Top Crypto Trading Platforms in 2025







%201.svg)
%201.svg)
Big news: We’re cranking up the heat on AI-driven crypto analytics with the launch of the Token Metrics API and our official SDK (Software Development Kit). This isn’t just an upgrade – it's a quantum leap, giving traders, hedge funds, developers, and institutions direct access to cutting-edge market intelligence, trading signals, and predictive analytics.
Crypto markets move fast, and having real-time, AI-powered insights can be the difference between catching the next big trend or getting left behind. Until now, traders and quants have been wrestling with scattered data, delayed reporting, and a lack of truly predictive analytics. Not anymore.
The Token Metrics API delivers 32+ high-performance endpoints packed with powerful AI-driven insights right into your lap, including:
Getting started with the Token Metrics API is simple:
At Token Metrics, we believe data should be decentralized, predictive, and actionable.
The Token Metrics API & SDK bring next-gen AI-powered crypto intelligence to anyone looking to trade smarter, build better, and stay ahead of the curve. With our official SDK, developers can plug these insights into their own trading bots, dashboards, and research tools – no need to reinvent the wheel.
%201.svg)
%201.svg)
The Layer 1 landscape is consolidating as users and developers gravitate to chains with clear specialization. Bitcoin Cash positions itself as a payment-focused chain with low fees and quick settlement for everyday usage.
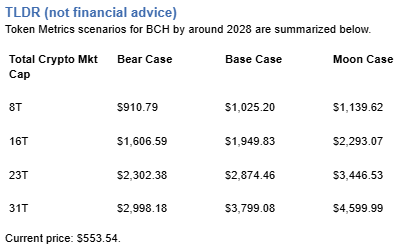
The scenario projections below map potential outcomes for BCH across different total crypto market sizes. Base cases assume steady usage and listings, while moon scenarios factor in stronger liquidity and accelerated adoption.
Disclosure
Educational purposes only, not financial advice. Crypto is volatile, do your own research and manage risk.
How to read it: Each band blends cycle analogues and market-cap share math with TA guardrails. Base assumes steady adoption and neutral or positive macro. Moon layers in a liquidity boom. Bear assumes muted flows and tighter liquidity.
TM Agent baseline:
Token Metrics lead metric for Bitcoin Cash, cashtag $BCH, is a TM Grade of 54.81%, which translates to Neutral, and the trading signal is bearish, indicating short-term downward momentum. This implies Token Metrics views $BCH as mixed value long term: fundamentals look strong, while valuation and technology scores are weak, so upside depends on improvements in adoption or technical development. Market context: Bitcoin has been setting market direction, and with broader risk-off moves altcoins face pressure, which increases downside risk for $BCH in the near term.
Live details:
Affiliate Disclosure: We may earn a commission from qualifying purchases made via this link, at no extra cost to you.
Token Metrics scenarios span four market cap tiers, each representing different levels of crypto market maturity and liquidity:




Each tier assumes progressively stronger market conditions, with the base case reflecting steady growth and the moon case requiring sustained bull market dynamics.
Bitcoin Cash represents one opportunity among hundreds in crypto markets. Token Metrics Indices bundle BCH with top one hundred assets for systematic exposure to the strongest projects. Single tokens face idiosyncratic risks that diversified baskets mitigate.
Historical index performance demonstrates the value of systematic diversification versus concentrated positions.
Bitcoin Cash is a peer-to-peer electronic cash network focused on fast confirmation and low fees. It launched in 2017 as a hard fork of Bitcoin with larger block capacity to prioritize payments. The chain secures value transfers using proof of work and aims to keep everyday transactions affordable.
BCH is used to pay transaction fees and settle transfers, and it is widely listed across major exchanges. Adoption centers on payments, micropayments, and remittances where low fees matter. It competes as a payment‑focused Layer 1 within the broader crypto market.
Token Metrics AI provides comprehensive context on Bitcoin Cash's positioning and challenges.
Vision:
Bitcoin Cash (BCH) is a cryptocurrency that emerged from a 2017 hard fork of Bitcoin, aiming to function as a peer-to-peer electronic cash system with faster transactions and lower fees. It is known for prioritizing on-chain scalability by increasing block sizes, allowing more transactions per block compared to Bitcoin. This design choice supports its use in everyday payments, appealing to users seeking a digital cash alternative. Adoption has been driven by its utility in micropayments and remittances, particularly in regions with limited banking infrastructure. However, Bitcoin Cash faces challenges including lower network security due to reduced mining hash rate compared to Bitcoin, and ongoing competition from both Bitcoin and other scalable blockchains. Its value proposition centers on accessibility and transaction efficiency, but it operates in a crowded space with evolving technological and regulatory risks.
Problem:
The project addresses scalability limitations in Bitcoin, where rising transaction fees and slow confirmation times hinder its use for small, frequent payments. As Bitcoin evolved into a store of value, a gap emerged for a blockchain-based currency optimized for fast, low-cost transactions accessible to the general public.
Solution:
Bitcoin Cash increases block size limits from 1 MB to 32 MB, enabling more transactions per block and reducing congestion. This on-chain scaling approach allows for faster confirmations and lower fees, making microtransactions feasible. The network supports basic smart contract functionality and replay protection, maintaining compatibility with Bitcoin's core architecture while prioritizing payment utility.
Market Analysis:
Bitcoin Cash operates in the digital currency segment, competing with Bitcoin, Litecoin, and stablecoins for use in payments and remittances. While not the market leader, it occupies a niche focused on on-chain scalability for transactional use. Its adoption is influenced by merchant acceptance, exchange liquidity, and narratives around digital cash. Key risks include competition from layer-2 solutions on other blockchains, regulatory scrutiny of cryptocurrencies, and lower developer and miner activity compared to larger networks. Price movements are often tied to broader crypto market trends and internal protocol developments. Despite its established presence, long-term growth depends on sustained utility, network security, and differentiation in a market increasingly dominated by high-throughput smart contract platforms.
Fundamental Grade: 80.41% (Community 62%, Tokenomics 100%, Exchange 100%, VC —, DeFi Scanner 72%).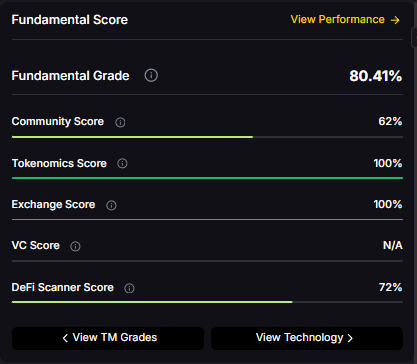
Technology Grade: 29.63% (Activity 22%, Repository 70%, Collaboration 48%, Security —, DeFi Scanner 72%).
Can BCH reach $3,000?
Based on the scenarios, BCH could reach $3,000 in the 23T moon case and 31T base case. The 23T tier projects $3,446.53 in the moon case. Not financial advice.
Can BCH 10x from current levels?
At current price of $553.54, a 10x would reach $5,535.40. This falls within the 31T base and moon cases. Bear in mind that 10x returns require substantial market cap expansion. Not financial advice.
Should I buy BCH now or wait?
Timing depends on your risk tolerance and macro outlook. Current price of $553.54 sits below the 8T bear case in our scenarios. Dollar-cost averaging may reduce timing risk. Not financial advice.
Want exposure? Buy BCH on MEXC
Disclosure
Educational purposes only, not financial advice. Crypto is volatile, do your own research and manage risk.
%201.svg)
%201.svg)
Infrastructure protocols become more valuable as the crypto ecosystem scales and relies on robust middleware. Chainlink provides critical oracle infrastructure where proven utility and deep integrations drive long-term value over retail speculation. Increasing institutional adoption raises demand for professional-grade data delivery and security.
Token Metrics projections for LINK below span multiple total market cap scenarios from conservative to aggressive. Each tier assumes different levels of infrastructure demand as crypto evolves from speculative markets to institutional-grade systems. These bands frame LINK's potential outcomes into 2027.

Disclosure
Educational purposes only, not financial advice. Crypto is volatile, do your own research and manage risk.
How to read it: Each band blends cycle analogues and market-cap share math with TA guardrails. Base assumes steady adoption and neutral or positive macro. Moon layers in a liquidity boom. Bear assumes muted flows and tighter liquidity.
TM Agent baseline: Token Metrics lead metric for Chainlink, cashtag $LINK, is a TM Grade of 23.31%, which translates to a Sell, and the trading signal is bearish, indicating short-term downward momentum. This means Token Metrics currently does not endorse $LINK as a long-term buy at current conditions.
Live details: Chainlink Token Details
Affiliate Disclosure: We may earn a commission from qualifying purchases made via this link, at no extra cost to you.
Token Metrics scenarios span four market cap tiers, each representing different levels of crypto market maturity and liquidity:
8T: At an 8 trillion dollar total crypto market cap, LINK projects to $26.10 in bear conditions, $30.65 in the base case, and $35.20 in bullish scenarios.
16T: Doubling the market to 16 trillion expands the range to $42.64 (bear), $56.29 (base), and $69.95 (moon).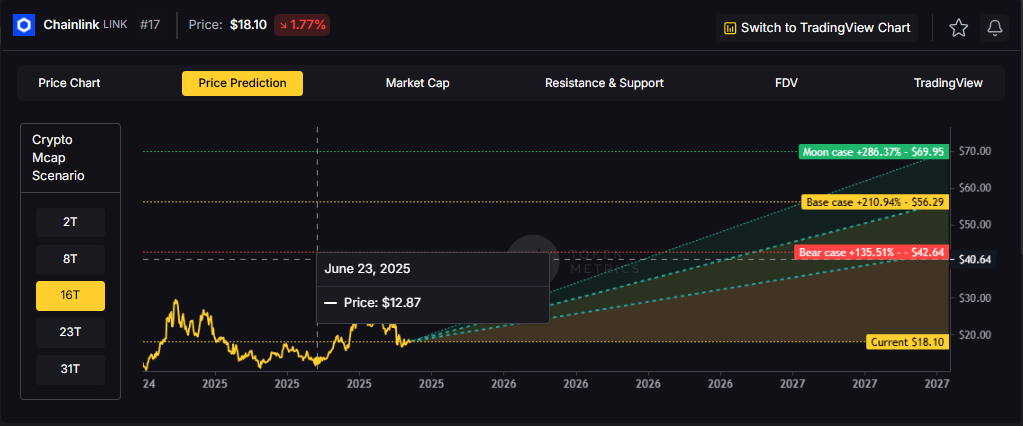
23T: At 23 trillion, the scenarios show $59.18, $81.94, and $104.70 respectively.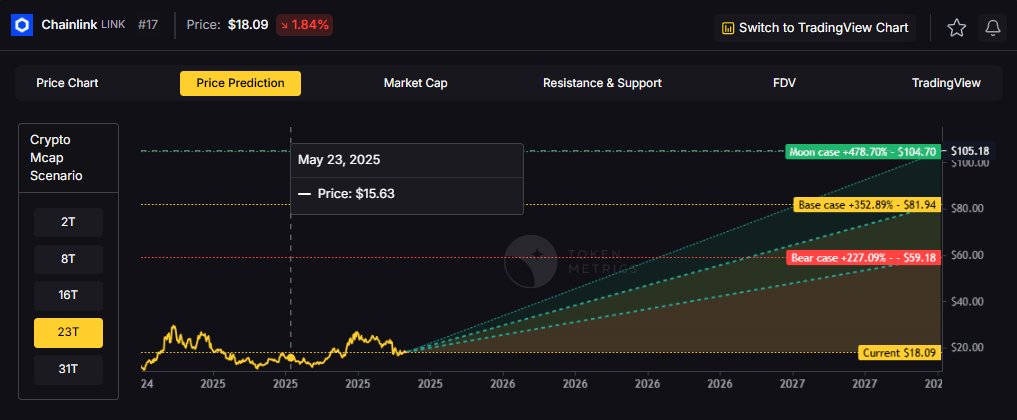
31T: In the maximum liquidity scenario of 31 trillion, LINK could reach $75.71 (bear), $107.58 (base), or $139.44 (moon).
Chainlink represents one opportunity among hundreds in crypto markets. Token Metrics Indices bundle LINK with top one hundred assets for systematic exposure to the strongest projects. Single tokens face idiosyncratic risks that diversified baskets mitigate.
Historical index performance demonstrates the value of systematic diversification versus concentrated positions.
Chainlink is a decentralized oracle network that connects smart contracts to real-world data and systems. It enables secure retrieval and verification of off-chain information, supports computation, and integrates across multiple blockchains. As adoption grows, Chainlink serves as critical infrastructure for reliable data feeds and automation.
The LINK token is used to pay node operators and secure the network’s services. Common use cases include DeFi price feeds, insurance, and enterprise integrations, with CCIP extending cross-chain messaging and token transfers.
Vision: Chainlink aims to create a decentralized, secure, and reliable network for connecting smart contracts with real-world data and systems. Its vision is to become the standard for how blockchains interact with external environments, enabling trust-minimized automation across industries.
Problem: Smart contracts cannot natively access data outside their blockchain, limiting their functionality. Relying on centralized oracles introduces single points of failure and undermines the security and decentralization of blockchain applications. This creates a critical need for a trustless, tamper-proof way to bring real-world information onto blockchains.
Solution: Chainlink solves this by operating a decentralized network of node operators that fetch, aggregate, and deliver data from off-chain sources to smart contracts. It uses cryptographic proofs, reputation systems, and economic incentives to ensure data integrity. The network supports various data types and computation tasks, allowing developers to build complex, data-driven decentralized applications.
Market Analysis: Chainlink is a market leader in the oracle space and a key infrastructure component in the broader blockchain ecosystem, particularly within Ethereum and other smart contract platforms. It faces competition from emerging oracle networks like Band Protocol and API3, but maintains a strong first-mover advantage and widespread integration across DeFi, NFTs, and enterprise blockchain solutions. Adoption is driven by developer activity, partnerships with major blockchain projects, and demand for secure data feeds. Key risks include technological shifts, regulatory scrutiny on data providers, and execution challenges in scaling decentralized oracle networks. As smart contract usage grows, so does the potential for oracle services, positioning Chainlink at the center of a critical niche, though its success depends on maintaining security and decentralization over time.
Fundamental Grade: 74.58% (Community 81%, Tokenomics 100%, Exchange 100%, VC —, DeFi Scanner 17%).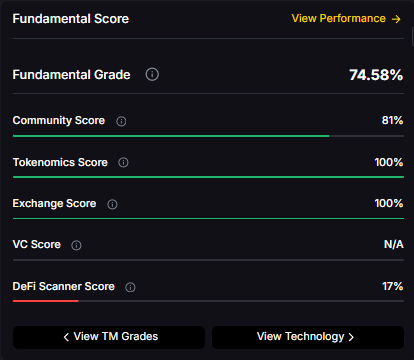
Technology Grade: 88.50% (Activity 81%, Repository 72%, Collaboration 100%, Security 86%, DeFi Scanner 17%).
Can LINK reach $100?
Yes. Based on the scenarios, LINK could reach $100+ in the 23T moon case. The 23T tier projects $104.70 in the moon case. Not financial advice.
What price could LINK reach in the moon case?
Moon case projections range from $35.20 at 8T to $139.44 at 31T. These scenarios assume maximum liquidity expansion and strong Chainlink adoption. Not financial advice.
Should I buy LINK now or wait?
Timing depends on risk tolerance and macro outlook. Current price of $18.09 sits below the 8T bear case in the scenarios. Dollar-cost averaging may reduce timing risk. Not financial advice.
Track live grades and signals: Token Details
Want exposure? Buy LINK on MEXC
Disclosure
Educational purposes only, not financial advice. Crypto is volatile, do your own research and manage risk.
Discover the full potential of your crypto research and portfolio management with Token Metrics. Our ratings combine AI-driven analytics, on-chain data, and decades of investing expertise—giving you the edge to navigate fast-changing markets. Try our platform to access scenario-based price targets, token grades, indices, and more for institutional and individual investors. Token Metrics is your research partner through every crypto market cycle.
%201.svg)
%201.svg)
The crypto market is tilting bullish into 2026 as liquidity, infrastructure, and participation improve across the board. Clearer rules and standards are reshaping the classic four-year cycle, flows can arrive earlier, and strength can persist longer than in prior expansions.
Institutional access is widening through ETFs and custody, while L2 scaling and real-world integrations help sustain on‑chain activity. This healthier backdrop frames our scenario work for HYPE. The ranges below reflect different total crypto market sizes and the share Hyperliquid could capture under each regime.
Disclosure
Educational purposes only, not financial advice. Crypto is volatile, do your own research and manage risk.
How to read it: Each band blends cycle analogues and market-cap share math with TA guardrails. Base assumes steady adoption and neutral or positive macro. Moon layers in a liquidity boom. Bear assumes muted flows and tighter liquidity.
TM Agent baseline: Token Metrics TM Grade is 73.9%, a Buy, and the trading signal is bearish, indicating short-term downward momentum. This means Token Metrics judges HYPE as fundamentally attractive over the long term, while near-term momentum is negative and may limit rallies.
Live details: Hyperliquid Token Details
Affiliate Disclosure: We may earn a commission from qualifying purchases made via this link, at no extra cost to you.
Scenario Analysis
Token Metrics scenarios span four market cap tiers, each representing different levels of crypto market maturity and liquidity:
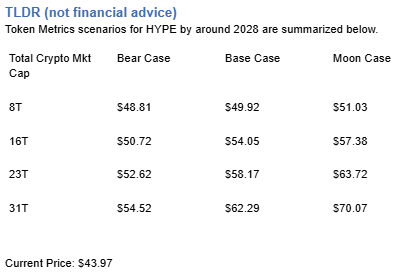
8T: At an 8 trillion dollar total crypto market cap, HYPE projects to $48.81 in bear conditions, $49.92 in the base case, and $51.03 in bullish scenarios.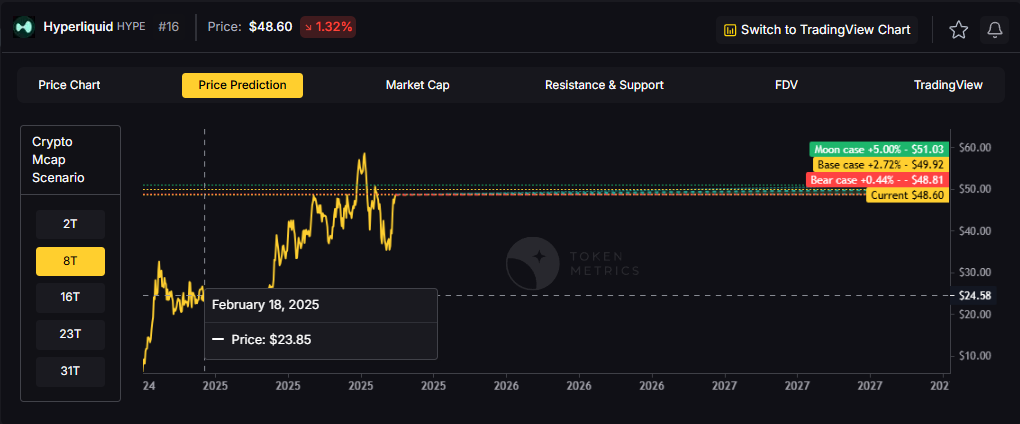
16T: Doubling the market to 16 trillion expands the range to $50.72 (bear), $54.05 (base), and $57.38 (moon).
23T: At 23 trillion, the scenarios show $52.62, $58.17, and $63.72 respectively.
31T: In the maximum liquidity scenario of 31 trillion, HYPE could reach $54.52 (bear), $62.29 (base), or $70.07 (moon).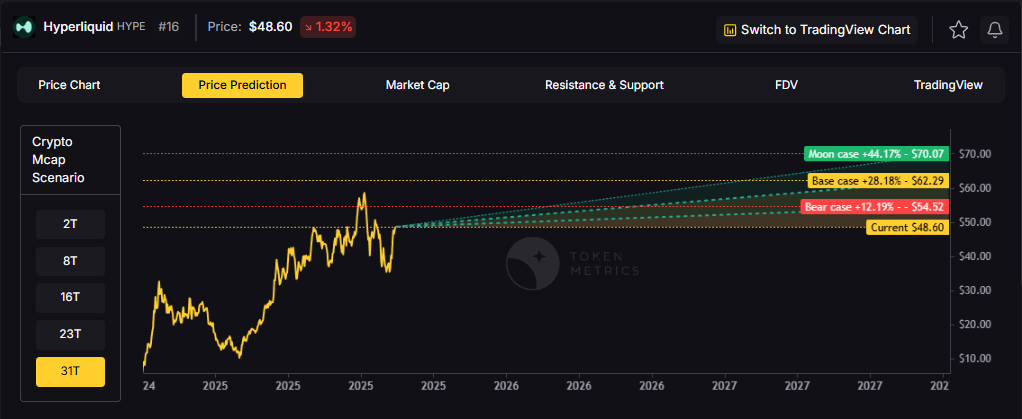
Each tier assumes progressively stronger market conditions, with the base case reflecting steady growth and the moon case requiring sustained bull market dynamics.
Diversification matters. HYPE is compelling, yet concentrated bets can be volatile. Token Metrics Indices hold HYPE alongside the top one hundred tokens for broad exposure to leaders and emerging winners.
Our backtests indicate that owning the full market with diversified indices has historically outperformed both the total market and Bitcoin in many regimes due to diversification and rotation.
Hyperliquid is a decentralized exchange focused on perpetual futures with a high-performance order book architecture. The project emphasizes low-latency trading, risk controls, and capital efficiency aimed at professional and retail derivatives traders. Its token, HYPE, is used for ecosystem incentives and governance-related utilities.
Can HYPE reach $60?
Yes, the 23T and 31T tiers imply ranges above $60 in the Base and Moon bands, though outcomes depend on liquidity and adoption. Not financial advice.
Is HYPE a good long-term investment?
Outcome depends on adoption, liquidity regime, competition, and supply dynamics. Diversify and size positions responsibly.
Disclosure
Educational purposes only, not financial advice. Crypto is volatile, do your own research and manage risk.
Token Metrics delivers AI-based crypto ratings, scenario projections, and portfolio tools so you can make smarter decisions. Discover real-time analytics on Token Metrics.
%201.svg)
%201.svg)
Crypto markets never sleep—prices shift 24/7, blockchain activity surges minute by minute, and traders, analysts, or developers want up-to-the-second data. But where do wallet trackers, trading bots, or dashboards source this real-time information? The answer: powerful crypto APIs that connect applications directly to live blockchain and market data streams.
Crypto APIs (Application Programming Interfaces) are the digital bridges between external software applications—like portfolio trackers, exchanges, or research platforms—and sources of cryptocurrency market and blockchain data. Instead of developers parsing raw blockchain nodes or manually scraping exchange data, APIs offer structured, standardized access to:
APIs can be called on-demand (REST APIs) for snapshots, or stream continuous updates (WebSockets) for real-time data. This accessibility enables faster, more reliable, and easily scalable integration for any crypto application.
Real-time crypto data means delivering the most current information to users, ideally within milliseconds or a few seconds of it being published on an exchange or blockchain. In volatile markets, the difference between real-time and delayed data can be significant, especially for automated applications like trading bots, AI agents, or alert systems.
Unlike historical data—used for backtesting or research—real-time data requires:
This demand for immediacy has shaped how top crypto APIs are built and how they interact with core data sources.
To supply accurate real-time data, APIs must connect with several pillars of the crypto ecosystem:
APIs with broad coverage ensure more accurate, real-time market snapshots and make it easier for applications to monitor thousands of assets or protocols efficiently.
The journey of real-time crypto data from its origin to your screen usually involves these steps:
The architecture behind these systems is complex—requiring careful engineering, robust security, and transparency to prevent data discrepancies or manipulation.
Real-time crypto data powers more than just flashy charts. Its uses include:
This abundance of real-time information can enhance decision-making, improve user experience, and expand what’s possible for crypto developers and professionals—even outside trading or investing contexts.
Build Smarter Crypto Apps & AI Agents with Token Metrics
Token Metrics provides real-time prices, trading signals, and on-chain insights all from one powerful API. Grab a Free API Key
Crypto APIs deliver real-time data primarily through WebSocket streams, which allow fast, continuous data transfer. REST APIs provide snapshot data for quick queries. Some use webhooks or subscribe to blockchain events for instant updates when transactions or blocks are confirmed.
APIs aggregate data from various exchanges and blockchain nodes, cross-referencing sources to detect discrepancies or outliers. They normalize ticker symbols, prioritize high-liquidity markets, and filter out manipulated or erroneous data before serving it to users.
Yes, most top crypto APIs provide endpoints for both real-time streaming and historical data retrieval. Developers can analyze past price trends, on-chain activity, or backtest strategies alongside accessing live market and blockchain feeds.
Leading crypto APIs use HTTPS encryption, authentication tokens, and strict permission controls to protect user data. Still, sensitive actions (like executing trades or broadcasting transactions) should use APIs from trusted, reputable providers with robust security policies.
Limitations include rate limits (restricting request frequency), potential latency during market surges, and incomplete coverage if certain exchanges or blockchains aren't integrated. Some APIs may also restrict access to premium real-time features behind subscriptions.
This content is for informational and educational purposes only. No financial, investment, or trading advice is provided or implied. Cryptocurrency carries risks; always conduct your own research and due diligence before using any platform, service, or API.
%201.svg)
%201.svg)
The explosive growth in cryptocurrency and blockchain technology has spawned a thriving ecosystem powered by data, automation, and real-time analytics. At the heart of this innovation are APIs—critical tools that connect crypto apps, trading platforms, wallets, and analytics dashboards to the blockchain or market data providers. But not all crypto APIs are created equal. Understanding the differences between REST, WebSocket, and GraphQL APIs can unlock new opportunities for enhanced performance, user experience, and scalability in your crypto projects.
APIs, or Application Programming Interfaces, act as bridges allowing different software systems to communicate with each other. In the context of cryptocurrency, APIs provide access to blockchain data, market price feeds, historical charts, transaction alerts, order book updates, and even smart contract interactions. Crypto APIs make it possible for developers and analysts to:
APIs differ in how they deliver information, their performance characteristics, and their flexibility. The three dominant types—REST, WebSocket, and GraphQL—each have unique strengths and best-fit scenarios.
REST (Representational State Transfer) APIs are among the most widely used in the crypto world. REST APIs rely on standard HTTP methods (like GET, POST, PUT, DELETE) to request or update data. Each endpoint URL represents a specific resource—for example, current price data for BTC/USD or historical trades.
REST remains the backbone of many data feeds, exchange integrations, and base-level blockchain explorers due to its universality and reliability.
For high-speed trading, instant alerts, or live order book monitoring, REST’s limitations become apparent. This is where WebSocket APIs excel. WebSockets enable persistent, bidirectional communication between client and server. Once the connection is established, data flows in real time—no need for repeated requests.
Any serious trading or live data dashboard in the crypto space will rely—at least in part—on WebSocket connections for their core user experience.
GraphQL, developed by Facebook, is a query language and runtime for APIs, and has gained traction in advanced crypto analytics and on-chain data services. Unlike REST, which returns fixed data structures, GraphQL allows clients to specify exactly what information they need in a single request.
GraphQL excels in scenarios demanding detailed, structured blockchain analytics, research dashboards, and customizable front ends that aggregate several data types.
Which API architecture should you use for your crypto development or analytical projects? The answer depends on multiple factors:
Many crypto apps combine these models—using REST for core data, WebSocket for live streams, and GraphQL for specialized research queries. Leading APIs—including Token Metrics—offer a blend of these approaches, allowing developers and analysts to match API features to use case requirements.
Build Smarter Crypto Apps & AI Agents with Token Metrics
Token Metrics provides real-time prices, trading signals, and on-chain insights all from one powerful API. Grab a Free API Key
REST APIs use single, on-demand requests for data, returning results each time a client asks. WebSocket APIs establish a persistent connection, enabling real-time, two-way updates perfect for live price feeds, trading platforms, and instant notifications.
GraphQL APIs are increasingly common for advanced research platforms, analytics dashboards, and projects needing complex, tailor-fit data queries. While REST and WebSocket remain more widespread, GraphQL’s adoption is growing rapidly among leading data providers such as Token Metrics.
Each API type has unique use cases—REST for simplicity and familiarity, WebSocket for real-time needs, and GraphQL for precision and customization. Many modern platforms offer a mix, allowing you to choose the most effective tool per feature.
Yes. Many robust crypto platforms and tools combine REST for standard data queries, WebSocket for live updates, and GraphQL for advanced analytics to provide comprehensive, efficient functionality.
Always secure API keys, use HTTPS, respect rate limits, and implement proper error handling. Choose reputable providers like Token Metrics for consistent data quality and platform security.
This article is for educational and informational purposes only. It does not constitute investment advice, trading recommendations, or offer guarantees of performance. Always conduct independent research and use APIs in accordance with their respective terms and conditions.
%201.svg)
%201.svg)
The world of crypto moves fast—data updates by the second and new protocols launch every week. Whether you're building trading bots, analytics dashboards, or AI-driven crypto research tools, your core infrastructure decision often comes down to this: should you use a pre-built crypto API or invest the time and resources to build your own data pipeline from scratch?
APIs, or Application Programming Interfaces, serve as gateways to real-time data and services. A crypto API provides standardized access to digital asset information such as price quotes, trading volumes, market histories, technical indicators, on-chain activity, and even AI-driven signals. Instead of scraping dozens of sources or building direct exchange integrations, developers and analysts get reliable, programmable access via a single, unified API. This foundation can power research dashboards, machine learning models, portfolio trackers, web or mobile apps, and more.
Constructing a DIY crypto data pipeline seems appealing for control and customization. However, the journey involves significant obstacles and ongoing effort:
For most users, these risks can outweigh the perceived benefits, especially as data needs become more sophisticated (e.g., real-time, AI-ready, or multi-chain inputs).
Leveraging a trusted crypto API provides significant advantages for both individual analysts and enterprise applications:
By leveraging APIs, developers and researchers capitalize on shared infrastructure, while gaining access to up-to-the-minute datasets crucial for machine learning, backtesting, and AI-driven workflows.
On the surface, building an in-house data solution seems cheaper, especially for technically capable teams. However, true cost calculations must account for:
In contrast, crypto API consumption usually follows a tiered, pay-as-you-grow model. For most projects, this delivers predictable costs versus the hidden, often escalating expenses of DIY approaches.
Many of today’s most innovative crypto tools—from algorithmic trading bots to predictive dashboards—rely on AI and big data analytics. These tools thrive on high-frequency, accurate, and broad market datasets. Building the data foundation in-house often diverts attention and resources from model design or product features.
API-first solutions enable seamless data ingestion for AI, supporting:
In the high-speed world of crypto, this agility and data quality often determine the difference between a useful tool and one that falls behind market realities.
Build Smarter Crypto Apps & AI Agents with Token Metrics
Token Metrics provides real-time prices, trading signals, and on-chain insights all from one powerful API. Grab a Free API Key
Crypto APIs can offer price quotes, historical data, order book snapshots, trading volumes, blockchain transactions, address activity, technical indicators, social mentions, and even AI-generated research signals—all packaged for easy retrieval and analysis.
Reputable API providers implement robust security measures, including end-to-end encryption, access controls, and continuous monitoring. Always research a provider’s security policies and consider limiting API permissions as a best practice.
Most advanced APIs provide real-time or near-real-time updates, typically every few seconds for price data. Some also offer streaming endpoints for continuous delivery. Always check the documentation for specific latency and refresh intervals.
Many APIs aggregate data from several exchanges, blockchains, or analytics providers, ensuring more comprehensive coverage and redundancy versus a single direct integration. This can improve data reliability and reduce downtime.
The Token Metrics API delivers a fusion of real-time market data, on-chain analytics, technical indicators, and algorithmic trading signals, all designed for reliability and easy integration by both developers and researchers.
This blog is for informational purposes only and should not be interpreted as financial, investment, or trading advice. The examples and providers mentioned are for educational comparison and analysis.
%201.svg)
%201.svg)
In the fast-moving world of cryptocurrency and blockchain, the foundation for many apps, exchanges, and research platforms is built on one crucial technology: APIs. If you’ve ever wondered how crypto apps access real-time prices or how traders tap into automated strategies, the answer is often a crypto API. But what exactly is a crypto API, how does it work, and why is it so indispensable?
An API, or Application Programming Interface, serves as a bridge allowing two software systems to communicate. In the context of cryptocurrency, a crypto API enables one platform (such as a website, trading bot, or analytical tool) to connect directly to blockchain networks, exchanges, and relevant databases. Developers and businesses use these APIs to access current market data, account information, blockchain analytics, or to execute operations such as placing a trade or transferring funds.
Crypto APIs are not exclusive to developers. Many common crypto services like portfolio trackers, news aggregators, and AI research tools all rely on APIs to source real-time data that users depend on every day. The use of APIs creates a standardized, efficient, and secure method for interacting with complex decentralized networks.
The primary function of a crypto API is to enable seamless and structured requests between a user-facing platform and deeper data sources, such as exchanges or blockchains. Here’s how the process typically unfolds:
Many APIs provide both public endpoints (such as market summaries or blockchain explorer queries) and private endpoints (like trading or wallet balance checks, which require stronger authentication).
The world of crypto APIs is broad, supporting a wide range of needs within the ecosystem. Here’s a breakdown of popular categories and their use cases:
These APIs underpin countless familiar crypto applications, from exchange mobile apps to AI-driven research platforms like Token Metrics.
Under the hood, most crypto APIs are RESTful, meaning they use standard HTTP methods (GET, POST, PUT, DELETE) to simplify requests and responses. However, some advanced use cases—such as streaming price updates or high-frequency trading—leverage WebSockets or gRPC for real-time, low-latency communication.
Security and authentication are paramount. API keys, OAuth authentication, and IP whitelisting help safeguard sensitive user actions and financial data. Good API providers also implement strict rate limits to ensure performance and fairness among users.
Integration often takes place through SDKs (software development kits) in popular languages like Python, JavaScript, or Java—making it easier for teams to embed crypto functionalities within apps, websites, or even AI agents.
The advantages offered by crypto APIs are profound for both developers and end users:
However, there are important considerations to evaluate when choosing or building a crypto API solution:
AI-powered crypto APIs, like those offered by Token Metrics, combine traditional market data with machine learning insights—unlocking deeper research capabilities for analysts, developers, and product teams.
Build Smarter Crypto Apps & AI Agents with Token Metrics
Token Metrics provides real-time prices, trading signals, and on-chain insights all from one powerful API. Grab a Free API Key
A crypto API lets you pull real-time market data, access blockchain analytics, monitor wallet balances, automate trades, aggregate research, and power custom dashboards. Developers and analysts use APIs to save time, improve data accuracy, and unlock advanced features in their applications.
Most crypto APIs offer a sign-up process where you’ll generate a unique API key. Popular providers like Token Metrics offer both free and premium tiers. Always follow the provider’s onboarding and security instructions when integrating with your software projects or research tools.
Reputable crypto APIs use industry-standard security protocols, such as HTTPS, API keys, and sometimes two-factor authentication or IP whitelisting. Users should store API keys securely and only grant the minimum required permissions for each application to minimize risk.
The best crypto API depends on your project’s needs. Consider factors such as supported exchanges, data refresh rates, reliability, available endpoints, support, and, when needed, AI or analytics features. Comparing providers based on usage requirements is recommended before integrating them into critical applications.
Most crypto APIs are open to developers, startups, and even individual hobbyists. However, some may restrict certain features or require KYC/AML processes for private account actions (such as trading or withdrawals). Always review the provider’s documentation and terms of service.
This content is for informational and educational purposes only. It does not constitute investment advice, offer, or solicitation. Users should exercise caution and conduct independent research before using any API or crypto tool. No endorsement of any specific API or product is implied. Token Metrics is not responsible for third-party API usage or integration outcomes.
%201.svg)
%201.svg)
In an era defined by rapid technological change and evolving cybersecurity threats, maintaining secure and resilient APIs is paramount. Key rotation, the periodic replacement of API credentials, is critical for keeping sensitive systems safe from unauthorized access. However, the challenge lies in updating or replacing API keys without causing disruptions or downtime for your users. How can you design a robust API key rotation strategy that’s both seamless and secure? In this article, we’ll dive deep into practical, real-world approaches for implementing key rotation in your API infrastructures with zero downtime, arming you with the know-how to fortify your applications while upholding uninterrupted service.
API keys are the digital credentials that regulate access to your platform’s endpoints. Over time, these keys can become vulnerable through accidental leaks, code exposure, or insider threats. Regular key rotation limits the lifespan of compromised credentials, minimizing potential attack windows and meeting the compliance demands of standards like SOC 2, HIPAA, and GDPR.
Key rotation can be straightforward for offline systems—but for APIs serving millions of daily requests or integrated into numerous clients, even brief downtime is unacceptable. A sophisticated rotation strategy is essential for:
Rotating keys while maintaining seamless API service is not trivial. Key challenges include:
Ignorance of these pitfalls can result in service downtime, frustrated users, and loss of trust—especially in the high-stakes world of crypto and financial APIs.
Best-in-class API architectures leverage systematic, automation-friendly methods for rotating keys. Here’s a step-by-step overview of how zero-downtime key rotation can be achieved:
This phased approach can be managed via API gateways, secrets managers (like AWS Secrets Manager or HashiCorp Vault), or custom automation pipelines. Automation is crucial for both security and operational scale.
Manual key rotation is error-prone and does not scale. Leading organizations use dedicated tools and APIs for secrets management, automating every phase of the lifecycle:
In the context of crypto APIs, rapid incident response is critical. Automated rotation empowers developers to replace at-risk credentials within minutes, eliminating the manual delays that adversaries can exploit.
Security and uptime are non-negotiable for APIs powering DeFi, exchanges, trading bots, or wallets. Effective rotation design patterns include:
By baking these patterns into your crypto API platform, you not only protect against security risks but also drive developer adoption through reliability and clarity.
Build Smarter Crypto Apps & AI Agents with Token Metrics
Token Metrics provides real-time prices, trading signals, and on-chain insights all from one powerful API. Grab a Free API Key
API key rotation is the process of periodically replacing digital credentials that control access to API endpoints. It is essential for limiting the risk window if a key is exposed and is a fundamental component of secure development and compliance programs.
By allowing both old and new keys to remain active during a transition period, clients can seamlessly migrate to the new key without interruption of service. Downtime only occurs when a key is disabled before all clients have switched over.
Yes. Modern API platforms often integrate with secrets management tools and automation scripts that generate, distribute, and retire keys according to policy—minimizing manual touchpoints and human error.
Continuous monitoring ensures that all clients are migrating as expected and alerts administrators to potential misconfigurations or unauthorized access attempts, enabling swift remediation before issues escalate into downtime.
Absolutely. Solutions like API gateways, cloud-native secrets managers (AWS, GCP, Azure), and specialized crypto API providers like Token Metrics make painless, automated key rotation achievable even at scale.
This article is for general informational purposes only and does not constitute investment, legal, or security advice. Always perform your own due diligence and consult with qualified professionals before implementing any security solution.
%201.svg)
%201.svg)
As the backbone of modern digital communication, APIs are a prime target for cyber threats—especially in crypto, DeFi, and AI-powered applications. One of the most pernicious attacks? The replay attack, in which valid data transmissions are maliciously or fraudulently repeated. For API providers and developers, preventing replay attacks isn’t an option—it's an absolute necessity for robust security.
A replay attack occurs when a malicious actor intercepts a valid data packet and then retransmits it to trick a system into performing unauthorized operations. In API contexts, attackers may reuse valid requests (often containing authentication details) to perform duplicate transactions or gain unauthorized access. Because the replayed request was originally valid, servers without adequate safeguards may not detect the threat.
Robust replay attack prevention begins with understanding core technical methods. The following are widely accepted best practices—often used together for comprehensive protection.
Leading crypto APIs, such as those used for trading, price feeds, or on-chain analytics, deploy multiple techniques in tandem. Here’s an analytical walkthrough of practical implementation:
Importantly, the combination of these techniques not only prevents replay attacks but also helps authenticate requests and ensure integrity—critical for the high-value operations typical in crypto environments.
Developers and security architects must employ a layered defense. Consider adopting the following practical steps:
By following these best practices, API providers can significantly reduce the risk of replay attacks—even in the fast-paced, high-stakes environment of crypto and AI-powered platforms.
Modern API infrastructure benefits from AI-driven monitoring tools that can detect and flag anomalies—such as repeated requests, abnormal traffic spikes, or suspicious timestamp patterns—suggesting a potential replay attack in progress. By integrating machine learning with traditional security controls, application teams can spot sophisticated threats that might slip past static rules, ensuring a more resilient API ecosystem.
Build Smarter Crypto Apps & AI Agents with Token Metrics
Token Metrics provides real-time prices, trading signals, and on-chain insights all from one powerful API. Grab a Free API Key
A replay attack involves resending valid data to trick an API, while a man-in-the-middle attack intercepts and can alter communication between two parties. Both can be used in tandem, but replay attacks specifically exploit a system’s inability to detect previously valid requests being repeated.
Nonces ensure each API request is unique. If an attacker tries to repeat a request using the same nonce, the server recognizes the duplicate and rejects it, preventing unauthorized operations.
TLS/HTTPS encrypt communications but do not inherently prevent replay attacks. Replay prevention requires application-level controls like nonces or timestamps, as encrypted packets can still be captured and resent if no additional safeguards exist.
APIs can log incoming requests’ nonces, timestamps, and signatures. If a duplicate nonce or old timestamp appears, the server detects and blocks the replay. Real-time monitoring and alerting further reduce risks.
Yes. OAuth 2.0, OpenID Connect, and major crypto API specs recommend nonces, timestamp validation, and signatures as standard practices to prevent replay attacks. Following established security frameworks ensures better protection.
This blog is for educational purposes only. It does not constitute investment, legal, or other professional advice. Please conduct your own research or consult experts before implementing security practices in critical systems. Token Metrics does not offer investment services or guarantees of performance.
%201.svg)
%201.svg)
In the fast-moving world of crypto, robust security isn’t just an option—it’s essential. With countless applications powered by APIs exchanging sensitive data, managing cryptographic keys effectively is a foundational pillar for trust and protection. But what exactly does strong key management look like for a crypto API service, and why does it matter so much?
APIs are arteries of modern crypto platforms. They power everything from automated trading to blockchain analytics, moving sensitive data such as user credentials, wallet addresses, and real-time transaction histories. Cryptographic keys serve as the gatekeepers to this data—enabling authentication, encrypting requests and responses, and regulating who can interact with a service.
If keys fall into the wrong hands due to inadequate management, the repercussions are significant: data breaches, unauthorized withdrawals, reputational damage, and regulatory penalties. With rising cyberattacks targeting API endpoints and credentials, the standard for key management in crypto APIs is more rigorous than ever.
Effective key management goes beyond simple storage. The following principles are vital for any crypto API provider or developer:
Every aspect—from onboarding to deprovisioning an API key—should reinforce these pillars.
Securing a crypto API requires a disciplined approach throughout the key’s lifecycle: from its generation and distribution to rotation and retirement. Here’s a best-practices checklist for each stage:
These best practices not only minimize the window of exposure but also simplify legal and regulatory compliance, such as with GDPR or SOC 2 obligations.
API secrets, including API keys, tokens, and passphrases, are prime targets for attackers. Here are proven approaches for secrets management and enforcing secure access control:
Modern cloud-based API management platforms—and frameworks for zero trust security—can streamline these controls and offer centralized monitoring for potential threats.
No security system is infallible. Continuous monitoring and rapid incident response are essential components of key management for crypto APIs:
Adopting a proactive, improvement-focused mindset helps API providers stay resilient as attacker techniques grow more sophisticated.
Build Smarter Crypto Apps & AI Agents with Token Metrics
Token Metrics provides real-time prices, trading signals, and on-chain insights all from one powerful API. Grab a Free API Key
Store keys in dedicated, encrypted vaults or hardware security modules (HSMs). Avoid keeping them in plaintext or hard coding them in application code or configuration files. Limit access via permissions and strong identity controls.
API keys should be rotated regularly (e.g., every 3–6 months) and immediately if there is any sign of compromise, personnel changes, or as part of a scheduled security protocol. Automation can streamline this process for large deployments.
Issuing API keys with only the permissions absolutely necessary for a given user or system—such as read-only vs. write access—limits potential damage if a key is compromised. This approach helps reduce risk exposure and aligns with zero trust models.
Yes. Proper key management practices, such as audit trails, incident response, and robust access controls, are essential components for demonstrating compliance with data protection and integrity standards like GDPR, SOC 2, or ISO 27001.
If an API key is exposed, it should be revoked or rotated immediately. Monitor system logs for unauthorized activity, conduct a root cause analysis to determine how the key was compromised, and update protocols to prevent recurrence.
This content is for educational and informational purposes only and should not be interpreted as legal, security, or investment advice. Always consult relevant professionals when implementing crypto security protocols or designing API services.
%201.svg)
%201.svg)
Securing REST API endpoints has become a fundamental concern for developers, especially as sensitive data and critical operations traverse the web. Choosing the right authentication process is vital, and one approach—HMAC (Hash-Based Message Authentication Code)—provides a robust mechanism to ensure secure and tamper-proof communications. But how exactly do you implement HMAC authentication for a REST API endpoint in practice?
HMAC, or Hash-Based Message Authentication Code, is a cryptographic technique that combines a secret key with a message (such as an HTTP request) and then hashes the combination using a secure hash algorithm (like SHA-256). The output hash, called the HMAC signature, is sent along with the API request. On the server side, the same process is repeated to confirm the authenticity and integrity of the request.
This approach protects against request tampering and eavesdropping because only someone with the shared secret key can generate a valid HMAC signature. Unlike basic authentication, which sends credentials with every request, HMAC signatures help defend APIs against replay attacks and man-in-the-middle threats. Additionally, as requested data is included in the signature, any changes during transit will invalidate the signature and trigger security alerts.
REST APIs are widely adopted due to their scalability, simplicity, and statelessness. However, such characteristics make them attractive targets for unauthorized actors. The benefits of using HMAC authentication for REST APIs include:
Financial institutions, crypto APIs, and enterprise SaaS solutions often favor HMAC as a standard defense mechanism for their public endpoints.
Below is a practical workflow to implement HMAC authentication on your REST API endpoint:
An example Authorization header might look like:
Authorization: HMAC apiKey="abc123", signature="d41d8cd98f00b204e9800998ecf8427e", timestamp="1660000000", nonce="fGh8Kl"
Always use time-based mechanisms and nonces to prevent replay. For REST APIs built in Python, Node.js, or Java, popular libraries are available to generate and validate HMAC signatures. Ensure secure storage of all secrets and keys—never hard-code them in source files or share them over email.
Even well-designed authentication processes can be vulnerable if not properly managed. To maximize HMAC's security benefits, follow these best practices:
Furthermore, document the required signature format and header structure for your API consumers to minimize implementation errors.
HMAC authentication is standard in the world of cryptocurrency APIs, where secure and rapid access to on-chain data and market signals is paramount. Leading blockchain data providers, crypto trading platforms, and analytic tools incorporate some variant of HMAC to manage authentication and authorization.
For developers building trading bots, portfolio trackers, or AI-driven analysis platforms, HMAC-protected REST endpoints are both flexible and secure. They allow granular control of permissions and can support high-frequency interactions without the heavy computational load of asymmetric encryption systems.
As the crypto ecosystem evolves, API authentication standards must adapt. Devs should look for providers and platforms—like Token Metrics—that offer transparent, HMAC-secured endpoints and clear implementation guidelines.
Build Smarter Crypto Apps & AI Agents with Token Metrics
Token Metrics provides real-time prices, trading signals, and on-chain insights all from one powerful API. Grab a Free API Key
The most common algorithms are HMAC-SHA-256 and HMAC-SHA-512, both providing strong security. Avoid using outdated algorithms like MD5 or SHA-1 due to known vulnerabilities. HMAC's flexibility allows other hash functions, but always prioritize well-supported, secure industry standards.
API secrets are typically generated and securely shared out-of-band (e.g., within a secure dashboard or encrypted email during onboarding). On the client, store secrets in environment variables or encrypted secrets managers; on the server, keep secrets in secure databases and never log them.
HMAC and OAuth/JWT are different approaches. HMAC is simpler, faster, and well-suited for service-to-service API authentication. OAuth and JWT, meanwhile, support more sophisticated user-based access or delegated authorization. The best choice depends on your use case and security goals.
HMAC is excellent for ensuring integrity and authenticity, but is not a complete solution against all attacks. Use it in combination with HTTPS, strict input validation, throttle policies, and regular security reviews. Comprehensive threat protection requires defense in depth.
Test both client and server components by intentionally altering requests to ensure invalid signatures are rejected. Use available unit tests, API mocking tools, and logging to confirm signatures are computed and validated as expected. Rotate secrets during testing to check for proper handling.
This content is for informational and educational purposes only. It does not constitute security advice or endorse any provider. Implementation details may vary by project and threat model. Always consult with professional security experts to ensure compliance and best practices.
%201.svg)
%201.svg)
In the rapidly evolving world of cryptocurrencies and blockchain development, security is a top concern—especially when building or integrating with crypto APIs. Encryption forms the backbone of secure data exchange, but the landscape includes more than one approach. Understanding the differences between symmetric and asymmetric encryption, and how each fits into the architecture of a secure crypto API, is fundamental for developers and technical decision-makers. In this article, we'll break down these encryption models, explore their uses within a crypto API, and illustrate how secure apps and services leverage them to safeguard digital assets and sensitive data.
Symmetric encryption is one of the oldest and most widely used cryptographic techniques. At its core, symmetric encryption uses a single, secret key to both encrypt (encode) and decrypt (decode) data. Popular algorithms include Advanced Encryption Standard (AES), Data Encryption Standard (DES), and Triple DES (3DES).
Within crypto APIs, symmetric encryption is often used for encrypting traffic between trusted systems or storing data securely on disk.
Asymmetric encryption, also known as public-key cryptography, solves some of the key distribution problems faced by symmetric encryption. It employs a pair of mathematically related keys: a public key (which can be freely distributed) and a private key (which must be kept secure).
Asymmetric encryption underpins digital signatures, public key infrastructure (PKI), and secure client authentication mechanisms found in most modern crypto APIs.
Both symmetric and asymmetric encryption play vital roles in data security, but each comes with its trade-offs. Here’s a breakdown:
Crypto APIs often combine both methods in a model called hybrid encryption, capitalizing on the strengths of each approach.
In the context of crypto APIs—whether for wallet integration, on-chain analytics, or exchange connectivity—security is not just about encrypting transmission but also about robust authentication and authorization.
This layered approach is considered a best practice for maximizing performance and security in crypto API design.
Developers and architects integrating or building crypto APIs can follow these data-backed practices:
By combining these strategies and leveraging strong encryption, API providers can reduce risk and deliver more secure crypto solutions.
Build Smarter Crypto Apps & AI Agents with Token Metrics
Token Metrics provides real-time prices, trading signals, and on-chain insights all from one powerful API. Grab a Free API Key
The primary drawback is key management: securely distributing and storing the same key among multiple parties can be challenging. If a key is leaked, all previously encrypted data may be exposed.
Asymmetric encryption allows one party to authenticate itself by proving knowledge of a private key without directly sharing that key, reducing the risk of credential theft during communication.
Hybrid encryption uses asymmetric algorithms for secure key exchange and authentication, then switches to symmetric encryption to protect high-speed or large-volume API traffic efficiently.
No. While encryption is essential, APIs must also enforce secure authentication, authorization, rate limiting, input validation, and regular security audits to guard against non-cryptographic attacks.
Developers can use tools like SSL Labs, cryptography libraries supporting key rotation and auditing, and AI-based monitoring within platforms like Token Metrics to monitor crypto ecosystem security risks.
This article is for educational and informational purposes only. It does not constitute investment advice, legal advice, or an endorsement of any protocol, technology, or platform. Always consult security professionals when implementing or handling cryptographic systems.

 Create Your Free Account
Create Your Free Account9450 SW Gemini Dr
PMB 59348
Beaverton, Oregon 97008-7105 US
.svg)




.png)
Token Metrics Media LLC is a regular publication of information, analysis, and commentary focused especially on blockchain technology and business, cryptocurrency, blockchain-based tokens, market trends, and trading strategies.
Token Metrics Media LLC does not provide individually tailored investment advice and does not take a subscriber’s or anyone’s personal circumstances into consideration when discussing investments; nor is Token Metrics Advisers LLC registered as an investment adviser or broker-dealer in any jurisdiction.
Information contained herein is not an offer or solicitation to buy, hold, or sell any security. The Token Metrics team has advised and invested in many blockchain companies. A complete list of their advisory roles and current holdings can be viewed here: https://tokenmetrics.com/disclosures.html/
Token Metrics Media LLC relies on information from various sources believed to be reliable, including clients and third parties, but cannot guarantee the accuracy and completeness of that information. Additionally, Token Metrics Media LLC does not provide tax advice, and investors are encouraged to consult with their personal tax advisors.
All investing involves risk, including the possible loss of money you invest, and past performance does not guarantee future performance. Ratings and price predictions are provided for informational and illustrative purposes, and may not reflect actual future performance.



