise in new token launches, accounting for over 87% of all tokens created across tracked platforms. This surge is largely attributed to Solana’s low transaction fees and exceptional speed.

The Solana blockchain boasts technical specifications that enable thousands of transactions per second with minimal fees, making it ideal for high-frequency trading, gaming, and consumer applications that demand fast, cheap transactions. However, Solana is considered more centralized than Bitcoin because running nodes on its network requires higher hardware specifications, which limits the number of participants who can operate nodes. Nodes in Solana are responsible for validating transactions, maintaining the ledger, and supporting the network’s speed and scalability, but the higher requirements for nodes can impact the overall decentralization of the network. Its unique consensus mechanism combines Proof of History (PoH) with Proof of Stake (PoS), enabling parallel transaction processing and remarkable scalability without relying on traditional Layer 2 solutions.
Looking ahead to 2026, Solana is poised to continue its upward trajectory, with price projections ranging between $400 and $450. This growth is expected to be fueled by further advancements in blockchain scalability and increasing adoption across DeFi and NFT sectors.
Solana’s ecosystem has flourished in niches where Ethereum’s higher fees create barriers to entry. It has become a hub for memecoin trading, gaming, and decentralized applications that require faster speeds and lower costs.
At the heart of every cryptocurrency lies a consensus mechanism—a system that ensures all transactions are validated and recorded securely across the network. In the crypto market, the most common consensus mechanisms are Proof of Work (PoW), Proof of Stake (PoS), and Proof of History (PoH), each with its own approach to maintaining trust and security.
Bitcoin relies on Proof of Work, where miners use computational power to solve complex puzzles, validate transactions, and create new blocks. This process is energy-intensive but has proven effective in securing the Bitcoin network. Solana, on the other hand, combines Proof of Stake with its innovative Proof of History, allowing validators to process transactions in parallel and achieve much faster speeds with greater energy efficiency. Ethereum has transitioned from PoW to PoS, enabling the network to scale more efficiently while reducing its environmental impact. Understanding these consensus mechanisms is crucial for anyone looking to invest in or use cryptocurrencies, as they directly influence the network’s security, scalability, and overall performance.
When comparing Solana vs Bitcoin vs Ethereum, the differences in their underlying architecture and consensus mechanisms are key to understanding their unique strengths. Block creation and validation play a crucial role in determining transaction throughput and network speed, with each blockchain handling blocks differently to optimize performance.
Bitcoin uses Proof of Work (PoW), prioritizing security and decentralization over speed. Its conservative approach ensures immutability but limits transaction throughput. Bitcoin’s consensus mechanism gains unmatched security and resistance to attacks, but at the cost of efficiency.
Ethereum transitioned to Proof of Stake (PoS) with Ethereum 2.0, significantly improving energy efficiency while maintaining decentralization. Additionally, Layer 2 solutions like Arbitrum and Optimism offer scalability enhancements without compromising the security of the Ethereum main chain. Ethereum gains scalability and reduced energy consumption through its PoS upgrade and Layer 2 integrations.
Solana’s innovative Proof of History (PoH) consensus mechanism, combined with PoS, allows for parallel transaction processing, resulting in much faster speeds and higher scalability. Unlike Bitcoin and Ethereum, Solana achieves these speeds without relying on Layer 2 scaling, setting it apart as a high-performance blockchain platform. The robust code underlying each blockchain is essential for ensuring both security and optimal performance, making software implementation a critical factor in their ongoing development.
Tokenomics—the economic design and distribution of cryptocurrency tokens—plays a pivotal role in shaping the value and utility of each crypto asset. Bitcoin’s tokenomics are defined by its fixed supply of 21 million coins, making it a secure store of value and a popular hedge against inflation. This scarcity is a key reason why many investors choose to buy Bitcoin as a long-term investment.
Solana’s tokenomics are more dynamic, with a variable supply and a focus on incentivizing network participation and powering decentralized applications. The Solana blockchain is designed to support a wide range of use cases, from high-frequency trading to gaming and DeFi protocols, making it a versatile platform for developers and users alike.
Ethereum stands out for its robust support of smart contracts and decentralized finance. Its token, ETH, is essential for executing transactions and interacting with DeFi protocols, NFT marketplaces, and other decentralized applications. As a result, Ethereum has become a cornerstone of the crypto market, driving innovation and enabling new forms of value creation. For investors and developers, understanding the tokenomics and use cases of each cryptocurrency is key to navigating the rapidly evolving market.
As the crypto market grows, regulation and security have become top priorities for investors and users. The regulatory landscape for cryptocurrency is still developing, with some countries embracing clear guidelines while others impose stricter controls or outright bans. This patchwork of regulations can create uncertainty and contribute to the market’s volatility.
Security is another critical concern, as the decentralized nature of crypto makes it a target for hackers and scammers. High-profile breaches of exchanges and wallets have underscored the importance of robust security measures. Investors are encouraged to use secure wallets, enable two-factor authentication, and stay informed about the latest security practices to protect their assets. As the industry matures, both regulation and security are expected to play increasingly important roles in shaping the future of the crypto market, helping to build trust and stability for all participants.
In 2025, the primary reason for investing in cryptocurrencies is long-term growth potential, cited by 49% of respondents, while
investors can purchase cryptocurrencies using various methods, including bank transfer, which allows for secure and direct funding from their bank accounts.
Cryptocurrencies enable secure transactions over the internet, making them accessible to a global audience.
Choosing which cryptocurrency to invest in or use requires a thoughtful and informed approach. Investors should carefully research each asset’s tokenomics, consensus mechanism, and real-world use cases, as well as consider the security and regulatory environment surrounding the crypto market. Staying updated with the latest news and market trends is essential, given the volatile nature of cryptocurrencies.
It’s also important for investors to assess their own financial goals and risk tolerance before making any decisions. Whether you’re interested in decentralized finance, trading, or using crypto as a store of value, taking the time to understand the unique features of Bitcoin, Solana, and Ethereum can help you make confident choices. By prioritizing research and security, investors can better navigate the dynamic world of crypto and position themselves for long-term value and success.

%201.svg)
%201.svg)
The blockchain landscape continues to evolve at a breakneck speed, with two titans standing at the forefront of innovation: Ethereum, the established giant, and Solana, the rising challenger. At first glance, Solana and Ethereum may appear similar or direct rivals, but deeper differences set them apart. As we navigate through 2025, the competition between these ecosystems has intensified, creating compelling opportunities for traders, developers, and investors alike. Understanding the key metrics and performance indicators of both networks is crucial for making informed investment decisions in today’s dynamic crypto market. This comprehensive comparison of Solana vs Ethereum will explore their market performance, user adoption, technical capabilities, transaction costs, ecosystems, and future outlook to help you navigate the rapidly evolving blockchain technology space.
In 2025, the market performance of Solana and Ethereum reveals distinct trajectories that highlight their evolving roles in the crypto market. Solana has demonstrated remarkable resilience and growth, with its native SOL token experiencing significant price appreciation. This surge has elevated Solana’s market capitalization, solidifying its position as a major player within the broader crypto ecosystem. The rapid expansion of the Solana blockchain and its ecosystem has attracted both retail and institutional investors looking for high performance and cost efficiency. Solana also draws significant on-chain capital, including assets and staking yields, which further contribute to its momentum.

Ethereum, on the other hand, remains a stalwart in the blockchain space. Despite facing different market dynamics, Ethereum continues to show impressive stability amid fluctuations. This resilience is bolstered by significant technological advancements, including Ethereum’s transition to a proof of stake consensus mechanism and the growing adoption of Layer-2 scaling solutions such as Arbitrum and Optimism. These upgrades have enhanced Ethereum’s scalability and user experience, strengthening its market position. Ethereum attracts substantial institutional capital and large holdings, providing a strong funding base for ongoing development and growth.
The SOL/ETH ratio continues to reflect shifting market dynamics, illustrating Solana’s growing market presence relative to Ethereum. This ratio provides valuable insight into investor sentiment and the comparative value of these two blockchain platforms as they vie for dominance in the decentralized finance (DeFi) and smart contract space.

When it comes to real-world usage and network adoption, Solana stands out with impressive user engagement metrics. The Solana network boasts approximately 3.25 million daily active users, significantly surpassing Ethereum’s 410,000+ daily active users. This level of engagement translates into substantial transaction volume, with Solana processing around 35.99 million daily transactions compared to Ethereum’s 1.13 million. These figures highlight Solana’s appeal to users who prioritize speed and low transaction fees.
The growth of new addresses further underscores Solana’s expanding user base. Solana generates about 56.31 million monthly new addresses, dwarfing Ethereum’s 7.18 million. This rapid increase reflects Solana’s ability to attract users with its high speed, low cost, and high throughput capabilities. Many DeFi protocols and decentralized applications (dApps) have flourished on Solana, benefiting from the network’s parallel execution and low latency.
Ethereum, with its largest developer ecosystem and established infrastructure, continues to attract developers and users focused on security, decentralization, and a broad array of services. Its ecosystem supports tokenized stocks, automated market makers, and decentralized exchanges, maintaining its role as the backbone of many DeFi and NFT projects.
The technical differences between Solana and Ethereum are fundamental to their respective value propositions and use cases. Solana’s architecture uniquely combines Proof of Stake (PoS) with Proof of History (PoH), a consensus mechanism that timestamps transactions to enable parallel processing. This innovative approach allows Solana to achieve exceptional scalability and performance metrics, making it the fastest blockchain platform currently available.
In real-world terms, Solana handles approximately 870.6 transactions per second (TPS), with observed peaks reaching up to 4,709 TPS. The network’s theoretical maximum throughput is an astounding 65,000 TPS, positioning it well for future growth and high-frequency applications. Solana’s block time is approximately 0.39 seconds, with transaction finality achieved in about 12.8 seconds, delivering a low-latency user experience.
Ethereum’s base layer, by contrast, currently processes around 15 to 30 TPS. However, Ethereum’s development strategy focuses on modular scaling through Layer-2 solutions rather than maximizing throughput at the base layer. This approach balances scalability with network security and decentralization, which remain top priorities for Ethereum’s large and diverse user base. The network’s ongoing upgrades, including danksharding, aim to improve transaction throughput while maintaining robust security guarantees.
For developers, Ethereum’s mature smart contract platform and vast array of tools provide a rich environment for building decentralized applications. Meanwhile, Solana’s high throughput and low latency make it particularly attractive for DeFi protocols, blockchain gaming, and applications requiring rapid transaction finality.
Transaction costs are a critical factor when comparing Solana vs Ethereum, especially for users and developers engaged in decentralized finance and high-frequency trading. Solana excels in cost efficiency, maintaining remarkably low fees with an average transaction cost of approximately $0.00025 (0.0001 SOL). This low cost makes Solana highly attractive for micropayments, DeFi interactions, and applications that require frequent transactions without incurring prohibitive expenses.
Ethereum’s fee structure, centered around gas fees, is more complex and often volatile. Gas fees can fluctuate widely, ranging from $1 to $30 during periods of high network congestion. The average gas price typically varies between 2 to 99 Gwei, which can make using Ethereum costly during peak times. This variability has driven many users to Layer-2 solutions that offer reduced fees while preserving Ethereum’s security and decentralization benefits.
The economic models of both networks also differ in how they incentivize participation. Ethereum’s proof of stake consensus mechanism allows users to stake their ETH and earn staking rewards, providing higher staking yields and encouraging network security through economic incentives. Solana also employs staking, with SOL holders able to stake tokens to support network security and earn rewards, although its consensus mechanism’s hybrid nature differentiates its staking dynamics.
Both Solana and Ethereum have cultivated vibrant ecosystems, but each with unique strengths and focuses. Ethereum remains the largest smart contract platform with the most extensive developer ecosystem. Its comprehensive tooling, documentation, and mature infrastructure have fostered a wide array of decentralized applications, from DeFi protocols and NFT marketplaces to enterprise blockchain solutions. Ethereum’s ecosystem continues to evolve quickly, supported by robust developer experience and a large community.
Solana, while younger, has rapidly gained traction, particularly in sectors demanding high performance and low fees. The Solana ecosystem is evolving quickly, with new SDKs, libraries, and projects emerging at a rapid pace. It has become synonymous with innovation in DeFi and NFTs, attracting projects that benefit from its high throughput and cost efficiency. Gaming applications and consumer-facing dApps have found particular success on Solana, leveraging its architecture to deliver seamless and engaging user experiences. Wallets like Phantom have further enhanced user accessibility to the Solana ecosystem. Phantom wallet enables bridging tokens across Solana, Ethereum, and other blockchains, and supports both browser extensions and mobile apps for cross-chain operations.
It is worth noting that Solana’s architecture supports parallel execution, which differentiates it from Ethereum’s sequential processing model. This technical advantage enables Solana to handle a higher volume of transactions simultaneously, fueling its ecosystem growth. However, despite these strengths, Solana has experienced network outages in the past, which have impacted user confidence and ecosystem development, though ongoing improvements aim to address these issues.
Smart contracts are the backbone of blockchain innovation, enabling self-executing agreements with the terms directly embedded in code. This technology powers a vast array of decentralized applications (dApps), from decentralized finance (DeFi) protocols and non-fungible tokens (NFTs) to gaming and tokenized stocks. Both Solana and Ethereum support robust smart contract development, but each brings unique strengths to the table.
Ethereum remains the established smart contract platform, boasting the largest developer ecosystem in the crypto market. Its mature infrastructure supports a wide range of DeFi protocols, including lending platforms, decentralized exchanges, and automated market makers. This extensive network has made Ethereum the go-to choice for developers building complex decentralized applications and for investors seeking exposure to the heart of decentralized finance. The transition to a Proof of Stake (PoS) consensus mechanism has further enhanced Ethereum’s network security and reduced its environmental impact, making it more attractive to environmentally conscious users and institutional investors.
However, Ethereum’s base layer still faces challenges with gas fees and transaction throughput, which can impact cost efficiency and user experience—especially during periods of high network activity. While Layer-2 solutions are helping to alleviate these issues, the need for scalability remains a key consideration for developers and users alike.
On the other hand, the Solana blockchain is engineered for high performance, low latency, and cost efficiency. Its innovative architecture, combining Proof of History (PoH) with parallel execution, enables high throughput and rapid transaction processing. This makes Solana particularly well-suited for applications that demand speed and low fees, such as high-frequency trading, real-time gaming, and consumer-facing dApps. The Solana ecosystem has seen rapid growth in recent months, with a surge in the creation and trading of tokenized stocks—digital representations of traditional equities that offer greater accessibility and liquidity in the crypto market.
Developers are increasingly drawn to Solana for its ease of use, high speed, and low transaction fees, while users benefit from seamless experiences through popular wallets like Phantom. The Solana vs Ethereum debate often centers on these key differences: Ethereum’s established smart contract platform and security versus Solana’s high performance and cost efficiency.
For investors looking to buy stock in blockchain technology or directly invest in SOL or ETH, it’s essential to conduct your own research, analyze market data, and consider factors such as network security, exchange commission, and potential for growth. Resources like Motley Fool’s Stock Advisor have demonstrated market crushing outperformance compared to the S&P 500, with a total average return worth noting for those aiming to produce monster returns in the evolving crypto market.
Ultimately, both Solana and Ethereum offer compelling opportunities for developers, users, and investors. The choice depends on your specific needs—whether you prioritize the largest developer ecosystem and established DeFi protocols with Ethereum, or seek high throughput, low fees, and rapid innovation within the Solana ecosystem. As blockchain technology continues to evolve quickly, staying informed about the latest trends and key differences between these platforms will help you make smarter investment decisions and capitalize on the next wave of decentralized applications.
From a trading perspective, both Solana and Ethereum offer distinct advantages depending on investor goals and risk tolerance. Ethereum’s established market cap and broader institutional adoption provide stability and predictable liquidity. The network’s transition to proof of stake has introduced new staking rewards, creating yield opportunities for long-term holders seeking steady income.
Solana’s rapid growth and technical superiority in speed and cost efficiency have made it attractive to growth-oriented investors. The network’s potential to support emerging trends in blockchain gaming, consumer applications, and high-frequency DeFi protocols positions SOL as a compelling investment for those willing to embrace higher volatility and risk.
Market data over the past three months reveals that Solana’s performance has delivered market crushing outperformance compared to many other coins, attracting attention from investors looking to produce monster returns. However, Ethereum remains a cornerstone of the crypto market, with its vast ecosystem and ongoing upgrades ensuring its continued relevance.
Looking ahead through 2025 and beyond, both Solana and Ethereum are pursuing ambitious upgrade paths that will shape their strategic positioning in the blockchain space. Solana’s upcoming Firedancer upgrade promises to dramatically increase transaction throughput, potentially handling up to 1 million transactions per second while further reducing fees. This development could cement Solana’s status as the go-to platform for performance-critical applications requiring low latency and high speed.
Ethereum’s roadmap focuses on enhancing scalability through danksharding and deeper Layer-2 integration. While these improvements may not reach Solana’s raw throughput numbers, they emphasize Ethereum’s commitment to maintaining decentralization and network security, which are highly valued by institutional users and developers.
For investors and developers, understanding these trajectories is essential. Solana’s focus on speed and low cost complements Ethereum’s emphasis on security and decentralization, suggesting that both networks will coexist and serve different segments of the blockchain market in the coming years.
For traders and investors, the choice between Solana and Ethereum is not necessarily binary. Each network offers distinct use cases, risk profiles, and growth potentials. Ethereum provides stability, institutional trust, and a proven track record, making it suitable for conservative investment strategies. Meanwhile, Solana offers innovation, high performance, and the potential for higher returns, appealing to those seeking growth opportunities in the evolving crypto market.
Success in crypto trading in 2025 increasingly depends on understanding these fundamental network differences and how they translate into market opportunities and risks. Utilizing professional crypto trading platforms that provide comprehensive market data, transaction volumes, token metrics, and network performance insights is crucial for making well-informed decisions.
Ultimately, Solana and Ethereum both play crucial roles in the future of decentralized finance and Web3 applications. By conducting your own research and staying informed about ongoing developments, you can strategically position your investment portfolio to benefit from the dynamic and rapidly evolving blockchain ecosystem.
Image source: Market data and performance charts from leading crypto analytics platforms.
If you are ready to start investing, consider the key differences between Solana and Ethereum carefully. Whether you choose to buy stock related to blockchain technology or invest directly in these coins, understanding their unique value propositions will help you navigate the exciting opportunities that lie ahead. For further insights, resources like Motley Fool and Stock Advisor provide valuable analysis on market trends and investment strategies, helping you produce monster returns with informed decisions.

%201.svg)
%201.svg)
Traditional crypto market analysis suggests we should be deep into altcoin season by now. Historically, extended bull runs trigger periods where 80-90% of returns come from alternative cryptocurrencies rather than Bitcoin. Yet current data shows only 58% of returns coming from altcoins – surprising for what should be a bull market peak.

This deviation from historical patterns reveals fundamental changes in crypto market structure that most investors are missing.
Instead of broad-based altcoin rallies, 2025 has seen strategic rotation into select large-cap alternatives:
This selectivity suggests institutional investors are driving market movements rather than retail speculation. Professional capital focuses on projects with clear value propositions and established track records.
The 90% altcoin dominance threshold that historically marked cycle peaks may no longer apply. Several structural changes explain this shift:
Increased Market Sophistication: Institutional participation has reduced the wild speculation that drove previous altcoin seasons.
Regulatory Clarity: Projects with clear regulatory positioning (like ETF-eligible assets) receive disproportionate attention.
Utility Focus: Tokens with actual usage (stablecoins, DEX tokens, infrastructure) outperform purely speculative assets.
Narrative Concentration: Rather than lifting all boats, capital flows to tokens aligned with specific themes (AI, gaming, DeFi infrastructure).
If traditional altcoin season patterns are broken, crypto cycles may extend longer than historically expected. Previous cycles lasted roughly 4 years, but structural changes suggest 2025-2026 could represent a single extended cycle.
Supporting evidence includes:
While meme coins capture headlines, two sectors are quietly attracting significant institutional investment: gaming and artificial intelligence.
Gaming projects have spent years building AAA-quality experiences, waiting for favorable market conditions to launch. Projects like Star Atlas have continued development through bear markets, potentially positioning them for significant growth during the next narrative cycle.
AI-focused crypto projects have attracted substantial venture funding despite recent price underperformance. This suggests institutional conviction in long-term utility, even as short-term trading favors other sectors.
Given these structural changes, successful crypto investing requires updated strategies:
Narrative Rotation: Rather than broad altcoin exposure, focus on tokens aligned with current market themes.
Quality Focus: Emphasize projects with real usage, strong teams, and institutional backing over speculative plays.
Shortened Time Horizons: The rapid attention shifts require more active position management rather than long-term holds.
Platform Intelligence: Use analytics tools to identify emerging trends before they become obvious to broader markets.
The emergence of specialized stablecoin blockchains represents one of the most overlooked investment opportunities. Projects like Plasma launching with immediate billion-dollar deposits suggest massive latent demand for improved stablecoin infrastructure.
This sector benefits from:
Rather than waiting for traditional altcoin season, successful investors should prepare for continued narrative-driven markets. This means:
The altcoin season of 2025-2026 won't look like previous cycles. But for investors who adapt their strategies to current market realities, the opportunities may be even greater.

%201.svg)
%201.svg)
On a single day in September 2025, Pump.fun generated over $2 million in fees – a 20x increase from their typical $100,000-$150,000 daily average. This explosive growth wasn't driven by market manipulation or celebrity endorsements. Instead, it came from a simple innovation: letting creators stream while launching their tokens.
This represents more than just a technical upgrade. It's the beginning of creator economy crypto.
Pump.fun's new dynamic fee model and streaming integration has created an entirely new category: creator coins. Instead of anonymous meme tokens, creators can now launch personalized tokens while streaming live to their audiences.

The mechanics are elegant:
Other platforms are taking notice. Bong Fun and additional launchpads are implementing similar streaming features, suggesting this trend will expand across the ecosystem.
What makes this model powerful is how it monetizes attention. Traditional social media platforms capture value from creator content while sharing minimal revenue. Creator coins flip this dynamic, allowing creators to directly monetize their audience engagement through token ownership.
Consider the potential:
This creates a self-reinforcing cycle where content quality, audience engagement, and financial returns align.
The streaming coin model extends beyond entertainment. Potential applications include:
Research and Development: Scientists or researchers could fund projects through token sales, with token value tied to research outcomes.
Community Building: Online communities could launch governance tokens during live events, creating immediate stakeholder engagement.
Pump.fun's success reflects broader market maturation. Rather than relying on speculative bubbles, the platform creates sustainable value by connecting content creation with financial participation.
This model addresses crypto's adoption challenge by making tokens useful rather than purely speculative. When tokens represent participation in creator economies, they gain utility beyond price appreciation.
The creator coin trend suggests several investment strategies:
The key is recognizing that creator coins represent a new asset class combining entertainment, community participation, and speculative investment.

 Create Your Free Account
Create Your Free Account9450 SW Gemini Dr
PMB 59348
Beaverton, Oregon 97008-7105 US
.svg)




.png)
Token Metrics Media LLC is a regular publication of information, analysis, and commentary focused especially on blockchain technology and business, cryptocurrency, blockchain-based tokens, market trends, and trading strategies.
Token Metrics Media LLC does not provide individually tailored investment advice and does not take a subscriber’s or anyone’s personal circumstances into consideration when discussing investments; nor is Token Metrics Advisers LLC registered as an investment adviser or broker-dealer in any jurisdiction.
Information contained herein is not an offer or solicitation to buy, hold, or sell any security. The Token Metrics team has advised and invested in many blockchain companies. A complete list of their advisory roles and current holdings can be viewed here: https://tokenmetrics.com/disclosures.html/
Token Metrics Media LLC relies on information from various sources believed to be reliable, including clients and third parties, but cannot guarantee the accuracy and completeness of that information. Additionally, Token Metrics Media LLC does not provide tax advice, and investors are encouraged to consult with their personal tax advisors.
All investing involves risk, including the possible loss of money you invest, and past performance does not guarantee future performance. Ratings and price predictions are provided for informational and illustrative purposes, and may not reflect actual future performance.



